当前位置:网站首页>Ad domain group policy management
Ad domain group policy management
2022-07-07 21:33:00
【There is Xiao Deng in operation and One 、Active Directory Group policy management ADManager Plus It's based on web Of Active Directory Management and reporting tools , With just a few clicks, you can help manage group policy objects for multiple domains (GPO). It also provides prefabricated group policies (GPO) report form , Fast extraction GPO Related information . Use ADManager Plus Easy to manage Windows Active Directory Every aspect of group policy : Active Directory Two 、 establish GPO and GPO link Create group policy objects at once and immediately link them to multiple organizational units 、 Domain 、 Site , With this machine Active Directory Group Policy Editor ( for example , Group policy management console (GPMC)) Perform the same task as , It can greatly reduce the time and energy required . When needed ,ADManager Plus Allow you to put the right GPO Link to related containers . ADManager Plus 3、 ... and 、 management GPO and GPO link Select multiple from any node GPO and GPO Link and immediately perform the following group policy management operations . management GPO management GPO and GPO link Four 、 edit GPO Use quick search to identify the user and computer configuration management template settings associated with the corresponding group policy object , And in Active Directory Editor in chief GPO Set up . You can fully or partially enable or disable GPO, in other words , User or computer configuration settings can be enabled or disabled separately . 5、 ... and 、 Enable GPO Link or disable GPO link Use this feature , You can choose more than one GPO Link and immediately enable or disable them . This allows the administrator to control GPO Application , To make it consistent with the organization's policy changes . 6、 ... and 、 perform GPO Or cancel execution GPO Use ADManager Plus, You can perform GPO To easily impose specific settings on other settings . When needed , You can also cancel execution GPO. 7、 ... and 、 Block or unblock GPO Inherit By default , Group policy settings are inherited from their parent objects . however , According to your needs , You can select the desired container and block inheritance . When needed , You can also unblock inheritance . 8、 ... and 、 Delete GPO and GPO link According to your needs , Batch deletion GPO And unnecessary GPO link . In the predefined GPO Clean up with the help of reports GPO, This makes it easier to identify unused and disabled GPO And delete them in batches . ADManager Plus Provide a set of pre encapsulated reports ( for example , Recently created GPO、GPO Prevent inheritance containers, etc ), Thus, it is easier to obtain immediately GPO Related information . As a free download ADManager Plus, You can try all these functions . 版权声明

本文为[There is Xiao Deng in operation and [email protected]]所创,转载请带上原文链接,感谢
https://yzsam.com/2022/188/202207071723256451.html
边栏推荐
- Devil daddy B1 hearing the last barrier, break through with all his strength
- 私募基金在中國合法嗎?安全嗎?
- What are the official stock trading apps in the country? Is it safe to use
- GridView defines its own time for typesetting "suggestions collection"
- Use br to back up tidb cluster data to azure blob storage
- Meta force force meta universe system development fossage model
- 201215-03-19—cocos2dx内存管理–具体解释「建议收藏」
- 恶魔奶爸 B2 突破语法,完成正统口语练习
- FatMouse' Trade (Hangdian 1009)
- Qt编写物联网管理平台39-报警联动
猜你喜欢
Demon daddy B3 read extensively in a small amount, and completed 20000 vocabulary+
Ubuntu安装mysql8遇到的问题以及详细安装过程
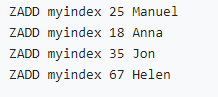
Implement secondary index with Gaussian redis
How to meet the dual needs of security and confidentiality of medical devices?
Ten thousand word summary data storage, three knowledge points
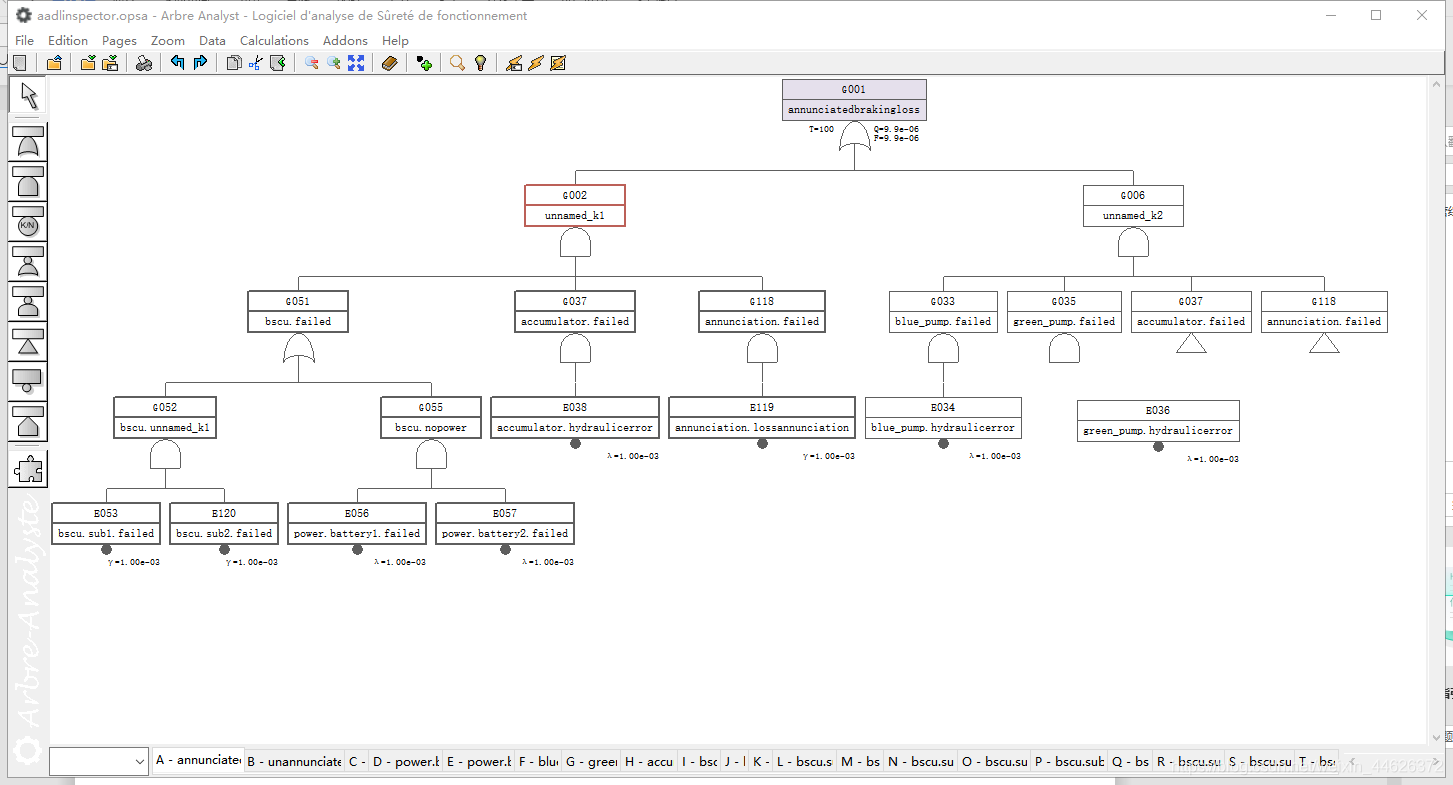
AADL inspector fault tree safety analysis module
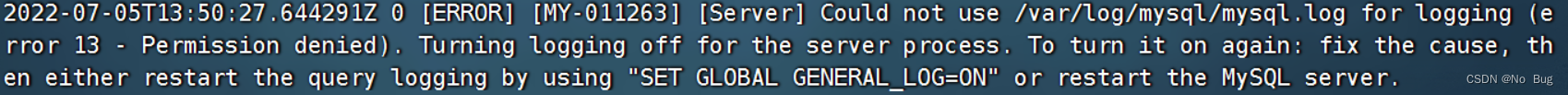
Problems encountered in installing mysql8 for Ubuntu and the detailed installation process

Focusing on safety in 1995, Volvo will focus on safety in the field of intelligent driving and electrification in the future

95年专注安全这一件事 沃尔沃未来聚焦智能驾驶与电气化领域安全
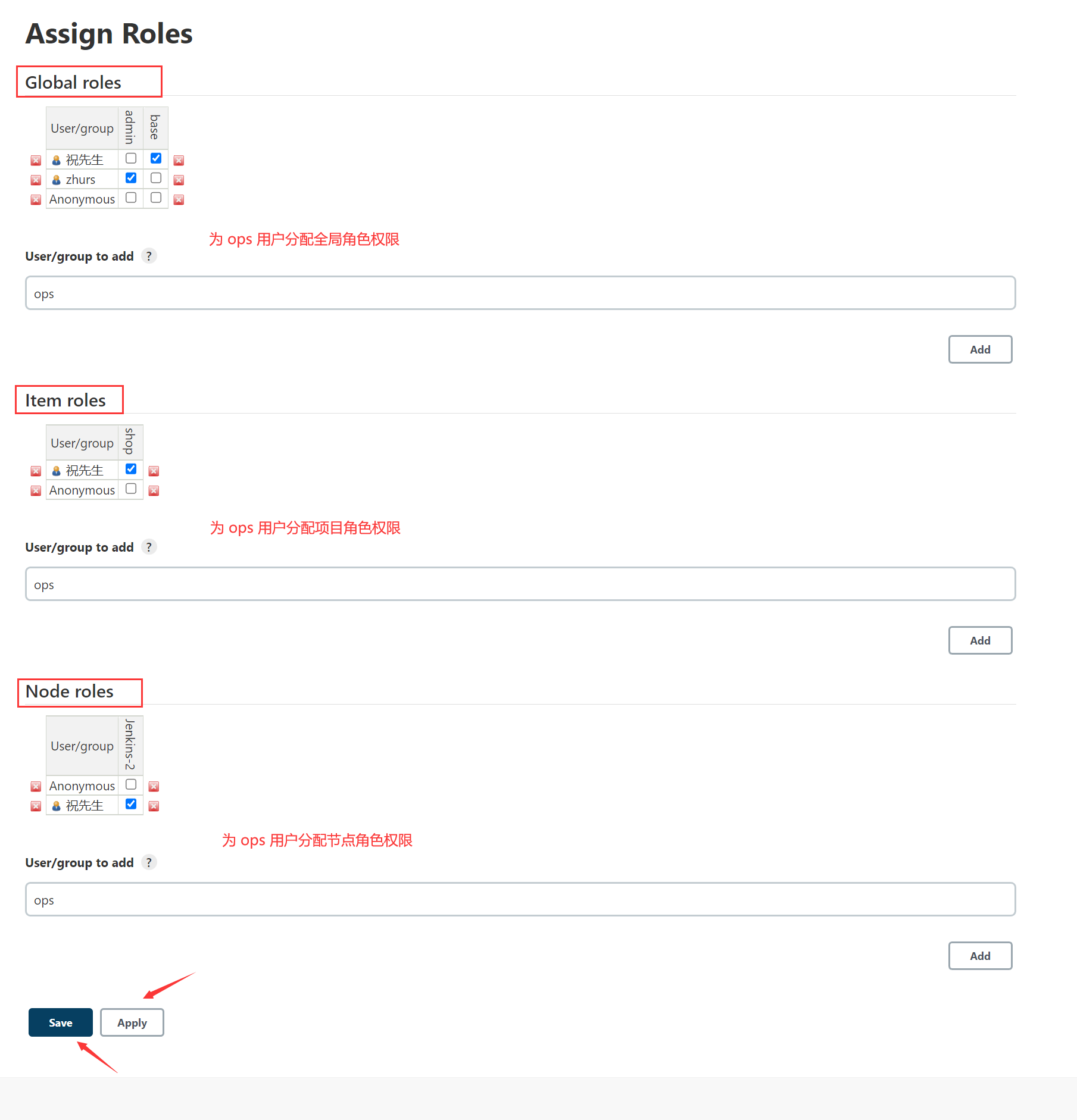
Jenkins user rights management
随机推荐
Le capital - investissement est - il légal en Chine? C'est sûr?
Mysql子查询关键字的使用方式(exists)
npm uninstall和rm直接删除的区别
Contour layout of margin
95年专注安全这一件事 沃尔沃未来聚焦智能驾驶与电气化领域安全
恶魔奶爸 指南帖——简易版
Cocos2d-x 游戏存档[通俗易懂]
Prometheus remote_ write InfluxDB,unable to parse authentication credentials,authorization failed
Solve the problem of using uni app mediaerror mediaerror errorcode -5
uva 12230 – Crossing Rivers(概率)「建议收藏」
Ubuntu安装mysql8遇到的问题以及详细安装过程
Deadlock conditions and preventive treatment [easy to understand]
Meta force force meta universe system development fossage model
Focusing on safety in 1995, Volvo will focus on safety in the field of intelligent driving and electrification in the future
恶魔奶爸 C
UVA 12230 – crossing rivers (probability) "suggested collection"
Feature generation
Deployment, recall and deletion solutions - stsadm and PowerShell "suggestions collection"
Micro service remote debug, nocalhost + rainbow micro service development second bullet
Do you have to make money in the account to open an account? Is the fund safe?