当前位置:网站首页>1996. number of weak characters in the game
1996. number of weak characters in the game
2022-07-05 05:42:00 【A big pigeon】
topic : Roles have two properties , Attack and defense . When the character's attack and defense are strictly smaller than that of a certain character , Then the role is “ Weak role ”. In the array “ Weak role ” Number .
Explain : This problem can sort the array by attack , Then compare defense . Remember that the current biggest defensive role is q, The currently accessed role is p.
If q defense >p defense , And q attack >p attack , that p Namely “ Weak role ”.
One problem is , How to ensure q defense > p Defensive time ,q attack also > p attack ?
The method given in the solution , Sort by attack descending , Attack at the same time , In ascending defense order .
It can be proved to the contrary :
hypothesis : If q Defense ratio p Big , And q Attack and p The attack is the same .
from ” Attack at the same time , In ascending defense order “ You know q It must be p Back .
But when we traverse from front to back q It must be p front , Wrong assumption .
class Solution:
def numberOfWeakCharacters(self, properties: List[List[int]]) -> int:
properties.sort(key=lambda x: (-x[0], x[1])) # Attack descending , Defense ascending
ans = 0
maxDef = 0
for _, def_ in properties:
if maxDef > def_:
ans += 1
else:
maxDef = max(maxDef, def_)
return ans边栏推荐
- 游戏商城毕业设计
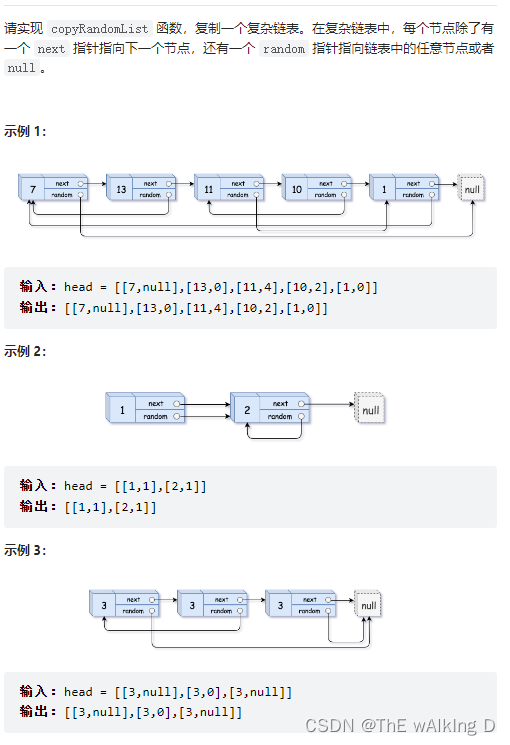
- Sword finger offer 35 Replication of complex linked list
- Web APIs DOM node
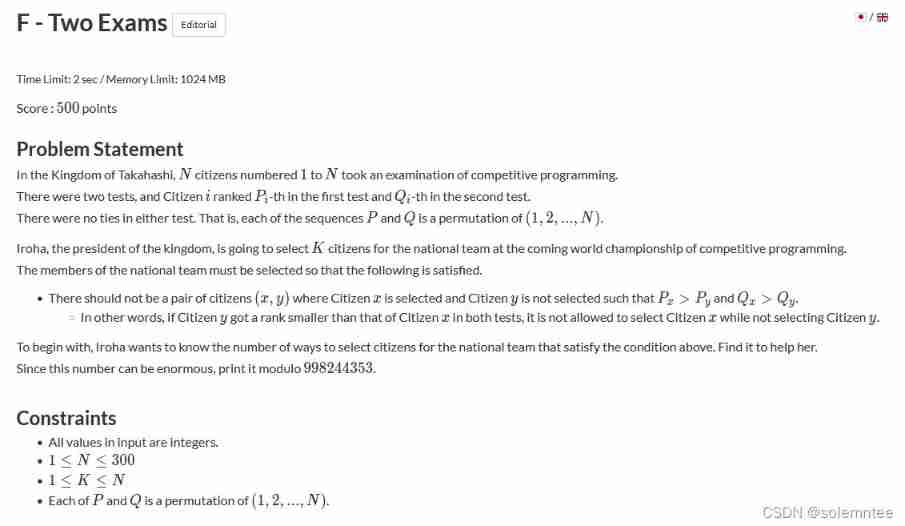
- CCPC Weihai 2021m eight hundred and ten thousand nine hundred and seventy-five
- 2020ccpc Qinhuangdao J - Kingdom's power
- 2022 极术通讯-Arm 虚拟硬件加速物联网软件开发
- Find a good teaching video for Solon framework test (Solon, lightweight application development framework)
- How can the Solon framework easily obtain the response time of each request?
- 网络工程师考核的一些常见的问题:WLAN、BGP、交换机
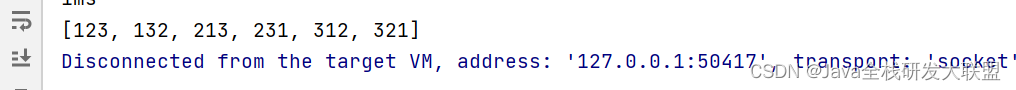
- Csp-j-2020-excellent split multiple solutions
猜你喜欢
随机推荐
Pointnet++ learning
On-off and on-off of quality system construction
Codeforces round 712 (Div. 2) d. 3-coloring (construction)
Warning using room database: schema export directory is not provided to the annotation processor so we cannot export
Simple knapsack, queue and stack with deque
剑指 Offer 35.复杂链表的复制
Introduction to tools in TF-A
2017 USP Try-outs C. Coprimes
Using HashMap to realize simple cache
[cloud native] record of feign custom configuration of microservices
MySQL数据库(一)
Add level control and logger level control of Solon logging plug-in
Demonstration of using Solon auth authentication framework (simpler authentication framework)
Animation scoring data analysis and visualization and it industry recruitment data analysis and visualization
SSH password free login settings and use scripts to SSH login and execute instructions
利用HashMap实现简单缓存
2020ccpc Qinhuangdao J - Kingdom's power
Configuration and startup of kubedm series-02-kubelet
Brief introduction to tcp/ip protocol stack
Bit mask of bit operation