当前位置:网站首页>Rhcsa day 3
Rhcsa day 3
2022-07-04 07:11:00 【Where are the peaches】
1、 Sum up vim Of the three modes, the commands you think are practical

1) application vi Command in /tmp Create files under folders , file name newfile. stay newfile Enter the date and time on the first line
2) take /boot/grub2/grub.cfg The contents of the document are read into newfile In the document ( On the next line of the date, i.e 2 That's ok )
3) Find documents that contain # The line of the sign character , Delete entire line
4) Turn on VI Line number prompt function
5) Move the cursor to 5 That's ok , And in the first place 5 A new blank line is generated after the line 6 That's ok
6) Modify the content . Will all timeout=5, Change to time=30
7) All... In the entire document root The character is changed to admin character
8) Copy No 1 The date and time content of the line to the end of the document
9) Save the document , Save the document again as /boot/newfile2, sign out VI Editor










4、 The file to view
Copy user profile to /opt Under the table of contents ;
see /opt/mima File first 6 That's ok ;


5. Statistics show user profiles nologin Number of occurrences

6. Displays the total number of users in the system

7. Set the system time ( Minutes and seconds ) write in time file

8.history The system command history can be displayed , Count the top three with the highest command frequency of the current system .( The command repeats three more commands )
边栏推荐
- Directory of tornado
- Selenium driver ie common problem solving message: currently focused window has been closed
- Master-slave replication principle of MySQL database
- js 常用时间处理函数
- Campus network problems
- Computer connects raspberry pie remotely through putty
- leetcode825. 适龄的朋友
- 响应式移动Web测试题
- what the fuck! If you can't grab it, write it yourself. Use code to realize a Bing Dwen Dwen. It's so beautiful ~!
- 响应式——媒体查询
猜你喜欢
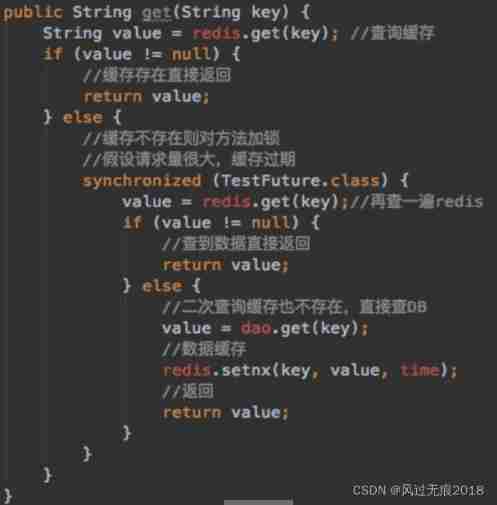
Redis - detailed explanation of cache avalanche, cache penetration and cache breakdown
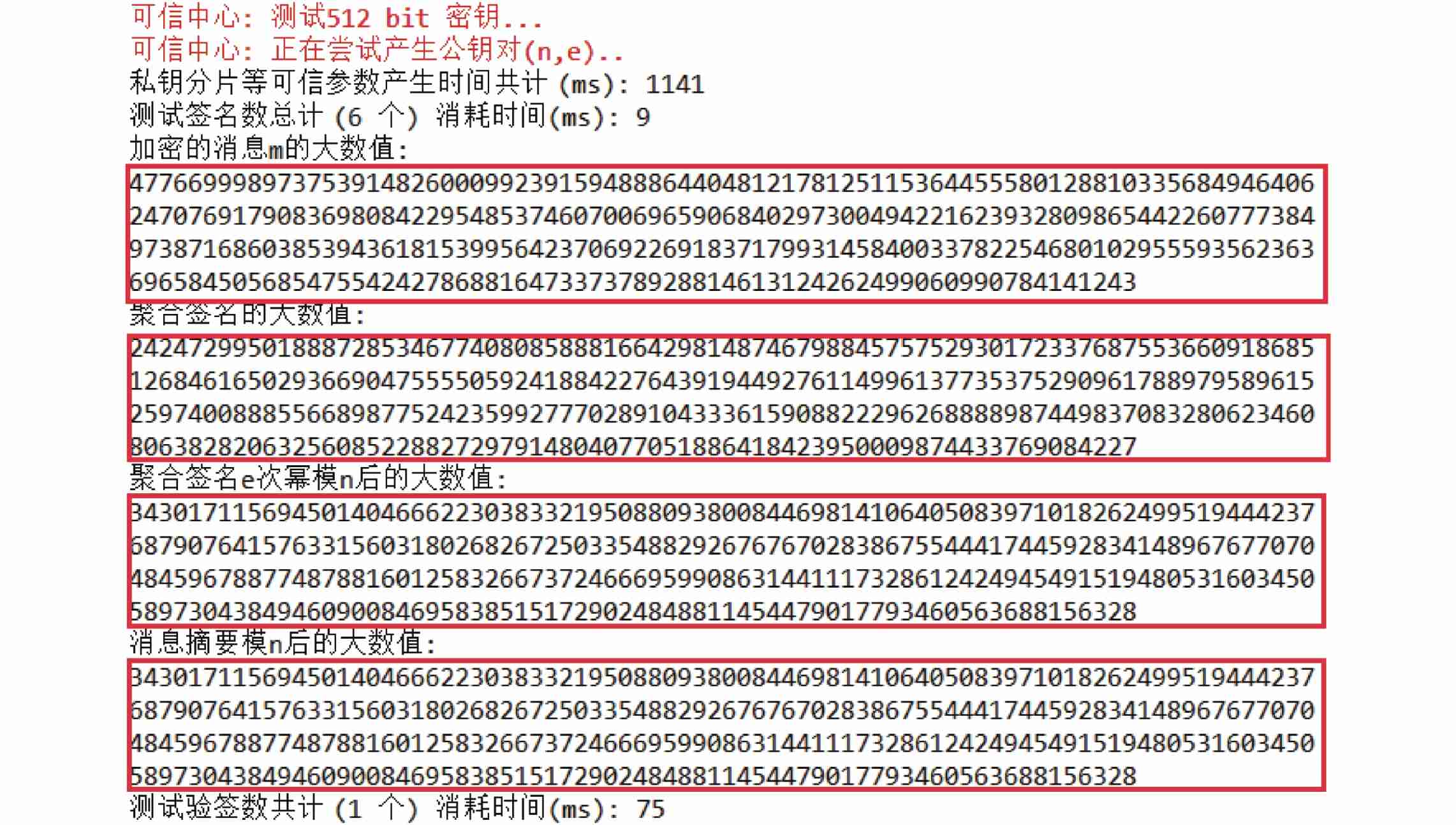
Research on an endogenous data security interaction protocol oriented to dual platform and dual chain architecture
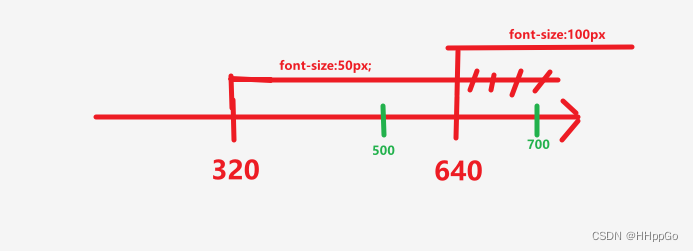
响应式移动Web测试题
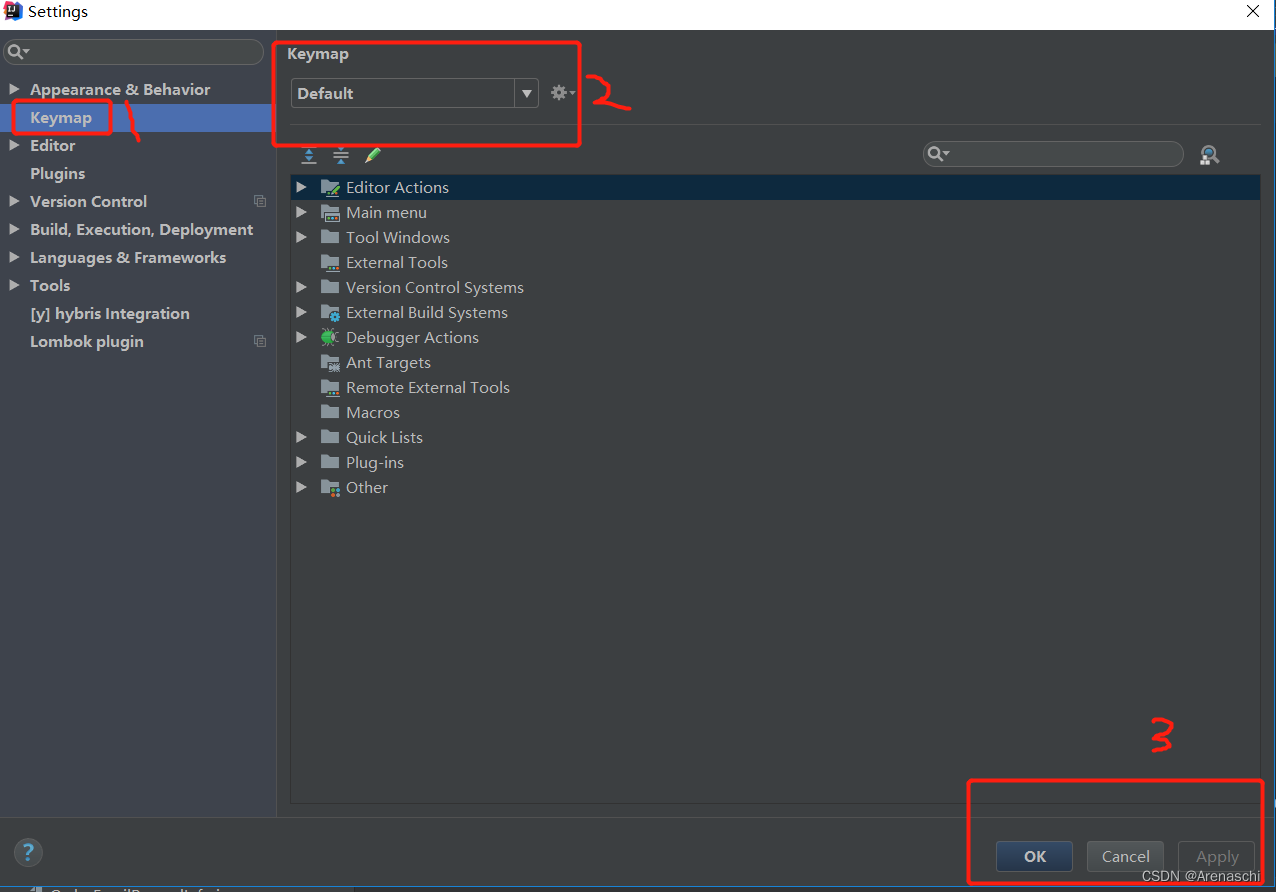
About how idea sets up shortcut key sets

Industrial computer anti-virus
校园网络问题

Two years ago, the United States was reluctant to sell chips, but now there are mountains of chips begging China for help
Vulhub vulnerability recurrence 76_ XXL-JOB
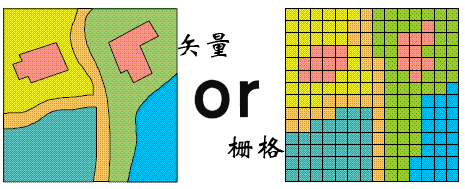
【森城市】GIS数据漫谈(一)
The final week, I split
随机推荐
Flink memory model, network buffer, memory tuning, troubleshooting
Chapter 1 programming problems
Redis interview question set
输入年份、月份,确定天数
MySQL 45 lecture learning notes (XIII) delete half of the table data, and the table file size remains the same
Electronic Association C language level 1 34, piecewise function
Summary of MySQL common judgment functions!! Have you used it
Introduction to spark core components
Selenium driver ie common problem solving message: currently focused window has been closed
If there are two sources in the same job, it will be reported that one of the databases cannot be found. Is there a boss to answer
tornado之目录
移动适配:vw/vh
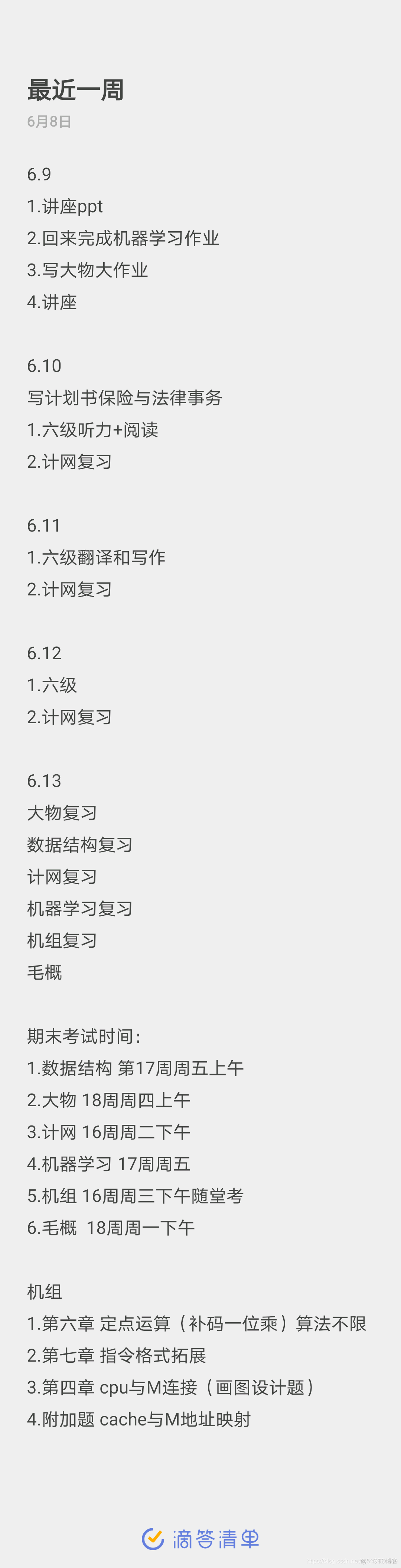
Summary of June 2022
jdbc连接es查询的时候,有遇到下面这种情况的大神嘛?
【FPGA教程案例7】基于verilog的计数器设计与实现
Adaptive spatiotemporal fusion of multi-target networks for compressed video perception enhancement
Electronic Association C language level 1 35, bank interest
MySQL storage engine
Experience installing VMware esxi 6.7 under VMware Workstation 16
关于IDEA如何设置快捷键集