当前位置:网站首页>Introduction to rce in attack and defense world
Introduction to rce in attack and defense world
2022-07-04 07:09:00 【Distant sky】
Shooting range problem php_rce It has been shown that , This is the question rce( Remote instruction / Code Execution Vulnerability )
Open the range , See only this promotion page , Promote a framework and specifically specify the version . I guess the version of this framework may have public vulnerabilities . So I went to Baidu ThinkphpPHP V5

After searching online, I found that this version framework really exists rce Loophole .
Click into a blog address casually :https://www.cnblogs.com/backlion/p/10106676.html
See the vulnerability affecting the version 、 Vulnerability analysis and utilization are introduced 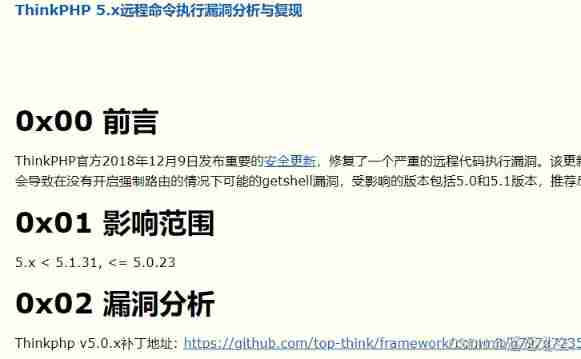
Refer directly to the code constructed here

Use instruction ls List the current catalog file 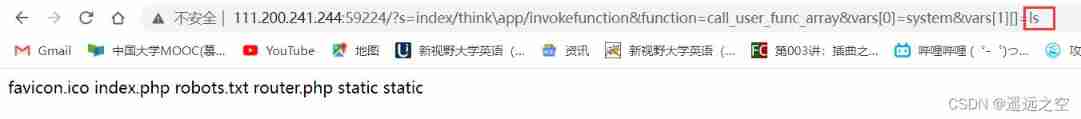
use cat After checking these files one by one , Didn't get flag, Guess it should be put in other directories ...... So I thought of using ../ Step up . Last ../../../ When backing up the third level directory, I found flag, This is actually in the root directory ...
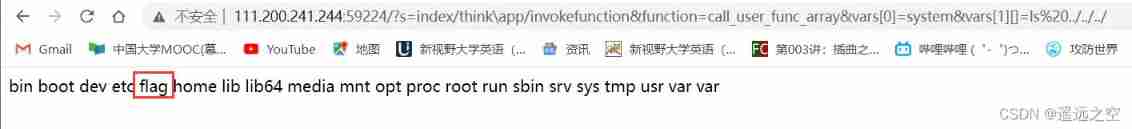
And then use cat Command to view the file , Get flag.

Later I went to check , View root file , direct ls / This command will do , And use it directly cat /flag Just go , Or right linux The instructions are unfamiliar .. Ah ~~
边栏推荐
- The number of patent applications in China has again surpassed that of the United States and Japan, ranking first in the world for 11 consecutive years
- Novel website program source code that can be automatically collected
- Responsive mobile web test questions
- How notepad++ counts words
- BasicVSR++: Improving Video Super-Resolutionwith Enhanced Propagation and Alignment
- 图的底部问题
- Tar source code analysis 6
- Flink memory model, network buffer, memory tuning, troubleshooting
- Label management of kubernetes cluster
- Vulhub vulnerability recurrence 76_ XXL-JOB
猜你喜欢

Four sets of APIs for queues
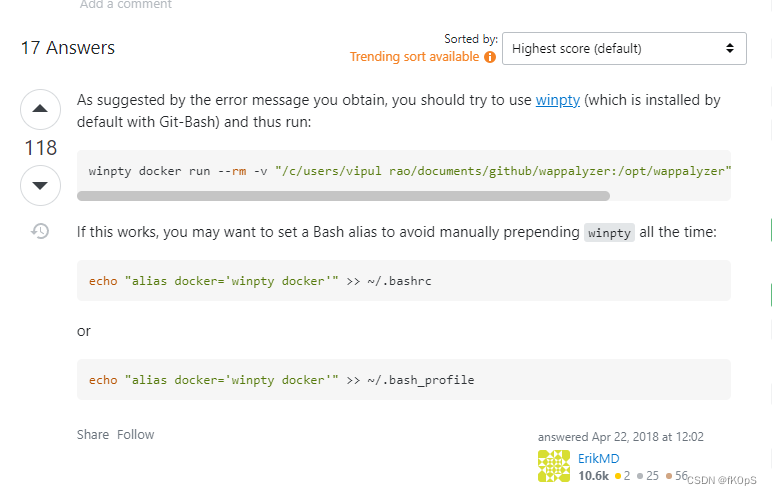
the input device is not a TTY. If you are using mintty, try prefixing the command with ‘winpty‘
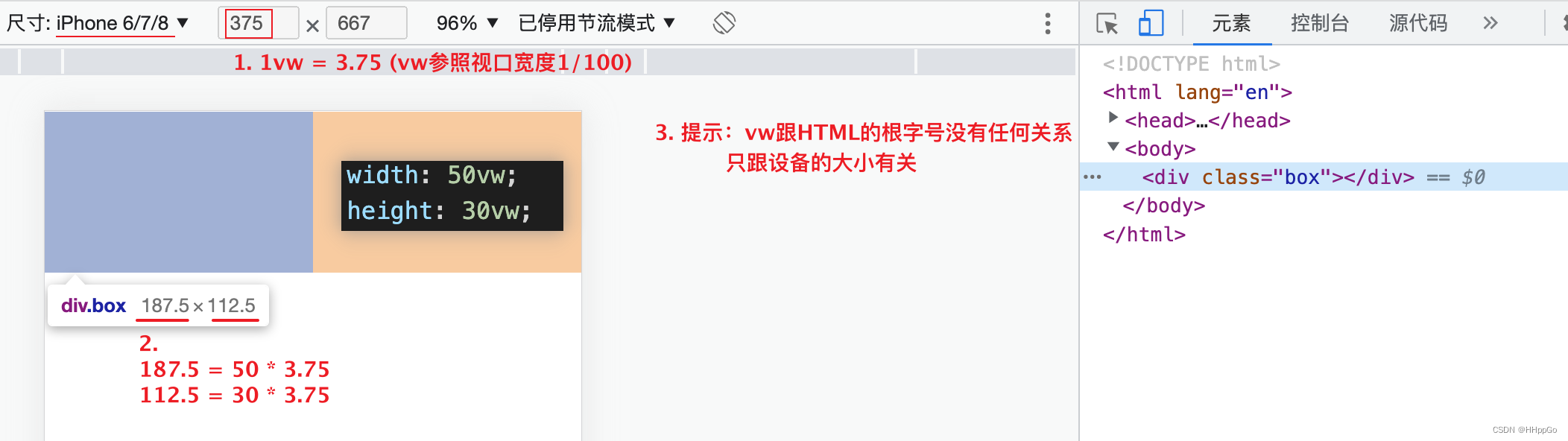
移动适配:vw/vh
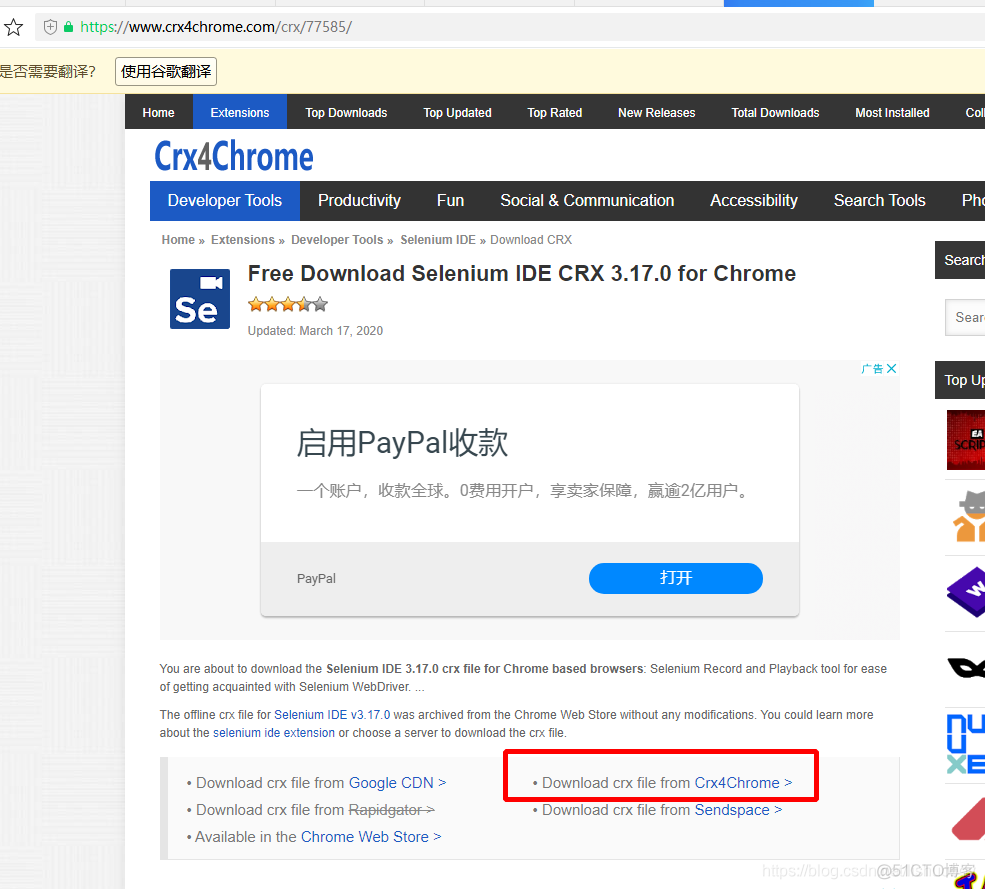
Selenium ide plug-in download, installation and use tutorial

云Redis 有什么用? 云redis怎么用?
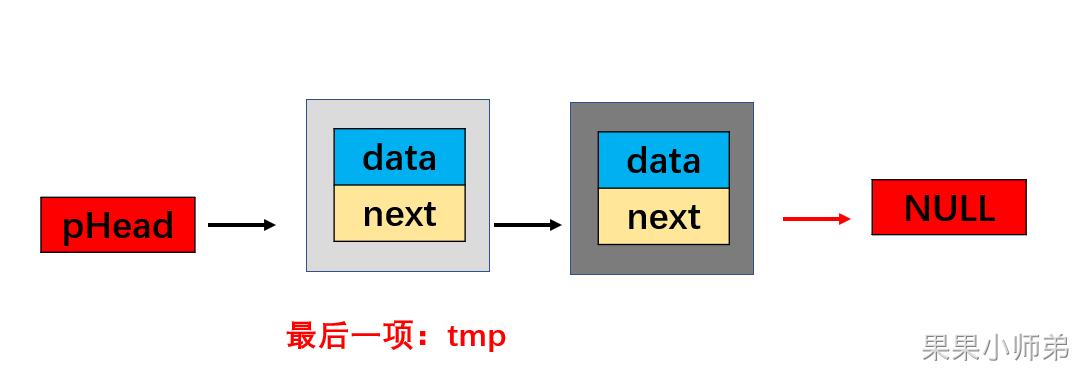
果果带你写链表,小学生看了都说好
![[GF (q) + LDPC] regular LDPC coding and decoding design and MATLAB simulation based on the GF (q) field of binary graph](/img/5e/7ce21dd544aacf23b4ceef1ec547fd.png)
[GF (q) + LDPC] regular LDPC coding and decoding design and MATLAB simulation based on the GF (q) field of binary graph
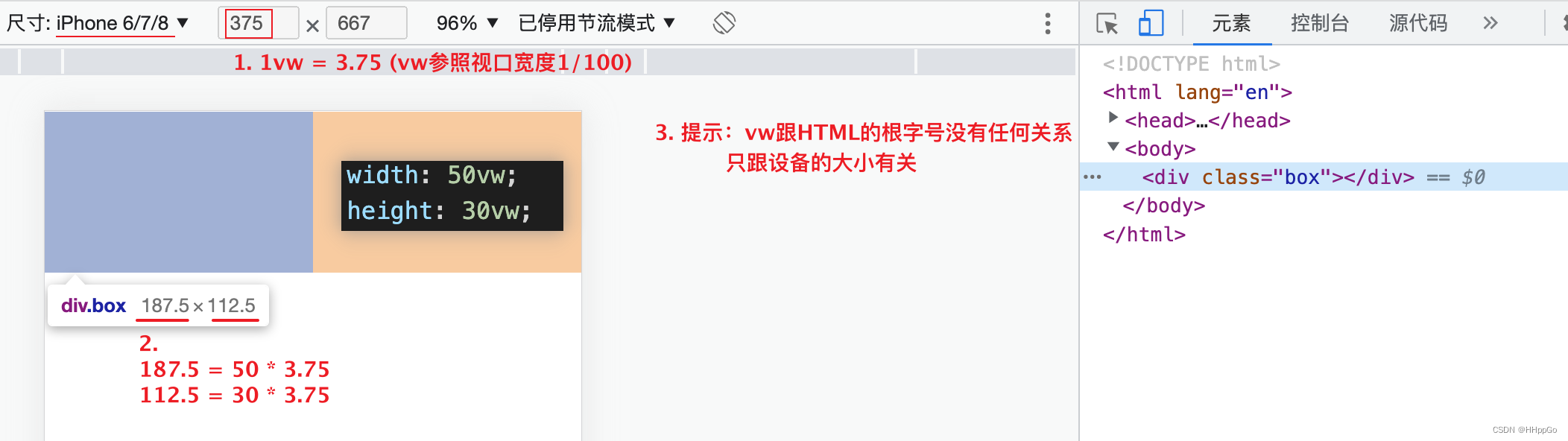
Mobile adaptation: vw/vh
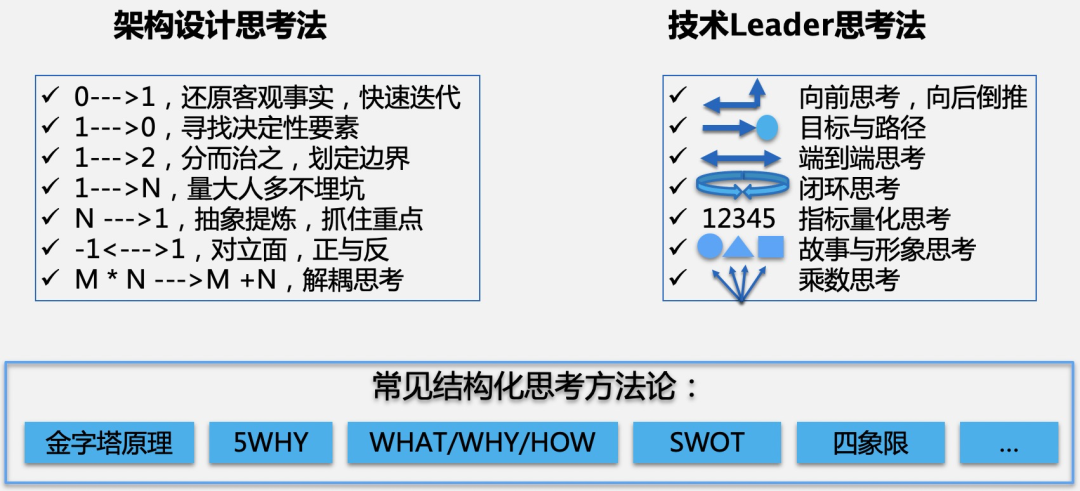
大厂技术专家:架构设计中常用的思维模型
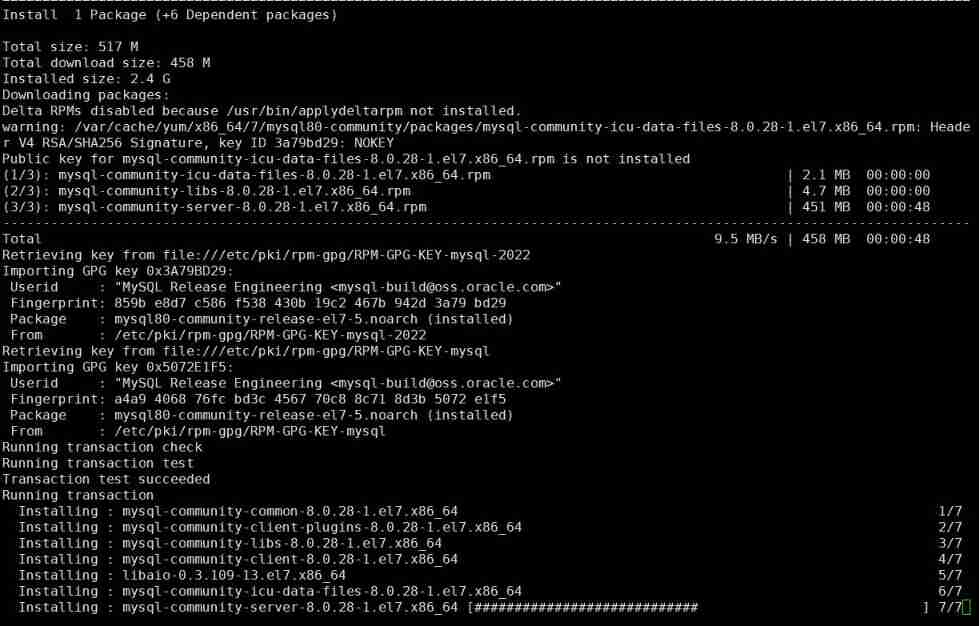
MySQL relearn 2- Alibaba cloud server CentOS installation mysql8.0
随机推荐
[thread pool]
Research on an endogenous data security interaction protocol oriented to dual platform and dual chain architecture
Selection (021) - what is the output of the following code?
uniapp小程序分包
电子协会 C语言 1级 35 、银行利息
Deep profile data leakage prevention scheme
Crawler (III) crawling house prices in Tianjin
Google Chrome Portable Google Chrome browser portable version official website download method
How to input single quotation marks and double quotation marks in latex?
tars源码分析之4
Novel website program source code that can be automatically collected
com. alibaba. nacos. api. exception. NacosException
Boast about Devops
Selenium driver ie common problem solving message: currently focused window has been closed
Introduction to deep learning Ann neural network parameter optimization problem (SGD, momentum, adagrad, rmsprop, Adam)
A new understanding of how to encrypt industrial computers: host reinforcement application
请问旧版的的常用SQL怎么迁移到新版本里来?
Cervical vertebra, beriberi
What is industrial computer encryption and how to do it
【GF(q)+LDPC】基于二值图GF(q)域的规则LDPC编译码设计与matlab仿真