当前位置:网站首页>captcha-killer验证码识别插件
captcha-killer验证码识别插件
2022-07-06 09:23:00 【又懒有菜】
目录
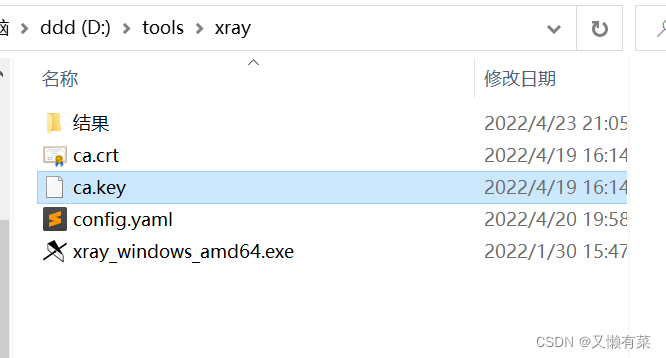
环境的配置
插件下载地址GitHub - broken5/captcha-killer-java8 https://github.com/broken5/captcha-killer-java8
https://github.com/broken5/captcha-killer-java8
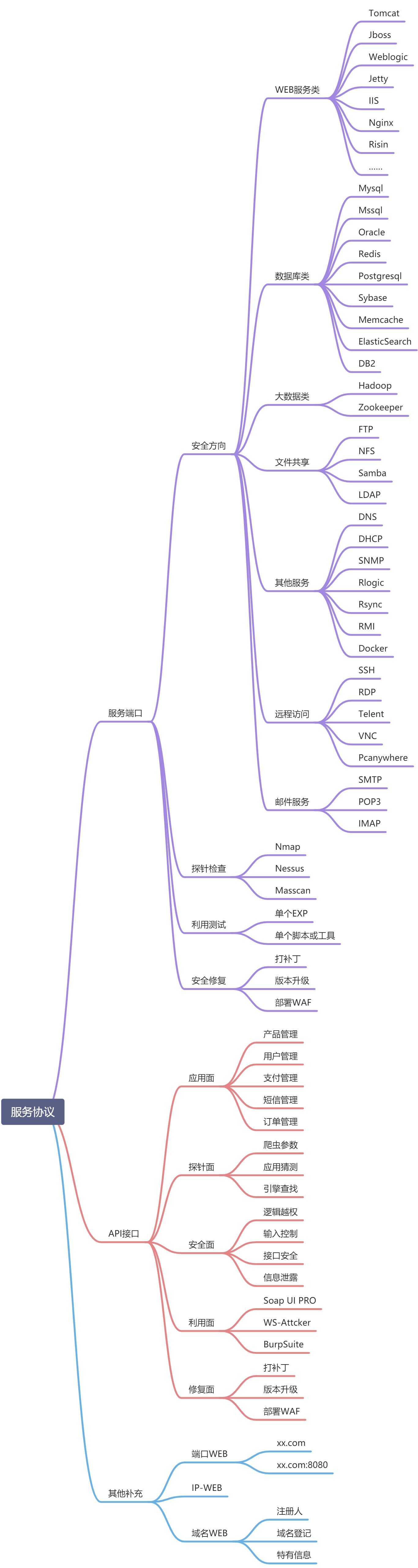
0x01 作用
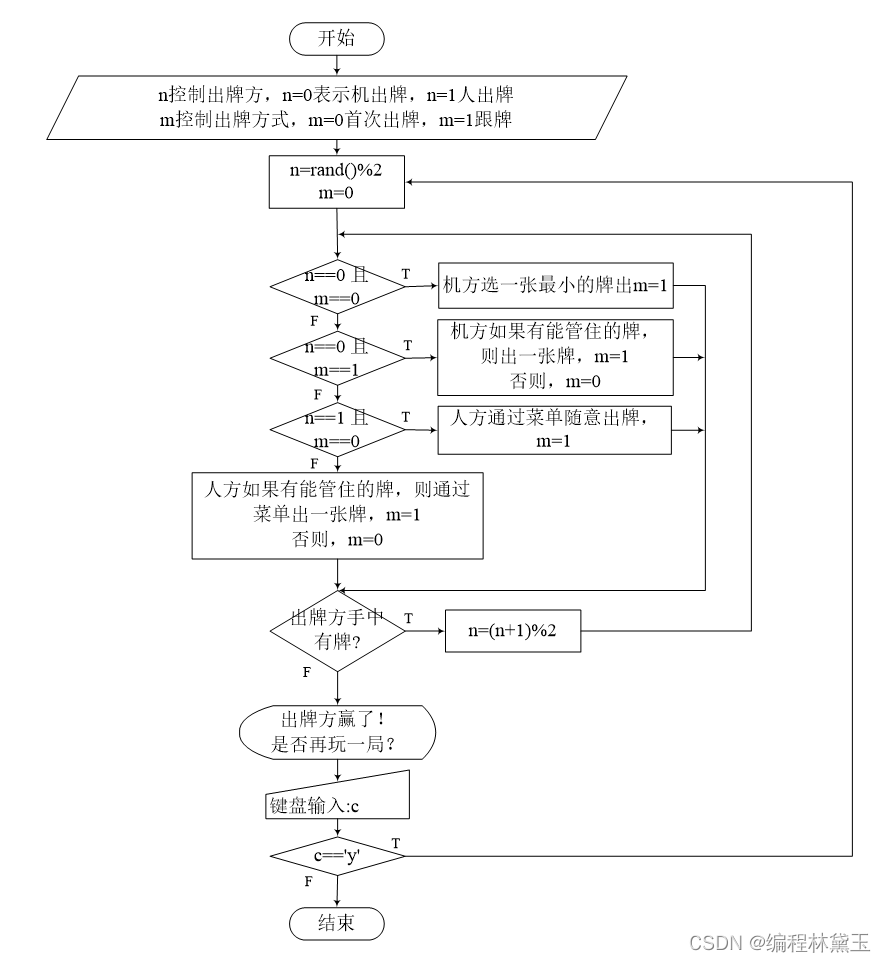
在目前实战挖掘src或者渗透测试中 大部分验证码是不可以啊绕过的 。想要通过爆破来进入后台页面 。 repeat模块测试后,验证码不可绕过,用captcha-killer能够识别验证码。 之后再进行弱口令爆破。
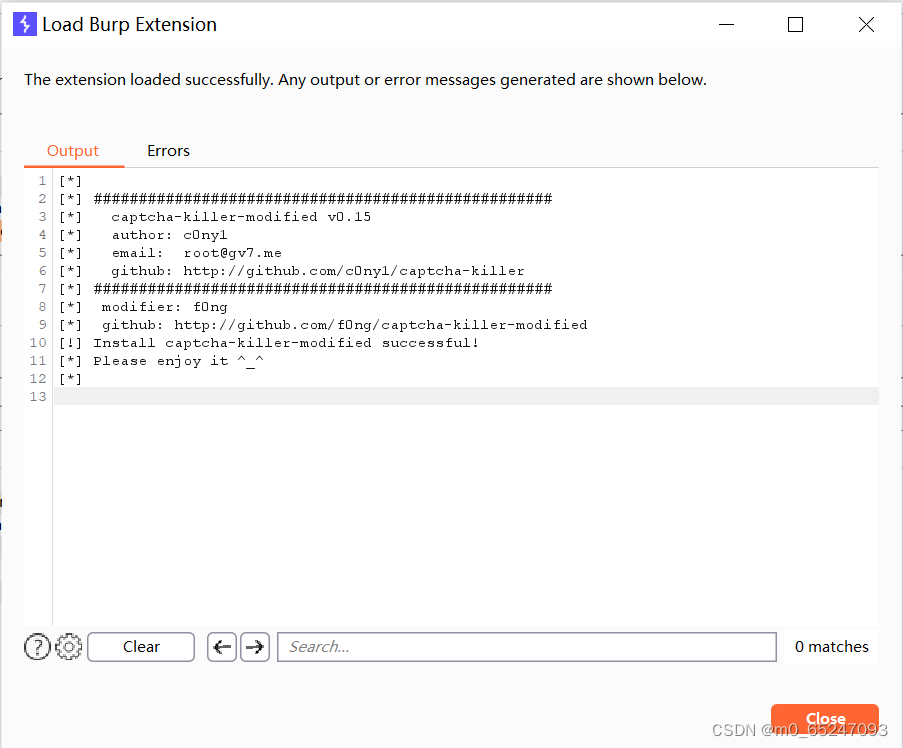
0x02 安装插件
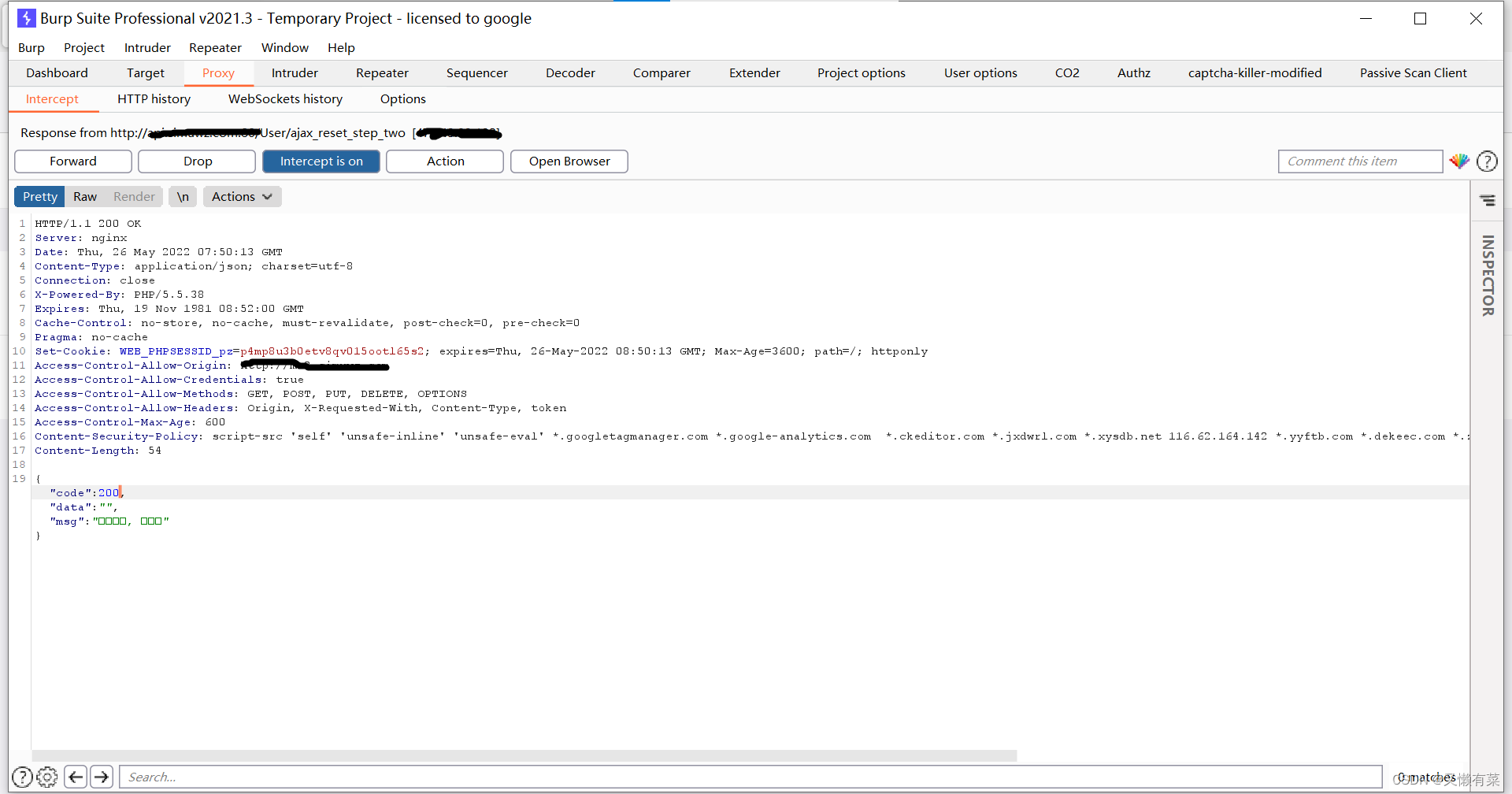
jar的安装跳过了 安装成功效果如下
实战第一步 抓包方式
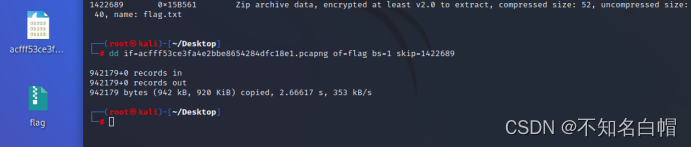
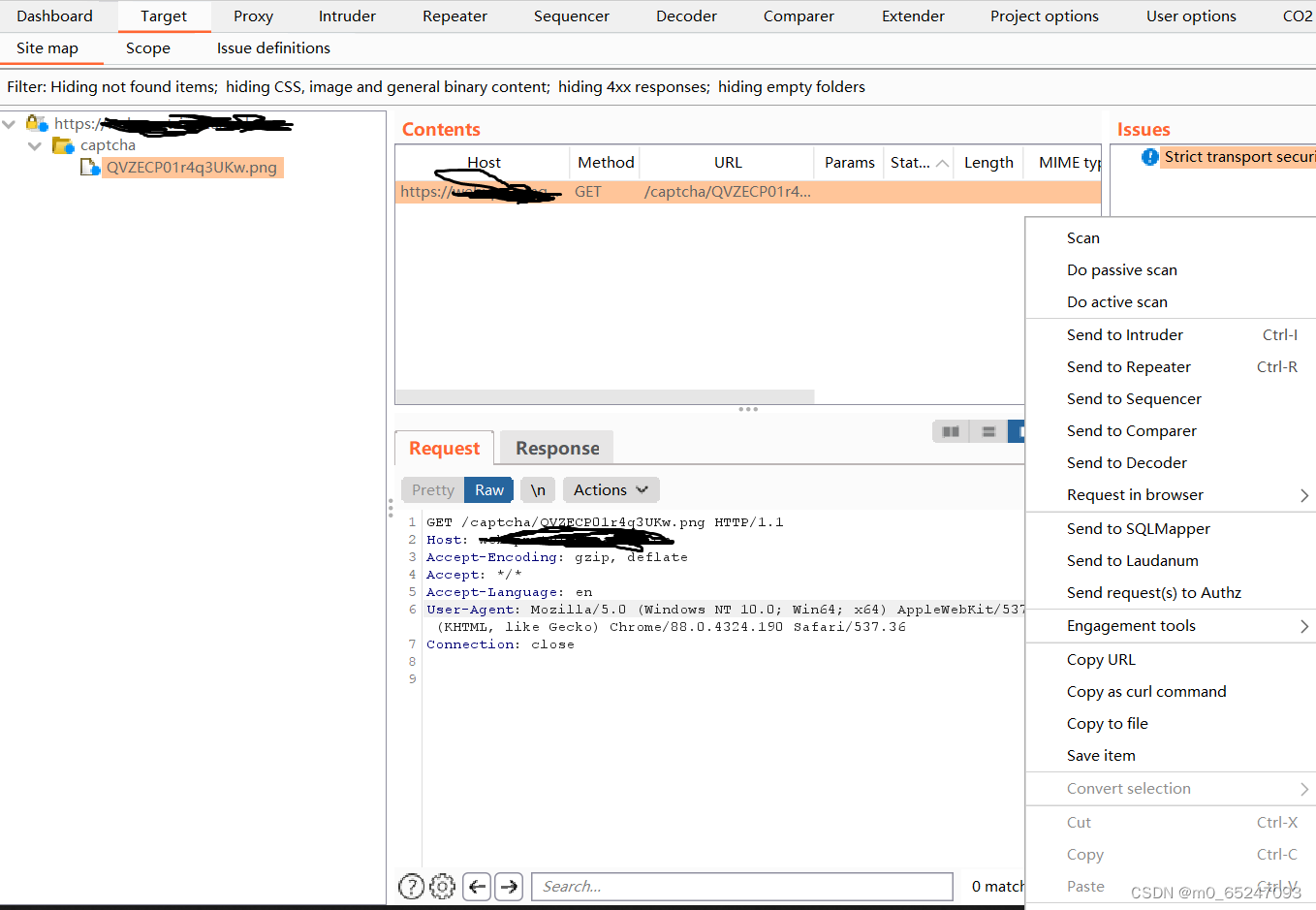
0x01 截取验证码包
这里截取之后不会再porxy中显示 但是history可以查看数据包
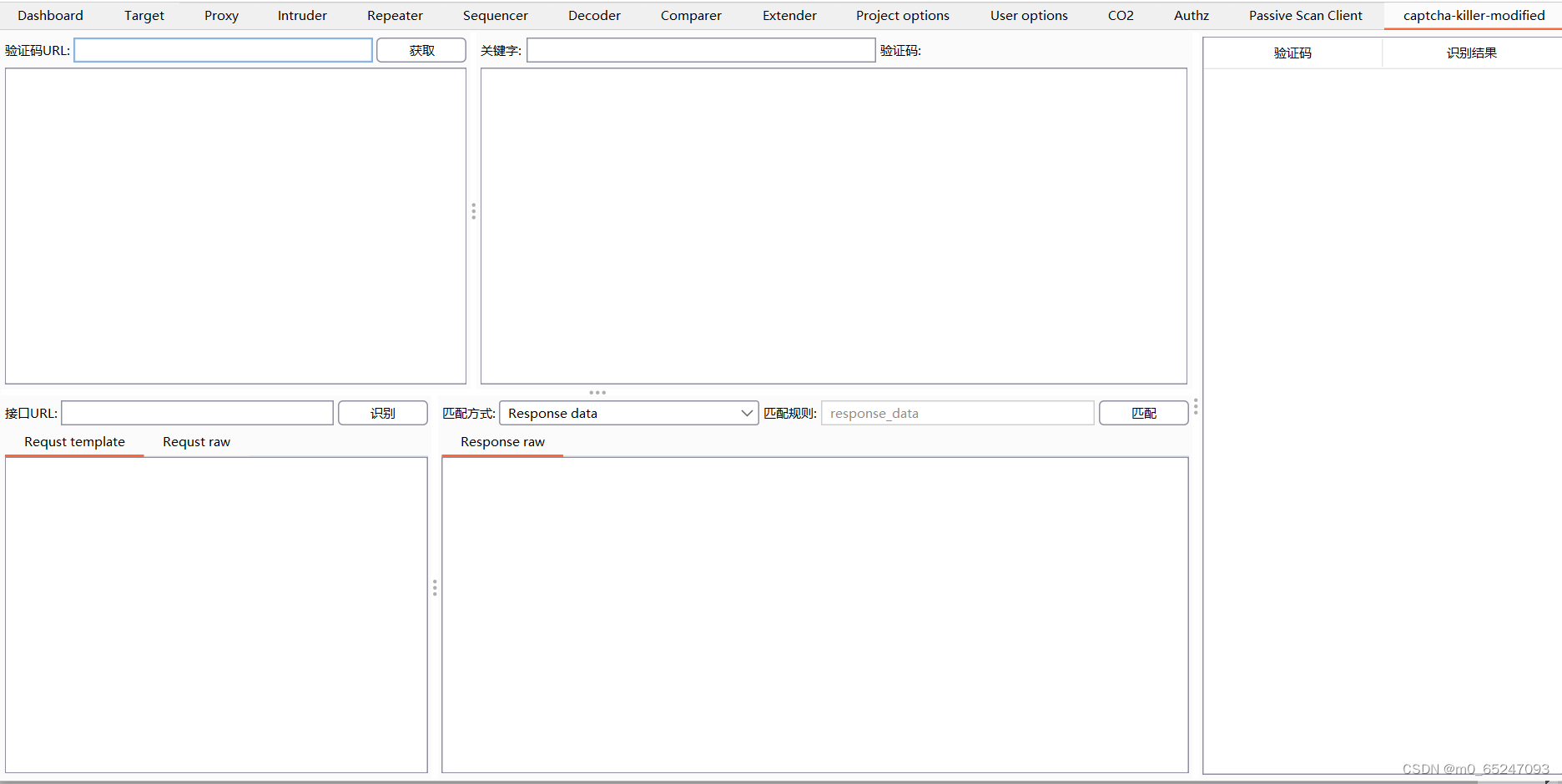
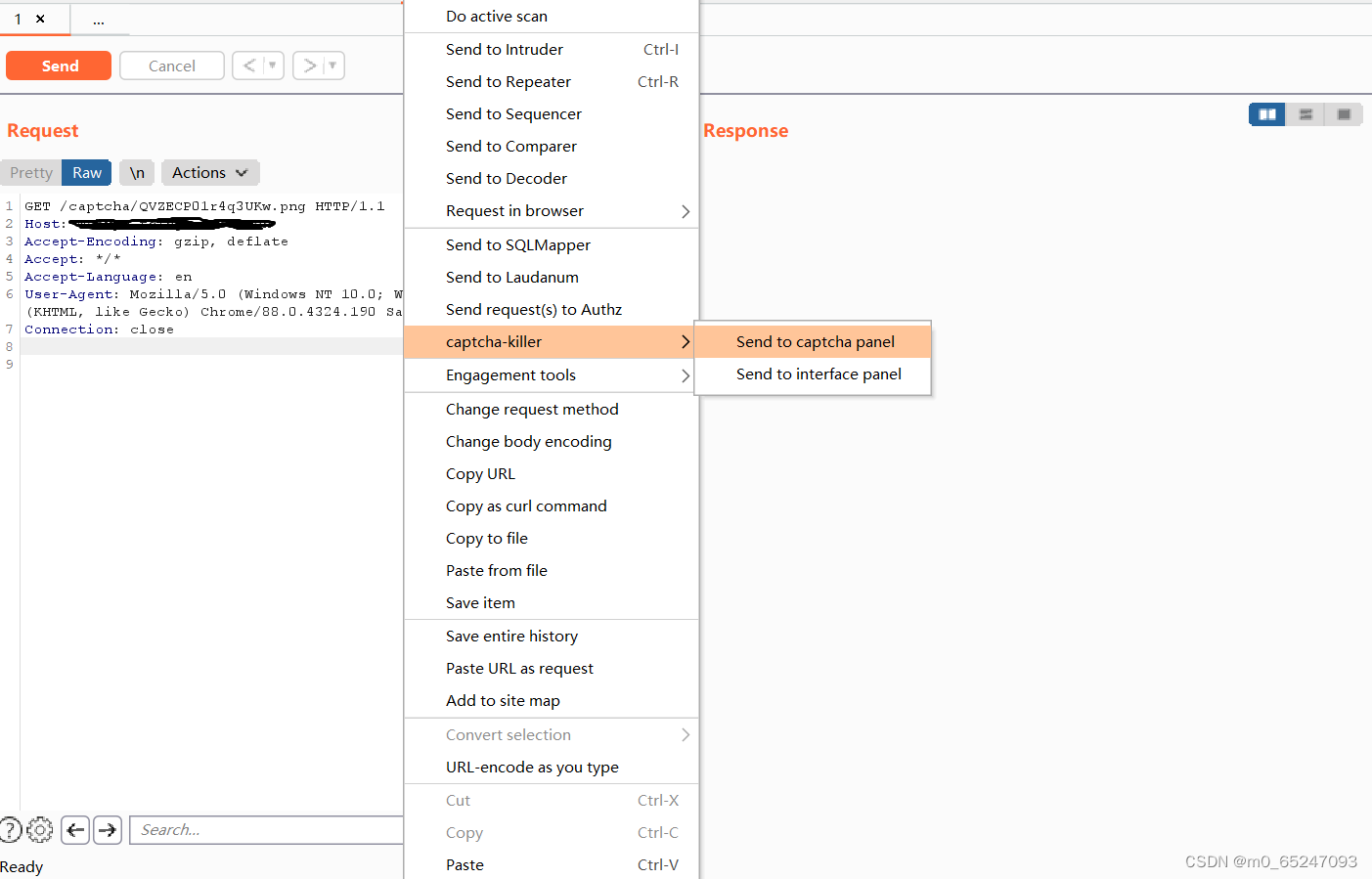
0x02 发送包
将验证码包发送到captcha-killer 如上图右键没有扩展插件
先将包发送到repeat中 再在repeat发送到capcha-killer模块
发送成功点击获取
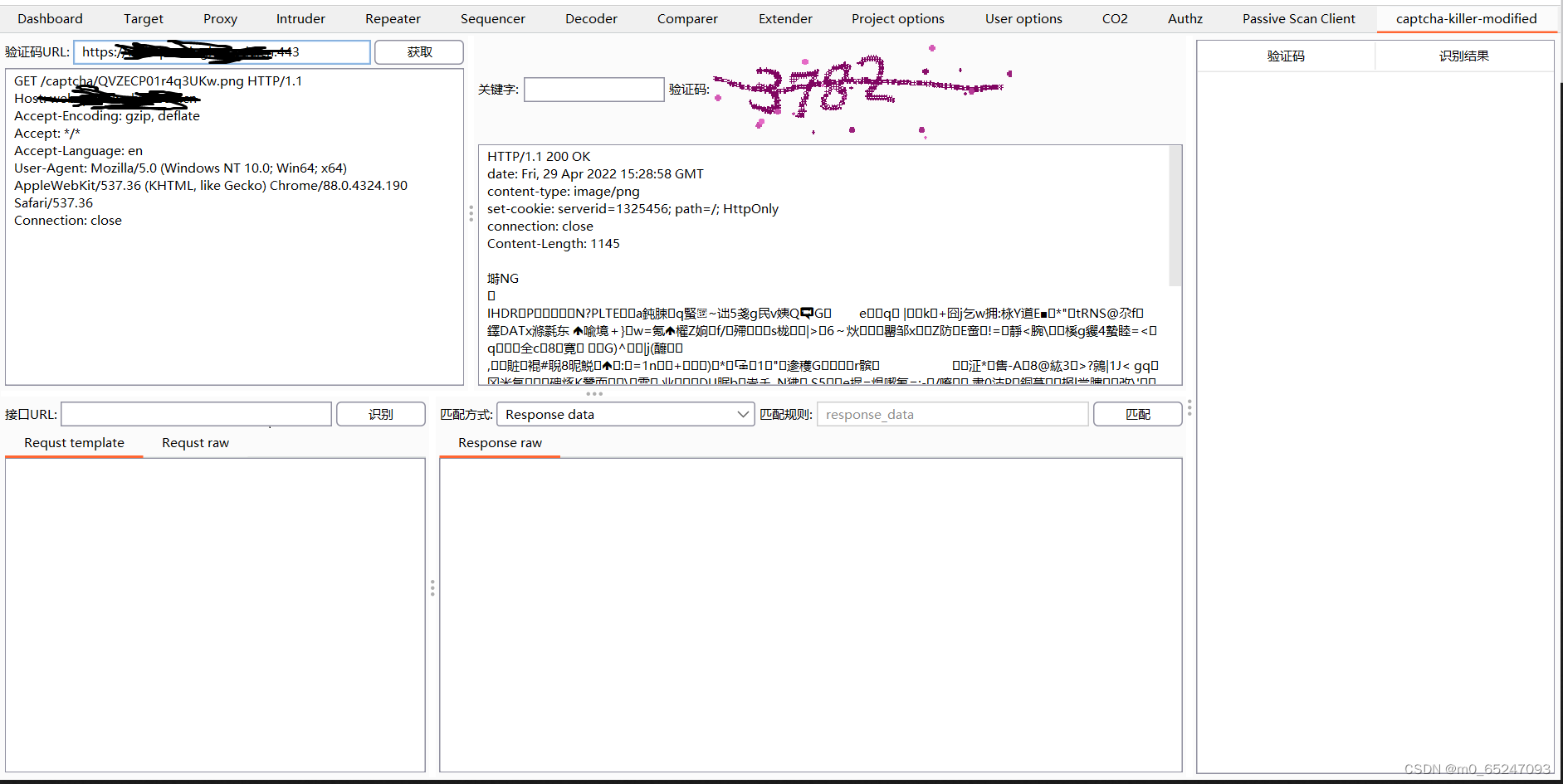
实战第二步 接口配置
0x01 接口的配置
这里接口选用云打码平台(错误率大概5%):
图片识别-打码平台-打码网站-识别验证码-图鉴网络科技有限公司 http://www.ttshitu.com/
http://www.ttshitu.com/
POST /predict HTTP/1.1
Host: api.ttshitu.com
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/80.0.3987.149 Safari/537.36
Accept: application/json;
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: Hm_lvt_d92eb5418ecf5150abbfe0e505020254=1585994993,1586144399; SESSION=5ebf9c31-a424-44f8-8188-62ca56de7bdf; Hm_lpvt_d92eb5418ecf5150abbfe0e505020254=1586144399
Connection: close
Content-Type: application/json;charset=UTF-8
Content-Length: 109
{"username":"账号","password":"密码","typeid":"3","image":"<@BASE64><@IMG_RAW></@IMG_RAW></@BASE64>"}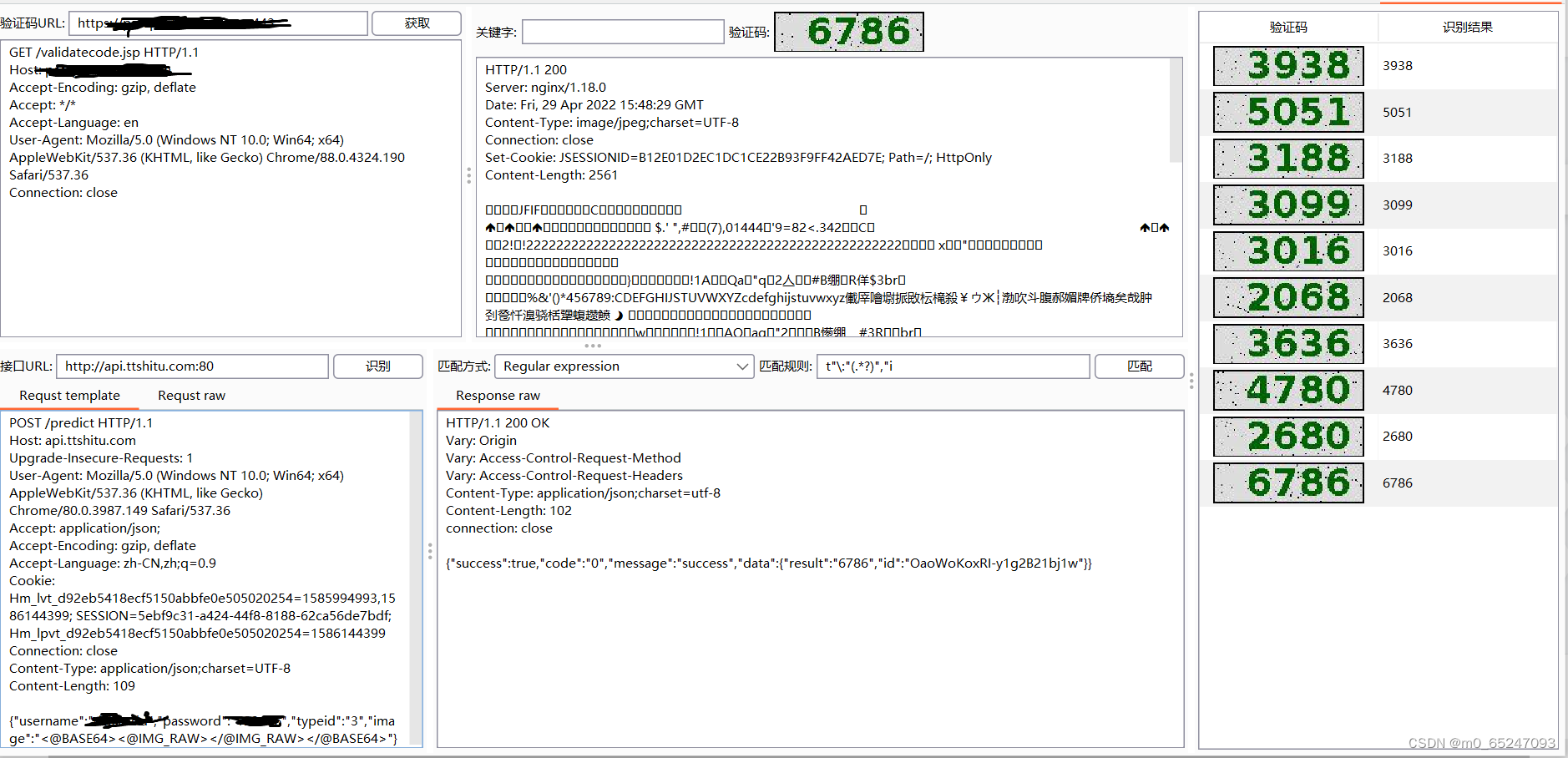
识别率如上图
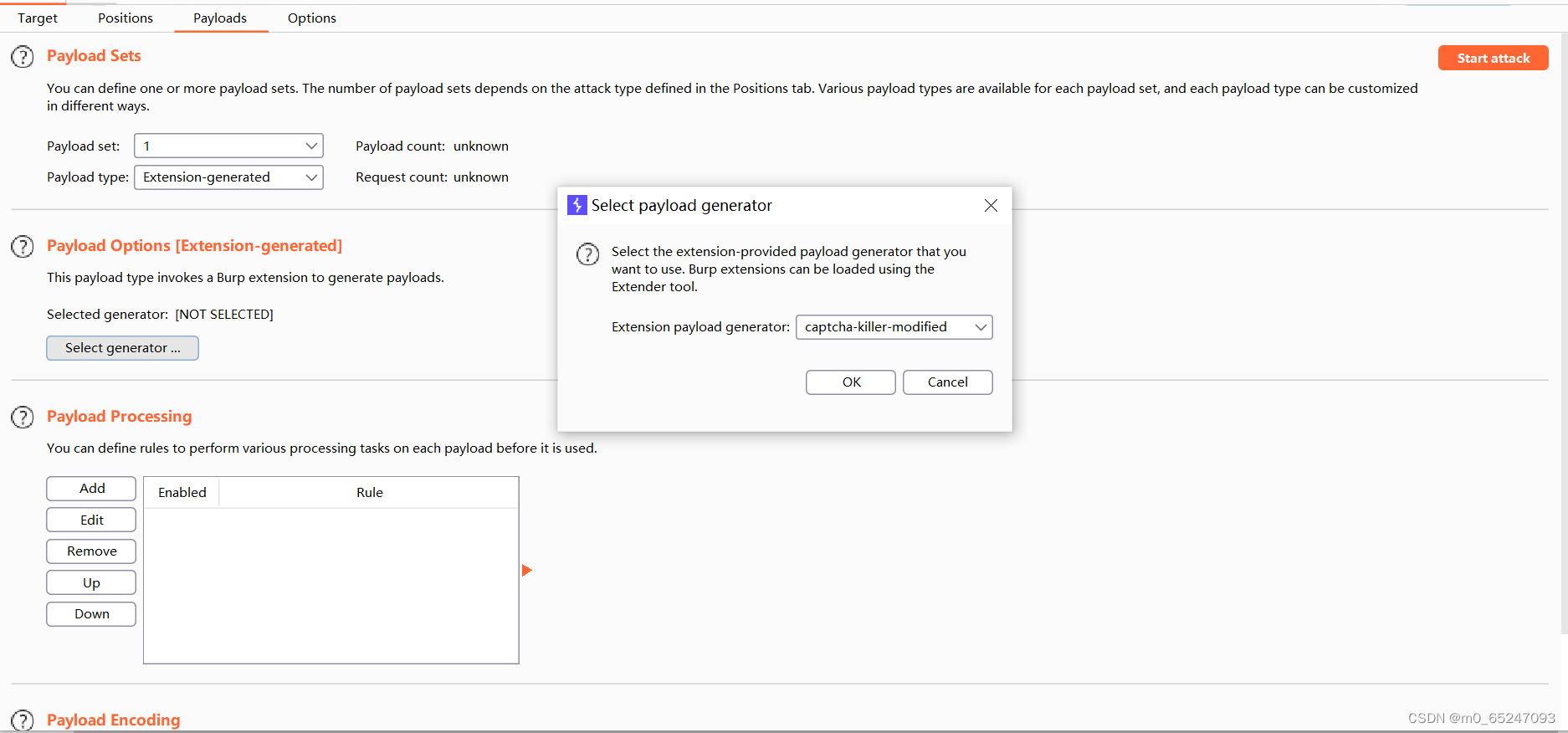
实战第三步 爆破模块的设置
0x01 为验证码设置变量
边栏推荐
猜你喜欢
随机推荐
JS several ways to judge whether an object is an array
【MySQL数据库的学习】
网络基础详解
Meituan dynamic thread pool practice ideas, open source
实验四 数组
网络基础之路由详解
Beautified table style
.Xmind文件如何上传金山文档共享在线编辑?
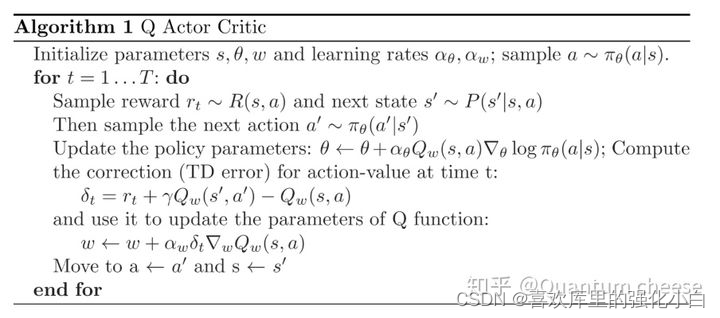
Reinforcement learning series (I): basic principles and concepts
1143_ SiCp learning notes_ Tree recursion
QT meta object qmetaobject indexofslot and other functions to obtain class methods attention
7-14 错误票据(PTA程序设计)
It's never too late to start. The tramp transformation programmer has an annual salary of more than 700000 yuan
DVWA (5th week)
Experiment 9 input and output stream (excerpt)
简单理解ES6的Promise
小程序web抓包-fiddler
[three paradigms of database] you can understand it at a glance
7-8 7104 Joseph problem (PTA program design)
Spot gold prices rose amid volatility, and the rise in U.S. prices is likely to become the key to the future