当前位置:网站首页>Redis key operation
Redis key operation
2022-07-06 01:40:00 【Freezing point contract】
operation key
keys * : View all... Of the current library key
exists key: Judge a certain key Whether there is
type key: Judge key What type is it
del key: Delete the specified key The data of
unlink key: Asynchronously delete the specified key( Only will keys from keyspace Delete from metadata , The real deletion will be done asynchronously later )
expire key 10: Set up key The expiration date is 10s
ttl key: see key How much more? s Be overdue ,-1 Represents never expires ,-2 Indicates that it has expired
select db: Switch to the specified library
dbsize: View the current library's key Number
flushdb: Empty the current library
flushall: Empty all libraries
边栏推荐
- Cadre du Paddle: aperçu du paddlelnp [bibliothèque de développement pour le traitement du langage naturel des rames volantes]
- 安装Redis
- Paddle框架:PaddleNLP概述【飛槳自然語言處理開發庫】
- Force buckle 9 palindromes
- Leetcode1961. Check whether the string is an array prefix
- You are using pip version 21.1.1; however, version 22.0.3 is available. You should consider upgradin
- National intangible cultural heritage inheritor HD Wang's shadow digital collection of "Four Beauties" made an amazing debut!
- 【已解决】如何生成漂亮的静态文档说明页
- Basic operations of databases and tables ----- non empty constraints
- [技术发展-28]:信息通信网大全、新的技术形态、信息通信行业高质量发展概览
猜你喜欢
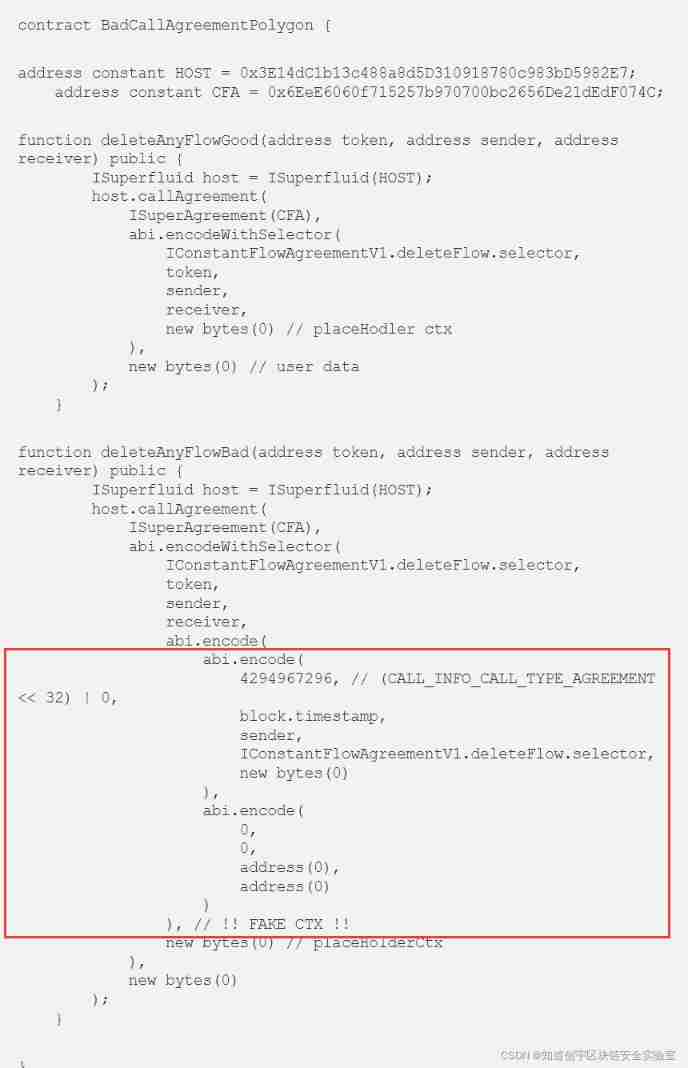
Superfluid_ HQ hacked analysis

False breakthroughs in the trend of London Silver
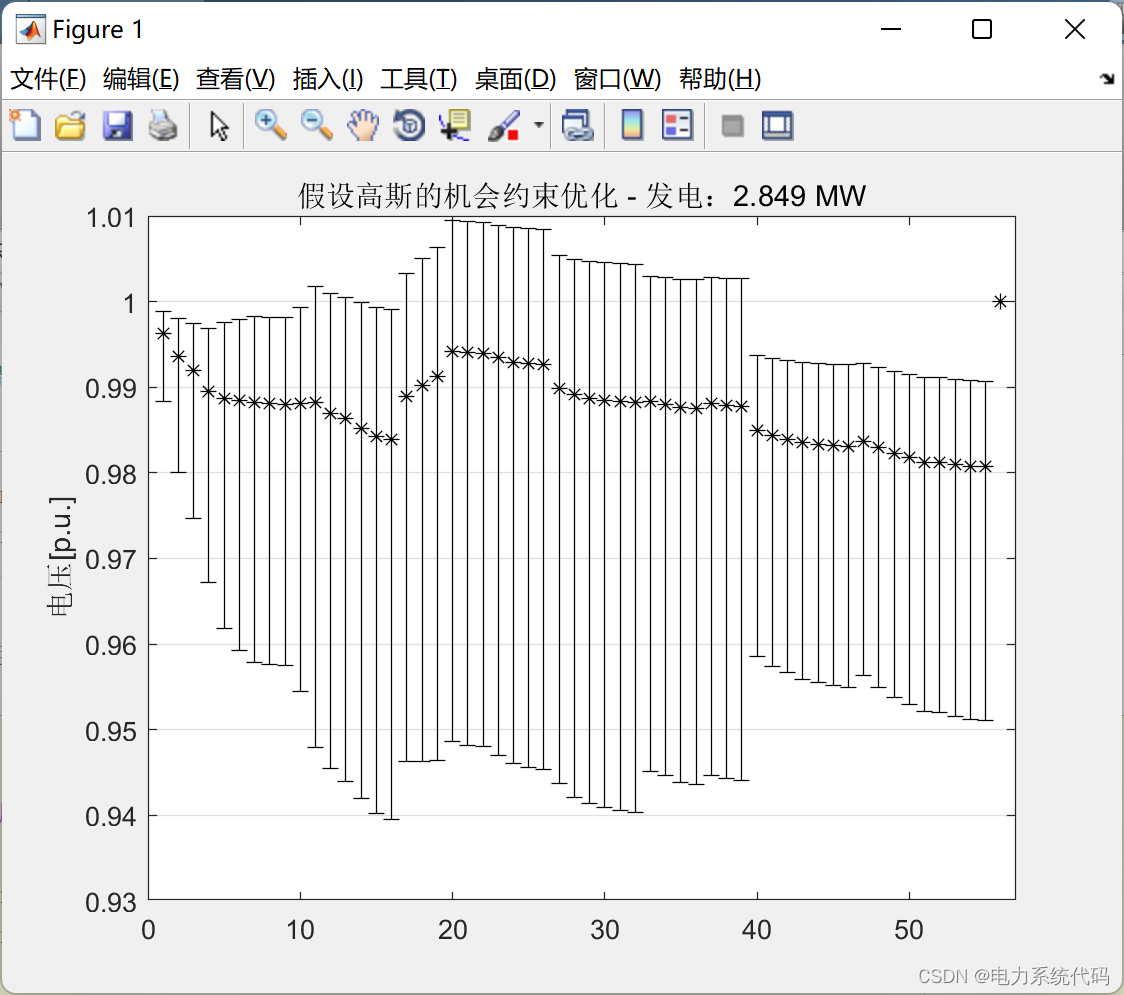
MATLB|实时机会约束决策及其在电力系统中的应用
![[ssrf-01] principle and utilization examples of server-side Request Forgery vulnerability](/img/43/a8f302eb69beff4037aadda808f886.png)
[ssrf-01] principle and utilization examples of server-side Request Forgery vulnerability
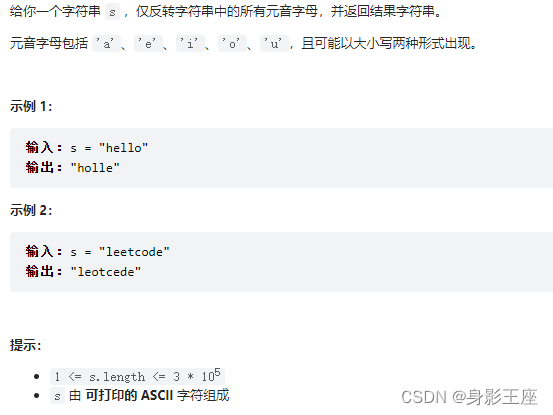
leetcode刷题_反转字符串中的元音字母

Poj2315 football games
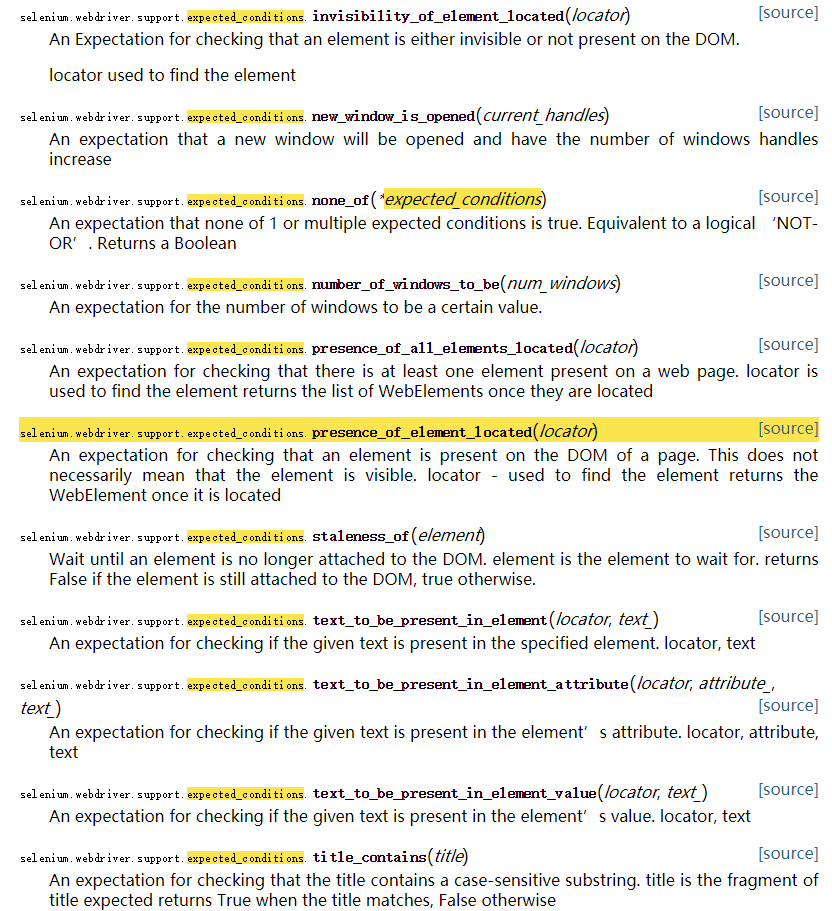
Selenium waiting mode
A picture to understand! Why did the school teach you coding but still not
C web page open WinForm exe
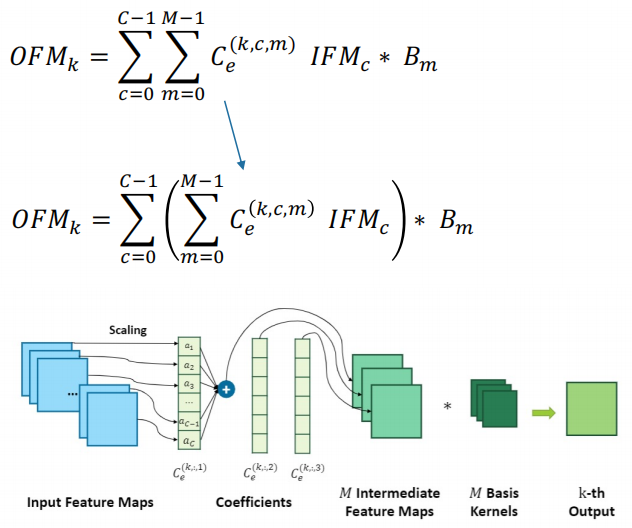
dried food! Accelerating sparse neural network through hardware and software co design
随机推荐
Initialize MySQL database when docker container starts
NLP fourth paradigm: overview of prompt [pre train, prompt, predict] [Liu Pengfei]
[flask] obtain request information, redirect and error handling
Card 4G industrial router charging pile intelligent cabinet private network video monitoring 4G to Ethernet to WiFi wired network speed test software and hardware customization
MATLB | real time opportunity constrained decision making and its application in power system
【全網最全】 |MySQL EXPLAIN 完全解讀
A Cooperative Approach to Particle Swarm Optimization
02.Go语言开发环境配置
Basic operations of database and table ----- set the fields of the table to be automatically added
Ali test Open face test
MUX VLAN configuration
How to get all sequences in Oracle database- How can I get all sequences in an Oracle database?
国家级非遗传承人高清旺《四大美人》皮影数字藏品惊艳亮相!
【Flask】响应、session与Message Flashing
Spir - V premier aperçu
Unreal browser plug-in
Huawei Hrbrid interface and VLAN division based on IP
【Flask】官方教程(Tutorial)-part2:蓝图-视图、模板、静态文件
Comments on flowable source code (XXXV) timer activation process definition processor, process instance migration job processor
Huawei converged VLAN principle and configuration