当前位置:网站首页>Apache APIs IX has the risk of rewriting the x-real-ip header (cve-2022-24112)
Apache APIs IX has the risk of rewriting the x-real-ip header (cve-2022-24112)
2022-07-06 14:18:00 【ApacheAPISIX】
Problem description
stay Apache APISIX 2.12.1 In the previous version ( It doesn't contain 2.12.1 and 2.10.4), Enable Apache APISIX batch-requests After the plug-in , There will be rewriting X-REAL-IP header risk .
This risk leads to two problems :
- Through
batch-requestsPlug ins bypass Apache APISIX Data plane IP Limit . For example, bypass IP Black and white list restrictions . - If the user uses Apache APISIX The default configuration ( Enable Admin API , Use the default Admin Key And no additional management ports are assigned ), Attackers can get through
batch-requestsPlug in call Admin API .
Affects version
- Apache APISIX 1.3 ~ 2.12.1 Between all versions ( It doesn't contain 2.12.1 )
- Apache APISIX 2.10.0 ~ 2.10.4 LTS Between all versions ( It doesn't contain 2.10.4)
Solution
- The problem has been solved in 2.12.1 and 2.10.4 Resolved in version , Please update to the relevant version as soon as possible .
- In the affected Apache APISIX In the version , It can be done to
conf/config.yamlandconf/config-default.yamlFile explicitly commented outbatch-requests, And restart Apache APISIX This risk can be avoided .
Vulnerability Details
Vulnerability priority : high
Vulnerability disclosure time :2022 year 2 month 11 Japan
CVE Details :https://nvd.nist.gov/vuln/detail/CVE-2022-24112
Contributor profile
The vulnerability was discovered by Changting technology in Real World CTF Found in , And by the Sauercloud Report to Apache Software foundation . Thank you for Apache APISIX Community contribution .

边栏推荐
- 7-11 mechanic mustadio (PTA program design)
- 链队实现(C语言)
- Matlab opens M file garbled solution
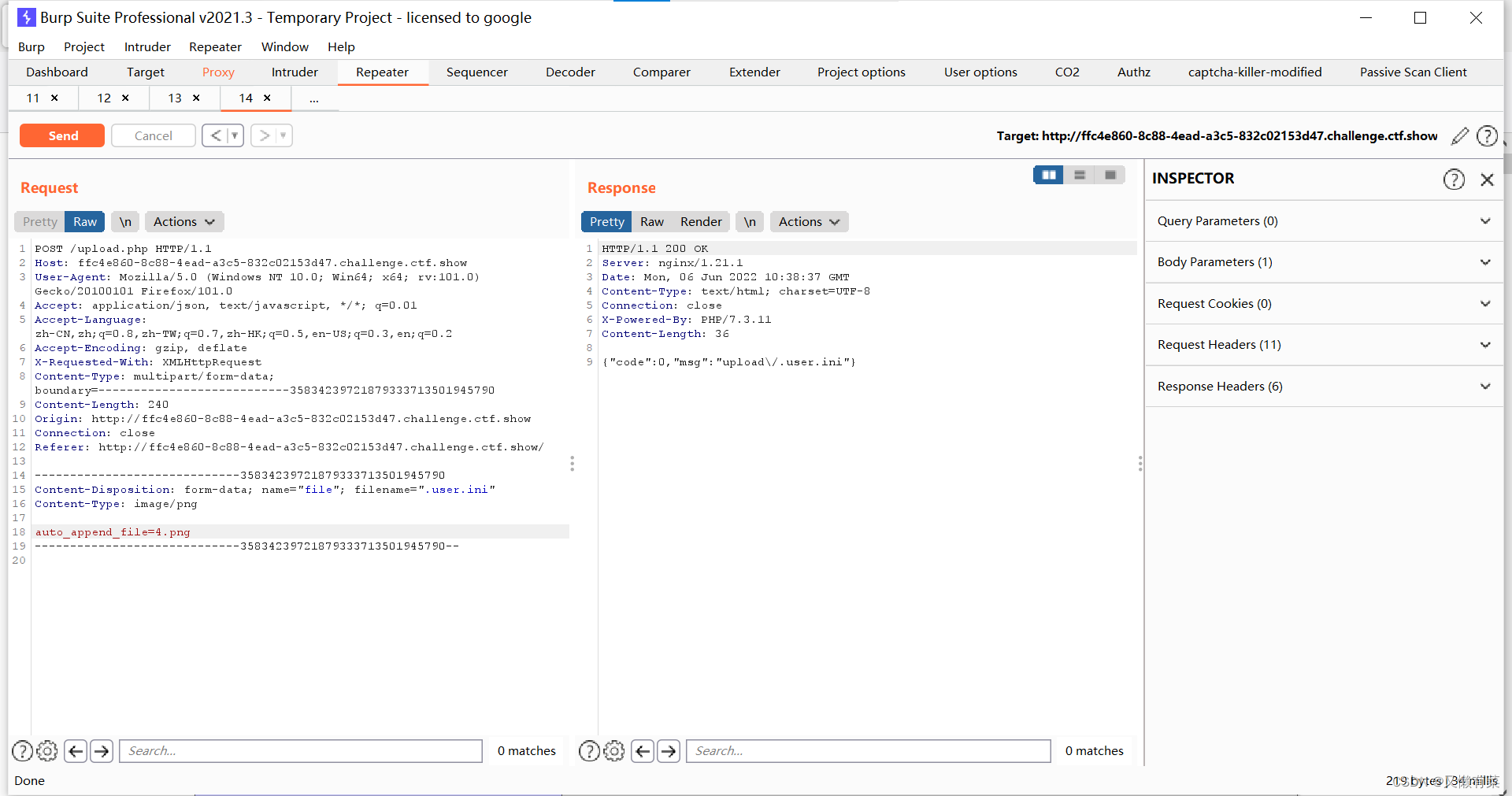
- Xray and burp linkage mining
- Hackmyvm target series (4) -vulny
- XSS之冷门事件
- Intensive literature reading series (I): Courier routing and assignment for food delivery service using reinforcement learning
- 搭建域环境(win)
- 7-3 construction hash table (PTA program design)
- [experiment index of educator database]
猜你喜欢
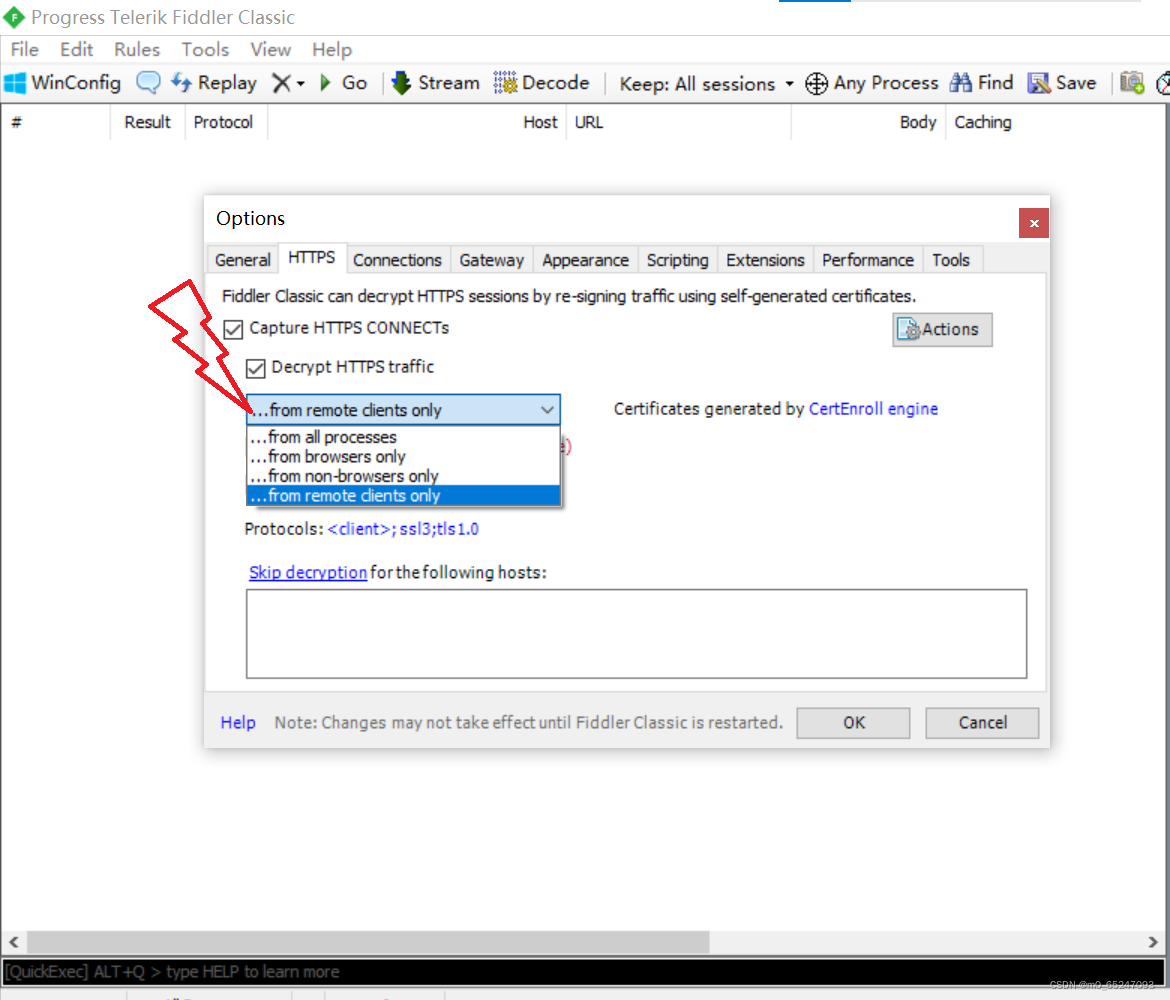
Applet Web Capture -fiddler
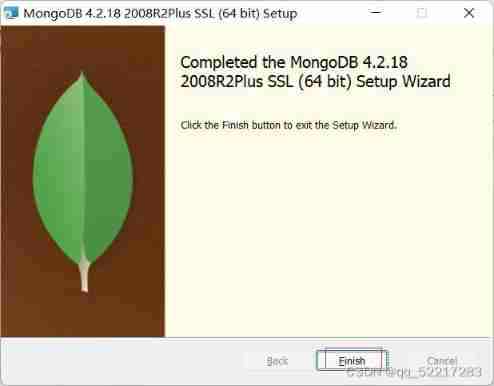
Windows platform mongodb database installation
中间件漏洞复现—apache
![[dark horse morning post] Shanghai Municipal Bureau of supervision responded that Zhong Xue had a high fever and did not melt; Michael admitted that two batches of pure milk were unqualified; Wechat i](/img/d7/4671b5a74317a8f87ffd36be2b34e1.jpg)
[dark horse morning post] Shanghai Municipal Bureau of supervision responded that Zhong Xue had a high fever and did not melt; Michael admitted that two batches of pure milk were unqualified; Wechat i
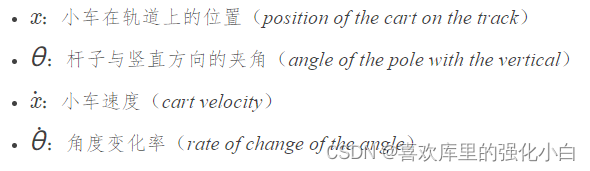
Strengthen basic learning records

Low income from doing we media? 90% of people make mistakes in these three points
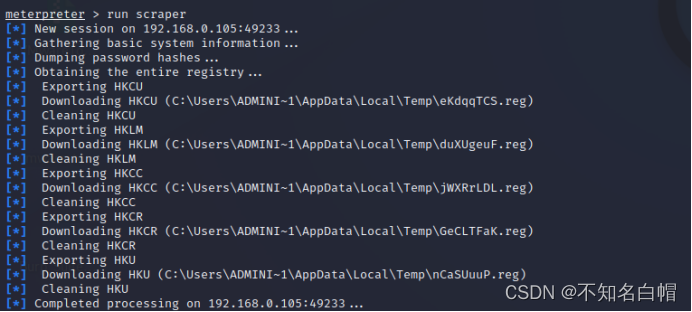
内网渗透之内网信息收集(四)
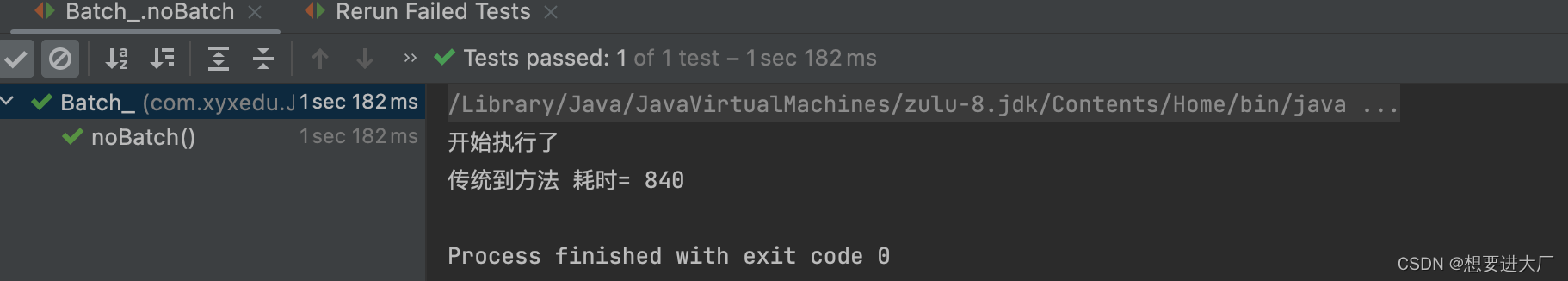
JDBC事务、批处理以及连接池(超详细)

附加简化版示例数据库到SqlServer数据库实例中
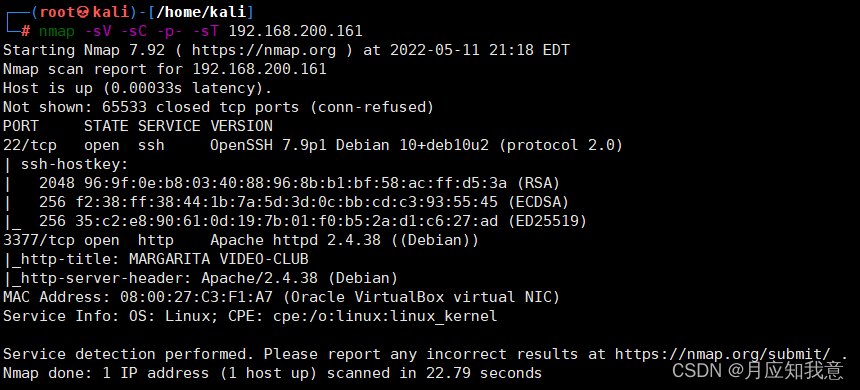
HackMyvm靶机系列(6)-videoclub
随机推荐
[VMware abnormal problems] problem analysis & Solutions
Hackmyvm target series (2) -warrior
The most popular colloquial system explains the base of numbers
Hackmyvm target series (3) -visions
Mixlab unbounded community white paper officially released
内网渗透之内网信息收集(一)
An unhandled exception occurred when C connected to SQL Server: system Argumentexception: "keyword not supported:" integrated
XSS之冷门事件
【MySQL数据库的学习】
Low income from doing we media? 90% of people make mistakes in these three points
7-7 7003 combination lock (PTA program design)
HackMyvm靶机系列(5)-warez
JDBC看这篇就够了
HackMyvm靶机系列(3)-visions
Windows platform mongodb database installation
What language should I learn from zero foundation. Suggestions
Detailed explanation of network foundation routing
Xray and Burp linked Mining
记一次api接口SQL注入实战
Strengthen basic learning records