当前位置:网站首页>L1-027 rental (20 points)
L1-027 rental (20 points)
2022-07-04 07:29:00 【Inter personal liabilities^】
L1-027 lease (20 branch )
Here is a picture of sina Weibo that used to be very popular :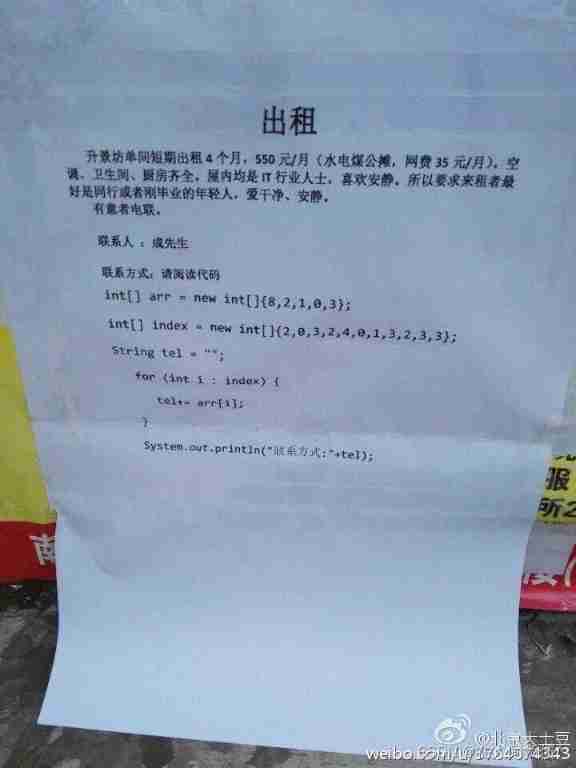
At one time, the Internet was full of cries for help , How to break this . In fact, this code is very simple ,index Array is arr Index of the array ,index[0]=2 Corresponding arr[2]=1,index[1]=0 Corresponding arr[0]=8,index[2]=3 Corresponding arr[3]=0, And so on …… It's easy to get a phone number 18013820100.
This question asks you to write a program , Generate this code for any phone number —— in fact , Just generate the first two lines , The rest is the same .
Input format :
Type in a line to give a result of 11 A cell phone number made up of digits .
Output format :
Generate the first two lines of code for the entered number , among arr The numbers in must be given in descending order .
sample input :
18013820100
sample output :
int[] arr = new int[]{8,3,2,1,0};
int[] index = new int[]{3,0,4,3,1,0,2,4,3,4,4};
AC Code
#include<iostream>
#include<algorithm>
#include<cstring>
#include<cmath>
#include<vector>
#include<stack>
#include<queue>
#include<sstream>
using namespace std;
typedef long long ll;
const int N=100010;
bool bo[15];
int main()
{
string a;
cin >> a;
int arr[15];
for(int i = 0; i < a.size(); i ++ )
if(!bo[a[i] - '0']) bo[a[i] - '0'] = true;
int k = 0;
for(int i = 9; i >= 0; i -- )
if(bo[i]) arr[k ++ ] = i;
int index[15];
int l = 0;
for(int i = 0; i < a.size(); i ++ )
for(int j = 0; j < k; j ++ )
if(a[i] - '0' == arr[j])
index[l ++ ] = j;
cout << "int[] arr = new int[]{";
for(int i = 0; i < k; i ++ )
{
if(i != k - 1) cout << arr[i] << ',';
else cout << arr[i] << "};" << endl;
}
cout << "int[] index = new int[]{";
for(int i = 0; i < l; i ++ )
{
if(i != l - 1) cout << index[i] << ',';
else cout << index[i] << "};" << endl;
}
return 0;
}
边栏推荐
- There is no Chinese prompt below when inputting text in win10 Microsoft Pinyin input method
- Vulhub vulnerability recurrence 76_ XXL-JOB
- 用于压缩视频感知增强的多目标网络自适应时空融合
- Research on an endogenous data security interaction protocol oriented to dual platform and dual chain architecture
- With excellent strength, wangchain technology, together with IBM and Huawei, has entered the annual contribution list of "super ledger"!
- Comparison between applet framework and platform compilation
- Summary of MySQL common judgment functions!! Have you used it
- BasicVSR++: Improving Video Super-Resolutionwith Enhanced Propagation and Alignment
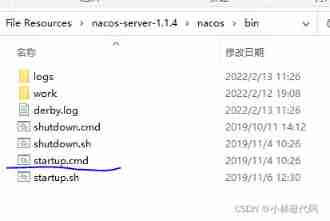
- Used on windows Bat file startup project
- MySQL 数据库 - 函数 约束 多表查询 事务
猜你喜欢
深入浅出:了解时序数据库 InfluxDB

A real penetration test

Blog stop statement
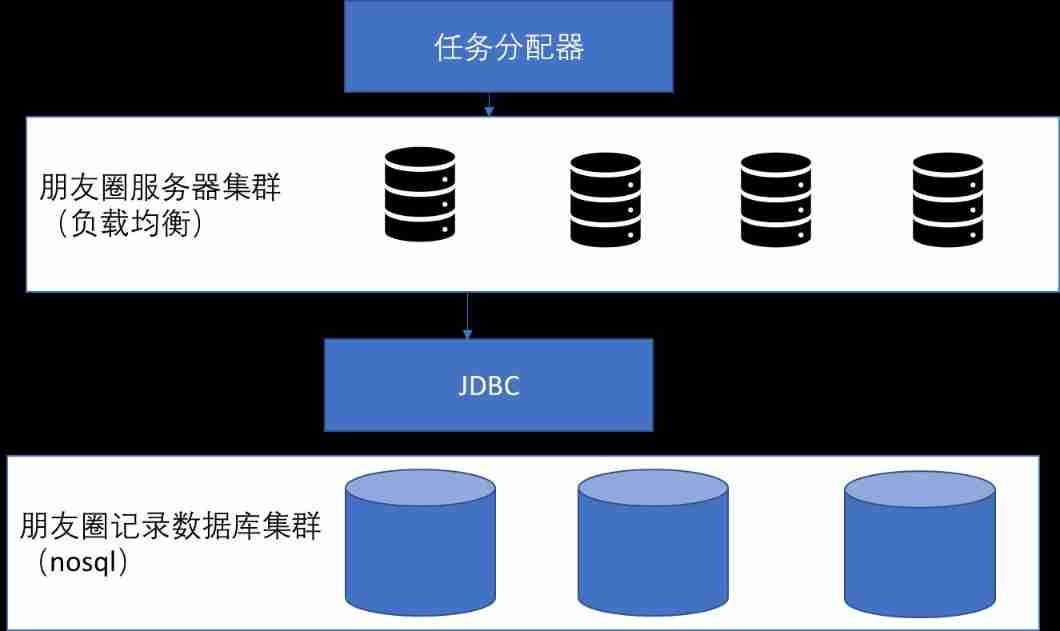
System architecture design of circle of friends
Solution of running crash caused by node error

Amd RX 7000 Series graphics card product line exposure: two generations of core and process mix and match
com. alibaba. nacos. api. exception. NacosException
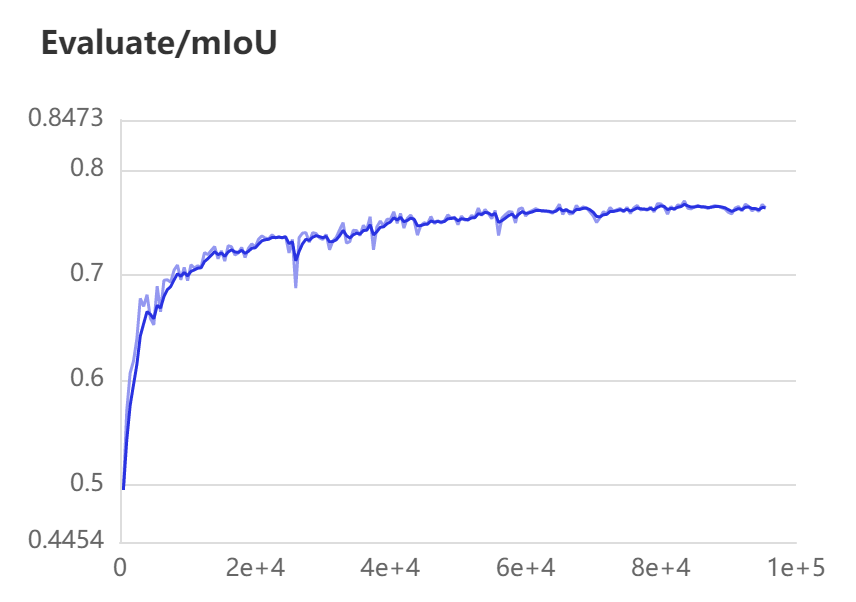
提升复杂场景三维重建精度 | 基于PaddleSeg分割无人机遥感影像

A new understanding of how to encrypt industrial computers: host reinforcement application
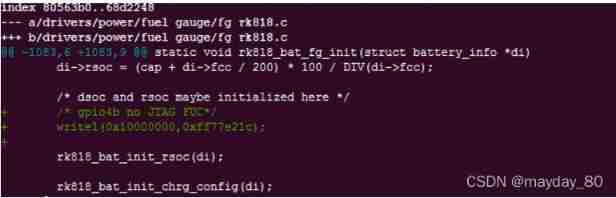
Set JTAG fuc invalid to normal IO port
随机推荐
Rhcsa the next day
输入年份、月份,确定天数
大厂技术专家:架构设计中常用的思维模型
It's healthy to drink medicinal wine like this. Are you drinking it right
Data double write consistency between redis and MySQL
Zephyr learning notes 1, threads
Chain ide -- the infrastructure of the metauniverse
MySQL中的文本处理函数整理,收藏速查
Industrial computer anti-virus
Unity opens the explorer from the inspector interface, selects and records the file path
Would you like to go? Go! Don't hesitate if you like it
What is industrial computer encryption and how to do it
Node connection MySQL access denied for user 'root' @ 'localhost' (using password: yes
Vulhub vulnerability recurrence 76_ XXL-JOB
Blog stop statement
A real penetration test
Solution of running crash caused by node error
Take you to master the formatter of visual studio code
[thread pool]
Summary of MySQL common judgment functions!! Have you used it