当前位置:网站首页>First batch selected! Tencent security tianyufeng control has obtained the business security capability certification of the ICT Institute
First batch selected! Tencent security tianyufeng control has obtained the business security capability certification of the ICT Institute
2022-07-06 21:18:00 【Tencent security】
In recent days, , Sponsored by China information and Communication Research Institute “2022 The first business and application security development forum ” Held in Beijing . At the meeting , The Chinese Academy of communications and communications announced 2022 Trusted security assessment results , Tencent security privacy protection decision system “ Credit version ” and “ Transaction anti fraud version ” Both were selected , Become the first batch to pass the China Academy of communications “ Business security capability requirements ” Certified products .
Receive visitors + Integration of risk control
Escort the steady development of credit business
For a long time , The financial industry is based on serving the real economy , It is the key force to promote the development of digital economy . With the deepening of the digital transformation of the financial industry , Big retail + Digitalization has become a significant feature of the deepening development of financial institutions in the future . Financial institutions are using artificial intelligence 、 While big data and other new generation information technologies promote the process of digital transformation , It will also face some security problems in the process of boundary expansion .
Especially in the financial industry, the credit business is expanding , In the face of the rapid changes in the external market and the rigid requirements of the bank's internal stable operation , The decision-making mechanisms of emerging Internet digital services and traditional credit services need to be deeply integrated .
In this context , Tencent security encapsulates customer acquisition and risk control capabilities , Made a set of “ Receive visitors + Risk control ” Integrated retail credit solutions , Focus on the credit business scenario , For pre loan 、 In credit 、 Requirements for risk assessment in the post loan scenario , Combining face recognition 、 Identity Authentication 、 Fraud identification and other technologies and schemes , Risk control of retail credit , It mainly covers feature management 、 Policy configuration 、 List management 、 Release management 、 Test management 、 Real time decision making 、 Decision result output and other functions . meanwhile , Tencent security also has a large number of industry experts , It can help financial institutions plan top-level businesses , Provide financial level business security support .
Take a city commercial bank as an example , Due to the single customer channel , Lack of digital platform , Tencent security helped the bank build a digital platform for retail credit 、 Big data risk control system and advanced channel customer acquisition system , And combined with Tencent's internal experts to jointly operate , The bank has accumulated users since its launch 170 ten thousand , The number of transactions 40 ten thousand , And already 150 Billion balance .
at present , This scheme has been applied in the Bank of China 、 China Everbright Bank 、 China Minsheng Bank 、 Huaxia bank 、 Jilin Rural Credit 、 Jining bank 、 Bank of Qingdao and other banks have successfully landed , It has served hundreds of millions of users , Escort hundreds of billions of credit funds .
Focus on transaction risk control
Help improve the quality and efficiency of enterprise fraud management
In the era of digital economy , Industrial digitalization and digital industrialization are constantly deepening and evolving , The types and scenarios of business security risks are becoming more and more complex , The anti fraud work in the financial market is also more difficult .
meanwhile ,《 Data security law 》 and 《 Personal information protection law 》 The promulgation of also put forward higher requirements for the anti fraud work of financial institutions . Financial science and technology development plan 2.0 It is highlighted in , We should promote the orderly sharing and comprehensive application of data on the premise of ensuring security and privacy , Fully activate the potential of data elements , Effectively improve the quality and efficiency of financial services .
So , Tencent security is based on long-term accumulated experience in service output of financial service infrastructure , Integrated a set of transaction anti fraud solutions , By sorting out the key information in the transaction process , Provide perception from risk 、 distinguish 、 The risk control capability of the full trading link released by the decision , Combine the global device fingerprint 、 Terminal risk control engine 、 User digital identity 、 Technology such as risk intelligence core , Build a complete closed loop of risk prevention and control , It can provide customers with millisecond level real-time risk control decision-making ability , Meet the corresponding requirements of financial institutions for transaction anti fraud , Provide more perfect business management and business analysis services for retail financial business .
In the practice of cooperating with a state-owned bank , This solution will eventually help the bank build a pre event 、 In the matter 、 Post event multi-dimensional risk model , Cumulative monitoring of high-risk transactions 31.9 Billion pen , Block suspicious transaction amount 118.27 One hundred million yuan .
It is worth mentioning that , In addition to federal Learning Technology , Tencent security self-developed SKAnets Small sample learning method , It can help financial institutions quickly grasp the learning tasks and the characteristics of new fraud patterns in the risk iteration period , Build new model samples even if the samples are very limited , Effectively help financial institutions identify fraud , Quantify risk .
Li Chao, an expert on Tencent security financial risk control, said , Risk control is not only the ballast of financial institutions , It is also the engine of financial institutions . This time, we received the recognition of the China Academy of communications technology on the security capability requirements of Tencent's security business , It further strengthened Tencent's determination to safeguard the safety and beauty of digitalization .
future , Tencent security will rely on 20 Years of safety protection experience , Continue to build consultation covering scenes 、 Solution 、 Risk control services 、 Risk control system and other multi-dimensional product matrix , Build a leading privacy computing decision-making system , Escort the digital transformation of all walks of life .
边栏推荐
- 缓存更新策略概览(Caching Strategies Overview)
- In JS, string and array are converted to each other (II) -- the method of converting array into string
- JS学习笔记-OO创建怀疑的对象
- Tips for web development: skillfully use ThreadLocal to avoid layer by layer value transmission
- JS traversal array and string
- Nodejs教程之让我们用 typescript 创建你的第一个 expressjs 应用程序
- Mtcnn face detection
- Study notes of grain Mall - phase I: Project Introduction
- Opencv learning example code 3.2.3 image binarization
- 3D人脸重建:从基础知识到识别/重建方法!
猜你喜欢
对话阿里巴巴副总裁贾扬清:追求大模型,并不是一件坏事

967- letter combination of telephone number
嵌入式开发的7大原罪
Seven original sins of embedded development
爱可可AI前沿推介(7.6)
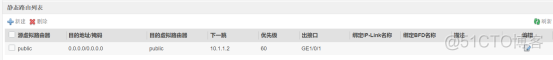
防火墙基础之外网服务器区部署和双机热备
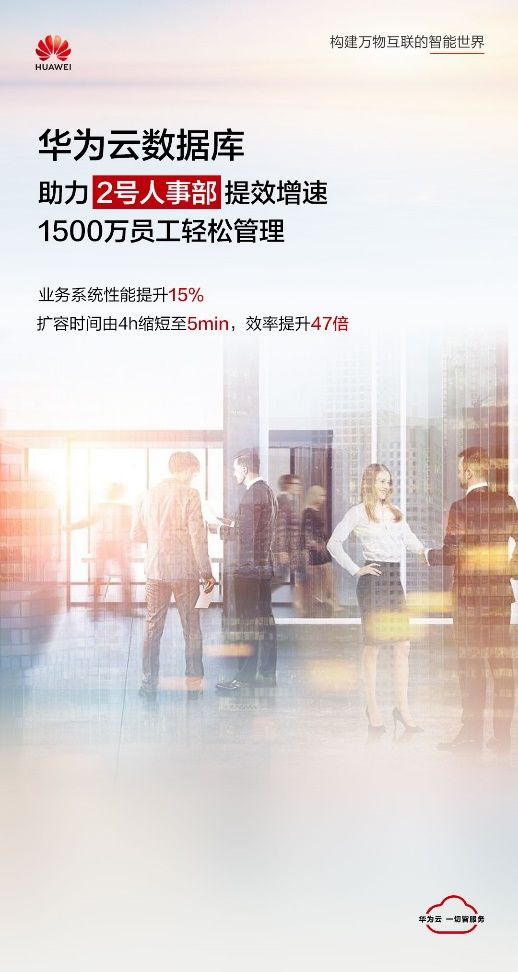
15million employees are easy to manage, and the cloud native database gaussdb makes HR office more efficient
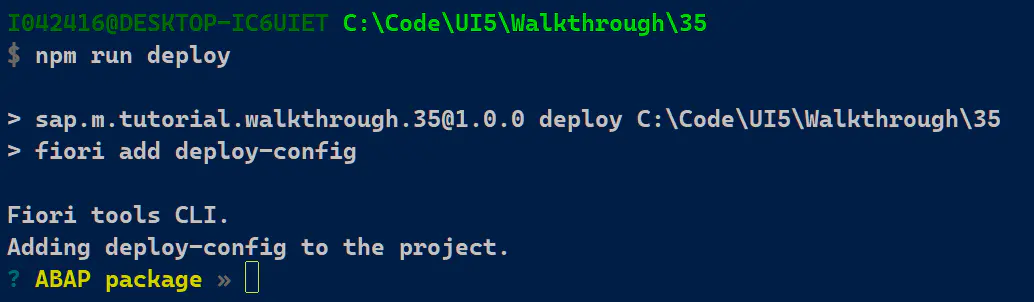
SAP Fiori应用索引大全工具和 SAP Fiori Tools 的使用介绍
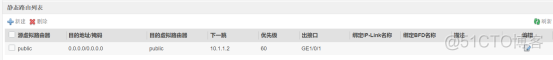
Deployment of external server area and dual machine hot standby of firewall Foundation
The most comprehensive new database in the whole network, multidimensional table platform inventory note, flowus, airtable, seatable, Vig table Vika, flying Book Multidimensional table, heipayun, Zhix
随机推荐
FZU 1686 龙之谜 重复覆盖
R语言可视化两个以上的分类(类别)变量之间的关系、使用vcd包中的Mosaic函数创建马赛克图( Mosaic plots)、分别可视化两个、三个、四个分类变量的关系的马赛克图
Swagger UI教程 API 文档神器
【论文解读】用于白内障分级/分类的机器学习技术
Select data Column subset in table R [duplicate] - select subset of columns in data table R [duplicate]
Nodejs教程之让我们用 typescript 创建你的第一个 expressjs 应用程序
Fastjson parses JSON strings (deserialized to list, map)
KDD 2022 | realize unified conversational recommendation through knowledge enhanced prompt learning
请问sql group by 语句问题
PHP saves session data to MySQL database
Seven original sins of embedded development
2022菲尔兹奖揭晓!首位韩裔许埈珥上榜,四位80后得奖,乌克兰女数学家成史上唯二获奖女性
Acdreamoj1110 (multiple backpacks)
Nodejs教程之Expressjs一篇文章快速入门
js中,字符串和数组互转(二)——数组转为字符串的方法
【力扣刷题】一维动态规划记录(53零钱兑换、300最长递增子序列、53最大子数组和)
[interpretation of the paper] machine learning technology for Cataract Classification / classification
[sliding window] group B of the 9th Landbridge cup provincial tournament: log statistics
What are RDB and AOF
ICML 2022 | Flowformer: 任务通用的线性复杂度Transformer