当前位置:网站首页>(POJ - 3579) median (two points)
(POJ - 3579) median (two points)
2022-07-06 16:09:00 【AC__ dream】
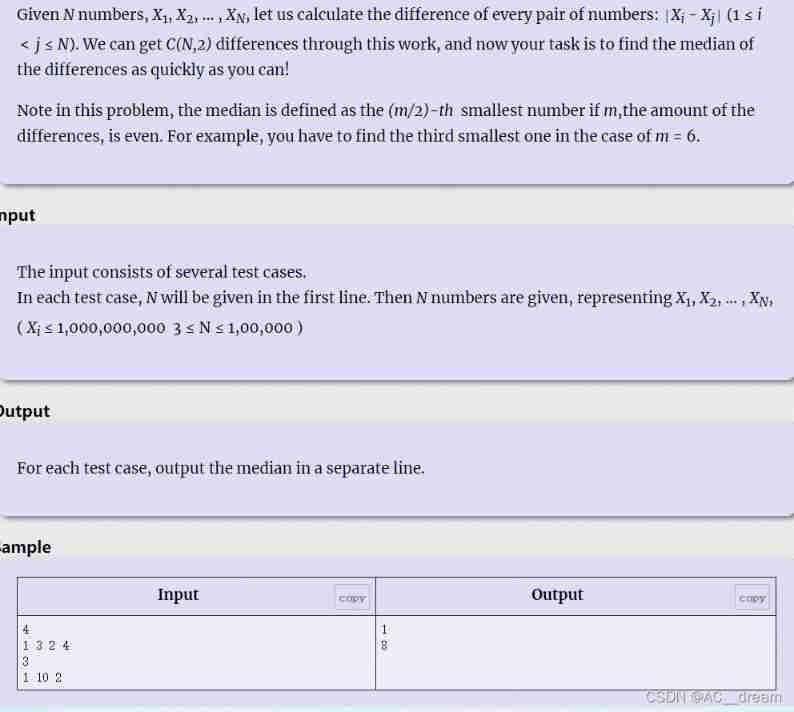
Chinese question meaning : Now there is N A mysterious number (A1,A2,A3….An), We need to get a password from this string of numbers .
The way to get the password is :
First calculate the difference between each number :|Ai-Aj|(1<=i<j<=N), In the end, you can get C Difference .
The final password is the median of these numbers .
If C It's even , It is stipulated that the median is C/2 Small difference .
This question and POJ-3579 The method of question is similar , We also solve it by dichotomy , For each number to be bisected x, We go through check Function to determine whether it is less than or equal to x How many pairs of distances are there , If the distance is less than or equal to x The number of pairs of is greater than half of the logarithm of the total , that r=x, conversely l=x+1, How should the specific dichotomy be carried out ? Let's start with a Sort the array from small to large , The dichotomy is found in ai On the right and the distance is less than or equal to x The number of , because aj-ai It is monotonically increasing , So this process is carried out through dichotomy , Traverse in turn ai, The distance is less than x Number to number , Two points are enough , There are quite a lot of details , See the code for details :
#include<cstdio>
#include<iostream>
#include<cstring>
#include<vector>
#include<algorithm>
#include<map>
#include<cmath>
#include<queue>
using namespace std;
const int N=1000003;
int a[N],n;
bool check(int x)// Find that the distance is less than or equal to x How many pairs are there , More than half the logarithm of all numbers returns true, Otherwise return to false
{
int cnt=0;
for(int i=1;i<=n;i++)
cnt+=upper_bound(a+1,a+n+1,a[i]+x)-a-i-1;
if(cnt>=((long long)n*(n-1)/2+1)/2) return true;
return false;
}
int main()
{
while(scanf("%d",&n)!=EOF)
{
for(int i=1;i<=n;i++)
scanf("%d",&a[i]);
sort(a+1,a+n+1);
int l=0,r=1000000000,mid;
while(l<r)
{
mid=l+r>>1;
if(check(mid)) r=mid;
else l=mid+1;
}
printf("%d\n",l);
}
return 0;
}边栏推荐
- China exterior wall cladding (EWC) market trend report, technical dynamic innovation and market forecast
- 栈的经典应用—括号匹配问题
- MySQL授予用户指定内容的操作权限
- Luogu P1102 A-B number pair (dichotomy, map, double pointer)
- 【练习-10】 Unread Messages(未读消息)
- What is the difficulty of programming?
- 渗透测试 2 --- XSS、CSRF、文件上传、文件包含、反序列化漏洞
- X-forwarded-for details, how to get the client IP
- 1605. Sum the feasible matrix for a given row and column
- 快速转 TypeScript 指南
猜你喜欢

1529. Minimum number of suffix flips

基于web的照片数码冲印网站
Configuration du cadre flask loguru log Library
C language is the watershed between low-level and high-level
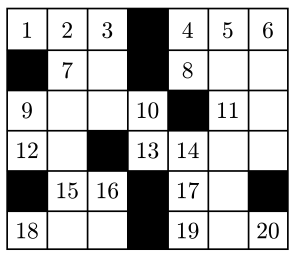
【练习-7】Crossword Answers
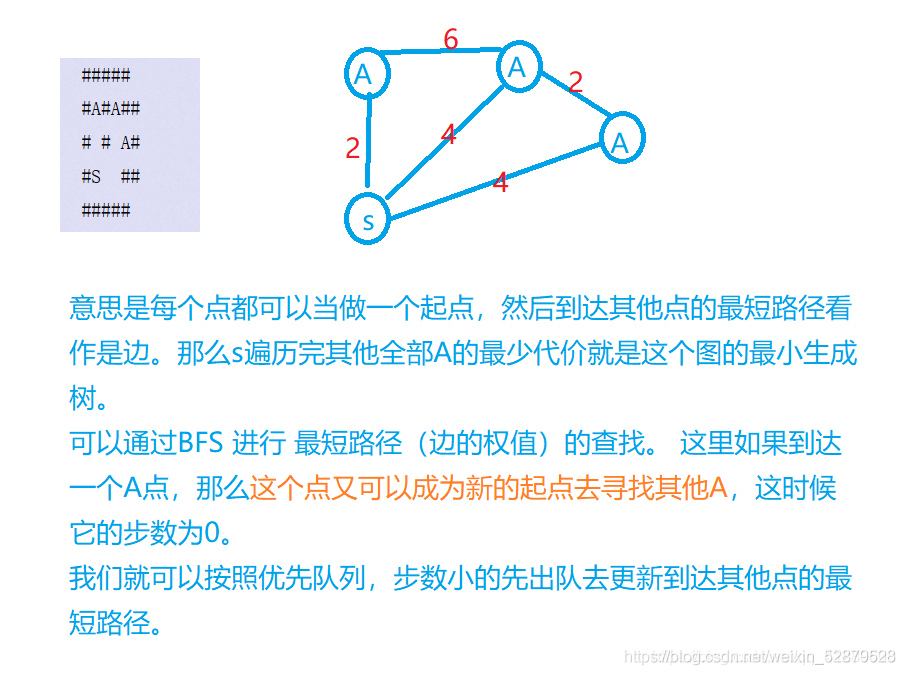
Borg maze (bfs+ minimum spanning tree) (problem solving report)
![mysql导入数据库报错 [Err] 1273 – Unknown collation: ‘utf8mb4_0900_ai_ci’](/img/e6/f4a696179282fe1f4193410c5a493a.png)
mysql导入数据库报错 [Err] 1273 – Unknown collation: ‘utf8mb4_0900_ai_ci’
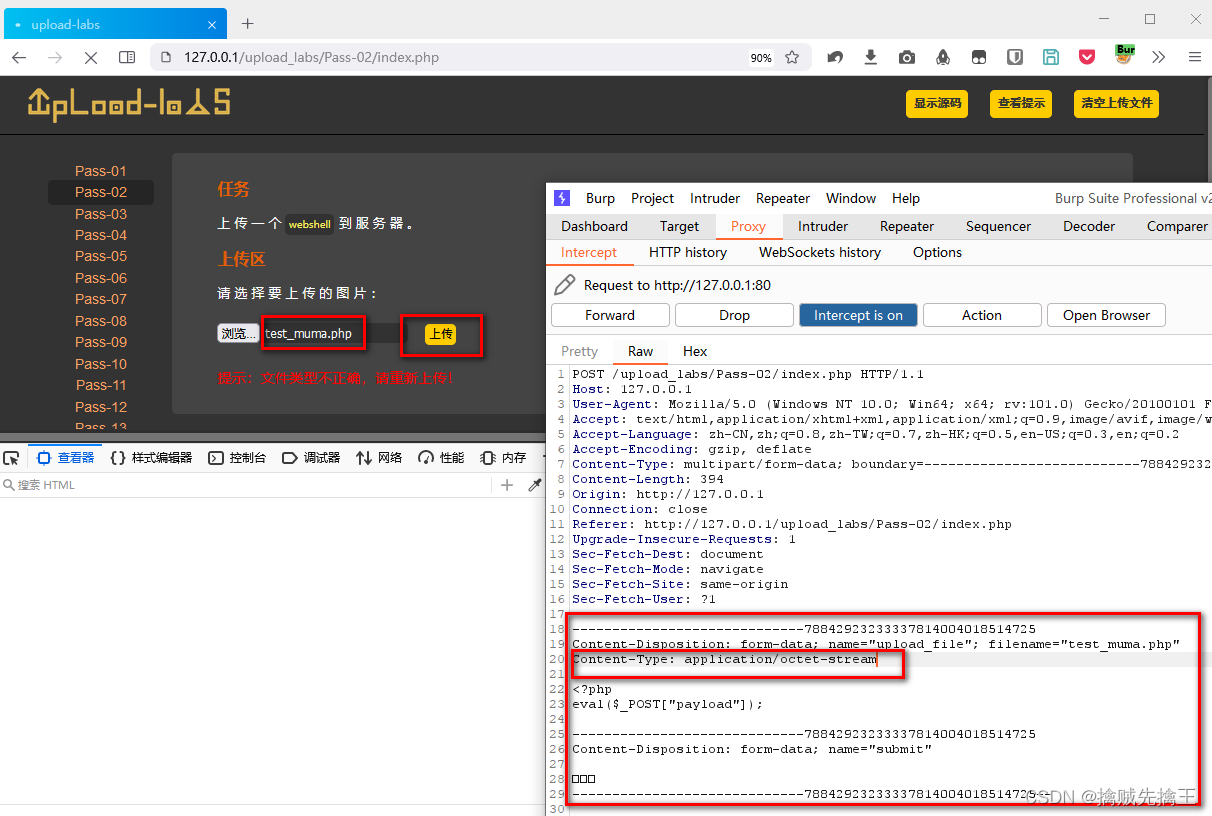
Penetration test 2 --- XSS, CSRF, file upload, file inclusion, deserialization vulnerability

Sword finger offer II 019 Delete at most one character to get a palindrome

信息安全-安全编排自动化与响应 (SOAR) 技术解析
随机推荐
Research Report of cylindrical grinder industry - market status analysis and development prospect forecast
【练习4-1】Cake Distribution(分配蛋糕)
Information security - Epic vulnerability log4j vulnerability mechanism and preventive measures
渗透测试 ( 4 ) --- Meterpreter 命令详解
D - function (HDU - 6546) girls' competition
Truck History
China potato slicer market trend report, technical dynamic innovation and market forecast
Nodejs crawler
Openwrt build Hello ipk
Auto.js入门
969. Pancake sorting
Opencv learning log 18 Canny operator
Suffix expression (greed + thinking)
(POJ - 3685) matrix (two sets and two parts)
Information security - threat detection - Flink broadcast stream broadcaststate dual stream merging application in filtering security logs
【练习-11】4 Values whose Sum is 0(和为0的4个值)
Nodejs+vue网上鲜花店销售信息系统express+mysql
信息安全-安全专业名称|CVE|RCE|POC|VUL|0DAY
Quick to typescript Guide
渗透测试 ( 7 ) --- 漏洞扫描工具 Nessus