当前位置:网站首页>"If life is just like the first sight" -- risc-v
"If life is just like the first sight" -- risc-v
2022-07-06 14:36:00 【Lntan0】
mention RISC-V, One word we have to mention is Instruction set architecture (ISA).
that , What is meant by “ISA”,ISA It can be called CPU Soul , Sometimes referred to as “ framework ” Otherwise known as “ Processor architecture ”.
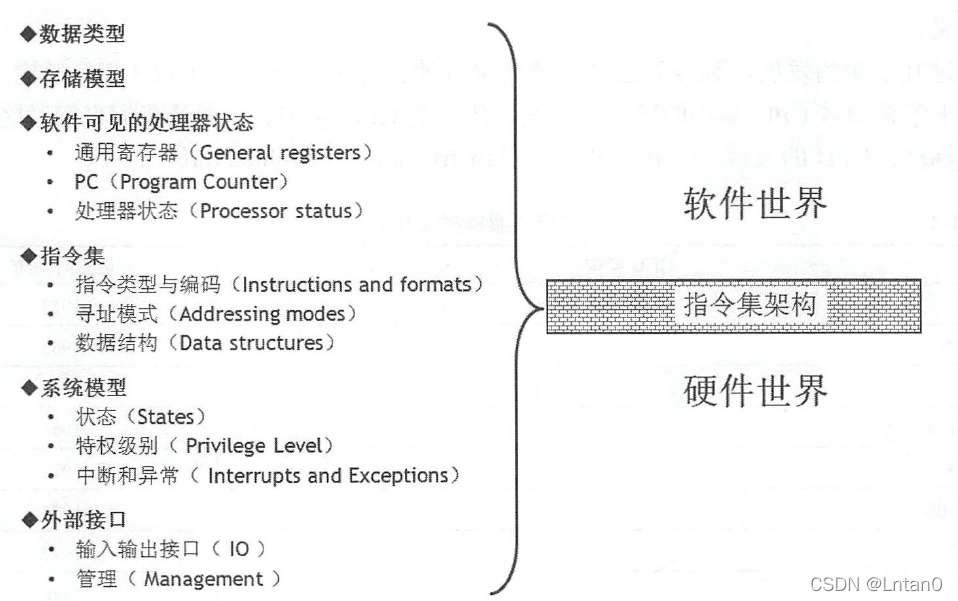
Above the ISA Made a detailed description , I won't repeat it here .
With instruction set architecture , Different processor hardware implementation schemes can be used to design processors with different performance . The specific hardware implementation scheme of the processor is called Microarchitecture (Microarchitecture).
RISC-V( English is read as “risk-five”), Is a new instruction set architecture .RISC-V The framework is mainly composed of several professors from the University of California, Berkeley 2010 The invention of . The reason why Berkeley developers invented a new instruction set architecture , Instead of using mature X86 perhaps arm framework , Because these architectures have been developed for many years , Become extremely complex and miscellaneous , And there are high patent and architecture licensing problems . therefore ,RISC-V Architecture is a new , Simple, open and free instruction set architecture .
Briefly introduce some CPU principle :
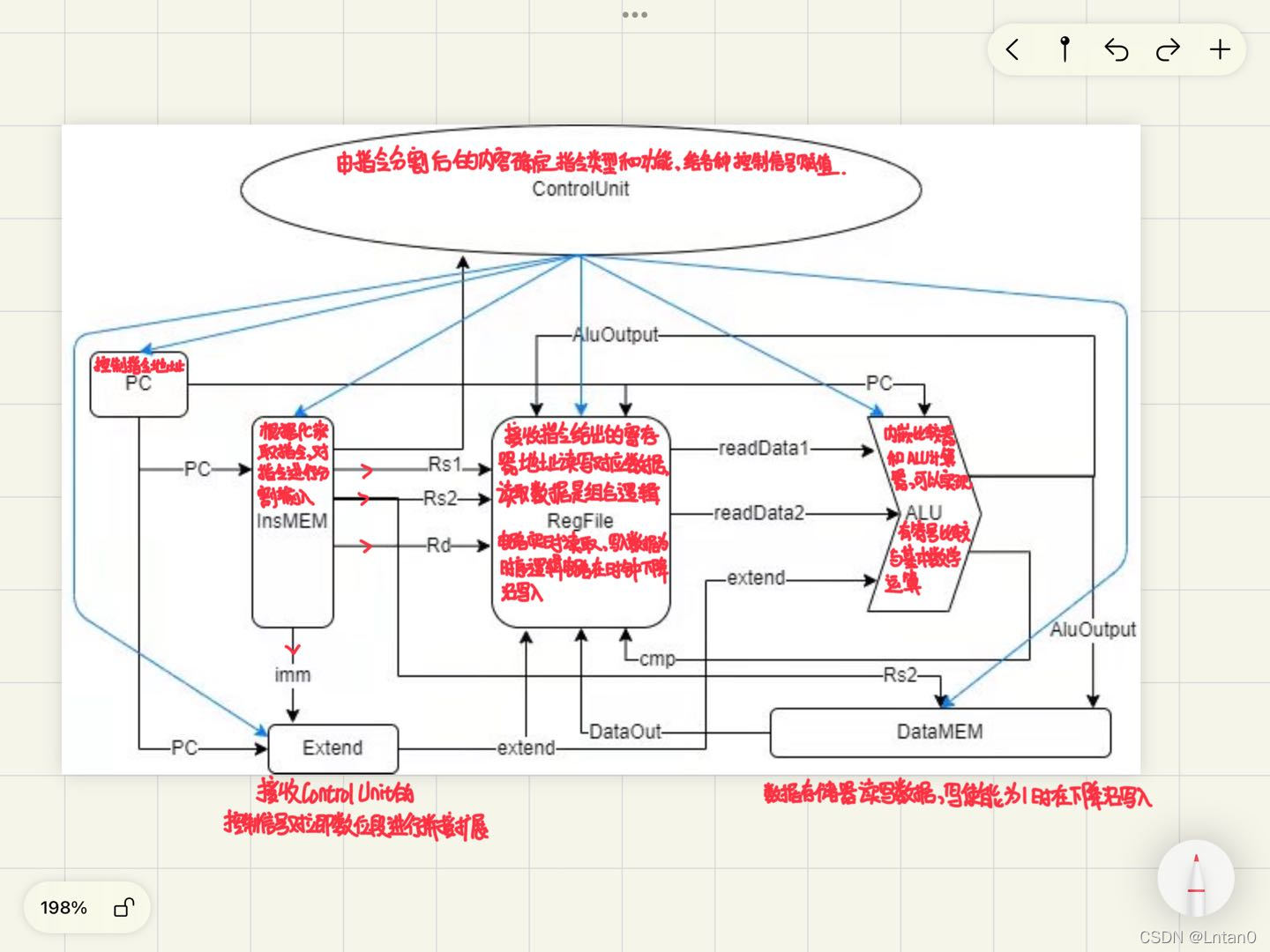
1. Classic five stage assembly line
Flow of an instruction : Fingering > decoding > perform > Visiting and depositing > Write back to
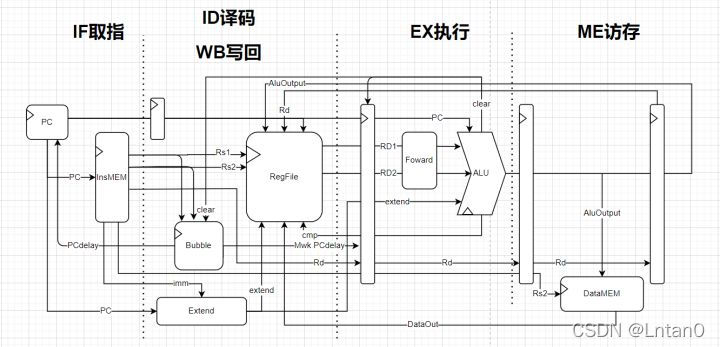
Simply mention a concept : Pipeline depth
Deeper and deeper assembly lines : Pursuing high performance
Shallower and shallower assembly lines : Pursue low power consumption
2.CPU Data access
About match
Competition questions : Based on hummingbird E203 RISC-V Intelligent recognition of kernel SoC Design and application system development
Content : Open source hummingbird based on xinlai Technology E203 Demo SoC(e203_hbirdv2) Expand , On the limited programmable logic platform, we build a..., which is oriented to the application field of intelligent recognition SoC, And then complete the actual application system development . It is required to build SoC In order to improve the overall performance of the system , The application system realized is innovative 、 Practicality and market application prospects .
Make complaints about it : I can't borrow & It's too persuasive to buy a board
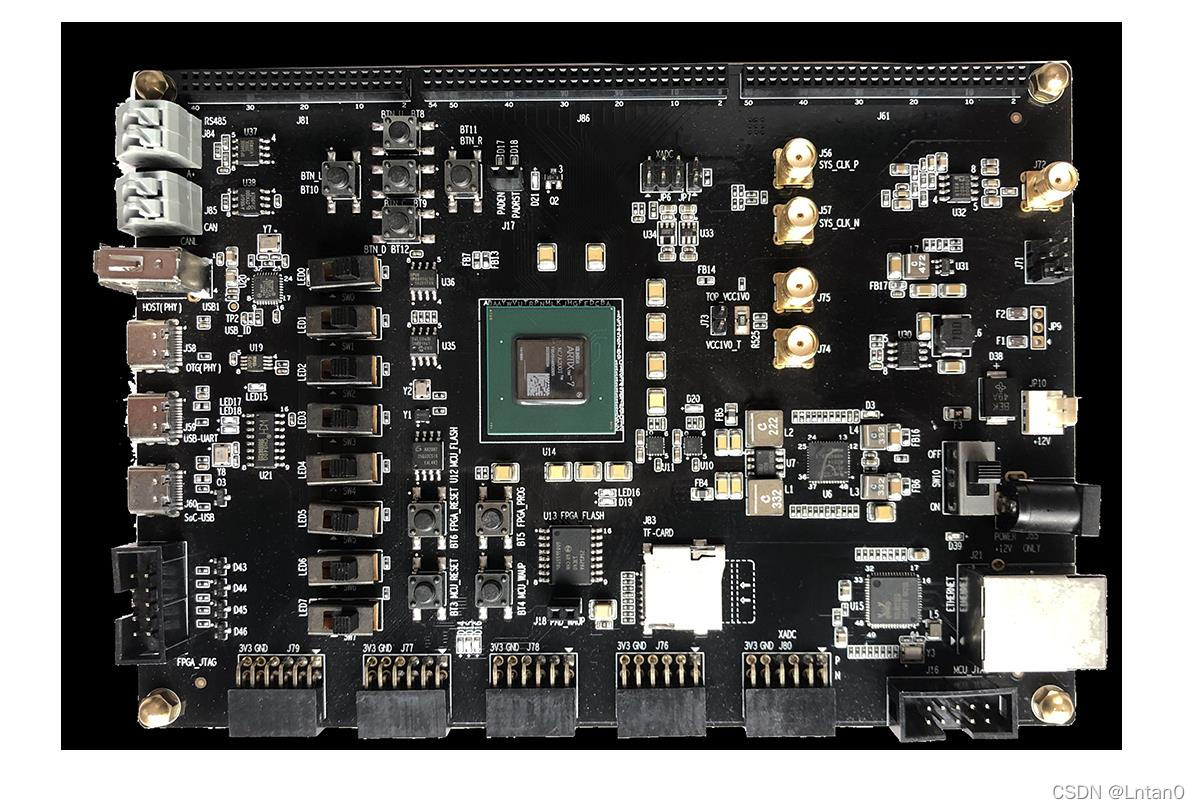
(Nuclei MCU200T, The price is 2499)
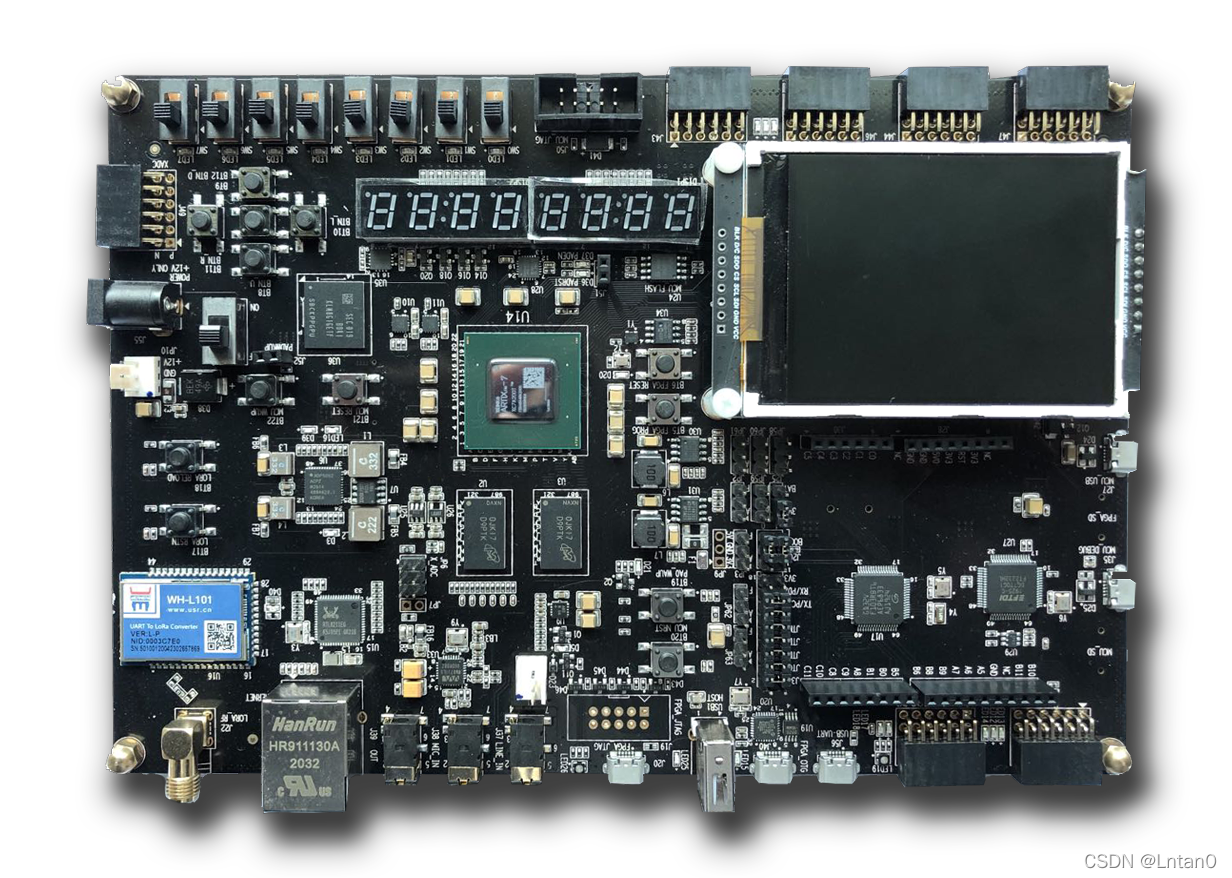
(Nuclei DDR200T, The price is 4999)
Finally, with the support of Wang Xuechang in the Laboratory , Bought a development board
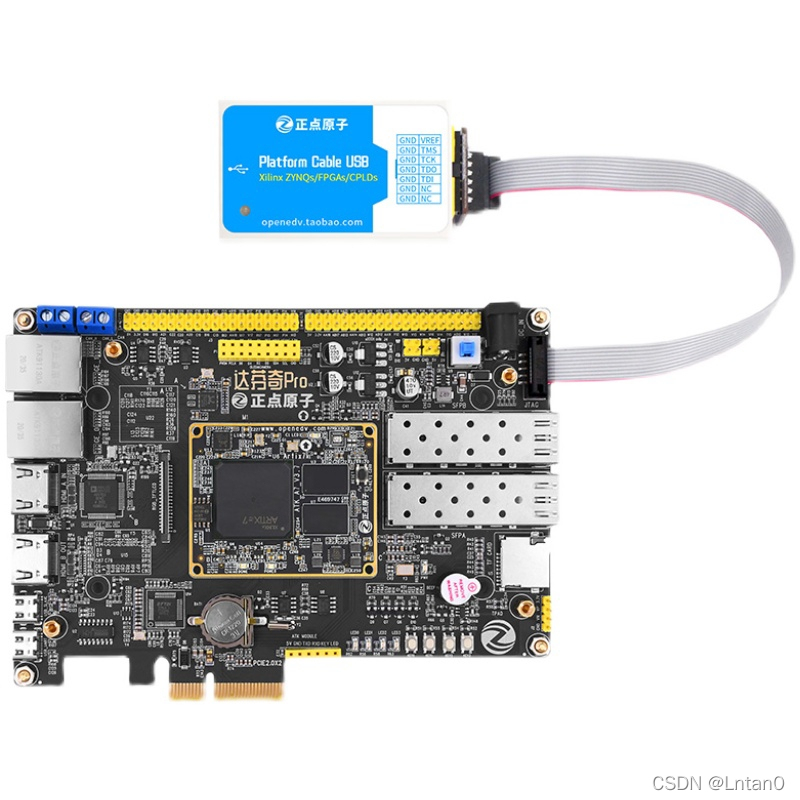
( Vinci pro 35T, The price is 1526)
Familiar with board , The biggest headache is still E203 soc Transplant the kernel to the board ( Online tutorials are almost 0)
The migration tutorial will be sent later
Sharing is only for learning and communication , I hope the big guys will not hesitate to give me advice 🥰
边栏推荐
- Ucos-iii learning records (11) - task management
- List and data frame of R language experiment III
- Intranet information collection of Intranet penetration (5)
- 【指针】求二维数组中最大元素的值
- Proceedingjoinpoint API use
- Intranet information collection of Intranet penetration (3)
- 【指针】数组逆序重新存放后并输出
- Record an edu, SQL injection practice
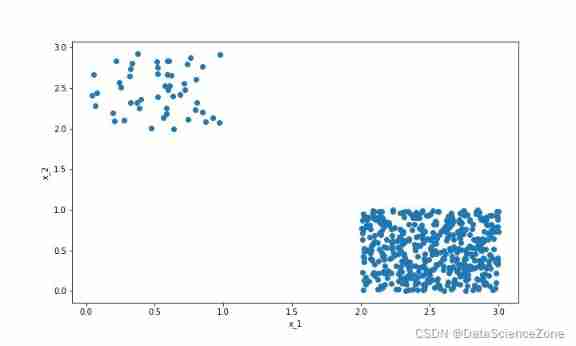
- Matplotlib绘图快速入门
- 数字电路基础(三)编码器和译码器
猜你喜欢

Only 40% of the articles are original? Here comes the modification method
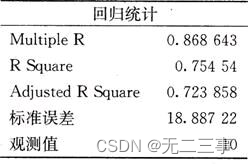
《统计学》第八版贾俊平第十一章一元线性回归知识点总结及课后习题答案
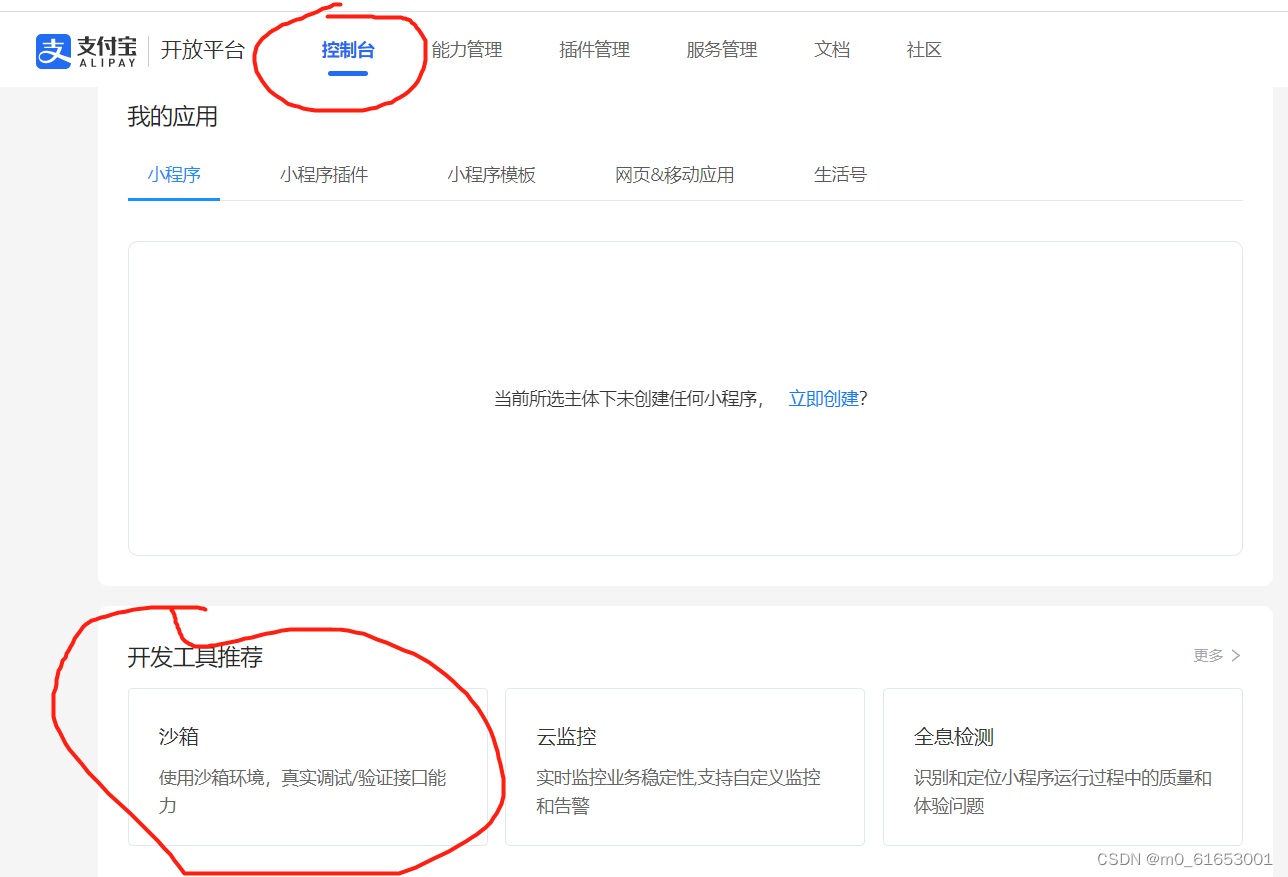
1.支付系统
Data mining - a discussion on sample imbalance in classification problems
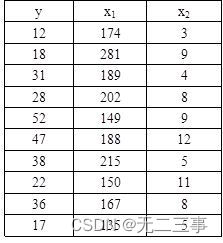
《统计学》第八版贾俊平第十二章多元线性回归知识点总结及课后习题答案
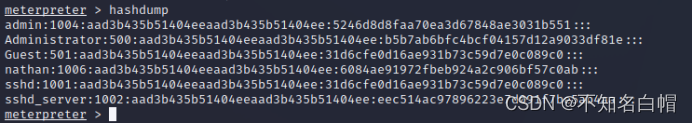
Intranet information collection of Intranet penetration (5)
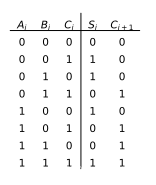
数字电路基础(五)算术运算电路

JVM memory model concept

Mysql的事务是什么?什么是脏读,什么是幻读?不可重复读?
《统计学》第八版贾俊平第三章课后习题及答案总结
随机推荐
函数:求1-1/2+1/3-1/4+1/5-1/6+1/7-…+1/n
刷视频的功夫,不如看看这些面试题你掌握了没有,慢慢积累月入过万不是梦。
Mysql的事务是什么?什么是脏读,什么是幻读?不可重复读?
图书管理系统
Low income from doing we media? 90% of people make mistakes in these three points
c语言学习总结(上)(更新中)
Function: find the maximum common divisor and the minimum common multiple of two positive numbers
Load balancing ribbon of microservices
captcha-killer验证码识别插件
《统计学》第八版贾俊平第九章分类数据分析知识点总结及课后习题答案
《统计学》第八版贾俊平第二章课后习题及答案总结
数字电路基础(四) 数据分配器、数据选择器和数值比较器
循环队列(C语言)
Intranet information collection of Intranet penetration (2)
【指针】求字符串的长度
《统计学》第八版贾俊平第一章课后习题及答案总结
Statistics 8th Edition Jia Junping Chapter 7 Summary of knowledge points and answers to exercises after class
Web vulnerability - File Inclusion Vulnerability of file operation
《统计学》第八版贾俊平第十三章时间序列分析和预测知识点总结及课后习题答案
Record an API interface SQL injection practice