当前位置:网站首页>[pointer] octal to decimal
[pointer] octal to decimal
2022-07-06 14:36:00 【|Light|】
requirement
Make up a function , Realize octal conversion to decimal .( Use a pointer to achieve )
Code
/* * This function is used to convert an octal number to a decimal number * Octal numbers are stored in formal parameters as strings a In the one-dimensional character array pointed to * Please return the calculated decimal number as a function value */
int oct_to_dec(char* a)
{
int d=0;
int i;
int k=strlen(a)-1;
for(i=0;i<20;i++)
{
if(a[i]=='\0')
{
break;
}
else
{
d = d + ((a[i]-48)*pow(8,k));
k--;
}
}
return d;
}
main function
int main()
{
char a[20];
int n;
gets(a);
n = oct_to_dec(a);
printf("%d",n);
return 0;
}
test
Test input
1234
Output
668
边栏推荐
- 内网渗透之内网信息收集(二)
- 函数:求方程的根
- 《统计学》第八版贾俊平第十一章一元线性回归知识点总结及课后习题答案
- 使用 flask_whooshalchemyplus jieba实现flask的全局搜索
- 函数:用牛顿迭代法求方程的根
- 《统计学》第八版贾俊平第二章课后习题及答案总结
- Bing Dwen Dwen official NFT blind box will be sold for about 626 yuan each; JD home programmer was sentenced for deleting the library and running away; Laravel 9 officially released | Sifu weekly
- Statistics 8th Edition Jia Junping Chapter 3 after class exercises and answer summary
- ES全文索引
- Record an edu, SQL injection practice
猜你喜欢
随机推荐
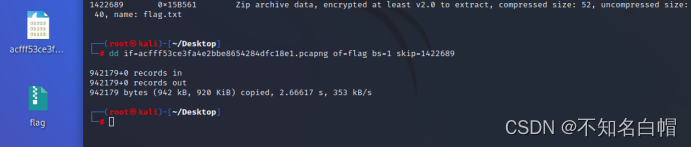
攻防世界MISC练习区(SimpleRAR、base64stego、功夫再高也怕菜刀)
Bing Dwen Dwen official NFT blind box will be sold for about 626 yuan each; JD home programmer was sentenced for deleting the library and running away; Laravel 9 officially released | Sifu weekly
【指针】求二维数组中最大元素的值
List and data frame of R language experiment III
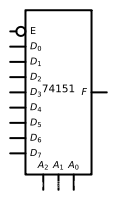
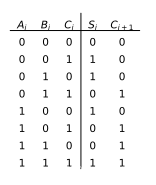
数字电路基础(五)算术运算电路
【指针】使用插入排序法将n个数从小到大进行排列
“Hello IC World”
Statistics 8th Edition Jia Junping Chapter 3 after class exercises and answer summary
Chain team implementation (C language)
Statistics 8th Edition Jia Junping Chapter 14 summary of index knowledge points and answers to exercises after class
Fundamentals of digital circuit (IV) data distributor, data selector and numerical comparator
Matplotlib绘图快速入门
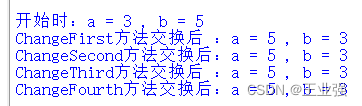
关于交换a和b的值的四种方法
Record an edu, SQL injection practice
MySQL interview questions (4)
Proceedingjoinpoint API use
指针:最大值、最小值和平均值
Only 40% of the articles are original? Here comes the modification method
线程的实现方式总结
Circular queue (C language)