当前位置:网站首页>Standard ACL and extended ACL
Standard ACL and extended ACL
2022-07-07 18:38:00 【Chen chacha__】
standard ACL

R0 Basic configuration
int f0/0
ip add 192.168.10.254 255.255.255.0
no shutdown
int f0/1
ip add 76.12.16.133 255.255.255.252
no shut
R1 Basic configuration
int f0/0
ip add 76.12.32.254 255.255.255.0
no shut
int f0/1
ip add 76.12.16.134 255.255.255.252
no shut
Then give them to R1、R2 Configure the default route
R1
ip route 0.0.0.0 0.0.0.0 76.12.16.133 #76.12.16.133 It is the next hop address connected to this router , It can also be written as the next hop port number connected to this router
R2
ip route 0.0.0.0 0.0.0.0 76.12.16.134 # ditto
standard ACL On the router near the destination address
stay R1 Upper configuration standard ACL
standard ACL The number of 1-99
ip access-list 1 permit host 192.168.10.100
ip access-list 1 deny host 192.168.10.1
interface f0/1
ip access-group 1 in
Expand ACL

R0 Basic configuration
int f0/0
ip add 192.168.10.254 255.255.255.0
no shutdown
int f0/1
ip add 76.12.16.133 255.255.255.252
no shut
R1 Basic configuration
int f0/0
ip add 76.12.32.254 255.255.255.0
no shut
int f0/1
ip add 76.12.16.134 255.255.255.252
no shut
Then give them to R1、R2 Configure the default route
R1
ip route 0.0.0.0 0.0.0.0 76.12.16.133 #76.12.16.133 It is the next hop address connected to this router , It can also be written as the next hop port number connected to this router
R2
ip route 0.0.0.0 0.0.0.0 76.12.16.134 # ditto
Expand ACL It is configured on the router close to the source address
stay R0 Configure extensions on ACL
Expand ACL The number of 100-199
You need an agreement 、 Source IP、 Source port 、 Purpose IP、 The destination ports match
ip access-list 100 deny icmp host 192.168.10.1 host 76.12.32.1 # Reject from 192.168.10.1 The host goes to 76.12.32.1 The host ping package
ip access-list 100 permit ip any any # Allow all
interface f0/1
ip access-group 100 out # take ACL Apply to the out interface
边栏推荐
- 嵌入式C语言程序调试和宏使用的技巧
- 云景网络科技面试题【杭州多测师】【杭州多测师_王sir】
- The highest level of anonymity in C language
- 通过 Play Integrity API 的 nonce 字段提高应用安全性
- 持续测试(CT)实战经验分享
- gsap动画库
- Backup Alibaba cloud instance OSS browser
- 2022年理财有哪些产品?哪些适合新手?
- Tips for this week 131: special member functions and ` = Default`
- Afghan interim government security forces launched military operations against a hideout of the extremist organization "Islamic state"
猜你喜欢
ICer知识点杂烩(后附大量题目,持续更新中)

RIP和OSPF的区别和配置命令
【蓝桥杯集训100题】scratch从小到大排序 蓝桥杯scratch比赛专项预测编程题 集训模拟练习题第17题
![[principle and technology of network attack and Defense] Chapter 1: Introduction](/img/d0/f33447e46ab405c668eef820a8f9fb.png)
[principle and technology of network attack and Defense] Chapter 1: Introduction

上市十天就下线过万台,欧尚Z6产品实力备受点赞
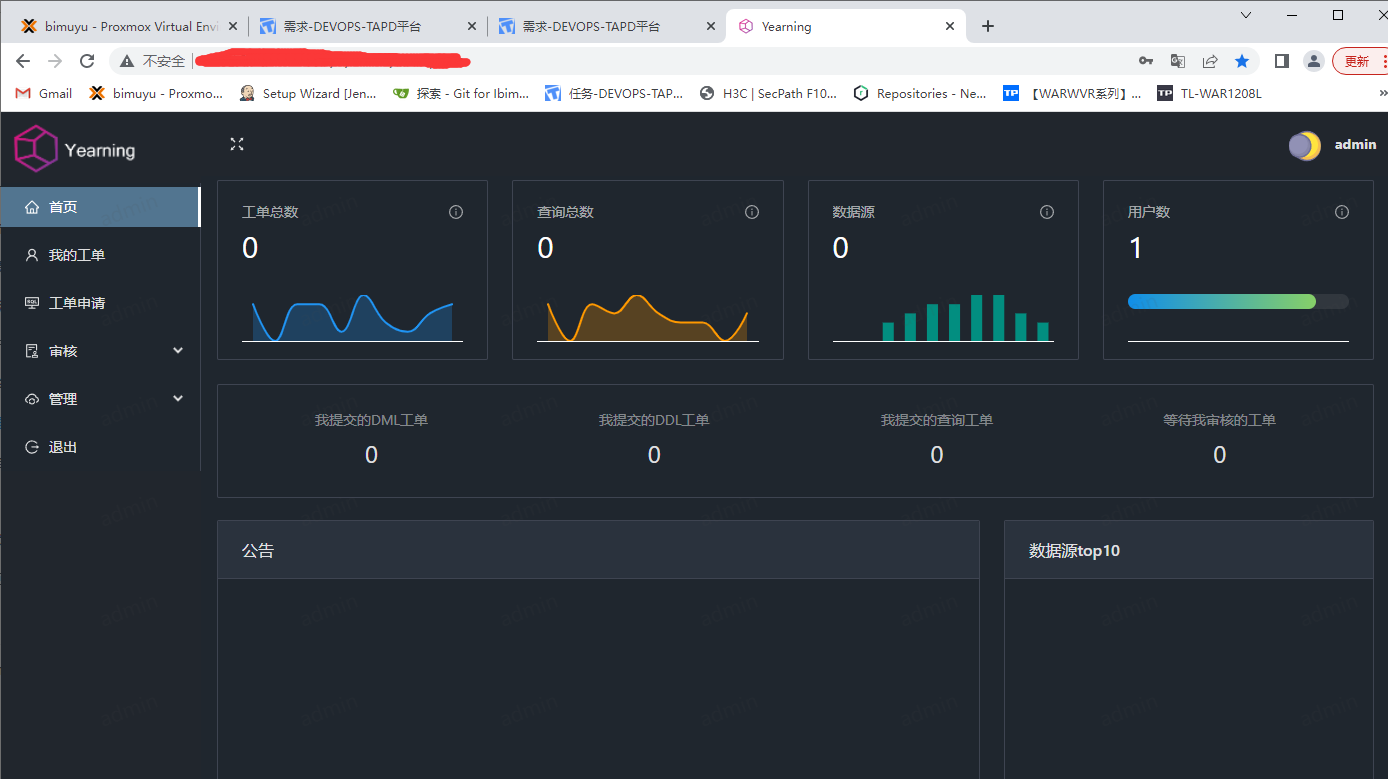
Year SQL audit platform
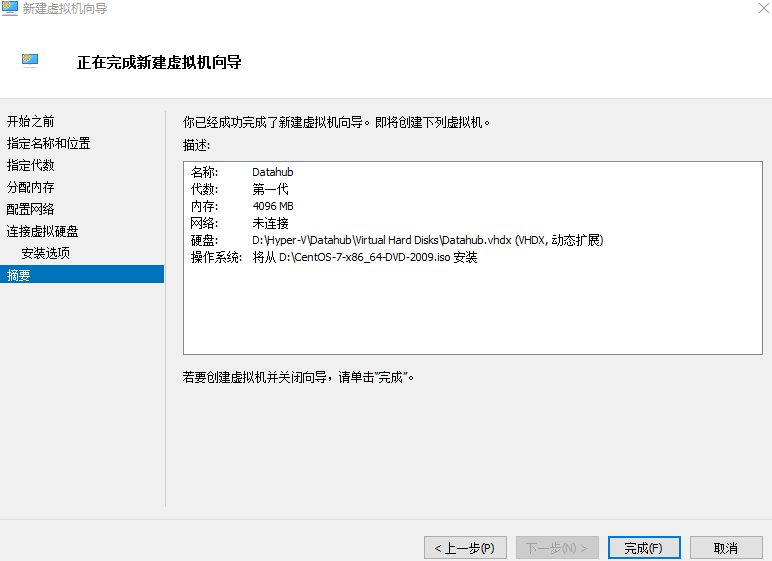
Ten thousand words nanny level long article -- offline installation guide for datahub of LinkedIn metadata management platform
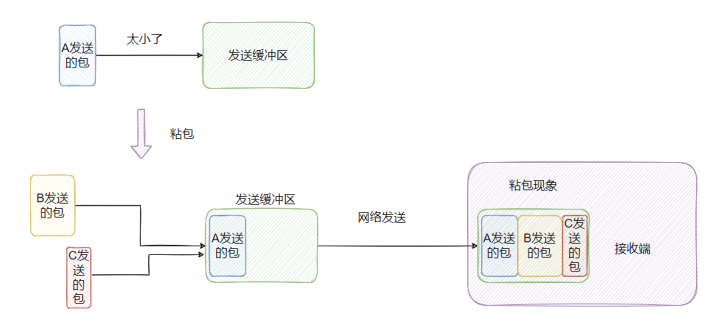
Do you really understand sticky bag and half bag? 3 minutes to understand it
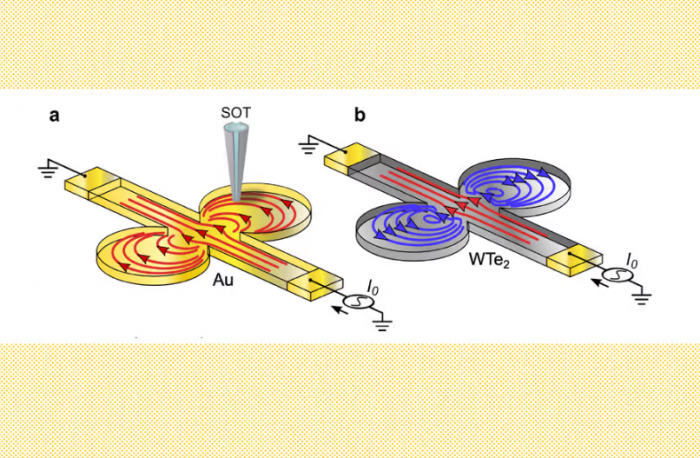
科学家首次观察到“电子漩涡” 有助于设计出更高效的电子产品

Backup Alibaba cloud instance OSS browser
随机推荐
Simple configuration of single arm routing and layer 3 switching
海量数据去重的hash,bitmap与布隆过滤器Bloom Filter
嵌入式C语言程序调试和宏使用的技巧
小程序中实现付款功能
SQLite SQL exception near "with": syntax error
Chapter 2 building CRM project development environment (building development environment)
线程池的拒绝策略
[principles and technologies of network attack and Defense] Chapter 5: denial of service attack
What is the general yield of financial products in 2022?
【剑指 Offer】59 - I. 滑动窗口的最大值
Nunjuks template engine
Yunjing network technology interview question [Hangzhou multi tester] [Hangzhou multi tester _ Wang Sir]
Discuss | frankly, why is it difficult to implement industrial AR applications?
元宇宙带来的创意性改变
PIP related commands
Download, installation and development environment construction of "harmonyos" deveco
通过 Play Integrity API 的 nonce 字段提高应用安全性
[trusted computing] Lesson 12: TPM authorization and conversation
nest.js入门之 database
Rules for filling in volunteers for college entrance examination