当前位置:网站首页>函数:用牛顿迭代法求方程的根
函数:用牛顿迭代法求方程的根
2022-07-06 09:24:00 【|光|】
要求
用牛顿迭代法求方程的根。方程为ax3+bx2+cx+d=0,系数由用户输入,求x在1附近的根。
,
代码
#include<math.h>
#define EPSILON 1E-6
/* * 函数f(x)=a*x**3+b*x**2+c*x+d */
double f(double a,double b,double c, double d, double x)
{
double t;
t=a*x*x*x+b*x*x+c*x+d;
return t;
}
/* * 函数f(x)=a*x**3+b*x**2+c*x+d的导函数 */
double derivatives(double a,double b,double c, double d, double x)
{
double t;
t=3*a*x*x+2*b*x+c;
return t;
}
/* * 在该函数中用迭代法求解方程在1附近的根,可以调用上面的f函数和f的导函数 */
double fun(double a,double b,double c,double d)
{
double x1,x=1;
do
{
x1=x;
x = x1 - f(a,b,c,d,x)/derivatives(a,b,c,d,x);
}
while(fabs(x1-x)>=1e-3);
return x;
}
测试
测试输入
10 5 -11 -3.28351
输出
方程在1附近的根为0.97
边栏推荐
- 移植蜂鸟E203内核至达芬奇pro35T【集创芯来RISC-V杯】(一)
- Intranet information collection of Intranet penetration (2)
- Interpretation of iterator related "itertools" module usage
- Intranet information collection of Intranet penetration (4)
- Harmonyos JS demo application development
- Record an API interface SQL injection practice
- New version of postman flows [introductory teaching chapter 01 send request]
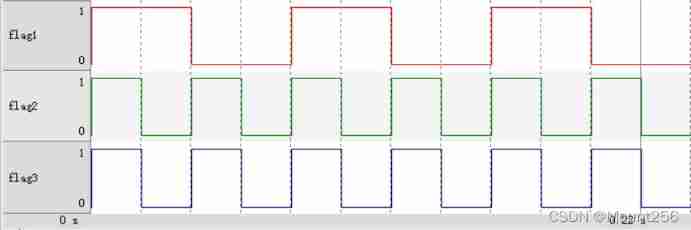
- Constants, variables, and operators of SystemVerilog usage
- 【指针】查找最大的字符串
- Binary search tree concept
猜你喜欢
Hackmyvm target series (2) -warrior
Build domain environment (win)
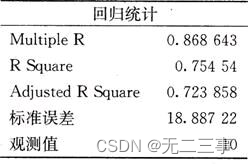
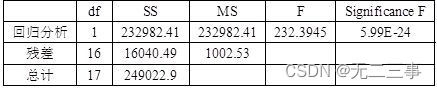
Statistics, 8th Edition, Jia Junping, Chapter 11 summary of knowledge points of univariate linear regression and answers to exercises after class
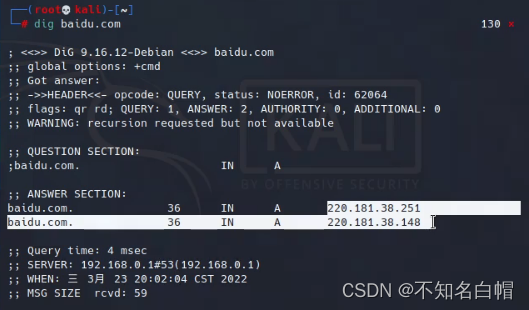
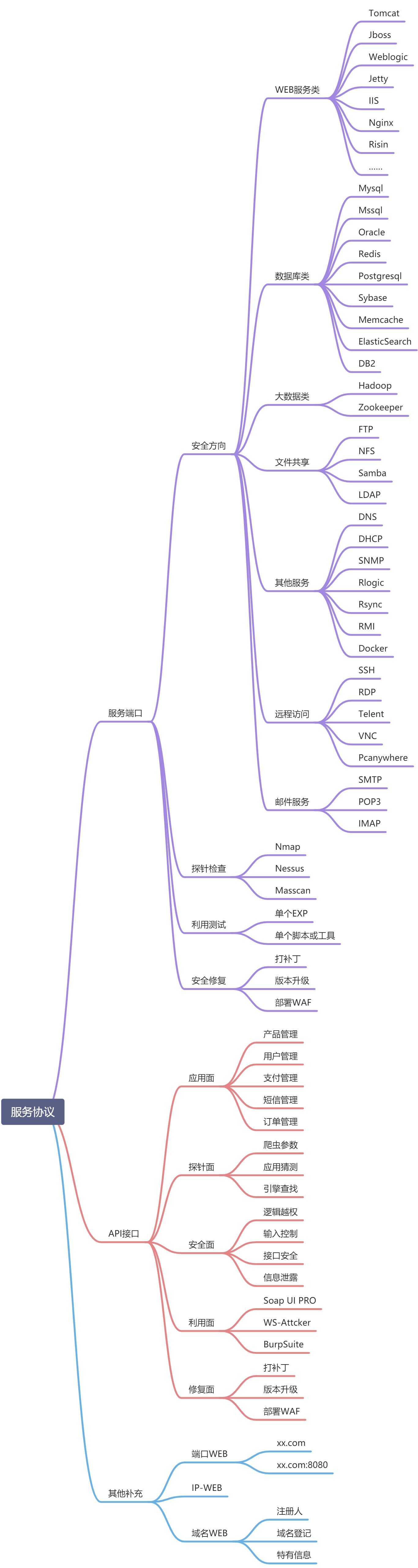
Internet Management (Information Collection)
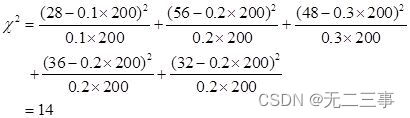
《统计学》第八版贾俊平第九章分类数据分析知识点总结及课后习题答案

How to earn the first pot of gold in CSDN (we are all creators)

Apache APIs IX has the risk of rewriting the x-real-ip header (cve-2022-24112)
Ucos-iii learning records (11) - task management
浅谈漏洞发现思路
《统计学》第八版贾俊平第十三章时间序列分析和预测知识点总结及课后习题答案
随机推荐
Realize applet payment function with applet cloud development (including source code)
内网渗透之内网信息收集(一)
外网打点(信息收集)
Statistics 8th Edition Jia Junping Chapter 5 probability and probability distribution
Load balancing ribbon of microservices
Windows platform mongodb database installation
How to turn wechat applet into uniapp
An unhandled exception occurred when C connected to SQL Server: system Argumentexception: "keyword not supported:" integrated
Statistics 8th Edition Jia Junping Chapter 14 summary of index knowledge points and answers to exercises after class
图书管理系统
flask实现强制登陆
Overview of LNMP architecture and construction of related services
线程的实现方式总结
New version of postman flows [introductory teaching chapter 01 send request]
Data mining - a discussion on sample imbalance in classification problems
Intranet information collection of Intranet penetration (2)
"Gold, silver and four" job hopping needs to be cautious. Can an article solve the interview?
Low income from doing we media? 90% of people make mistakes in these three points
Network layer - simple ARP disconnection
循环队列(C语言)