当前位置:网站首页>Reading notes of the beauty of programming
Reading notes of the beauty of programming
2022-07-06 00:22:00 【It rained and windy last night】
Preface
Text
Reading progress
P12
Introduction
So why The manhole cover of the sewer is round ?
Online answers : a. If it is square , Boring man , It's possible to pick up the manhole cover , Throw it diagonally .b. Because the hole at the bottom is a cylinder , therefore , The manhole cover is round .Show me the most beautiful program I wrote ?
Sentiment :
a. A function does only one thing , One function should not be able to abstract another function .
b. The ideal situation is zero parameter , If any , Up to three input parameters are allowed , More functions would be silly . Be careful , The identification parameters are ugly ,
c. High readability , Clear logic , High cohesion , Low coupling , TestedHow to write a program to make CPU The usage rate of 50%?
To be changed ~
Reference resources
边栏推荐
- 云呐|公司固定资产管理系统有哪些?
- Upgrade openssl-1.1.1p for openssl-1.0.2k
- 从底层结构开始学习FPGA----FIFO IP核及其关键参数介绍
- Hardware and interface learning summary
- DEJA_VU3D - Cesium功能集 之 055-国内外各厂商地图服务地址汇总说明
- Intranet Security Learning (V) -- domain horizontal: SPN & RDP & Cobalt strike
- LeetCode 1189. Maximum number of "balloons"
- Yunna | what are the main operating processes of the fixed assets management system
- PV static creation and dynamic creation
- Single source shortest path exercise (I)
猜你喜欢
LeetCode 1598. Folder operation log collector
云呐|固定资产管理系统功能包括哪些?
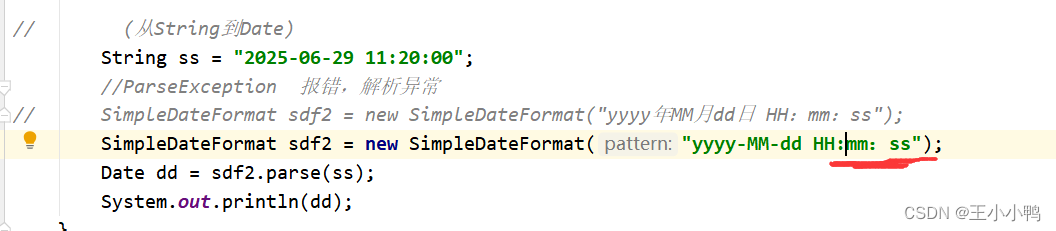
Date类中日期转成指定字符串出现的问题及解决方法
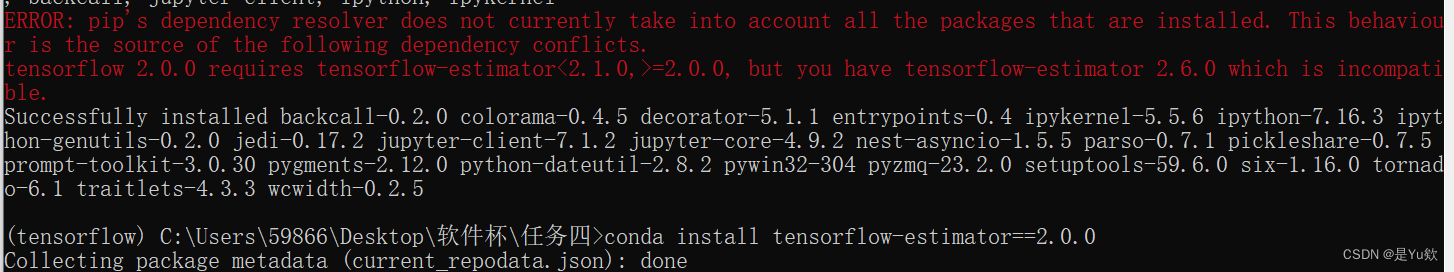
anconda下载+添加清华+tensorflow 安装+No module named ‘tensorflow‘+KernelRestarter: restart failed,内核重启失败
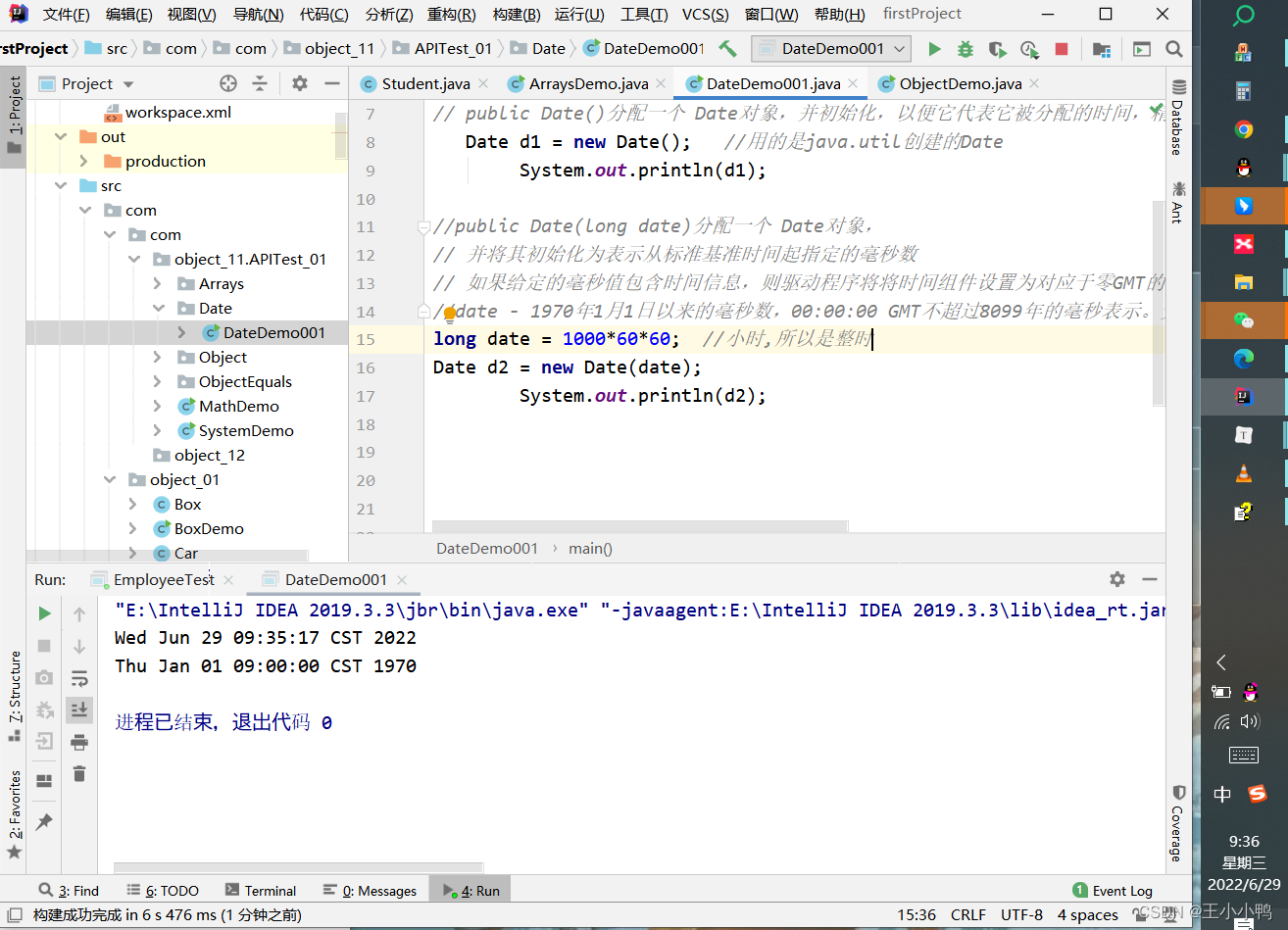
常用API类及异常体系
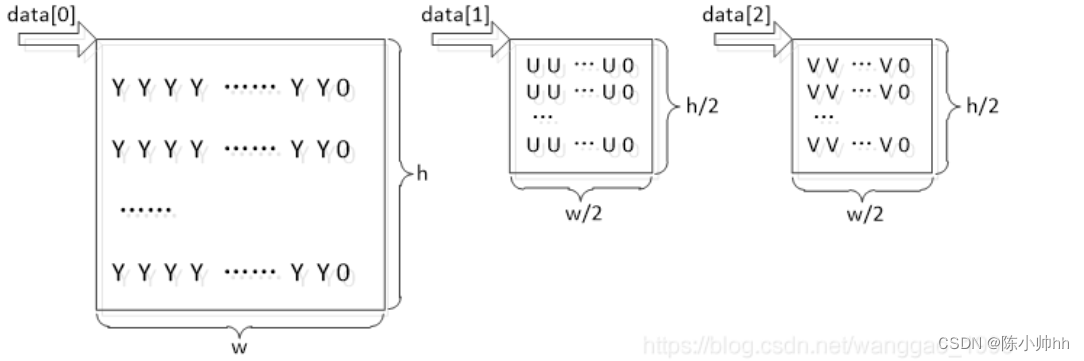
FFMPEG关键结构体——AVFrame
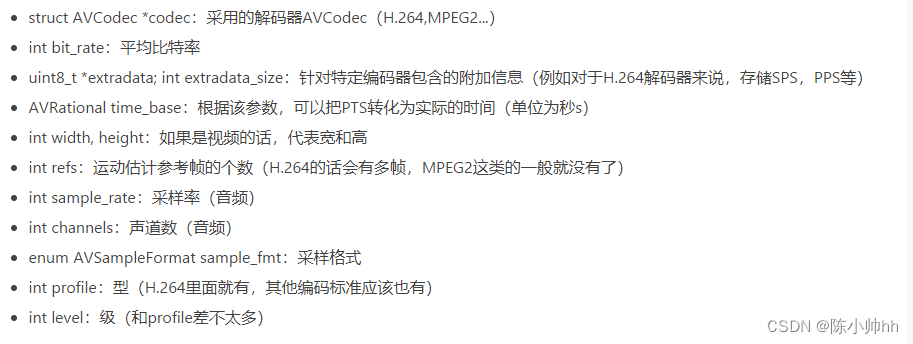
FFMPEG关键结构体——AVCodecContext
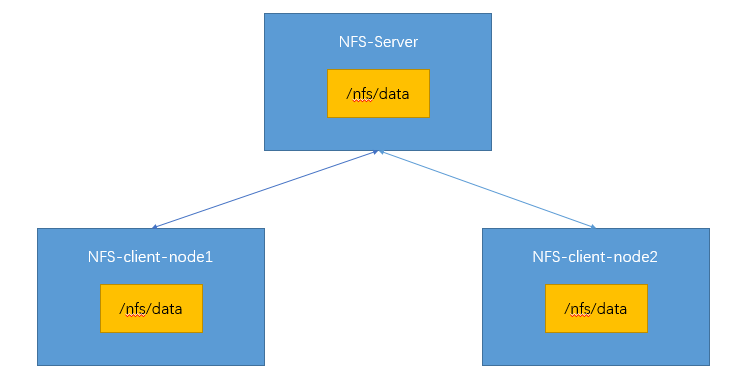
PV static creation and dynamic creation
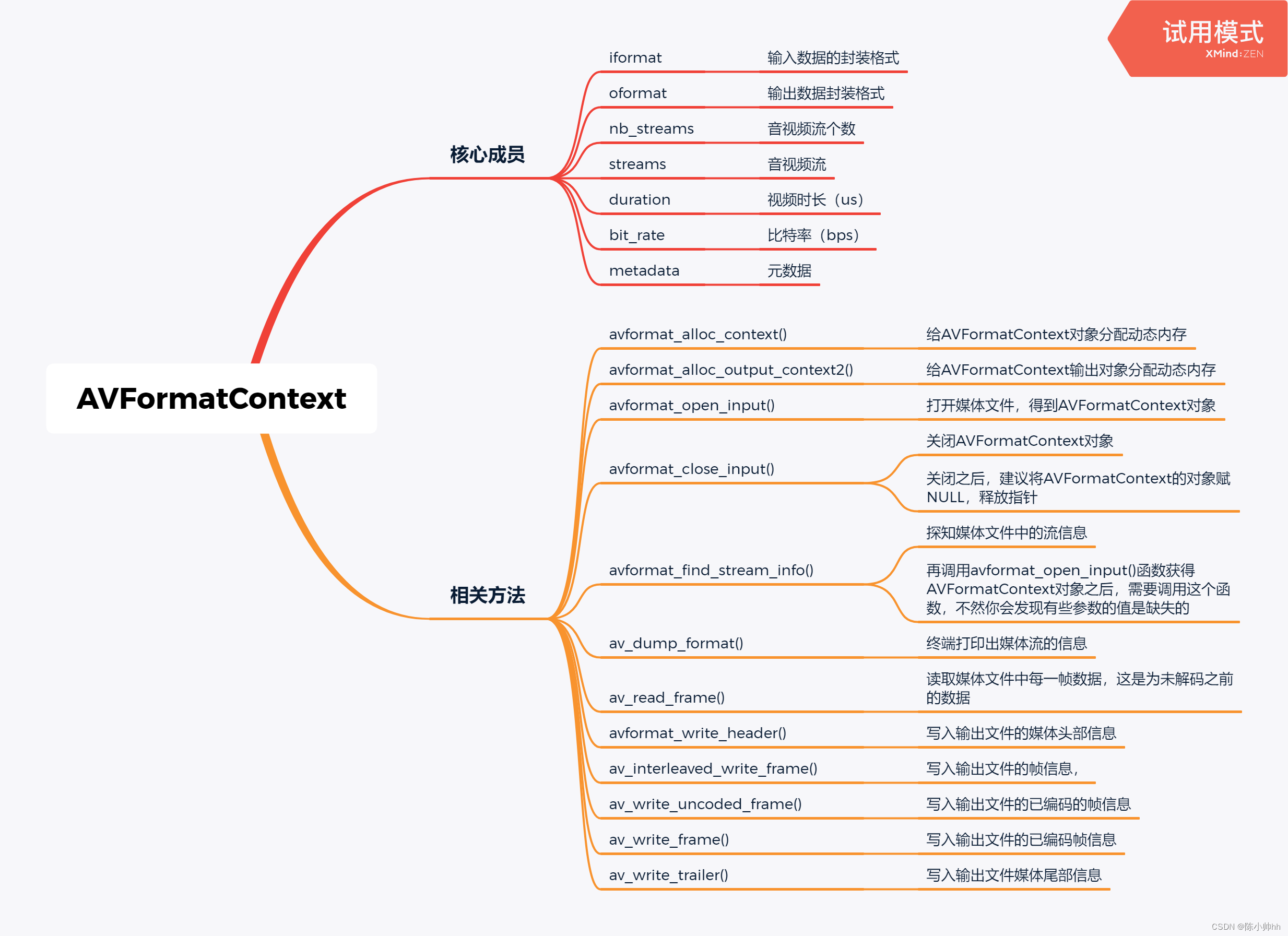
Key structure of ffmpeg - avformatcontext
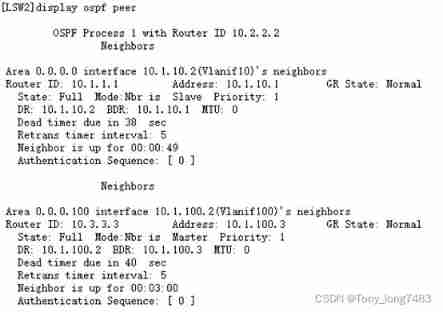
Configuring OSPF GR features for Huawei devices
随机推荐
Detailed explanation of APP functions of door-to-door appointment service
PHP determines whether an array contains the value of another array
[Chongqing Guangdong education] reference materials for Zhengzhou Vocational College of finance, taxation and finance to play around the E-era
【线上小工具】开发过程中会用到的线上小工具合集
What are Yunna's fixed asset management systems?
FFmpeg学习——核心模块
Global and Chinese markets of universal milling machines 2022-2028: Research Report on technology, participants, trends, market size and share
wx. Getlocation (object object) application method, latest version
MySql——CRUD
如何解决ecology9.0执行导入流程流程产生的问题
软件测试工程师必会的银行存款业务,你了解多少?
Determinant learning notes (I)
After summarizing more than 800 kubectl aliases, I'm no longer afraid that I can't remember commands!
Knowledge about the memory size occupied by the structure
Mysql - CRUD
Gavin teacher's perception of transformer live class - rasa project actual combat e-commerce retail customer service intelligent business dialogue robot system behavior analysis and project summary (4
Chapter 16 oauth2authorizationrequestredirectwebfilter source code analysis
The difference of time zone and the time library of go language
Leetcode:20220213 week race (less bugs, top 10% 555)
Transport layer protocol ----- UDP protocol