当前位置:网站首页>NR modulation 1
NR modulation 1
2022-07-06 03:03:00 【Bai Xiaosheng in Ming Dynasty】
Preface
When testing throughput, the terminal mainly depends on two parameters , Network assigned RB, as well as Modulation
This series mainly refers to the courses of some overseas experts for sharing
The main reference here is cisco Of tutorangel
- summary
- RF Encoding and modulation Mechanisms
- BPSK
- QPSK
- QAM
One summary
After the coding , What we get is still digital signal 0,1 , As mentioned earlier, I will QPSK Will be able to 0
Modulation into 1,1 Modulation into -1 Simulation information of , Corresponding to one waveform.
How to distinguish between wavefrom(symbol) , Mainly through amplitude , frequency , phase
Why modulate :
Finally, the signal should be transmitted through the antenna
The length of the antenna is proportional to the wavelength , So it is inversely proportional to the frequency , The higher the frequency is. , Shorter wavelength , The shorter the antenna can be . The length of the antenna is not equal to one wavelength , Tend to be 1/4 Wavelength or 5/8 wavelength .
Two RF Encoding and modulation Mechanisms
After modulation ,0,1 Corresponding to one symbol( or waveform), We can distinguish in three ways 0,1
Amplitude, frequency, phase
2.1 Amplitude distinguish
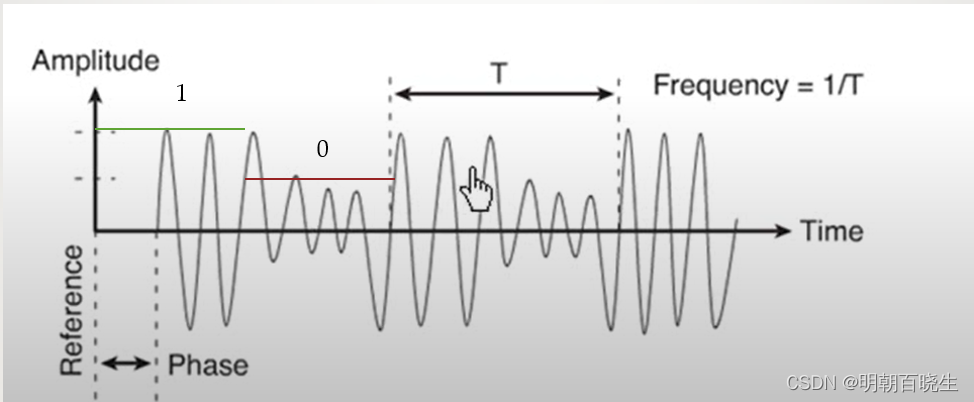
The above can be distinguished by amplitude 1,0
2.2 Frequency distinguish
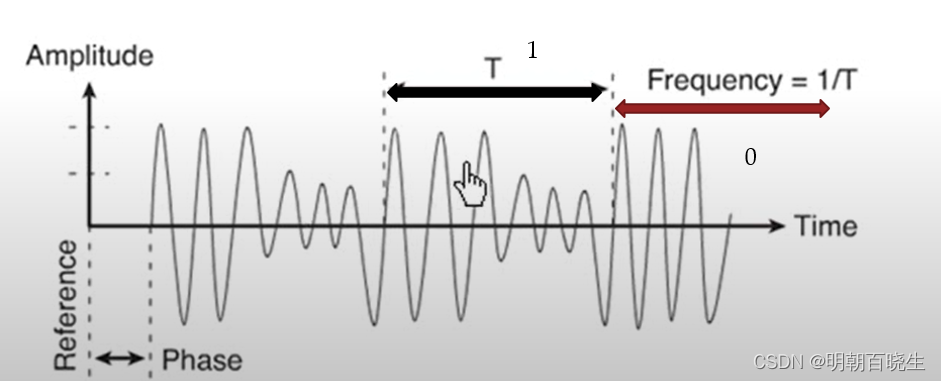
Pictured , The frequency of the second half is higher , Low frequency is thought to be 1, High frequency thinks so 0.
2.3 phase distinguish
0,1 Phase difference 

2.4 Modulation algorithm
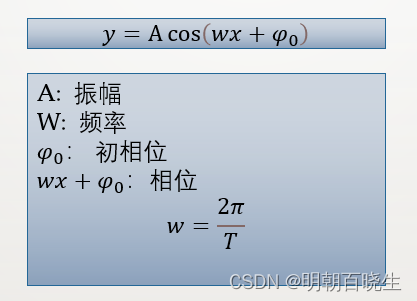
Corresponding to a time domain waveform
3: BPSK(Binary phase shift keying) Binary phase shift keying

According to the two levels of digital baseband signal , A phase modulation method that makes the carrier phase switch between two different values . Usually the two phases are different  , It is sometimes called inverse keying PSK
, It is sometimes called inverse keying PSK
Take binary phase modulation as an example , The symbol is 0 when , The modulated carrier is in phase with the modulated carrier
The symbol is 1, The modulated carrier is in inverse phase with the modulated carrier .
One for each symbol bit, Or a waveform Corresponding to one bit
# -*- coding: utf-8 -*-
"""
Created on Mon Jul 4 15:06:27 2022
@author: chengxf2
"""
import numpy as np
import matplotlib.pyplot as plt
def bpsk(bit):
a = 1.0
w = 2.0
if bit ==0:
p = -np.math.pi/2.0
else:
p = np.math.pi/2.0
x = np.linspace(0, 2*np.math.pi,1000)
y = []
for t in x:
v = a*np.cos(w*t+p)
y.append(v)
if 0 ==bit:
plt.plot(x, y, color='g',linewidth=2.0,linestyle="-.") # plot Methods drawing points
else:
plt.plot(x, y, color='r',linewidth=2.0,linestyle="-.") # plot Methods drawing points
plt.xlabel("x")
plt.ylabel("y")
plt.show()
bpsk(0)
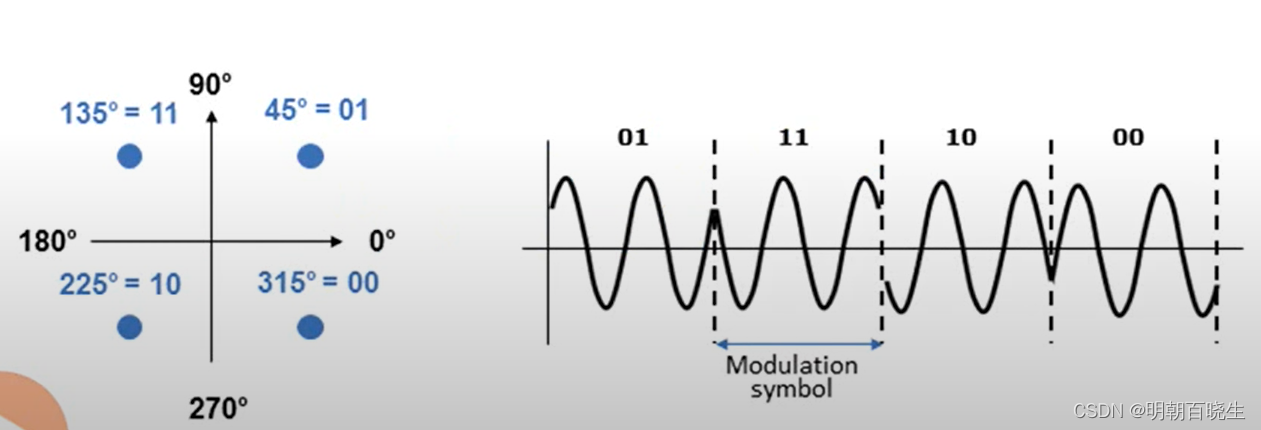
4: QPSK(Quadrature phase shift key Quadrature phase shift keying )
BPSK yes 1bit/symbol
QPSK yes 2bit/symbol
Equivalent to doubling the rate
# -*- coding: utf-8 -*-
"""
Created on Mon Jul 4 15:06:27 2022
@author: chengxf2
"""
import numpy as np
import matplotlib.pyplot as plt
from enum import Enum
class QPSK_PHASE(Enum):
ONE = 1
TWO = 2
THREE =3
FOUR =4
def qpsk(phase):
a = 1.0
w = 2.0
if phase is QPSK_PHASE.ONE:
p = np.math.pi/2*0
elif phase is QPSK_PHASE.TWO:
p = np.math.pi/2
elif phase is QPSK_PHASE.THREE:
p = np.math.pi
else:
p = np.math.pi*3/2
x = np.linspace(0, 2*np.math.pi,1000)
y = []
for t in x:
v = a*np.cos(w*t+p)
y.append(v)
if phase is QPSK_PHASE.ONE:
plt.plot(x, y, color='g',linewidth=2.0,linestyle="-.") # plot Methods drawing points
elif phase is QPSK_PHASE.TWO:
plt.plot(x, y, color='r',linewidth=2.0,linestyle="-.") # plot Methods drawing points
elif phase is QPSK_PHASE.THREE:
plt.plot(x, y, color='b',linewidth=2.0,linestyle="-.") # plot Methods drawing points
else :
plt.plot(x, y, color='y',linewidth=2.0,linestyle="-.") # plot Methods drawing points
plt.xlabel("x")
plt.ylabel("y")
plt.show()
qpsk(QPSK_PHASE.FOUR)
5: Quadrature Amplitude Modulation( Quadrature amplitude modulation )
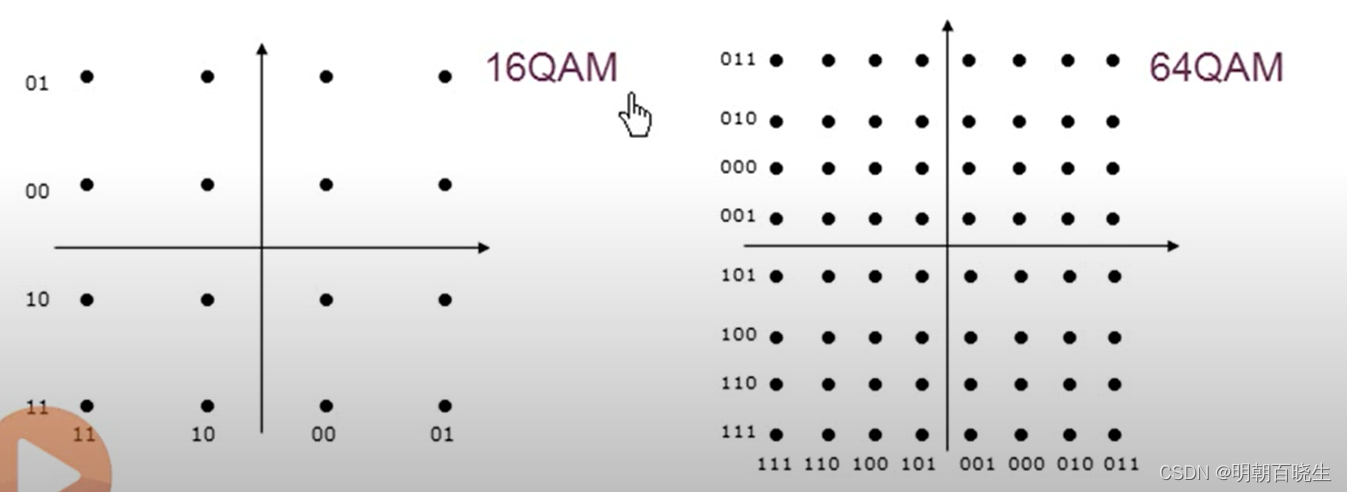
The front is all adjusted phase, It has been said that it can be distinguished by increasing the range bit 0,1
Such as 16QAM
One symbol It can transmit 4bit
64AQM
One symbol It can transmit 6bit
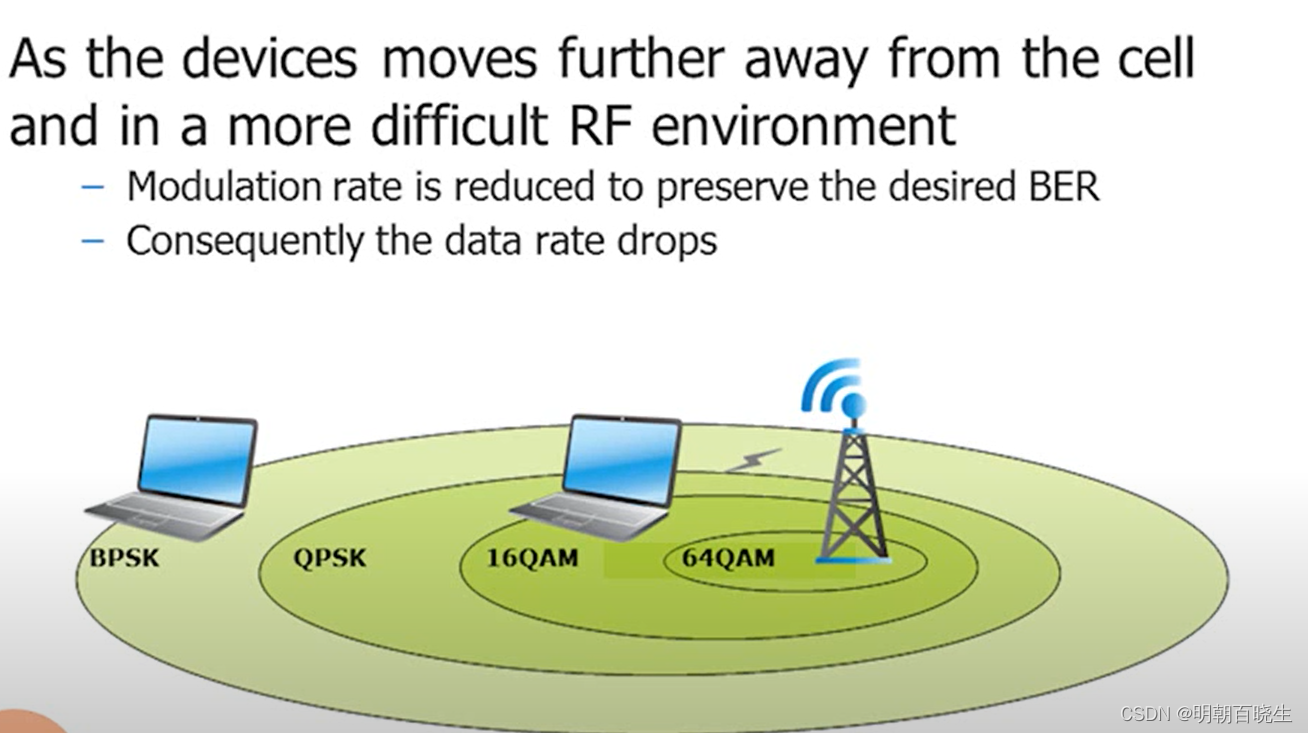
The higher the modulation mode , The distance between points is getting closer , If in a noisy environment
The multipath transmission of signals affects , Signal attenuation and other effects , The obtained symbols will produce deviation , There is an error
At this time, the modulation mode needs to be gradually reduced 64QAM-16QAM-QPSK-BPSK, The speed will gradually decrease
边栏推荐
- Era5 reanalysis data download strategy
- "Hands on learning in depth" Chapter 2 - preparatory knowledge_ 2.5 automatic differentiation_ Learning thinking and exercise answers
- My C language learning record (blue bridge) -- on the pointer
- Detailed use of dbutils # yyds dry goods inventory #
- Introduction to robotframework (III) Baidu search of webui automation
- [Chongqing Guangdong education] higher mathematics I reference materials of Southwest Petroleum University
- Day 50 - install vsftpd on ceontos6.8
- [ruoyi] ztree custom icon (iconskin attribute)
- Which ecology is better, such as Mi family, graffiti, hilink, zhiting, etc? Analysis of five mainstream smart brands
- Microsoft speech synthesis assistant v1.3 text to speech tool, real speech AI generator
猜你喜欢
CobaltStrike-4.4-K8修改版安装使用教程
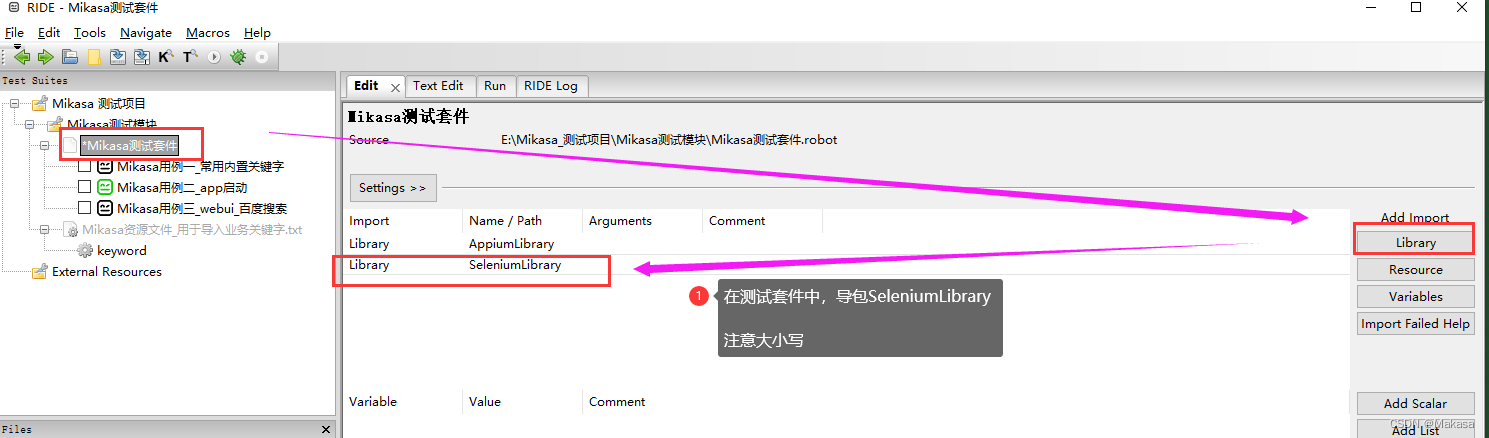
RobotFramework入门(三)WebUI自动化之百度搜索
My C language learning record (blue bridge) -- under the pointer
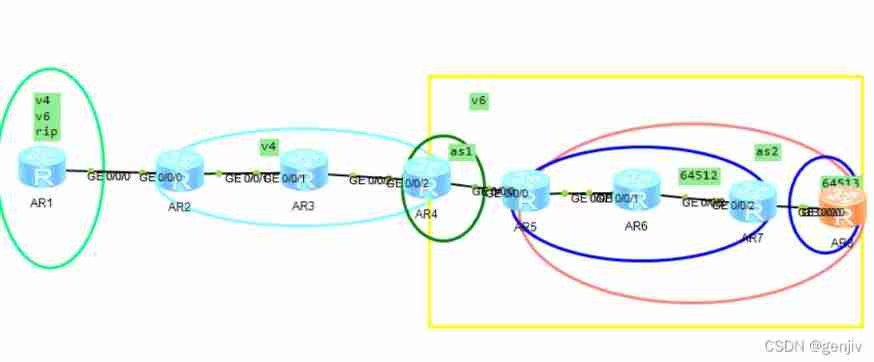
IPv6 jobs
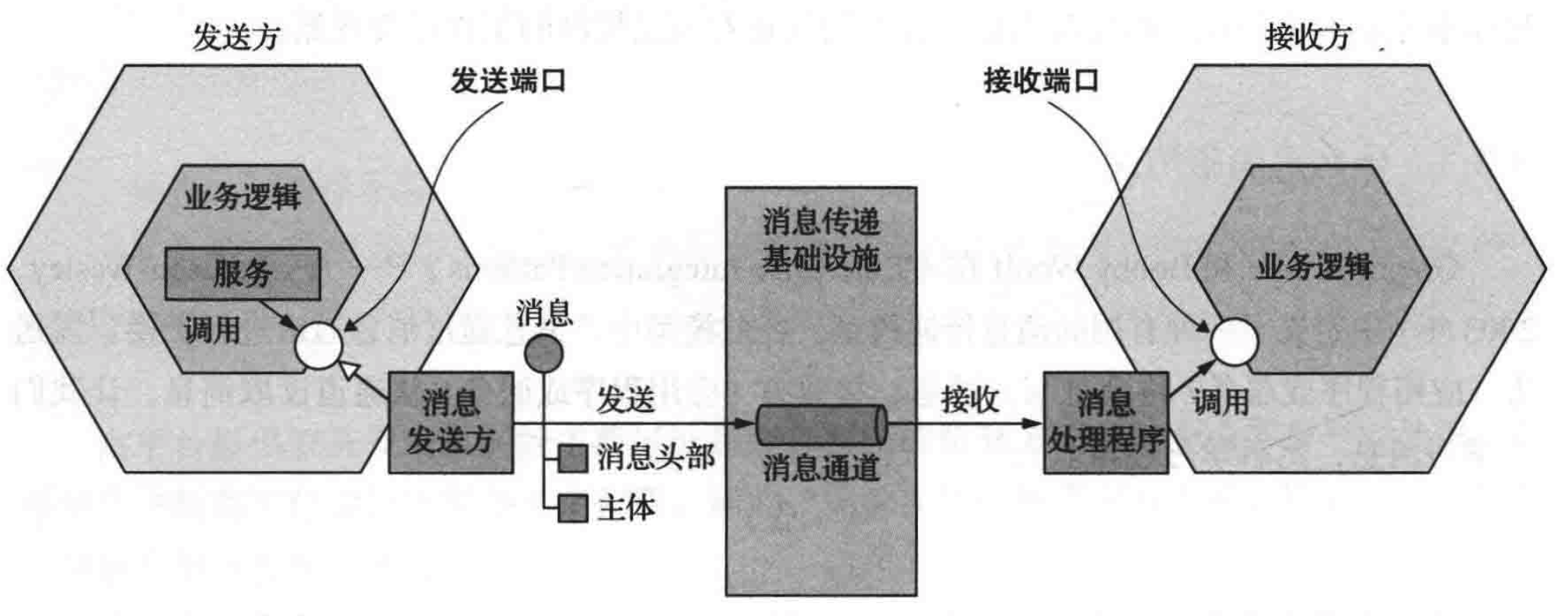
Communication between microservices
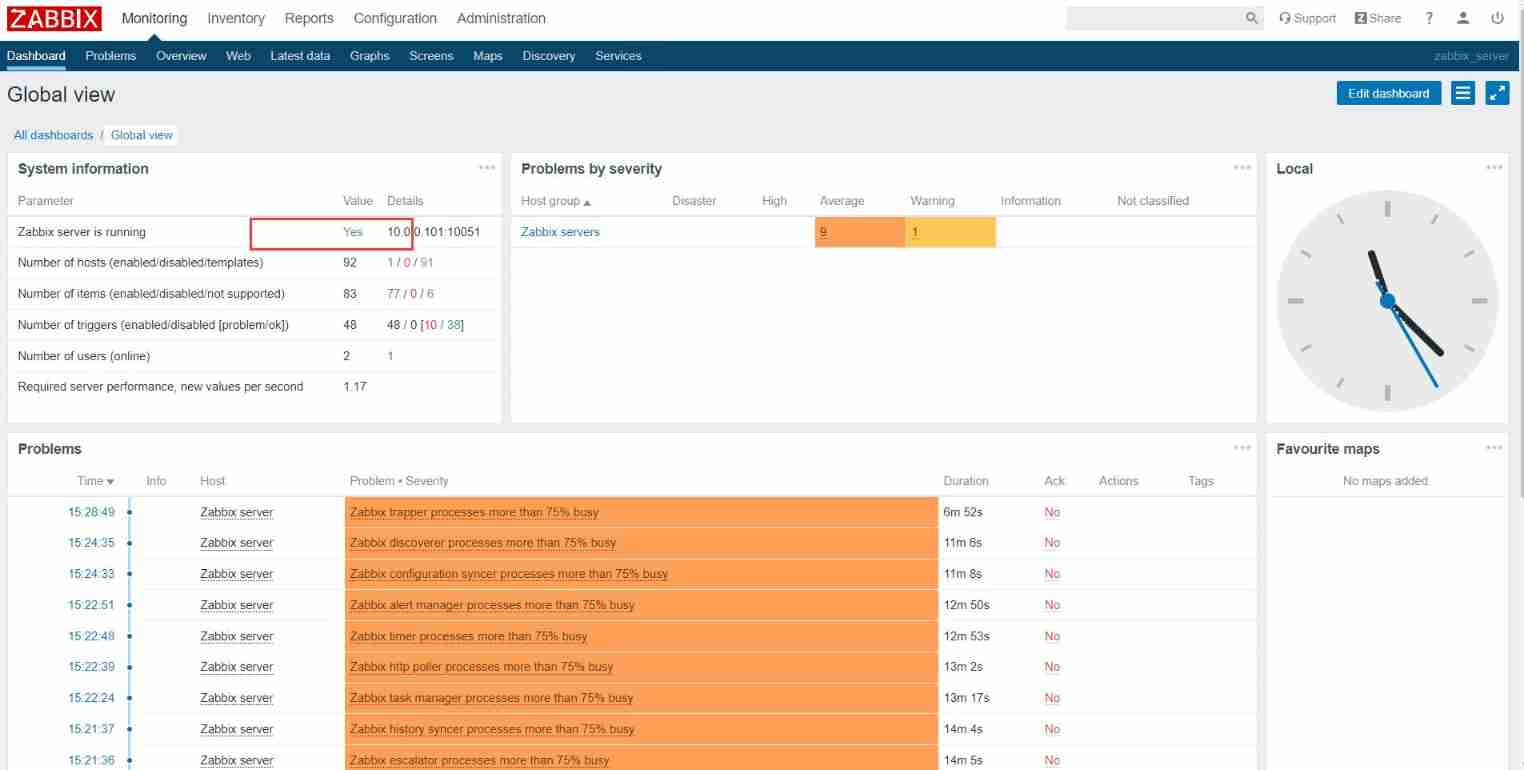
Apt installation ZABBIX
![[ruoyi] enable Mini navigation bar](/img/28/a8b38aecd90c8ddc98333f0e2d3eab.png)
[ruoyi] enable Mini navigation bar

Codeworks 5 questions per day (1700 average) - day 6
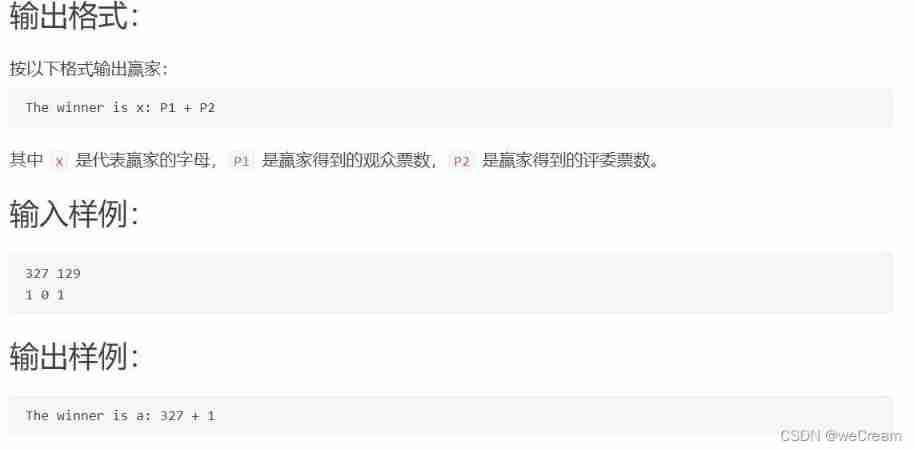
Who is the winner of PTA
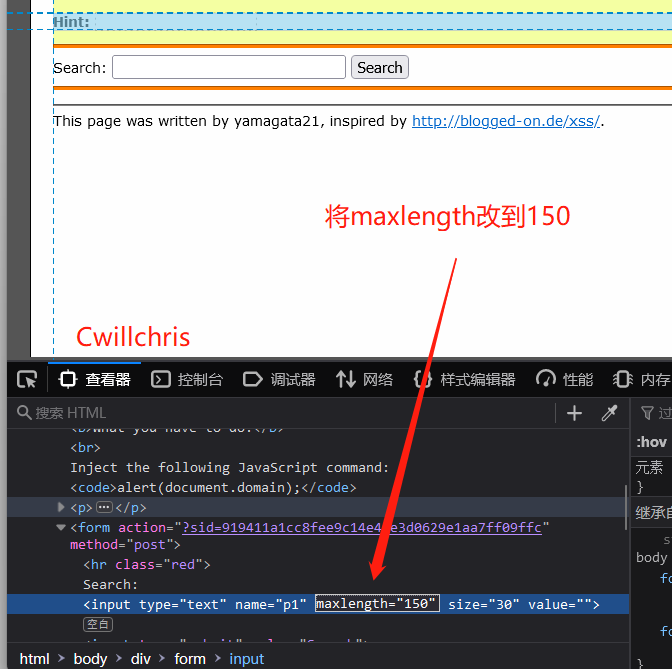
XSS challenges bypass the protection strategy for XSS injection
随机推荐
Briefly describe the implementation principle of redis cluster
Résumé des méthodes de reconnaissance des caractères ocr
Patch NTP server at the beginning of DDoS counterattack
PMP practice once a day | don't get lost in the exam -7.5
2.11 simulation summary
【Kubernetes 系列】一文學會Kubernetes Service安全的暴露應用
[pointer training - eight questions]
如何精准识别主数据?
淘宝焦点图布局实战
Which ecology is better, such as Mi family, graffiti, hilink, zhiting, etc? Analysis of five mainstream smart brands
华为、H3C、思科命令对比,思维导图形式从基础、交换、路由三大方向介绍【转自微信公众号网络技术联盟站】
07 singleton mode
Self made CA certificate and SSL certificate using OpenSSL
ERA5再分析资料下载攻略
1003 emergency (25 points), "DIJ deformation"
原型图设计
继承day01
Differences and usage scenarios between TCP and UDP
多态day02
Apt installation ZABBIX