当前位置:网站首页>Improve application security through nonce field of play integrity API
Improve application security through nonce field of play integrity API
2022-07-07 11:49:00 【Google developers 】

author / Oscar Rodriguez, Developer Relations Engineer
We recently released Play Integrity API, Hope to help developers protect their applications and games , Protect them from fraudulent interactions that may pose risks ( Such as spoofing and unauthorized access ) Hazards of , Enable you to take appropriate measures to prevent attacks and reduce abuse .
Play Integrity API
https://developer.android.google.cn/google/play/integrity
In addition to application integrity 、 Useful signals related to equipment integrity and licensing information ,Play Integrity API It also provides a simple but very practical function , namely "nonce". If used properly , Developers can further strengthen Play Integrity API Existing protective measures , And reduce the risk of specific types of attacks , For example, intermediaries (PITM) Tamper attack and replay attack .
In this article , We will introduce in depth what is nonce、 How it works , And how to use it nonce Field to further protect your applications and games .
What is? nonce?
In cryptography and security engineering ,nonce (number once) It is a number that can only be used once in secure communication .nonce A wide range of uses , Like authentication 、 Data encryption and hash processing .
stay Play Integrity API in ,nonce You are calling API Opacity set before integrity check Base64 Code binary blob, And return the original sample through the signed response . Create and verify according to nonce The way , You can use it to further enhance Play Integrity API Existing protective measures , And mitigate specific types of attacks , For example, intermediaries (PITM) Tamper attack and replay attack .
Except return as is in the signed response nonce,Play Integrity API It won't be right nonce Any processing of actual data , So you can set any value , As long as it is an effective Base64 value . in other words , To digitally sign the response ,nonce The value will be sent to Google The server , So please do not nonce Set to any type of personally identifiable information (PII), For example, user name 、 Phone or email address .
Set up nonce
Set your app to use Play Integrity API after , You can use setNonce() Method , Or its appropriate variant settings nonce, These variants apply to API Of Kotlin、Java、Unity and Native edition .
Set your app to use Play Integrity API
https://developer.android.google.cn/google/play/integrity/setup
Set up nonce
https://developer.android.google.cn/google/play/integrity/verdict#request
Kotlin:
val nonce: String = ...
// establish manager Example
val integrityManager =
IntegrityManagerFactory.create(applicationContext)
// adopt nonce Get integrity token
val integrityTokenResponse: Task<IntegrityTokenResponse> =
integrityManager.requestIntegrityToken(
IntegrityTokenRequest.builder()
.setNonce(nonce) // Set up nonce
.build())Java:
String nonce = ...
// establish manager Example
IntegrityManager integrityManager =
IntegrityManagerFactory.create(getApplicationContext());
// adopt nonce Get integrity token
Task<IntegrityTokenResponse> integrityTokenResponse =
integrityManager
.requestIntegrityToken(
IntegrityTokenRequest.builder()
.setNonce(nonce) // Set up nonce
.build());Unity:
string nonce = ...
// establish manager Example
var integrityManager = new IntegrityManager();
// adopt nonce Get integrity token
var tokenRequest = new IntegrityTokenRequest(nonce);
var requestIntegrityTokenOperation =
integrityManager.RequestIntegrityToken(tokenRequest);Native:
// establish IntegrityTokenRequest object
const char* nonce = ...
IntegrityTokenRequest* request;
IntegrityTokenRequest_create(&request);
IntegrityTokenRequest_setNonce(request, nonce); // Set up nonce
IntegrityTokenResponse* response;
IntegrityErrorCode error_code =
IntegrityManager_requestIntegrityToken(request, &response);verification nonce
Play Integrity API Response of with JSON Network token (JWT) Form return of , Its load is plain text JSON, The format is as follows :
{
requestDetails: { ... }
appIntegrity: { ... }
deviceIntegrity: { ... }
accountDetails: { ... }
}JSON Network token (JWT)
https://jwt.io/
Pure text JSON
https://developer.android.google.cn/google/play/integrity/verdict#returned-payload-format
You can go to requestDetails Structure nonce, The format is as follows :
requestDetails: {
requestPackageName: "...",
nonce: "...",
timestampMillis: ...
}nonce The value of the field should be the same as you called API The passed values match exactly . Besides , because nonce Values in the Play Integrity API In the encrypted signature response , After receiving the response, it cannot be changed . Through these properties , You can use nonce Further protect your application .
Protect important operations
Imagine this scene , An attacker is trying to maliciously falsely report players' scores to the game server . In this case , The equipment and application are complete , However, the attacker can still view and modify the communication data flow with the game server through the proxy server or virtual private network , So as to achieve the purpose of falsely reporting scores .
under these circumstances , Call only Play Integrity API Not enough to protect the application : The device has not been cracked 、 Application is also legal , Therefore, this operation can be done through Play Integrity API All inspections of .
But you can use Play Integrity API Of nonce To protect this specific high-value operation that reports game scores , That is to say nonce The value of the encoding operation in . The implementation method is as follows :
Users initiate important operations ;
The application is ready to protect messages , for example JSON Formatted message ;
The application calculates the encrypted hash value of the message to be protected . for example , Use SHA-256 or SHA-3-256 The hash algorithm ;
Application call Play Integrity API, And call setNonce() In order to nonce Field is set to the encrypted hash value calculated in the previous step ;
The message that the application will protect and Play Integrity API Send the signature result of to the server ;
The application server verifies whether the encrypted hash value of the message it receives is consistent with nonce Field values match , And reject any mismatched results .
The following sequence diagram illustrates the relevant steps :
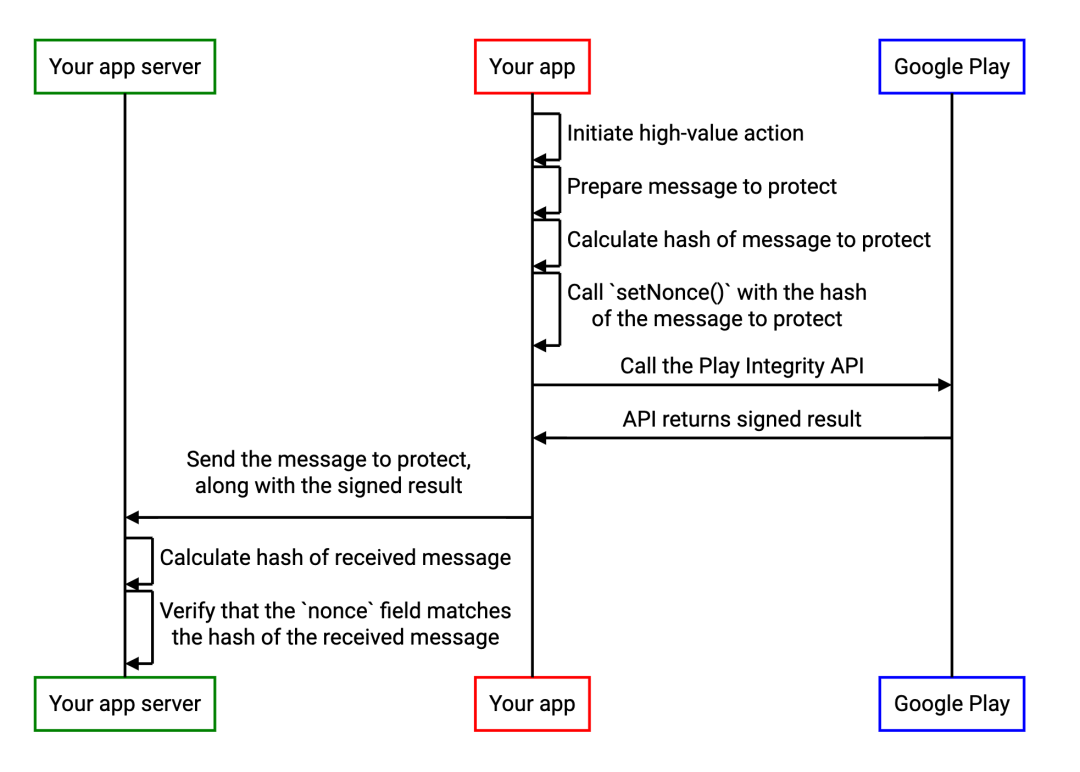
As long as the protected original message is sent with the signature result , And both the server and the client use the same mechanism to calculate nonce, In this way, the message will not be tampered .
Please note that , In the above scenario , The effectiveness of the security model is limited to attacks that occur in the network ( Not in devices or applications ), So verify Play Integrity API The equipment and application integrity signals provided are also particularly important .
Prevent replay attacks
Let's imagine another scenario , An application or game uses Play Integrity API To protect yourself C/S framework , But the attacker tried to interact with the server by using the cracked device , And don't let the server detect .
If you want to " a " This attack target , The attacker will first make the application and Play Integrity API Interact , And get the signed response content , Then run the application on the cracking device and intercept Play Integrity API Call to , Use previously recorded 、 Respond with the signed response content , In this way, the integrity check will not be performed .
Since the signed response has not been changed in any way , So digital signature seems normal , The application server will mistakenly think that it is communicating with legitimate devices . We call this Replay attack .
The first line of defense against such attacks is to verify the signature response timestampMillis Field . This field contains the timestamp when the response was created , Even if the digital signature is verified , It can also be used on the server side to detect whether it is a suspicious old response .
in other words , Application servers can also take advantage of Play Integrity API Medium nonce, Assign a unique value to each response , And verify that the response matches the unique value set previously . The implementation method is as follows :
The server creates globally unique values in a way that attackers cannot predict . for example ,128 Encrypted secure random numbers with bits or more ;
Application call Play Integrity API, And will nonce Field is set to the unique value received by the application server ;
The app will Play Integrity API Send the signature result of to the server ;
The server verifies nonce Whether the field matches the previously generated unique value , And reject all mismatched results .
The following sequence diagram illustrates the relevant steps :
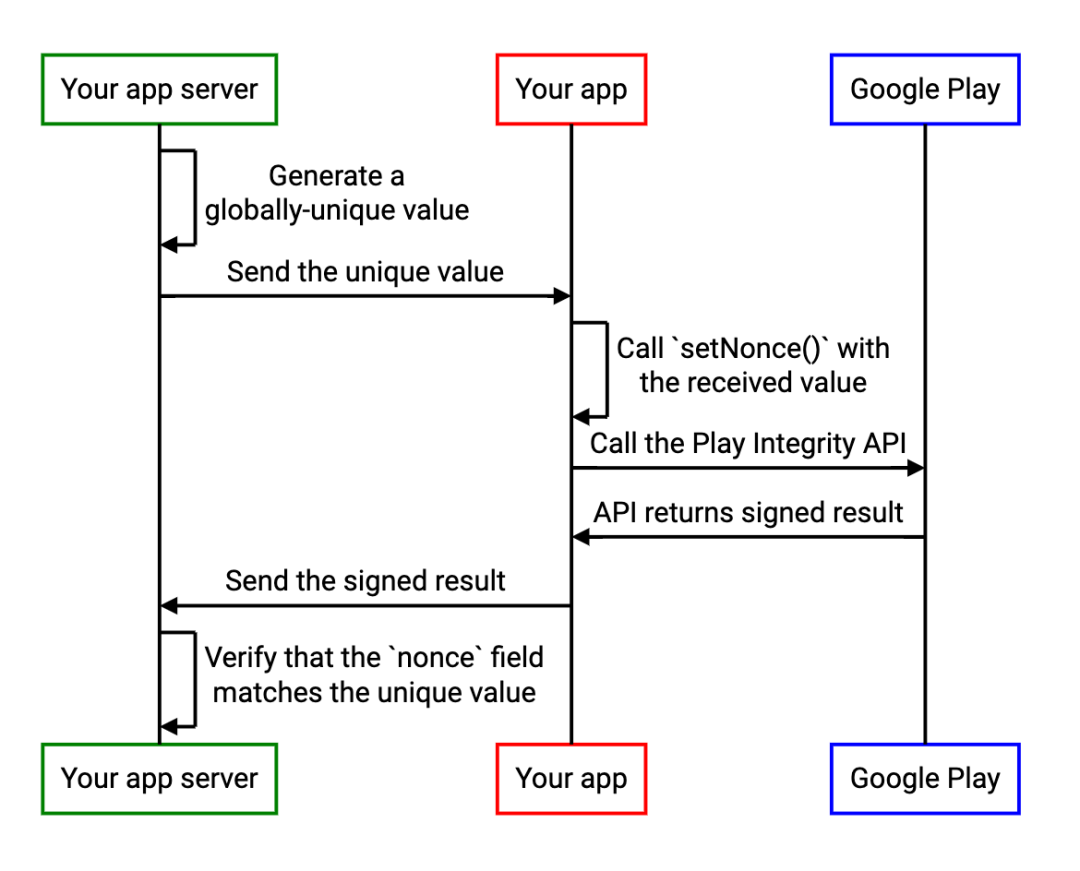
After realizing the above process , Every time the server requires the application to call Play Integrity API when , It will use different globally unique values , So as long as the attacker cannot predict this value ,nonce Does not match the expected value , The previous response cannot be reused .
Combine two protective measures
Although the above two mechanisms work in different ways , But if the application needs two kinds of protection at the same time , These two mechanisms can be combined in one Play Integrity API in call , for example , Attach the results of the two protective measures to a larger Base64 nonce in . The implementation method of combining the two protection measures is as follows :
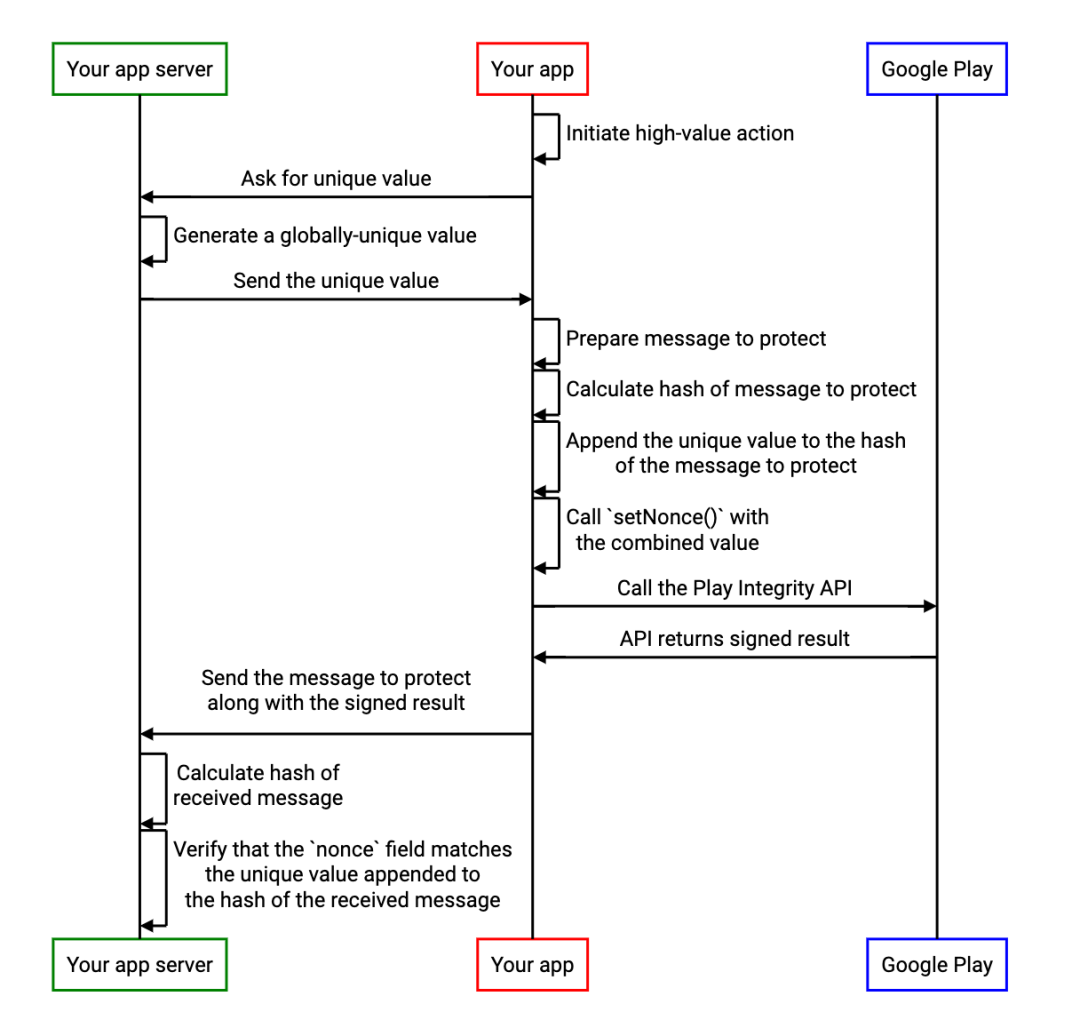
Users initiate important operations ;
The application requires the server to provide a unique value to identify the request ;
The application server generates a globally unique value , Prevent attackers from making predictions . for example , You can create such a value using a cryptographic secure random number generator . We recommend that you create not less than 128 The value of a ;
The application server sends a globally unique value to the application ;
The application is ready to protect messages , for example JSON Formatted message ;
The application calculates the encrypted hash value of the message to be protected . for example , Use SHA-256 or SHA-3-256 The hash algorithm ;
The application creates a string by appending the unique value received from the application server and the hash value of the message to be protected ;
Application call Play Integrity API, And call setNonce() In order to nonce Field is set to the string created in the previous step ;
The message that the application will protect and Play Integrity API Send the signature result of to the server ;
Application server split nonce Value of field , Then verify whether the encrypted hash value of the message and the previously generated unique value match the expected value , And reject any mismatched results .
The following sequence diagram illustrates the relevant steps :
The above is what you can use nonce Some examples of further protecting applications from malicious user attacks . If your application can handle sensitive data , Or easy to be abused , We suggest you consider using Play Integrity API, Take relevant measures to mitigate the threat .
For information about using Play Integrity API For more information and start experiencing , Please go to Play Integrity API page :
https://developer.android.google.cn/google/play/integrity
 Click at the end of the screen | Read the original | immediately understand Play Integrity API For more information
Click at the end of the screen | Read the original | immediately understand Play Integrity API For more information

Check the size and color of the square at the same time
边栏推荐
- The road to success in R & D efficiency of 1000 person Internet companies
- There are so many factors that imprison you
- . Net Maui performance improvement
- Use metersphere to keep your testing work efficient
- Onedns helps college industry network security
- Flet教程之 16 Tabs 选项卡控件 基础入门(教程含源码)
- Summed up 200 Classic machine learning interview questions (with reference answers)
- 對比學習之 Unsupervised Learning of Visual Features by Contrasting Cluster Assignments
- 清华姚班程序员,网上征婚被骂?
- [encapsulation of time format tool functions]
猜你喜欢
总结了200道经典的机器学习面试题(附参考答案)
Mastering the new functions of swiftui 4 weatherkit and swift charts

Use metersphere to keep your testing work efficient
一度辍学的数学差生,获得今年菲尔兹奖

Onedns helps college industry network security
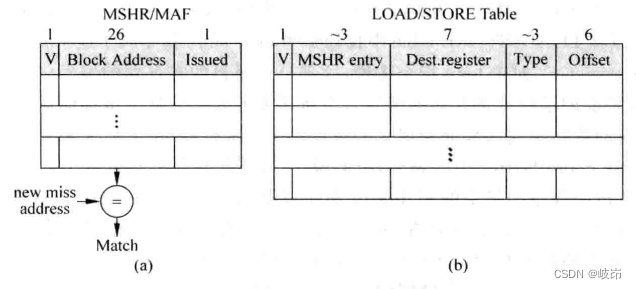
超标量处理器设计 姚永斌 第9章 指令执行 摘录

核舟记(一):当“男妈妈”走进现实,生物科技革命能解放女性吗?
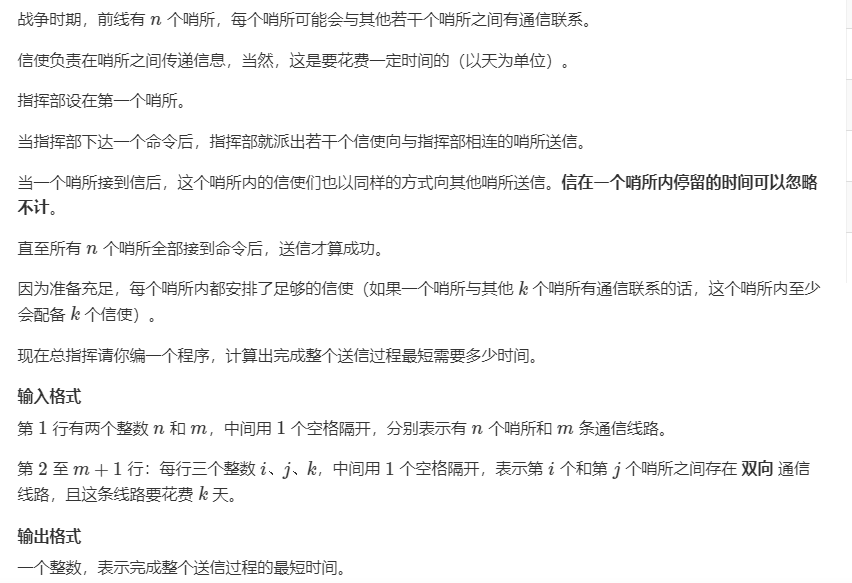
【最短路】Acwing1128信使:floyd最短路
Flet教程之 19 VerticalDivider 分隔符组件 基础入门(教程含源码)
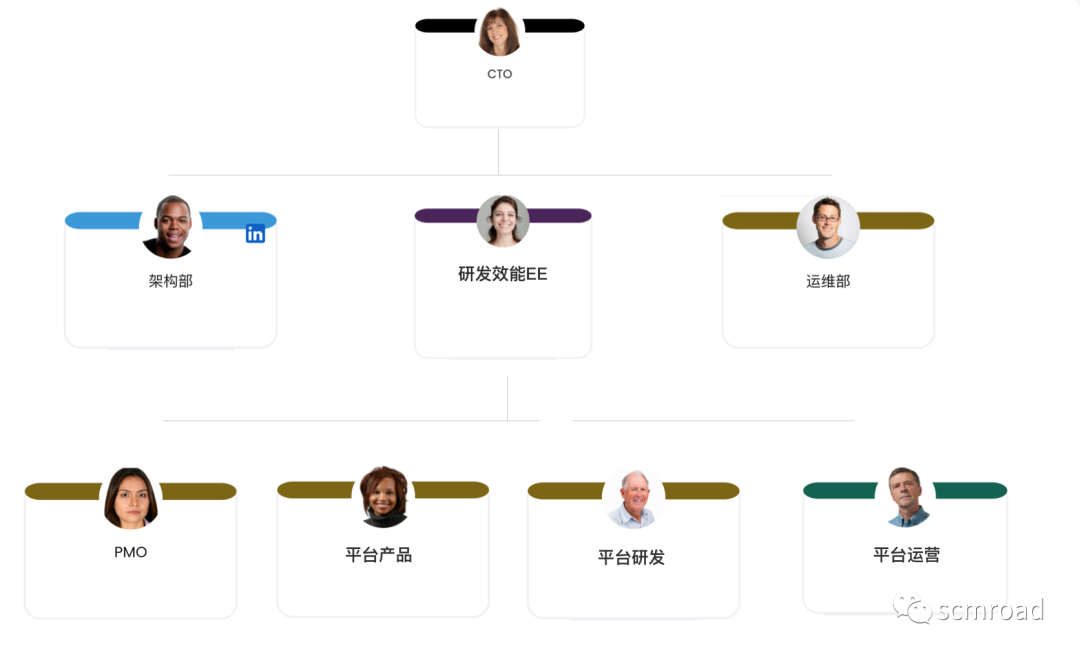
La voie du succès de la R & D des entreprises Internet à l’échelle des milliers de personnes
随机推荐
Distributed database master-slave configuration (MySQL)
SwiftUI 教程之如何在 2 秒内实现自动滚动功能
對比學習之 Unsupervised Learning of Visual Features by Contrasting Cluster Assignments
STM32 entry development write DS18B20 temperature sensor driver (read ambient temperature, support cascade)
【神经网络】卷积神经网络CNN【含Matlab源码 1932期】
Common SQL statement collation: MySQL
When sink is consumed in mysql, the self incrementing primary key has been set in the database table. How to operate in Flink?
【最短路】Acwing1128信使:floyd最短路
Tsinghua Yaoban programmers, online marriage was scolded?
STM32 entry development NEC infrared protocol decoding (ultra low cost wireless transmission scheme)
超标量处理器设计 姚永斌 第9章 指令执行 摘录
正在运行的Kubernetes集群想要调整Pod的网段地址
超标量处理器设计 姚永斌 第10章 指令提交 摘录
聊聊SOC启动(十一) 内核初始化
About how to install mysql8.0 on the cloud server (Tencent cloud here) and enable local remote connection
通过环境变量将 Pod 信息呈现给容器
相机标定(1): 单目相机标定及张正友标定基本原理
Table replication in PostgreSQL
sql里,我想设置外键,为什么出现这个问题
What development models did you know during the interview? Just read this one